The digital realm, much like the physical world, operates under a constant flux of evolving threats and vulnerabilities. Staying ahead of these challenges requires a keen understanding of the tools and methodologies employed to safeguard our digital assets. While often associated with chemistry labs, the concept of a “litmus paper” transcends its scientific origins to serve as a potent metaphor within the technology sector, specifically in the domain of digital security. In this context, a “litmus paper” refers not to a physical strip of paper, but to a diagnostic technique, a method, or a tool that provides a quick, clear, and often binary indication of a system’s security posture or the presence of a specific threat.

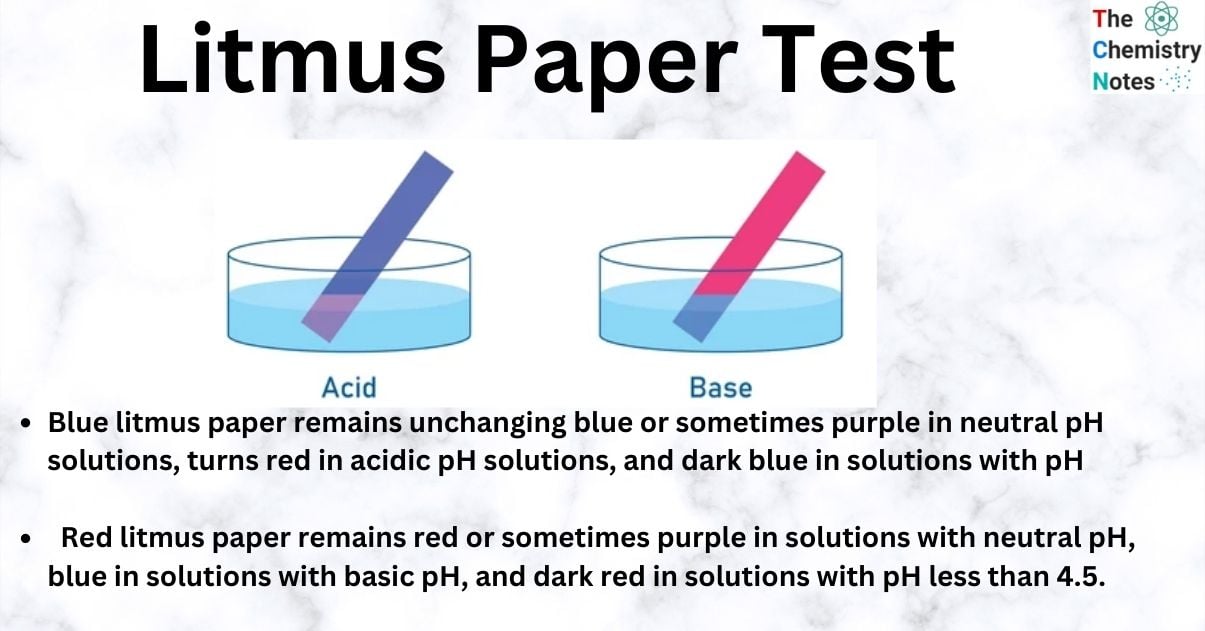
Just as a chemical litmus paper turns red in acidic conditions and blue in alkaline conditions, a digital security “litmus paper” provides a definitive signal. It’s a rapid assessment mechanism, designed to answer a crucial question with a high degree of confidence, allowing security professionals to make swift and informed decisions. This article will explore the concept of the “litmus paper” within digital security, delving into its various manifestations, its importance, and how it contributes to a robust cybersecurity strategy. We will examine its applications in threat detection, vulnerability assessment, and incident response, illustrating its value through practical examples and highlighting its role in empowering proactive security measures.
The Digital Litmus Test: Identifying Security Anomalies
In the complex landscape of information technology, identifying deviations from expected or secure behavior is paramount. This is where the concept of a digital “litmus paper” truly shines. It’s about creating a system or a process that acts as an immediate indicator, flagging potential issues before they escalate into significant breaches. The core principle is to establish a baseline of normal, secure operation and then employ tests that quickly reveal any significant departures from this baseline.
