In the realm of business operations, particularly those reliant on robust technological infrastructure, the concept of a “maintenance emergency” is a critical one. It’s not merely about something breaking; it’s about the immediate, often catastrophic, impact of that breakdown on the core functions of an organization. For businesses operating in the digital age, where uptime, data integrity, and seamless customer interaction are paramount, understanding what constitutes a maintenance emergency is fundamental to proactive risk management and rapid response. This isn’t about scheduled upgrades or routine tune-ups; it’s about those high-stakes situations that demand immediate, often round-the-clock attention to prevent significant financial loss, reputational damage, or critical operational paralysis.
The definition of a maintenance emergency is intrinsically tied to the business context and the specific technologies that power it. What might be a minor inconvenience in one setting could be a full-blown crisis in another. The underlying principle is that a maintenance emergency represents a deviation from normal, expected operational status that poses an immediate and severe threat to business continuity, security, or profitability. It’s the moment when the digital gears of a company grind to a halt, and the wheels of commerce threaten to stop turning altogether.
Defining the Threshold: When Routine Becomes Critical
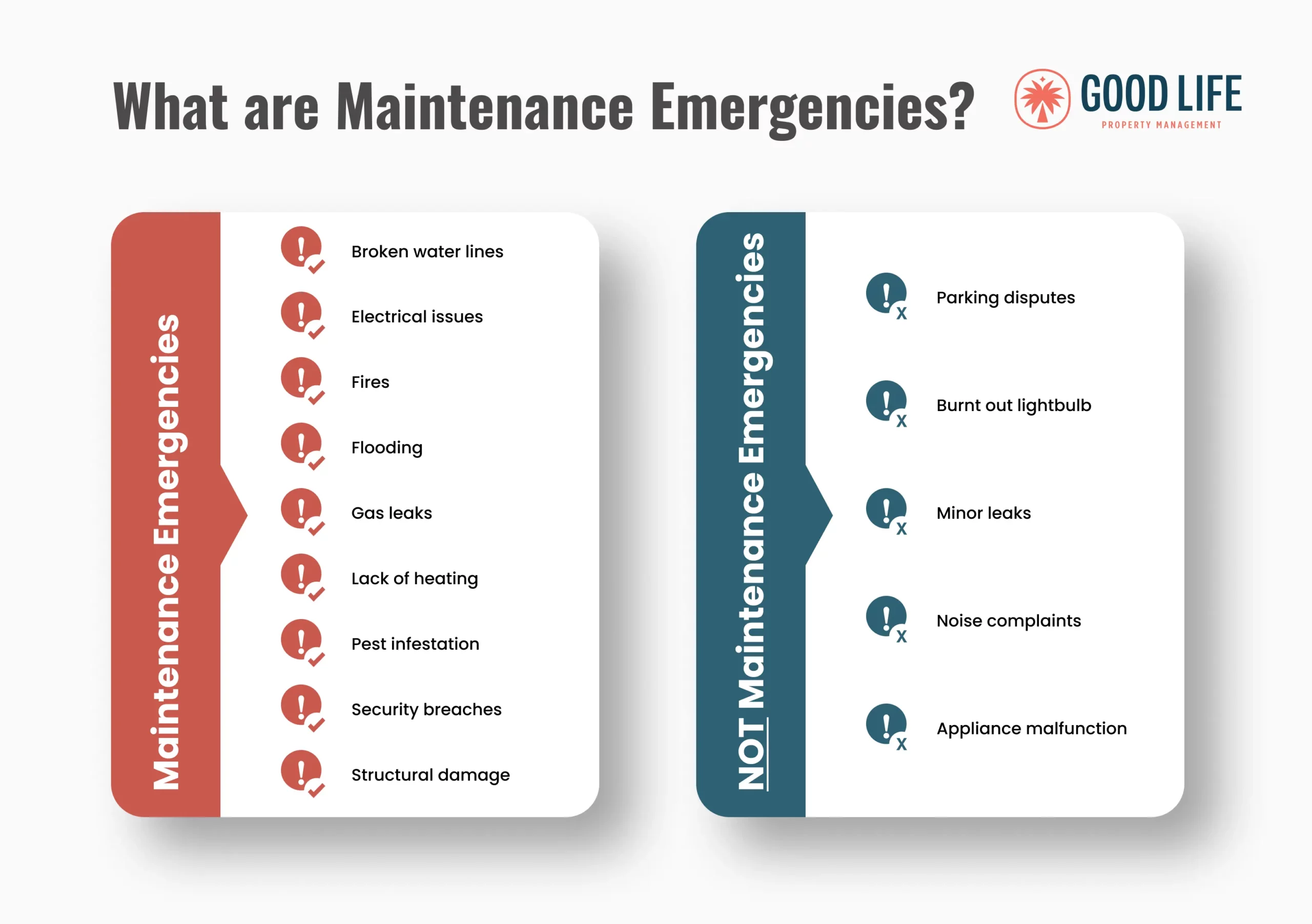
The distinction between a planned maintenance event and an emergency is stark. Planned maintenance, though sometimes disruptive, is scheduled, communicated, and executed with the intent of preventing future issues or optimizing performance. It’s a controlled process. A maintenance emergency, conversely, is unplanned, often unexpected, and necessitates an immediate, high-priority response. It’s characterized by its urgency and the potential for severe negative consequences if not addressed swiftly.
