In the contemporary digital landscape, the question “what is scanned?” has evolved from a simple inquiry about paper documents into a multifaceted exploration of how we digitize reality itself. In its broadest technological sense, scanning is the process of sampling a physical object, a signal, or a data environment to convert it into a digital format that can be processed, analyzed, and stored by a computer.
Today, scanning permeates every layer of our technological existence. We scan our faces to unlock smartphones, companies scan their networks for vulnerabilities, and industrial sensors scan physical components to create “digital twins.” As we move further into the era of Artificial Intelligence (AI) and the Internet of Things (IoT), understanding the mechanics and the scope of what is being scanned is essential for grasping how data-driven decisions are made.

1. The Evolution of Document Scanning: From Paper to Intelligence
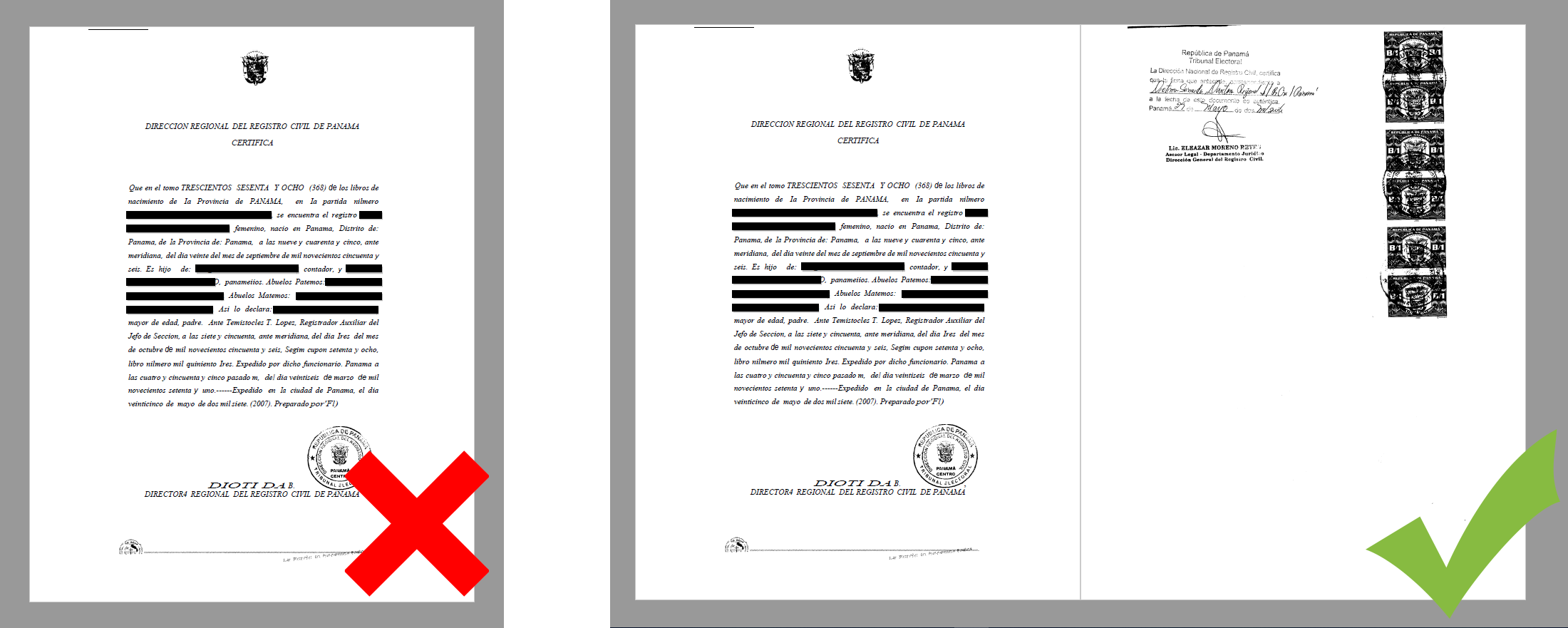
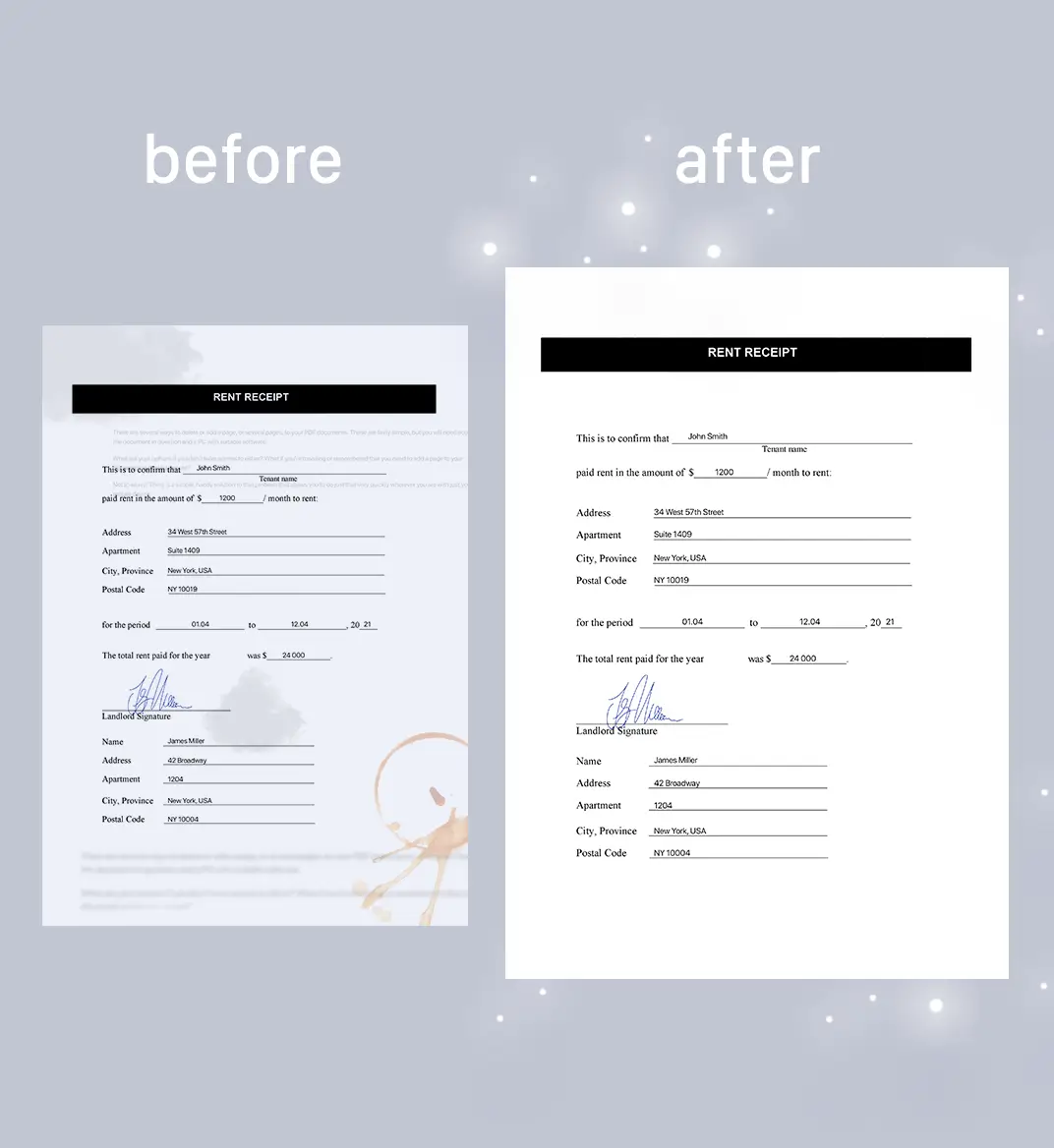
The most traditional answer to “what is scanned” involves the conversion of physical documents into digital files. However, the technology has moved far beyond the flatbed scanners of the 1990s. Today, document scanning is synonymous with “Intelligent Document Processing” (IDP).
The Mechanics of Optical Character Recognition (OCR)
At the heart of modern document scanning lies Optical Character Recognition (OCR). OCR technology has transitioned from basic pattern matching—where a computer simply compared a scanned shape to a known letter—to sophisticated neural networks. Modern OCR can recognize