Behavioral Anomalies as Red Flags
One of the most effective forms of digital litmus tests involves monitoring user and system behavior. By establishing patterns of normal activity – such as login times, typical data access, and network traffic flow – security systems can be trained to recognize deviations. For instance, a user account suddenly attempting to access highly sensitive data outside of its usual operational hours or from an unusual geographic location would act as a digital “litmus paper,” triggering an alert. This isn’t just about looking for known malware signatures; it’s about detecting suspicious behavior that might indicate a compromised account or an insider threat.
Network Traffic Analysis for Suspicious Signatures
The flow of data within a network is a rich source of information for security diagnostics. Tools that analyze network traffic can act as digital litmus papers by identifying patterns that are characteristic of malicious activity. This could include:
- Unusual Protocol Usage: The unexpected use of certain network protocols or unusual patterns in their implementation can signal an attempt to exfiltrate data or establish covert communication channels.
- High Volume of Outbound Connections: A sudden surge in outgoing connections from a server that normally has minimal outbound traffic could indicate a botnet activity or data exfiltration.
- Encrypted Traffic to Unknown Destinations: While encrypted traffic is often legitimate, a sudden spike in encrypted connections to servers with no prior legitimate interaction can be a warning sign.
- Specific Payload Signatures: While not as dynamic as behavioral analysis, the presence of known malicious payloads or command-and-control (C2) communication patterns within network traffic still serves as a clear litmus test for active infection.
Endpoint Security Diagnostics
Beyond network-level monitoring, individual endpoints – such as workstations, servers, and mobile devices – can also be subjected to digital litmus tests. These tests aim to quickly assess the security health of a device.
- Malware Scans with Aggressive Signatures: While traditional antivirus scans are a standard practice, more advanced endpoint detection and response (EDR) solutions can perform rapid, targeted scans designed to quickly identify the presence of known threats based on advanced behavioral and signature analysis.
- Configuration Drift Detection: Systems can be configured to regularly check for unauthorized changes to critical system settings, software installations, or registry entries. Any deviation from the approved configuration acts as a litmus test, indicating a potential compromise.
- Running Process and Service Monitoring: Continuously monitoring running processes and services for the presence of known malicious entities or unusual activity can provide an immediate alert.
The effectiveness of these digital litmus tests lies in their ability to provide actionable intelligence quickly. They are designed to be sensitive enough to detect anomalies but also precise enough to minimize false positives, allowing security teams to focus their resources on genuine threats.
Vulnerability Assessment: Proactive Security Checks
Before an attack can occur, vulnerabilities often exist within systems and applications. The concept of a “litmus paper” extends to proactively identifying these weaknesses, acting as an early warning system for potential exploitation. These tests are crucial for maintaining a strong security posture and preventing breaches before they materialize.
Automated Scanning Tools: The First Line of Defense
Automated vulnerability scanners are perhaps the most common and accessible form of digital litmus paper for identifying known weaknesses. These tools systematically probe systems, networks, and applications for common vulnerabilities.
- Network Vulnerability Scanners: Tools like Nessus, Qualys, and OpenVAS can be configured to scan an entire network infrastructure. They look for outdated software, missing security patches, misconfigurations, and known exploits, providing a report that clearly indicates the severity of each identified vulnerability. A high-severity finding essentially turns the system into a “red” litmus paper, indicating a critical need for remediation.
- Web Application Scanners: For web applications, scanners like OWASP ZAP, Burp Suite, and Acunetix can detect common web vulnerabilities such as SQL injection, cross-site scripting (XSS), and broken authentication. An automated scan that flags these issues acts as an immediate litmus test for the application’s security.
- Database Scanners: Specialized tools can scan databases for vulnerabilities, such as weak passwords, improper access controls, and unpatched database software.
The output of these scanners provides a clear, often color-coded, indication of the security status of the scanned assets. They simplify the complex task of identifying potential weaknesses by providing a straightforward assessment.