Unforeseen System Failures and Downtime
At the heart of most maintenance emergencies lies the unexpected failure of critical IT systems. This can manifest in various forms, from hardware malfunctions to software bugs that cripple essential services. The key factor is the impact on the business. If a server hosting a company’s primary e-commerce platform crashes, leading to an inability to process orders, that’s an emergency. If a database responsible for customer records becomes inaccessible, preventing sales teams from accessing crucial information, that’s also an emergency. The immediacy of the business impact is the defining characteristic. It’s not just about the technology failing; it’s about the business process failing because the technology did.
The Ripple Effect of Critical Component Failure
When a core technological component fails, the consequences rarely remain isolated. A failure in a payment gateway, for instance, doesn’t just stop transactions; it can lead to lost revenue, customer frustration, and potentially a decline in trust and brand loyalty. Similarly, a breach in cybersecurity, which is a form of system vulnerability maintenance emergency, can have far-reaching consequences, including data theft, regulatory fines, and severe reputational damage that can take years to repair. The interconnected nature of modern technological systems means that a single point of failure can indeed cascade, impacting multiple operational areas and creating a widespread crisis.
Data Loss and Corruption Incidents
Data is the lifeblood of most modern businesses. Any event that jeopardizes the integrity or availability of this data automatically escalates to emergency status. This includes situations where data is unexpectedly lost due to hardware failure, accidental deletion, or malicious attack, or when data becomes corrupted, rendering it unusable or inaccurate. The inability to access or rely on critical business data can halt operations, invalidate reports, and lead to significant compliance and legal challenges. For organizations that handle sensitive customer information or proprietary intellectual property, data loss is not just an operational hiccup; it’s a potential existential threat.
The Paramountcy of Data Integrity and Availability
The concept of data integrity refers to the accuracy and consistency of data throughout its lifecycle. Corruption can arise from various sources, including power surges, software errors, or cyber threats. Data availability, on the other hand, concerns the accessibility of that data when needed. An emergency arises when either integrity or availability is compromised to a degree that impedes critical business functions. For example, if financial records become corrupted, preventing accurate reporting or auditing, or if customer order history becomes inaccessible, making it impossible to fulfill existing orders, these are clear maintenance emergencies. The ability to recover this data, or to continue operating without it, will dictate the severity and duration of the emergency.
Identifying the Indicators: Recognizing the Signs of Imminent Crisis
Proactive identification of potential maintenance emergencies is crucial. It’s about recognizing the subtle (and sometimes not-so-subtle) warning signs that indicate a system is moving beyond routine maintenance needs and towards critical failure. This requires a keen understanding of system performance metrics, security logs, and user feedback. The ability to distinguish between a minor performance degradation and a harbinger of complete system collapse is a hallmark of effective IT management.
Performance Degradation Beyond Tolerable Limits

While systems naturally experience fluctuations in performance, a significant and sustained degradation in speed, responsiveness, or error rates can signal a looming emergency. This isn’t about a single slow loading webpage; it’s about an entire application becoming sluggish, processing times for critical operations tripling, or an increasing number of users reporting errors or timeouts. These symptoms often indicate underlying issues such as hardware strain, resource contention, or critical software bugs that are beginning to manifest. Ignoring these signs can allow a manageable problem to snowball into an unmanageable crisis.
