In the modern digital landscape, the term “network traffic” is often used as a catch-all phrase to describe the activity occurring within a computer system or across the internet. However, for technology professionals, network administrators, and cybersecurity experts, network traffic represents the vital lifeblood of global communication. Every email sent, every video streamed, and every database query executed contributes to a massive, invisible surge of data moving across copper wires, fiber optics, and wireless frequencies.
Understanding what network traffic is, how it is measured, and why its management is critical to both performance and security is essential for navigating today’s hyper-connected world. This guide delves into the technical intricacies of data flow, the methods used to monitor it, and the strategies employed to keep digital pipelines running efficiently.
Understanding the Fundamentals of Network Traffic
At its most basic level, network traffic refers to the amount of data moving across a network at any given time. This data is not sent as a single, massive block; instead, it is broken down into smaller, manageable units known as packets. This process ensures that if a single piece of data is lost or corrupted during transmission, only that small segment needs to be resent, rather than the entire file.
The Anatomy of a Data Packet
To understand traffic, one must understand the packet. A packet typically consists of three parts: the header, the payload, and the trailer.
- The Header: This contains the “metadata” or routing instructions. It includes the source IP address, the destination IP address, the protocol being used (such as HTTP or FTP), and the packet number (to help the receiving device reassemble the data in the correct order).
- The Payload: This is the actual content being transmitted—be it a snippet of a high-definition video, a piece of a text message, or a segment of a software update.
- The Trailer (or Footer): This contains error-checking information, such as a cyclic redundancy check (CRC), which tells the receiving device whether the packet arrived intact or was damaged during transit.
How Traffic Moves: The Role of Protocols
Network traffic does not move randomly; it follows strict sets of rules known as protocols. These protocols act as a common language that allows different devices—ranging from a smartphone in Tokyo to a server in London—to communicate seamlessly.
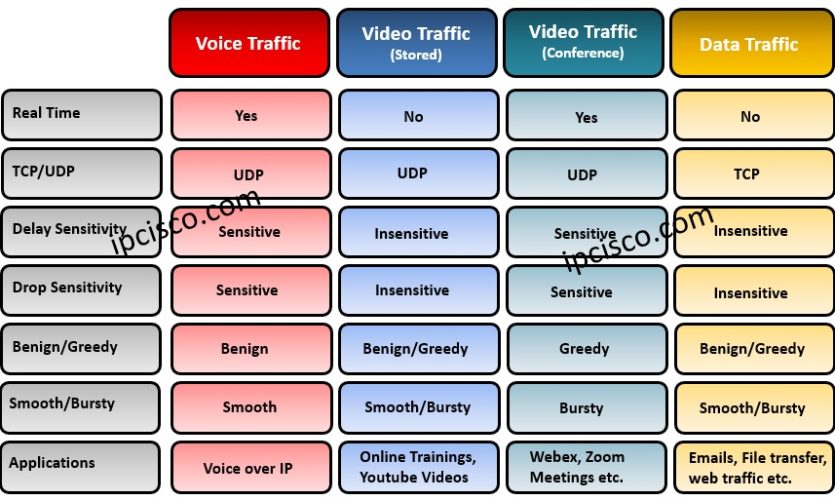
The most fundamental of these is the Internet Protocol Suite (TCP/IP). Transmission Control Protocol (TCP) is designed for reliability, ensuring that every packet arrives and is in the correct order. In contrast, User Datagram Protocol (UDP) is used for speed-sensitive traffic like live gaming or video calls, where losing a few packets is preferable to a delay in the live stream. Other common protocols include HTTP/HTTPS for web browsing, SMTP for email, and DNS for translating domain names into IP addresses.
The Different Types of Network Traffic
Not all network traffic is created equal. Categorizing traffic helps IT professionals prioritize important data and identify potential security threats. Traffic is generally classified by its direction and its origin.
Inbound vs. Outbound Traffic
The most common distinction made by firewalls and security software is between inbound and outbound traffic.
- Inbound Traffic: This refers to data entering a network from an external source. For a business, this might be a customer accessing their website or a remote employee downloading a file from the company server.
- Outbound Traffic: This is data leaving the internal network to go elsewhere. Examples include sending an email to a client or a local server uploading a backup to a cloud provider. Monitoring outbound traffic is a critical security measure, as unusual spikes can indicate that a computer on the network has been compromised and is “exfiltrating” sensitive data to a hacker’s server.
Internal (East-West) vs. External (North-South) Traffic
In a data center or large enterprise environment, engineers also categorize traffic by its physical path.
- North-South Traffic: This describes data moving between the internal network and the outside world (the internet). It passes through the “gateway” or perimeter of the network.
- East-West Traffic: This describes data moving laterally between servers or devices within the same internal network. In modern cloud environments and microservices architectures, East-West traffic has grown exponentially. Because this traffic never leaves the internal network, it is often less scrutinized, making it a favorite hiding spot for sophisticated cyber threats that move laterally across a system after an initial breach.
Measuring and Monitoring Traffic Health
To maintain a healthy digital infrastructure, organizations must move beyond simply knowing traffic exists; they must measure its quality and volume. Network performance is dictated by several key metrics that determine how “fast” or “reliable” a connection feels to the end-user.

Key Performance Indicators: Bandwidth, Latency, and Jitter
When we talk about network speed, we are usually referring to a combination of three factors:
- Bandwidth: This is the maximum capacity of a network link. Think of it as the width of a highway. A wider highway can accommodate more cars at once, but it doesn’t necessarily mean the cars are driving faster.