Penetration Testing: Simulating Real-World Attacks
While automated scanners are efficient for broad assessments, penetration testing (pen testing) offers a more sophisticated digital litmus test by simulating the actions of a real attacker. A pen test involves ethical hackers attempting to exploit vulnerabilities within a defined scope.
- The Goal of Mimicry: The core idea of a pen test is to answer the question: “Can an attacker breach our defenses?” By actively trying to break in, pen testers effectively put the security controls to a stringent test.
- Indicative Findings: Successful exploitation of a vulnerability during a pen test is a definitive “red” litmus test result. It proves that a weakness exists and is exploitable, necessitating immediate attention. Even failed attempts can provide valuable insights by highlighting the effectiveness of existing defenses.
- Types of Pen Tests: These can range from external pen tests (simulating attacks from the internet) to internal pen tests (simulating attacks from within the network) and even social engineering tests. Each type acts as a tailored litmus paper for specific attack vectors.
The insights gained from penetration testing are invaluable. They go beyond simply listing vulnerabilities; they demonstrate the real-world impact and provide a clear understanding of how attackers might gain access.
Code Review and Static Analysis: Building Security In
For software development teams, identifying vulnerabilities early in the development lifecycle is crucial. Static Application Security Testing (SAST) tools and manual code reviews act as digital litmus papers during the coding phase.
- SAST Tools: These tools analyze source code without executing it, looking for common programming errors that can lead to security vulnerabilities. A SAST tool flagging potential buffer overflows or insecure deserialization is akin to a litmus paper turning red, indicating a problem that needs fixing before the code is deployed.
- Manual Code Reviews: Experienced security engineers can manually review code, looking for logic flaws, insecure coding practices, and potential vulnerabilities that automated tools might miss. This human-driven approach offers a deeper and more nuanced assessment, acting as a qualitative litmus test of the code’s security.
By integrating these types of vulnerability assessment into the development and operational workflows, organizations can continuously test their defenses and ensure that their digital assets are as resilient as possible.
Incident Response: Rapid Threat Identification and Containment
When a security incident occurs, time is of the essence. The ability to quickly and accurately identify the nature and scope of a breach is critical for effective incident response. In this high-pressure environment, digital “litmus papers” are indispensable for making rapid decisions and mitigating damage.
Threat Intelligence Feeds as Predictive Litmus Tests
Threat intelligence feeds provide valuable, up-to-date information about emerging threats, attacker tactics, techniques, and procedures (TTPs), and indicators of compromise (IoCs). These feeds act as predictive litmus papers, helping organizations anticipate and detect potential attacks.
- IoCs as Red Flags: IoCs can include IP addresses associated with malicious servers, known malware hash values, specific domain names used for command-and-control, or unusual file names. When these IoCs are detected within an organization’s network or systems, they serve as a clear “red” signal, indicating a likely compromise.
- Behavioral Threat Intelligence: Beyond static IoCs, some threat intelligence focuses on behavioral patterns associated with known threat actors. If an organization’s systems exhibit behaviors that align with these TTPs, it acts as a strong indicator of a potential attack.
The integration of threat intelligence into security monitoring tools allows for automated detection, effectively turning the threat intelligence itself into a real-time digital litmus paper.
Security Information and Event Management (SIEM) Systems
SIEM systems are designed to aggregate and analyze security data from various sources across an organization’s IT infrastructure. They are powerful platforms that can implement numerous digital litmus tests in real-time.
- Correlation Rules: SIEMs use predefined or custom correlation rules to identify suspicious patterns of activity. For example, a rule might trigger an alert if a user logs in from two geographically distant locations within a short period, or if multiple failed login attempts are followed by a successful login from an unusual source. These rules act as sophisticated litmus tests, constantly evaluating the security posture.
- Alerting and Prioritization: When a correlation rule is triggered, the SIEM generates an alert. The system’s ability to prioritize these alerts based on severity and potential impact is crucial, allowing security teams to focus on the most critical “red” indicators first.
Digital Forensics Tools for Deep Dives
When an incident is suspected or confirmed, digital forensics tools come into play. These tools allow investigators to meticulously examine digital evidence to understand what happened, how it happened, and who was responsible. While more investigative than immediate diagnostic, certain forensic techniques can also act as digital litmus tests.