Monitoring Key Performance Indicators (KPIs) and Anomaly Detection
Effective IT management relies on rigorous monitoring of Key Performance Indicators (KPIs). These are quantifiable measures that demonstrate how effectively a system is achieving its key business objectives. For example, website uptime percentage, average response time, error rates, and transaction processing times are all critical KPIs. An anomaly detection system, which uses algorithms to identify unusual patterns or outliers in these KPIs, can provide early warnings. A sudden spike in CPU usage on a critical server, a significant increase in network latency, or a surge in failed login attempts can all be flagged by anomaly detection tools, prompting investigation before a full-blown emergency erupts.
Security Vulnerabilities and Cyberattack Incidents
In the digital landscape, security is not a separate concern but an integral part of maintenance. A newly discovered vulnerability in a widely used software or operating system, especially one that is actively being exploited, constitutes a maintenance emergency. Similarly, any indication of a live cyberattack, such as unauthorized access attempts, malware infections, or distributed denial-of-service (DDoS) attacks, demands immediate attention. The potential for data breaches, system disruption, and reputational damage makes these incidents high-priority emergencies.
Responding to Exploited Vulnerabilities and Active Threats
When a critical security vulnerability is identified and known to be exploited in the wild, a rapid response is imperative. This often involves applying emergency patches, reconfiguring security settings, or even temporarily disabling certain functionalities to mitigate the risk. Active cyberattacks are even more urgent. The focus shifts from prevention to immediate containment and eradication. This may involve isolating compromised systems, blocking malicious IP addresses, initiating incident response protocols, and engaging cybersecurity experts. The goal is to stop the attack in its tracks and minimize its impact.
Escalation and Response: Mobilizing for Action
Once a maintenance emergency is recognized, the focus shifts to swift and coordinated action. This involves clear communication, defined roles and responsibilities, and access to the necessary resources and expertise to resolve the issue as quickly and efficiently as possible. The speed and effectiveness of the response can significantly influence the overall business impact.
The Role of Incident Response Teams and Protocols
Most organizations that rely heavily on technology will have established Incident Response Teams (IRTs) and detailed protocols for handling emergencies. An IRT is a group of individuals specifically trained and tasked with responding to and managing IT incidents. Incident response protocols outline the steps to be taken, from initial detection and assessment to containment, eradication, recovery, and post-incident analysis. These protocols ensure a structured and systematic approach, minimizing confusion and maximizing efficiency during a high-stress situation. The clearer and more well-rehearsed these protocols are, the more effective the response will be.
Communication Channels and Stakeholder Management
Effective communication is paramount during a maintenance emergency. This involves establishing clear channels for internal communication among the IRT and relevant IT personnel, as well as external communication with affected business units, management, and potentially customers or partners. Stakeholder management is critical; keeping key individuals informed about the nature of the problem, the steps being taken to resolve it, and the estimated time to recovery helps manage expectations and mitigate panic. Transparency, even when delivering bad news, builds trust and fosters collaboration.
Prioritization and Resource Allocation
Not all emergencies are created equal. During a widespread outage, the IRT must be able to quickly prioritize issues based on their potential impact on critical business functions. For example, an outage affecting customer-facing sales portals might take precedence over an internal administrative system issue, depending on the business context. Resource allocation follows this prioritization; ensuring that the most skilled personnel, critical hardware, and necessary software tools are directed towards the highest-priority issues is essential for efficient resolution. This often involves a dedicated “war room” or virtual command center where the response can be coordinated.

Root Cause Analysis and Post-Mortem
Once the immediate crisis is resolved, the work is not done. A thorough root cause analysis (RCA) is crucial to understand why the emergency occurred in the first place. This involves dissecting the events leading up to the incident, identifying the underlying technical or procedural flaws, and developing corrective actions to prevent recurrence. A post-mortem meeting, where the incident is reviewed by all involved parties, serves as a learning opportunity. Documenting lessons learned and implementing the recommended changes strengthens the organization’s resilience and improves future incident response capabilities. This iterative process of learning and improvement is key to long-term IT stability and business continuity.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.