In the realm of technology, particularly within the cybersecurity and gaming sectors, the term “attack potency” emerges as a critical, albeit sometimes vaguely defined, concept. It signifies the inherent power or effectiveness of an offensive action, whether that action is a digital exploit, a malicious software’s capability, or a character’s special move in a virtual world. Understanding attack potency is crucial for developers crafting secure systems, defenders building robust defenses, and players strategizing for victory. This article delves into the multifaceted nature of attack potency, exploring its definition, its key determinants, and its implications across various technological domains.

Defining Attack Potency in a Digital Context
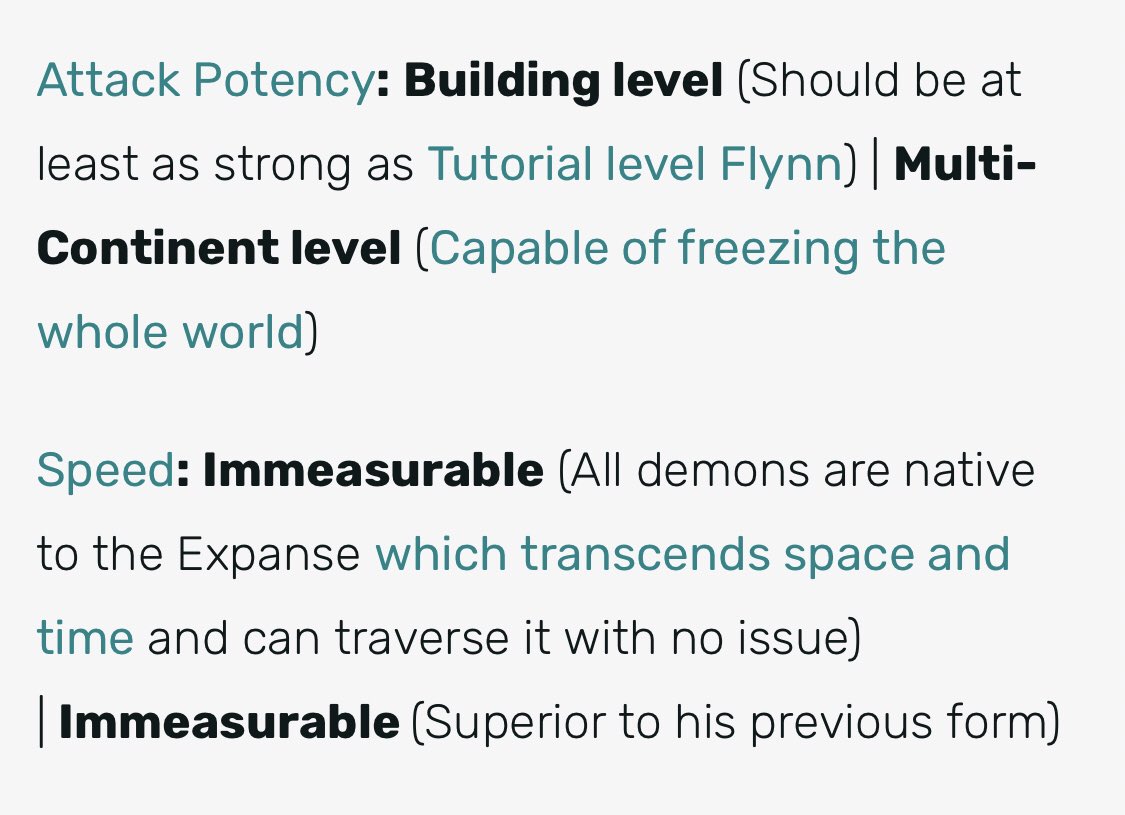
Attack potency, at its core, refers to the potential for an offensive action to achieve its intended goal. This goal can vary widely depending on the context. In cybersecurity, it might be the successful exploitation of a vulnerability to gain unauthorized access, disrupt services, or steal data. In gaming, it represents the damage or debilitating effect a character’s attack can inflict on an opponent. While the specific metrics might differ, the underlying principle remains: the capacity to cause a significant, undesirable outcome for the target.
The Spectrum of Offensive Capabilities
Attack potency is not a binary state; it exists on a spectrum. An attack might be highly potent, capable of overwhelming even sophisticated defenses with ease, or it might be relatively weak, requiring multiple successful attempts or specific conditions to have any significant impact. This spectrum is influenced by a multitude of factors, which we will explore in detail.
Beyond Raw Power: Contextual Effectiveness
It’s vital to recognize that attack potency isn’t solely about raw power or the magnitude of a potential impact. Context is paramount. An attack that is devastating in one scenario might be ineffective in another. For instance, a sophisticated zero-day exploit targeting a specific software version might be incredibly potent against an unpatched system but render useless against a system employing different architecture or security protocols. Similarly, in gaming, a powerful attack might be easily dodged or countered if the opponent has specific defenses or weaknesses. Therefore, a comprehensive understanding of attack potency requires an appreciation for the interplay between the offensive action, the target’s defenses, and the environment in which the interaction occurs.