- File System Analysis: Examining file system metadata, such as creation dates, modification times, and access logs, can reveal the timeline of an attack. The presence of recently created or modified files in unusual locations, or files with suspicious names, can be a clear indicator of malicious activity.
- Memory Analysis: Analyzing the contents of a system’s RAM can reveal running processes, network connections, and other volatile data that might not be present on the disk. The identification of specific malicious processes or injected code within memory acts as a powerful litmus test for active compromise.
In the realm of incident response, the digital litmus paper isn’t just about detecting an initial breach; it’s about confirming the scope, understanding the methods used, and ultimately, containing the threat as quickly and effectively as possible. The ability to rapidly discern the “red” from the “green” can be the difference between a minor incident and a catastrophic data breach.
The Future of Digital Litmus Tests: AI and Automation
The evolution of digital security is intrinsically linked to technological advancements. The concept of the “litmus paper” is not static; it’s constantly being refined and enhanced by emerging technologies, most notably Artificial Intelligence (AI) and advanced automation. These advancements are making digital diagnostics faster, more accurate, and more proactive than ever before.
AI-Powered Anomaly Detection
Traditional anomaly detection relies on predefined rules and known patterns. AI, particularly machine learning (ML), takes this a step further by enabling systems to learn and adapt to evolving threats and normal behavior.
- Unsupervised Learning: AI algorithms can analyze vast datasets of normal system behavior without explicit programming. They can then identify subtle deviations that might indicate previously unknown threats or zero-day exploits. This “learning” capability makes AI a highly sophisticated and adaptable digital litmus paper.
- Behavioral Biometrics: In the realm of user authentication, AI can analyze a user’s typing cadence, mouse movements, and interaction patterns. Any significant deviation from these established “biometric” signatures can trigger an alert, acting as a personal digital litmus paper for account security.
- Predictive Threat Modeling: AI can analyze global threat landscapes and historical data to predict future attack trends and identify potential vulnerabilities before they are widely exploited. This proactive approach acts as a forward-looking litmus test for an organization’s readiness.
Autonomous Security Operations
The increasing complexity and volume of cyber threats necessitate a move towards more autonomous security operations. This means empowering systems to not only detect threats but also to respond to them with minimal human intervention.
- Automated Incident Triage and Response: AI-driven SIEMs and Security Orchestration, Automation, and Response (SOAR) platforms can automatically analyze alerts, determine their severity, and initiate predefined response playbooks. This could include isolating a compromised endpoint, blocking malicious IP addresses, or revoking user credentials. These automated actions are the ultimate manifestation of a digital litmus paper – immediate, decisive, and automated.
- Proactive Threat Hunting: AI can assist human threat hunters by sifting through massive amounts of data to identify subtle indicators of compromise that might otherwise go unnoticed. This allows security teams to focus on more complex investigations, knowing that the initial “litmus tests” are being performed effectively by AI.

The Importance of Continuous Validation
Even with advanced AI and automation, the effectiveness of any digital litmus test, whether manual or automated, relies on continuous validation and refinement.
- Regular Updates: Threat landscapes change rapidly. Security tools, threat intelligence feeds, and AI models must be regularly updated to remain effective.
- False Positive/Negative Management: It’s crucial to monitor the performance of diagnostic tools and adjust them to minimize false positives (alerting on benign activity) and false negatives (failing to detect actual threats). This iterative process ensures the reliability of the digital litmus test.
- Human Oversight: While automation is key, human expertise remains indispensable. Security professionals are needed to interpret complex alerts, conduct deeper investigations, and make strategic decisions that go beyond the scope of automated tests.
In conclusion, the concept of the “litmus paper” in digital security is a powerful metaphor for rapid, clear, and actionable diagnostics. From simple behavioral anomaly detection to sophisticated AI-driven threat prediction, these tools and methodologies are essential for navigating the ever-evolving cybersecurity landscape. As technology continues to advance, we can expect digital litmus tests to become even more sophisticated, playing a critical role in safeguarding our increasingly interconnected world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.