handwriting, multiple languages within a single document, and even the “intent” of a layout. When a page is scanned today, the software isn’t just taking a picture; it is identifying semantic structures, such as headers, footers, and tables, ensuring that the resulting digital file is searchable and editable.
Intelligent Document Processing (IDP) and AI Integration
Beyond simple text recognition, we now see the rise of Intelligent Document Processing. IDP utilizes Machine Learning (ML) to categorize “what is scanned” automatically. For instance, in a corporate environment, a scanner can distinguish between an invoice, a legal contract, and a medical record without human intervention. By extracting specific data points—such as tax IDs, totals, or expiration dates—IDP transforms a static image into actionable data that can be fed directly into Enterprise Resource Planning (ERP) systems.
Cloud-Integrated Scanning Workflows
The physical hardware of the scanner is no longer a standalone silo. Most modern scanning solutions are cloud-integrated. When a document is scanned, it is instantly uploaded to a secure server where it undergoes automated version control and encryption. This allows for global collaboration, where a document scanned in London is instantly accessible, indexed, and categorized for a team in Singapore.
2. Cybersecurity and Network Scanning: What Lies Beneath the Surface
In the realm of digital security, scanning refers to the systematic inspection of networks, ports, and code to identify weaknesses. In this context, “what is scanned” is the invisible infrastructure that keeps our digital world running.