Determinants of Attack Potency in Cybersecurity
In the domain of cybersecurity, attack potency is a complex interplay of several critical factors. These elements combine to determine how likely an attack is to succeed and the severity of its consequences. Understanding these determinants is fundamental for both offensive and defensive strategies.
Vulnerabilities and Exploits
The most direct contributor to an attack’s potency is the presence of exploitable vulnerabilities within a target system. These vulnerabilities are weaknesses in software, hardware, or configurations that an attacker can leverage. The potency of an exploit is directly tied to the severity of the vulnerability it targets. A critical vulnerability, such as a buffer overflow that allows arbitrary code execution, grants an attacker immense potency. Conversely, a minor vulnerability, like an information disclosure that reveals non-sensitive details, contributes less to an attack’s overall potency.
Severity of Vulnerabilities
Vulnerabilities are typically categorized by their severity, often using systems like the Common Vulnerability Scoring System (CVSS). CVSS assigns scores based on factors such as attack vector (how the vulnerability can be exploited), complexity, privileges required, user interaction needed, and the impact on confidentiality, integrity, and availability. A higher CVSS score generally correlates with a more potent vulnerability and, consequently, a more potent attack. For example, a vulnerability that allows remote code execution without user interaction (CVSS score 10.0) is significantly more potent than one that requires physical access and a low-privilege user (CVSS score 2.0).
Exploit Maturity and Reliability
Beyond the vulnerability itself, the maturity and reliability of the exploit are crucial. An exploit that is well-tested, stable, and has a high success rate is far more potent than a proof-of-concept exploit that is prone to crashing or failing. The development of sophisticated exploit kits, often by advanced persistent threat (APT) groups, significantly enhances the potency of attacks by providing attackers with reliable tools that require less individual technical expertise.
Attack Vector and Method
The way an attack is delivered, the attack vector, also plays a significant role in its potency. Some attack vectors are inherently more potent due to their stealth or ability to bypass common defenses.
Network-Based Attacks
Attacks that can be launched remotely over a network, such as SQL injection, cross-site scripting (XSS), or denial-of-service (DoS) attacks, often possess high potency because they can target a broad range of systems without requiring direct physical access. The ease of access and the potential for widespread impact contribute to their potency.
Social Engineering and Phishing
While not purely technical, social engineering techniques, particularly phishing and spear-phishing, can be incredibly potent when combined with technical exploits. By tricking users into divulging credentials or executing malicious code, attackers bypass many technical security controls. The potency here lies in human psychology and the ability to exploit trust and deception.
Insider Threats
Attacks originating from within an organization, by disgruntled employees or compromised accounts, can be particularly potent. Insiders often have legitimate access to systems and data, allowing them to operate with a higher degree of stealth and to target critical assets without triggering many external security alerts.
Payload and Malicious Functionality
The actual malicious code or script that is delivered by an exploit, known as the payload, directly dictates the potential damage and therefore the attack’s potency. The capabilities of the payload determine what an attacker can achieve once a system is compromised.
Data Exfiltration and Destruction
Payloads designed for stealing sensitive data or irrevocably destroying data are inherently highly potent. The loss of confidential information or critical operational data can have devastating financial and reputational consequences for an organization.
Ransomware and Extortion
Ransomware, which encrypts a victim’s data and demands payment for its decryption, is a prime example of a highly potent attack. The threat of permanent data loss and the disruption to business operations create immense pressure on victims, making this a financially lucrative and strategically potent form of attack.
Privilege Escalation and Lateral Movement
Payloads that enable attackers to escalate their privileges within a compromised system or move laterally to other connected systems are crucial for increasing an attack’s overall potency. These actions allow an attacker to gain deeper access and control, expanding their reach and the potential impact of their intrusion.
Attack Potency in Gaming and Virtual Worlds
The concept of attack potency extends beyond cybersecurity and finds a prominent place in the realm of video games, particularly in genres like RPGs (Role-Playing Games), MOBAs (Multiplayer Online Battle Arenas), and fighting games. Here, attack potency refers to the raw damage output or debilitating effect of a character’s offensive abilities.
Damage Metrics and Calculations
In games, attack potency is often quantifiable through numerical values. This can manifest as:
Base Damage
The fundamental damage value of an attack before any modifiers are applied. This is the raw power of the strike.

Attack Power Scaling
Many games feature character statistics, such as “Attack Power” or “Strength,” which directly influence the damage an attack deals. The higher a character’s relevant stat, the more potent their attacks become. This creates a progression system where investing in offensive capabilities directly enhances attack potency.
Damage Multipliers and Buffs
Various game mechanics can further increase attack potency. These include temporary buffs that boost damage, critical hit chances that inflict significantly more damage, and special attack multipliers that are activated under specific conditions. For example, hitting an enemy’s weak point or exploiting a status effect could trigger a damage multiplier, dramatically increasing the potency of a single blow.
