In the world of mathematics, certain concepts serve as the foundational building blocks for complex structures. Prime factorization is one such concept. At its simplest level, finding the prime factorization of a number like 35—which yields the primes 5 and 7—might seem like an elementary school exercise. However, in the realm of technology, these integer decompositions are the silent sentinels guarding our digital lives. From the encryption protocols that protect your credit card information to the algorithms that optimize database searches, the logic behind the factorization of 35 is a microcosm of the logic that drives the modern tech landscape.

Understanding the Mathematical Foundation: Why 5 and 7 Matter
To appreciate the technological implications of prime factorization, one must first understand the purity of the mathematical process. Prime factorization is the process of breaking down a composite number into a product of prime numbers. A prime number, by definition, is a natural number greater than 1 that has no positive divisors other than 1 and itself.
The Logic of Factoring 35
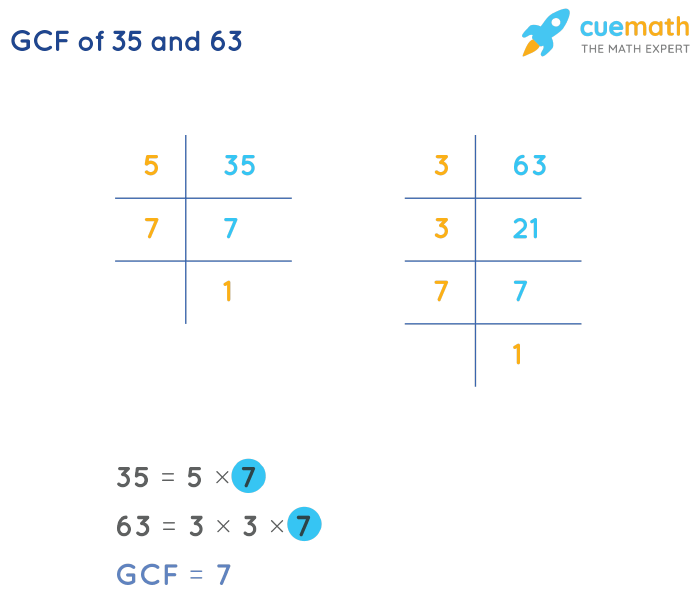
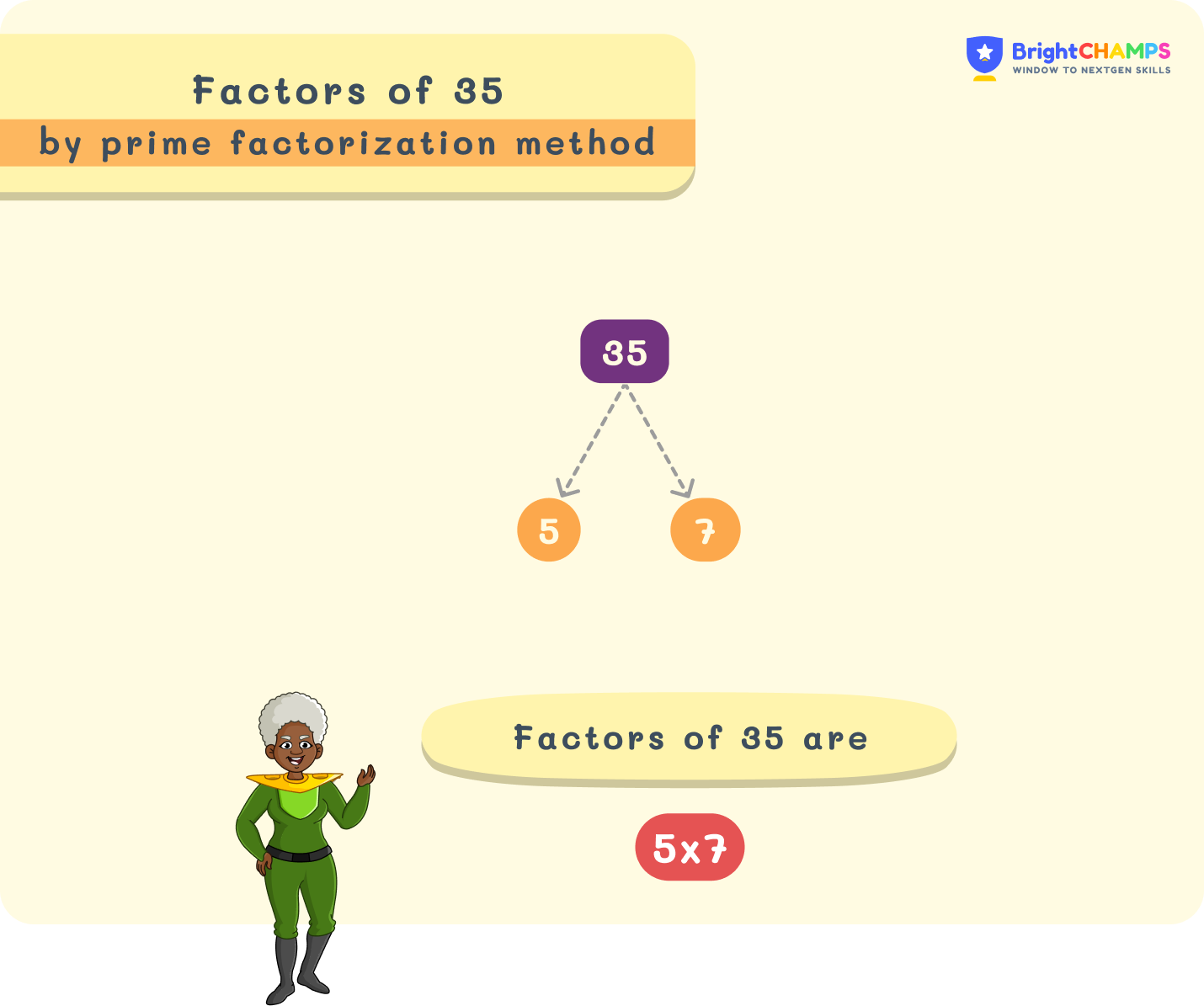
When we look at the number 35, we are looking at a “composite” number. To find its prime factors, we employ several methods, the most common being the factor tree or the division method.
- The Search for Divisors: We begin with the smallest prime number, 2. Since 35 is odd, 2 is not a factor.
- Moving Up the Prime Scale: We check 3. The sum of the digits (3+5=8) is not divisible by 3, so 35 is not divisible by 3.
- Identifying the First Factor: We move to 5. Since 35 ends in a 5, it is divisible by 5.
- The Final Result: Dividing 35 by 5 gives us 7. Both 5 and 7 are prime numbers.
