In the rapidly evolving landscape of digital file sharing, the methods we use to distribute and acquire data have undergone significant transformations. For anyone who has ventured into the world of peer-to-peer (P2P) networking, the term “Magnet link” is likely familiar, yet its underlying mechanics often remain a mystery to the average user. Traditionally, downloading files via BitTorrent required the use of a “.torrent” file—a small document that acted as a roadmap for your client. However, the industry has largely shifted toward Magnet links.
Understanding what a Magnet link is, how it functions, and why it has become the standard in decentralized file sharing is essential for anyone interested in modern technology and digital security. This guide explores the technical architecture of Magnet links, their advantages over traditional methods, and the security protocols necessary for safe usage.
The Fundamentals of Magnet Links and Their Role in P2P
To understand a Magnet link, one must first understand the BitTorrent protocol. At its core, BitTorrent is a communication protocol for P2P file sharing that is used to distribute data and electronic files over the Internet in a decentralized manner. Unlike traditional downloads, where you fetch a file from a single server, BitTorrent allows you to download pieces of a file from multiple users (peers) simultaneously.
Defining the Magnet Link
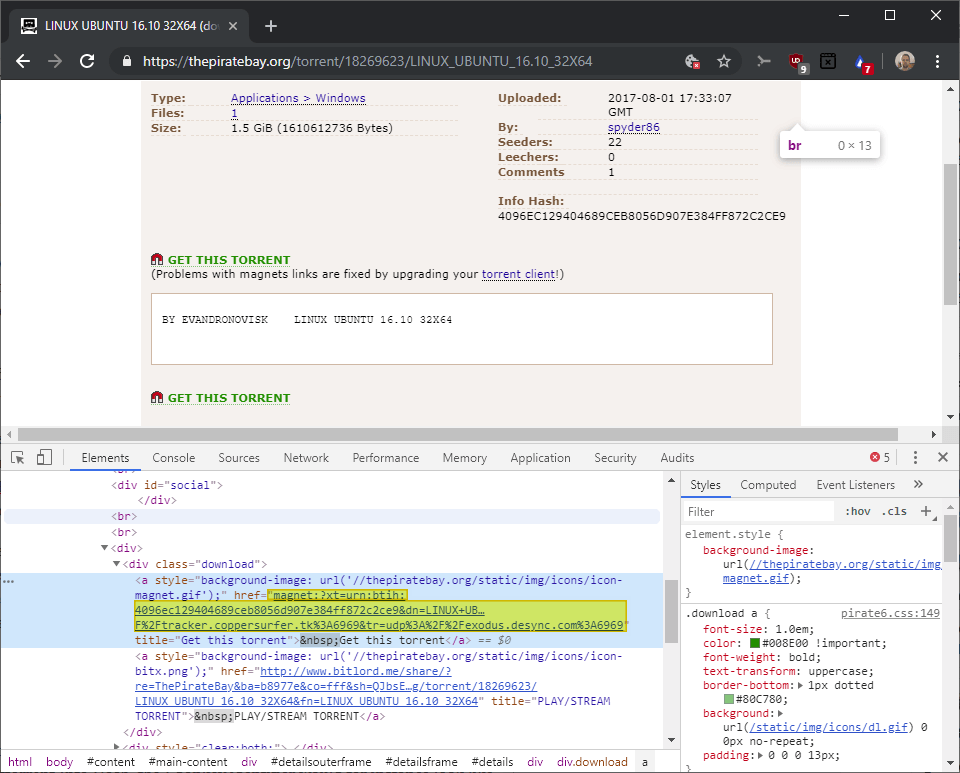
A Magnet link is a type of hyperlink that identifies files by their content—specifically, by a cryptographic hash—rather than by their location on a specific server or computer. In technical terms, it is a Uniform Resource Identifier (URI). While a standard URL (Uniform Resource Locator) tells your browser where to find a file (e.g., https://website.com/file.zip), a Magnet link tells your software what the file is, regardless of where it is hosted.
The structure of a Magnet link typically starts with magnet:?xt=urn:btih:. The “xt” stands for “exact topic,” and “btih” stands for “BitTorrent Info Hash.” This long string of alphanumeric characters is a unique fingerprint of the data you are trying to download.
How Magnet Links Differ from .torrent Files
For years, the standard way to initiate a BitTorrent download was to download a .torrent file from a website and open it in a client like qBittorrent or Transmission. This file contained “metadata” about the files you wanted to download and the address of a “tracker”—a central server that coordinated the connection between peers.
Magnet links eliminate the need for this middleman file. Instead of downloading a document to tell your client where the tracker is, the Magnet link provides the hash directly. Your client then uses this hash to find other users who have the file. This transition from “location-based” to “content-based” identification is the defining characteristic of the Magnet link.
The Technology Behind the Magic: DHT and PEX
The shift from torrent files to Magnet links was made possible by advancements in how P2P networks organize themselves. Because Magnet links often bypass centralized trackers, the network needs a way to find peers autonomously. This is achieved through two primary technologies: Distributed Hash Tables (DHT) and Peer Exchange (PEX).