Status Effects and Debilitations
Attack potency isn’t solely about direct damage. Some attacks are potent because they inflict status effects or debilitating conditions on opponents, hindering their ability to fight back effectively.
Crowd Control Effects
Attacks that can stun, silence, root, or slow down enemies are highly potent as they disrupt an opponent’s actions and create opportunities for allies. These “crowd control” effects can dictate the flow of a battle and are often considered as potent as direct damage in strategic gameplay.
Damage Over Time (DoT)
Attacks that apply a lingering effect, causing damage over a period, can also be very potent, especially in combination with other attacks. While the initial impact might be low, the cumulative damage can be significant, and it forces opponents to expend resources on healing or cleansing the effect.
Defense Reduction and Vulnerability
Some attacks are potent because they reduce an opponent’s defenses or make them more vulnerable to subsequent attacks. These debuffs amplify the potency of an ally’s subsequent offensive actions, making them crucial for coordinated team strategies.
Strategic Implications in Gameplay
Understanding and manipulating attack potency is fundamental to success in many games. Players constantly assess the attack potency of their own abilities and those of their opponents to make informed strategic decisions.
Countering and Defense
Players must learn to identify and counter high-potency attacks. This might involve dodging, blocking, using defensive abilities, or interrupting an opponent’s charge-up sequence. The effectiveness of a defense is often measured by its ability to mitigate or negate incoming attack potency.
Resource Management
Many potent attacks consume valuable resources, such as mana, energy, or cooldown timers. Players must strategically decide when to unleash their most potent abilities to maximize their impact, balancing the immediate gain with the cost of expending these resources.
Team Synergy and Composition
In team-based games, the combined attack potency of a team is crucial. Players choose characters and abilities that synergize to create powerful offensive combinations, overwhelming opponents through sheer force or by exploiting vulnerabilities more effectively.
The Evolving Landscape of Attack Potency
The nature and significance of attack potency are constantly evolving, driven by rapid advancements in technology and evolving adversarial tactics. Both in cybersecurity and gaming, the pursuit of greater offensive capabilities and more robust defenses fuels continuous innovation, shaping how we define and measure the effectiveness of an attack.
Cybersecurity Advancements
In cybersecurity, the increasing sophistication of threats, coupled with advancements in defensive technologies, creates a dynamic arms race.
AI and Machine Learning in Attacks
The integration of Artificial Intelligence (AI) and Machine Learning (ML) is starting to impact attack potency. AI can be used to automate vulnerability discovery, craft more sophisticated phishing campaigns, and even develop adaptive malware that can evade detection. This potentially increases the potency of automated attacks, making them more effective and harder to counter with traditional signature-based defenses.
Cloud and IoT Vulnerabilities
The expansion of cloud computing and the Internet of Things (IoT) introduces new attack surfaces and novel vulnerabilities. Exploiting these often interconnected systems can grant attackers significant leverage and potency, as a compromise in one area can ripple through an entire ecosystem. The distributed nature of these environments presents unique challenges in assessing and mitigating attack potency.
Quantum Computing and Future Threats
Looking further ahead, the advent of quantum computing poses a theoretical threat to current encryption standards. While still in its nascent stages, the potential for quantum computers to break widely used cryptographic algorithms could drastically increase the potency of data interception and decryption attacks, forcing a fundamental shift in digital security paradigms.
Gaming Innovation
In the gaming world, developers continuously introduce new mechanics and balance existing ones to keep gameplay fresh and challenging.
Procedural Generation and Dynamic Environments
The use of procedural generation and increasingly dynamic game environments can alter the effectiveness of attacks. Environments that change during gameplay, or are generated uniquely for each session, can require players to constantly adapt their strategies and reassess the potency of their chosen attacks based on the current situation.
Player-Driven Content and Modding
Player-created content and modifications can introduce entirely new offensive capabilities, sometimes with unintended consequences for game balance. The ability for players to develop and share custom attacks or modify existing ones can lead to unexpected shifts in attack potency meta-games, requiring developers to monitor and adjust.
Evolving Esports and Competitive Play
The growth of esports has placed a significant emphasis on competitive balance and the precise tuning of offensive and defensive capabilities. The constant scrutiny from professional players and analysts leads to frequent updates and patches aimed at fine-tuning attack potency to ensure fair and engaging competition. This continuous refinement ensures that the concept of attack potency remains a central focus in game design.
In conclusion, attack potency is a versatile and significant concept that permeates critical aspects of our digital lives. Whether safeguarding against malicious actors in the cybersecurity landscape or strategizing for victory in virtual arenas, understanding the multifaceted nature of attack potency—its determinants, its context, and its evolving trajectory—is essential for informed decision-making and effective action. As technology continues to advance, so too will the complexity and implications of attack potency, demanding ongoing vigilance and adaptation from all involved.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.