Thus, the prime factorization of 35 is 5 x 7. This simple equation represents a unique “numerical fingerprint.” According to the Fundamental Theorem of Arithmetic, every integer greater than 1 either is a prime number itself or can be represented as a product of prime numbers in a way that is unique, regardless of the order of the factors.
The Concept of Primality in Computational Logic
In computer science, prime numbers are valued because they are “indivisible” units of data logic. When software engineers design systems that require unique identification or non-repeating cycles, they often turn to primes. The fact that 35 can only be broken down into 5 and 7—and no other combination of primes—ensures a level of predictability and stability in algorithmic structures. This mathematical certainty is the bedrock upon which secure software is built.
Prime Factorization in the Digital Age: The Backbone of Cybersecurity
While factoring 35 is a task a human can perform in seconds, the technological world relies on the fact that factoring much larger numbers is incredibly difficult for computers. This disparity is the basis for modern cybersecurity, specifically in the field of public-key cryptography.
From Simple Integers to RSA Encryption
The most famous application of prime factorization in tech is the RSA (Rivest–Shamir–Adleman) encryption algorithm. RSA is used by almost every secure web connection (HTTPS), email service, and digital signature platform. The core mechanism of RSA involves choosing two very large prime numbers (think hundreds of digits long) and multiplying them together to create a massive composite number.
In our analogy, if 35 were the public key, the factors 5 and 7 would be the private key. In a real-world scenario, a tech system might use a composite number that is 2,048 bits long. While a computer can multiply two 1,024-bit primes instantly to get a product, reversing the process—finding those original primes from the product—would take a modern supercomputer trillions of years.