Distributed Hash Tables (DHT)
DHT is essentially a decentralized “phonebook” for the BitTorrent network. In a traditional setup, the tracker server kept a list of every user’s IP address and the files they were sharing. If the tracker went offline, the “swarm” (the group of users sharing a file) would often collapse.
With DHT, every user in the network acts as a mini-tracker. When you click a Magnet link, your client looks at the unique hash and asks its immediate neighbors if they know who has that specific file. This request ripples through the network until it finds peers who are seeding the data. This “trackerless” system makes the network incredibly resilient, as there is no single point of failure.
Peer Exchange (PEX)
While DHT helps you find the first few peers, Peer Exchange (PEX) helps you expand that list rapidly. Once your client has connected to a few peers, those peers share their own lists of known users with you. This creates a high-speed, self-optimizing web of connections. By combining DHT and PEX, Magnet links allow for a fully decentralized experience where a central website or server is no longer strictly necessary once the link has been shared.
The Advantages of Using Magnet Links in Modern Computing

The tech community has embraced Magnet links not just because they are “new,” but because they offer tangible benefits in terms of infrastructure, speed of access, and longevity.
Serverless Resilience and Reduced Bandwidth
One of the biggest hurdles for torrent indexing websites is the massive amount of bandwidth required to host and serve millions of .torrent files. Magnet links are just snippets of text. They can be shared via email, instant messages, or even written on a piece of paper. For website operators, this reduces server load and makes it much harder for entities to take down content by simply removing a file from a server.
Furthermore, because Magnet links don’t rely on a single tracker, they are much harder to censor. If a central tracker is blocked by an Internet Service Provider (ISP), the Magnet link can still find peers through DHT, ensuring that the data remains accessible as long as at least one person in the world is sharing it.
Improved User Experience and “One-Click” Functionality
From a user-experience perspective, Magnet links are significantly more convenient. Instead of downloading a file, locating it in your “Downloads” folder, and double-clicking it to open your torrent client, you simply click the link. Most modern browsers automatically recognize the magnet: protocol and prompt your torrent client to open instantly. This “one-click” workflow mimics the ease of standard web downloads while maintaining the power of P2P distribution.
Security Considerations and Digital Best Practices
While the technology behind Magnet links is a masterpiece of decentralized engineering, it is not without risks. Users interacting with P2P networks must remain vigilant about digital security and privacy.
Avoiding Malicious Links and Metadata Spoofing
Because Magnet links are just strings of text, it can be difficult for a human to tell what they are about to download just by looking at the URI. While most clients will show a “metadata retrieval” screen before the download begins—allowing you to see the file names and sizes—malicious actors can still attempt to distribute malware by naming files deceptively.
It is vital to only source Magnet links from reputable communities and verified contributors. Additionally, because Magnet links rely on DHT, your IP address is essentially broadcast to the network as you search for peers. This lack of anonymity can be a concern for users in regions with strict data monitoring.
The Essential Role of VPNs in P2P Sharing
To mitigate the privacy risks associated with Magnet links, the use of a Virtual Private Network (VPN) has become a standard recommendation in the tech community. A VPN masks your actual IP address by routing your traffic through an encrypted tunnel to a remote server.
When you use a Magnet link while connected to a VPN, other peers in the swarm see the IP address of the VPN server rather than your home connection. This prevents third parties from tracking your download habits and protects you from potential “man-in-the-middle” attacks that can occur on open P2P networks.
The Future of Decentralized File Sharing
The evolution from .torrent files to Magnet links was a major step toward a truly decentralized internet. However, the technology continues to advance. We are now seeing the integration of these concepts into broader “Web3” and decentralized web projects.
Beyond Torrents: IPFS and the Permanent Web
The logic behind Magnet links—identifying a file by what it is rather than where it is—is the foundation of the InterPlanetary File System (IPFS). IPFS aims to replace the traditional HTTP protocol with a content-addressed system that makes the web faster, safer, and more open. In this ecosystem, the concept of a “link” becomes even more powerful, potentially allowing for a web where pages never go 404 (File Not Found) because they are stored across a global network of nodes.
BitTorrent 2.0 and Enhanced Hashing
The protocol is also receiving its own upgrades. BitTorrent v2 introduces the use of SHA-256 hashing (an upgrade over the older SHA-1), which provides even greater security against “hash collisions” and allows for per-file hashing within a single Magnet link. This means that if you are downloading a large collection of files, your client can verify the integrity of each individual file more efficiently.
In conclusion, Magnet links represent a sophisticated shift in how we think about data ownership and distribution. By moving away from centralized servers and toward a content-addressed, peer-to-peer model, they have made the internet more resilient and efficient. Whether you are a developer looking at the future of decentralized apps or a casual user wanting a faster way to share files, understanding the “Magnet” is your key to mastering the modern digital landscape.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.