- Latency: Often called “ping,” latency is the time it takes for a packet to travel from the source to the destination and back. High latency results in “lag,” which is highly noticeable in real-time applications like VoIP calls or online gaming.
- Jitter: This refers to the variation in latency. If some packets arrive in 10ms and others in 100ms, the resulting “jitter” causes stuttering in audio and video transmissions.
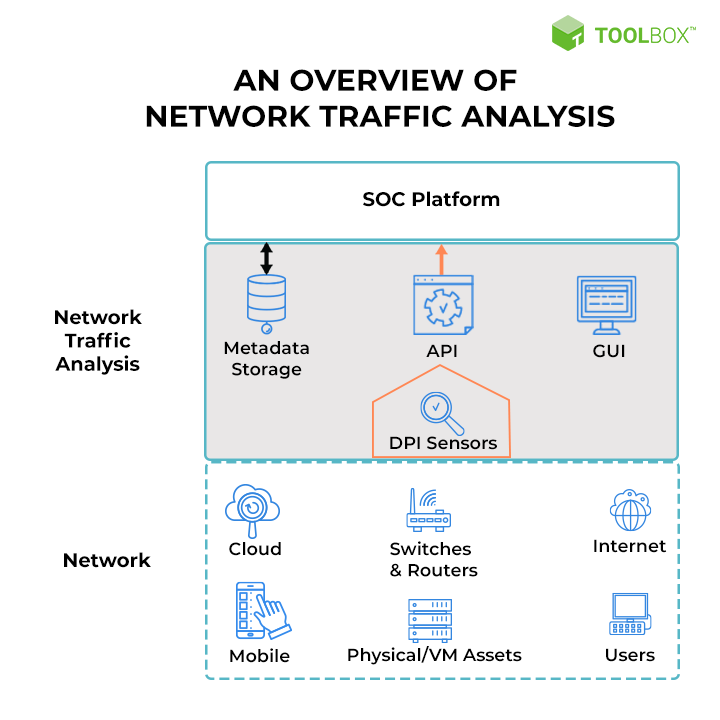
The Necessity of Network Traffic Analysis (NTA)
Network Traffic Analysis (NTA) is the practice of intercepting and inspecting packets to understand what is happening on a network. Modern NTA tools use sophisticated algorithms to provide real-time visibility. By analyzing traffic patterns, administrators can perform Capacity Planning, ensuring they have enough bandwidth to handle peak usage times, and Troubleshooting, identifying which specific application or device is hogging resources and slowing down the network for everyone else.
Network Traffic and Cybersecurity: Protecting the Digital Pipeline
Traffic is not just about utility; it is also the primary vector for cyberattacks. Every packet that enters a network is a potential carrier for malware, or part of a larger scheme to take down a service.
Identifying Malicious Traffic Patterns
Security professionals look for specific “signatures” or anomalies in network traffic that indicate an attack.
- DDoS (Distributed Denial of Service): This occurs when a network is flooded with an overwhelming amount of traffic from thousands of different sources, causing the system to crash.
- Port Scanning: This involves a bot sending small packets to various “ports” on a server to see which ones are open and vulnerable to attack.
- Botnet Traffic: If a large number of internal devices start communicating with a single unknown IP address simultaneously, it is a strong indicator that they have been infected and are being controlled by a remote “command and control” server.
The Impact of Encryption on Traffic Visibility
Today, over 90% of web traffic is encrypted via HTTPS (using TLS/SSL protocols). While encryption is vital for privacy and protecting sensitive data like passwords and credit card numbers, it presents a challenge for security teams. If the traffic is encrypted, how can a firewall see if a packet contains malware?
To solve this, many organizations use SSL Inspection (or TLS Decryption). This involves “unwrapping” the packet at the network gateway, scanning its contents for threats, and then re-encrypting it before sending it to its final destination. This balance between privacy and security is a central theme in modern network management.
Optimizing Network Traffic for the Modern Enterprise
As the volume of global data continues to grow—fueled by 4K video, IoT devices, and AI-driven applications—managing traffic has become a complex engineering feat.
Traffic Shaping and Quality of Service (QoS)
Not all traffic is equally important. A CEO’s video conference call is more time-sensitive than an employee’s large file download. Quality of Service (QoS) allows network administrators to prioritize certain types of traffic over others. By implementing Traffic Shaping, they can “throttle” or limit the bandwidth available to non-essential applications (like social media or software updates) during business hours to ensure that mission-critical tools have a clear path.
The Future: AI and Machine Learning in Traffic Management
The future of network traffic lies in automation. With the rise of Software-Defined Networking (SDN) and Artificial Intelligence (AI), networks are becoming “self-healing.” AI-driven traffic management tools can predict spikes in demand before they happen and reroute data dynamically to avoid congestion.
Furthermore, machine learning models are now capable of identifying “Zero-Day” threats—attacks that have never been seen before—by recognizing subtle deviations from a network’s “normal” traffic behavior. As we move into the era of 5G and the Internet of Things (IoT), where billions of devices will be generating traffic simultaneously, these intelligent systems will be the only way to keep our digital infrastructure stable and secure.
In conclusion, network traffic is far more than just “data in motion.” It is a complex, regulated, and highly monitored ecosystem. By understanding the mechanics of packets, the nuances of different traffic types, and the vital importance of monitoring and security, we can better appreciate the invisible architecture that supports the modern technological world. Whether you are an IT professional or a curious user, recognizing the flow of traffic is the first step in mastering the digital domain.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.