The “Trapdoor Function”: Why Factorization is Hard
In technology, we refer to this as a “trapdoor function.” It is easy to go one way (multiplication) but nearly impossible to go the other (factorization) without a “key.” When you send an encrypted message, your device uses the “35” (the public composite number) to lock the data. Only the recipient, who knows the “5” and “7” (the private prime factors), can unlock it. This mathematical wall is what prevents hackers from intercepting and reading your sensitive data. Without the ability to factorize that large number, the encrypted data remains a meaningless string of characters.
Algorithmic Efficiency and Software Development
Beyond the high-stakes world of cybersecurity, the principles of prime factorization and the properties of numbers like 35 play a vital role in everyday software optimization and data architecture.
Optimization in Data Processing and Hashing
Software developers frequently use prime numbers to handle data distribution. When building a “hash table”—a data structure used to implement associative arrays—developers need to map data to specific locations in memory. To avoid “collisions” (where two pieces of data try to occupy the same spot), the size of the hash table is often set to a prime number.
If a developer were working with a small dataset, they might choose a table size related to a prime factor of a number like 35. By using prime-based logic, the algorithm ensures that data is distributed more uniformly across the system, reducing lag and increasing the speed of information retrieval.
Prime Numbers in Load Balancing and Scheduling
In distributed computing, where multiple servers handle millions of requests, prime factorization helps in “load balancing.” Engineers use prime cycles to ensure that tasks are rotated across processors in a way that prevents any single node from being overwhelmed. If a system is designed to cycle through tasks in increments based on prime factors, it minimizes the chance of “harmonics” or repetitive patterns that could lead to synchronized system crashes. The “uniqueness” of 5 and 7 in the factorization of 35 ensures that these cycles do not overlap in inefficient ways.
The Future of Factorization: Quantum Computing and the Threat to Security
The tech world is currently facing a “cryptographic crisis” known as the Quantum Threat. For decades, our digital security has relied on the difficulty of prime factorization. However, the advent of quantum computing promises to change the rules of the game entirely.
Shor’s Algorithm: Breaking the Code
In 1994, mathematician Peter Shor developed a quantum algorithm that could factor large integers exponentially faster than any known classical algorithm. While a traditional computer must check factors one by one or use complex sieves, a quantum computer uses the principle of superposition to evaluate many possibilities simultaneously.
Using Shor’s Algorithm, a sufficiently powerful quantum computer could take a number like 35 and identify 5 and 7 almost instantaneously. More importantly, it could do the same for the 2,048-bit numbers that currently protect the global financial system. This would render RSA encryption obsolete, effectively “breaking the internet” as we know it.
Preparing for Post-Quantum Cryptography
In response to this technological shift, the tech industry is racing to develop “Post-Quantum Cryptography” (PQC). This involves creating new encryption methods that do not rely on prime factorization. Tech giants like Google, IBM, and Microsoft are investing billions into lattice-based cryptography and other mathematical problems that even quantum computers find difficult to solve.
Even as we move away from factorization for our most sensitive secrets, the logic remains a fundamental part of tech education. Understanding how 35 breaks down into 5 and 7 is the first step for any aspiring computer scientist in understanding the relationship between mathematics and machine logic.
Conclusion: The Infinite Value of Finite Factors
The question “what is the prime factorization of 35” may seem like a simple mathematical query, but it is the doorway to the most sophisticated systems ever built by humanity. The numbers 5 and 7 represent more than just factors; they represent the concept of digital integrity.
In the tech niche, we recognize that our digital world is built on these mathematical certainties. Whether it is the security of a blockchain transaction, the efficiency of a cloud server, or the future of quantum processing, the principles of prime factorization remain at the core. As we continue to innovate, we must look back at these fundamental building blocks. The journey from the simple factorization of 35 to the complex encryption of the global web is a testament to the power of mathematics in driving technological progress. As we move into the quantum era, the “prime” challenges will only grow more complex, but the logic established by these ancient mathematical truths will continue to guide us.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.