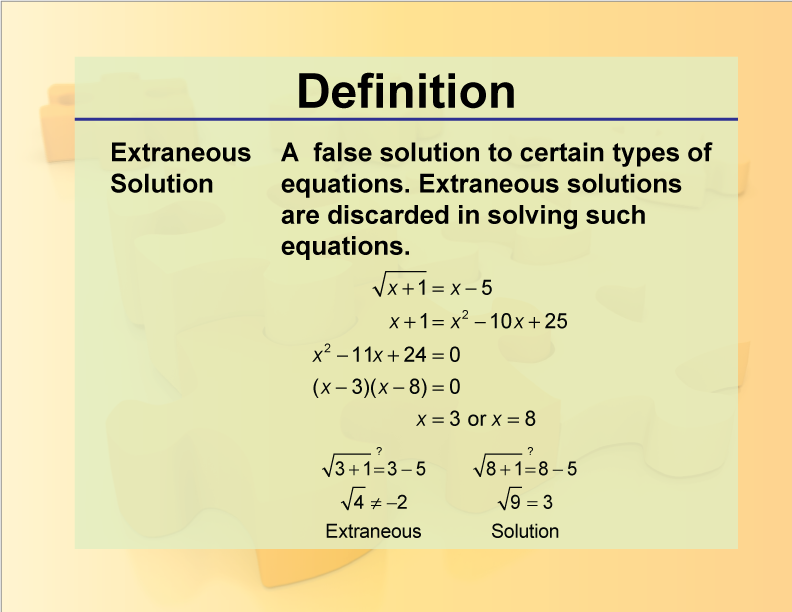
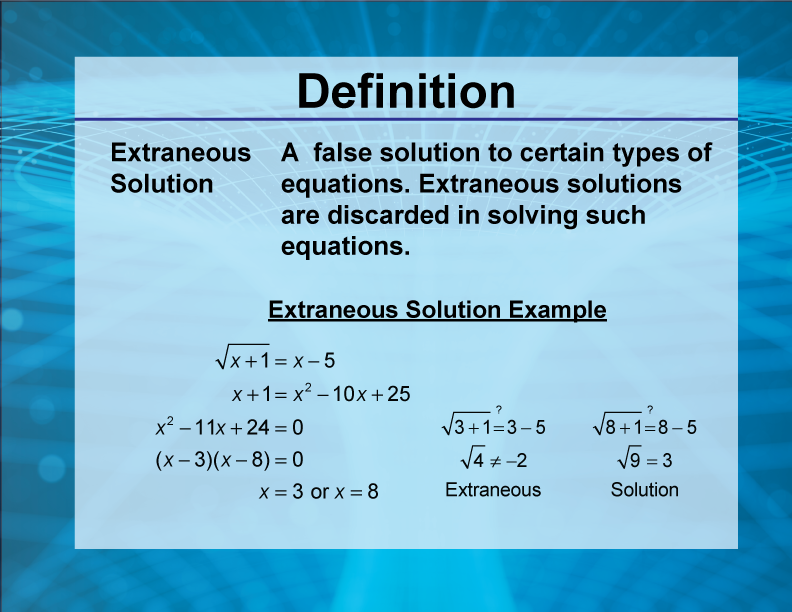
In the world of mathematics, an extraneous solution is a root that emerges during the process of solving an equation but does not actually satisfy the original problem. It is a mathematical “ghost”—a logical artifact that appears valid on paper but fails when tested against the initial constraints. While this concept is a staple of high school algebra, it has profound implications in the world of technology, software development, and algorithmic design.
In technology, an extraneous solution manifests as a logical error where a system produces an output that seems correct within a specific function but creates a failure, a security vulnerability, or a resource leak when integrated into the broader architecture. As we move toward increasingly complex AI-driven systems and automated software engineering, understanding and identifying these “logical ghosts” is critical for building robust, secure, and efficient digital tools.
The Core Concept: Defining Extraneous Solutions in a Digital Context
To understand extraneous solutions in technology, we must first look at why they happen in logic. They typically occur when a mathematical operation is performed that is not “one-to-one.” For instance, squaring both sides of an equation can introduce a negative-turned-positive value that wasn’t there originally.
From Algebra to Algorithms
In software development, we perform “logical operations” on data constantly. When we transform data—converting a string to an integer, normalizing a database, or mapping a JSON object to a class—we are performing the digital equivalent of algebraic manipulation. An extraneous solution in tech occurs when a transformation produces a result that passes a local validation check but violates a global system constraint.
For example, a search algorithm might find a “solution” (a data point) that fits the search parameters provided by the user, but because of a logic error in how the database index was built, that data point points to a null reference. The solution is “extraneous” because it exists within the logic of the search function but does not exist in the reality of the database.
Why Logic Fails: The “Shadow Solution” Phenomenon
In high-level programming languages, we often rely on abstractions to simplify complex tasks. These abstractions can hide the “shadow solutions” that emerge from edge cases. A shadow solution is an execution path that the developer did not intend for the program to take, but which the program considers valid based on its written rules.