Vulnerability Scanning and Penetration Testing
Vulnerability scanners are automated tools that “scan” an organization’s IT environment to find security holes. These tools probe operating systems, applications, and networks for known vulnerabilities, such as unpatched software or misconfigured firewalls. A vulnerability scan provides a roadmap for IT teams, highlighting the “attack surface” that a hacker might exploit. This proactive scanning is a cornerstone of modern cybersecurity posture, moving security from a reactive “fix-it-when-it-breaks” model to a continuous monitoring state.
Port Scanning and Network Topology Mapping
On a more granular level, port scanning is the process of sending packets to specific ports on a host to see which ones are “open,” “closed,” or “filtered.” This tells a network administrator which services are running (such as web servers or email protocols). By scanning ports across an entire subnet, software can generate a network topology map—a visual representation of every device connected to a network. This is vital for hardware asset management and for detecting unauthorized “rogue” devices that might have been introduced to a secure environment.
Code Scanning in DevOps
In the world of software development, “what is scanned” is the source code itself. Through Static Application Security Testing (SAST), developers scan their code for logic errors, hard-coded passwords, or insecure API calls before the software is ever deployed. This “shift-left” approach to security ensures that vulnerabilities are caught early in the development lifecycle, reducing the cost and risk associated with post-release patches.
3. Biometrics and Physical Scans: Digitizing the Human Body and Environment
One of the most significant shifts in scanning technology is the transition from two-dimensional data to three-dimensional and biological data. We are increasingly scanning the physical world and our own bodies to enhance security and convenience.
Facial Recognition and Iris Scanning
Biometric scanning has become the gold standard for identity verification. Facial recognition technology scans the geometry of a human face—measuring the distance between the eyes, the shape of the cheekbones, and the depth of the eye sockets. Similarly, iris scanning captures the unique patterns in the colored ring of the eye. Unlike traditional passwords, these scans are incredibly difficult to spoof. When your phone “scans” your face, it is projecting thousands of invisible infrared dots to create a mathematical model of your features, ensuring that only the authorized user gains access.
3.D Scanning and LiDAR Technology
The integration of LiDAR (Light Detection and Ranging) into consumer electronics, such as the iPad Pro and high-end smartphones, has revolutionized what can be scanned in a physical space. LiDAR scans the environment by emitting light pulses and measuring how long they take to bounce back. This allows for the creation of high-precision 3D maps of rooms, objects, and landscapes. This technology is foundational for Augmented Reality (AR), where digital objects must interact realistically with a scanned physical environment, and for autonomous vehicles, which must constantly scan their surroundings to navigate safely.
Medical Imaging and Bio-Scanning
In the medical tech sector, scanning is a lifesaver. MRI, CT, and PET scans provide a non-invasive way to “scan” the internal structures of the human body. The frontier of this technology involves AI-assisted scanning, where algorithms help radiologists identify anomalies that might be too subtle for the human eye. Furthermore, wearable tech now allows for the continuous “scanning” of vital signs, such as heart rate variability and blood oxygen levels, turning the human body into a source of real-time health data.
4. The Future of Scanned Data: Privacy, Integration, and Edge Computing
As the scope of “what is scanned” expands, the tech industry faces new challenges regarding data volume, processing speed, and ethical considerations.
Data Privacy in a “Scanned” World
The more we scan, the more sensitive data we generate. Whether it is a scanned biometric signature or a scanned legal document, the security of this data is paramount. Tech trends are moving toward enhanced encryption and the implementation of “Zero Trust” architectures. The question of who owns “scanned” data—especially biometric data—is a central theme in modern tech legislation like the GDPR (General Data Protection Regulation). Companies are now required to be transparent about what is being scanned and how that data is being stored.
Edge Computing and Real-Time Scanning
The sheer volume of data generated by modern scanning (especially 3D and high-resolution video scanning) creates a bandwidth bottleneck. This is where edge computing comes in. Instead of sending all scanned data to a centralized cloud server for processing, “edge” devices process the scan locally. For example, a security camera with an integrated AI chip can “scan” a crowd for a specific object and only send an alert if that object is found, rather than uploading hours of raw footage. This makes scanning faster, more efficient, and more private.
The Role of Digital Twins
Perhaps the most ambitious application of scanning is the creation of “Digital Twins.” By scanning an entire industrial plant or a complex piece of machinery with high-fidelity sensors, engineers can create a digital replica that mirrors the physical object in real-time. This scanned model allows for predictive maintenance, where the system can simulate “what-if” scenarios and predict a mechanical failure before it happens in the physical world.
Conclusion
“What is scanned” is no longer a question with a single answer. It is a spectrum of technology that spans from the simple digitization of a receipt to the complex, real-time mapping of a smart city. As OCR, cybersecurity scanning, biometrics, and LiDAR continue to converge, the line between the physical and digital worlds will continue to blur.
For businesses and individuals alike, the value lies not just in the act of scanning, but in the intelligence derived from the scan. By transforming physical reality into structured digital data, scanning provides the fuel for the AI revolution, enabling a world that is more efficient, more secure, and more deeply understood. Whether it is for security, productivity, or innovation, scanning remains the primary bridge between the world we inhabit and the digital future we are building.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.