In tech, these often arise from “lossy” operations. Just as squaring a number loses the information of its original sign (positive or negative), a poorly designed data filter might lose the context of a user’s permission level, resulting in an extraneous solution where the system “correctly” calculates a result that the user should not have been able to access.
Common Scenarios Where Extraneous Solutions Occur in Development
The emergence of extraneous solutions is rarely the result of a single catastrophic failure. Instead, they are usually the byproduct of subtle logic gaps in how software handles state and data types.
Division by Zero and Null Pointers
One of the most common ways an extraneous solution enters a tech system is through undefined behavior. If a developer writes a function that divides a variable by a user-inputted value, and that value is zero, many systems will return an error. However, in more complex environments—such as low-level graphics rendering or specific financial algorithms—the system might attempt to resolve this through “wrapping” or “clamping” values.
When a system forces an undefined value into a defined one to keep the program running, it creates an extraneous solution. The resulting data point is a fabrication of the error-handling logic, not a true representation of the input data.
Non-Linear Operations in Data Processing
In machine learning and AI tool development, non-linear operations are the standard. When we train a model, we are essentially asking it to find the “best fit” solution for a massive set of equations. Sometimes, the model finds a local minimum—a solution that looks perfect according to the loss function but fails miserably when applied to real-world data.
This is the ultimate tech-centric extraneous solution: the model has “solved” the training data, but the solution is an artifact of the training process itself (overfitting), not a functional rule that applies to the real world.

Floating Point Inaccuracies
In fintech software and high-performance computing, floating-point arithmetic is a notorious source of extraneous errors. Because computers represent decimal numbers in binary, certain values cannot be represented with perfect precision. Over millions of calculations, these tiny rounding errors can compound into a “solution” that is off by a significant margin. If a financial app calculates a balance that is mathematically possible within its own rounding logic but doesn’t match the actual transactional ledger, it has produced an extraneous solution.
The Impact on System Integrity and Digital Security
Extraneous solutions are not just academic curiosities; they are a primary source of technical debt and security vulnerabilities. When a system accepts a solution that it shouldn’t, it opens the door for exploitation.
Vulnerabilities Created by Logic Errors
Many of the most famous hacks in history were essentially the exploitation of extraneous solutions. Consider a “buffer overflow” or an “integer overflow.” In these cases, a hacker provides an input that the system processes mathematically. The system reaches a state—a “solution”—where the memory buffer is full. Instead of stopping, the logic allows the data to “overflow” into the next memory address.
The computer sees this as a valid execution step, but it is an extraneous one. It shouldn’t exist within the context of a secure application. By forcing the system into these unintended states, attackers can execute arbitrary code.
Resource Leaks and Process Deadlocks
In cloud computing and infrastructure management, extraneous solutions can lead to “ghost processes.” This happens when a management script thinks a task has been completed and moves on to the next one, but the original task is actually stuck in a loop or has failed to release its memory. The management script’s “solution” (marking the task as done) is extraneous because it doesn’t reflect the actual state of the server. Over time, these ghost processes accumulate, leading to system crashes and inflated cloud costs.
Debugging and Verification Strategies
Identifying an extraneous solution is significantly harder than identifying a standard bug. A bug usually causes a crash; an extraneous solution causes the system to keep running, but incorrectly.
Unit Testing for Edge Cases
The first line of defense is rigorous unit testing, specifically focused on “boundary value analysis.” Developers must test not just the expected inputs, but the inputs that define the boundaries of the logic. By testing the “square root of a negative” or the “division by zero” equivalent in their code, they can ensure that extraneous solutions are caught before they reach production.
Formal Verification Methods
In mission-critical technology, such as aerospace software or medical device firmware, engineers use “formal verification.” This involves using mathematical proofs to ensure that the code is logically sound. Unlike standard testing, which checks if the code works for some inputs, formal verification uses logic engines to prove that the code works for all possible inputs. This effectively eliminates the possibility of an extraneous solution ever arising.
Using AI Debugging Tools to Identify Logical Ghosts
Modern AI tools and LLM-based coding assistants are becoming adept at spotting these logical fallacies. By analyzing code patterns, these tools can flag “unreachable code” or “illogical comparisons” that humans might miss. For instance, an AI might notice that a developer has written a conditional statement that can never be true, or one that produces a result that will be immediately overwritten, pointing toward a potential extraneous logic path.
Future-Proofing Code Against Logical Redundancy
As software moves toward more modular and microservice-oriented architectures, the risk of extraneous solutions increases. When dozens of different services communicate, the “output” of one is the “input” of another. If Service A produces an extraneous solution, Service B will treat it as gospel, compounding the error across the entire ecosystem.
Type Safety and Functional Programming
One of the best ways to prevent extraneous solutions is to use “strongly typed” languages (like Rust or TypeScript) and functional programming principles. These methodologies restrict the types of operations that can be performed, making it much harder to perform a “lossy” operation that would create an extraneous result. In functional programming, functions are “pure,” meaning they always produce the same output for the same input and have no side effects, which dramatically reduces the chance of logical artifacts.
The Role of Robust Exception Handling
Finally, technology must be built with the assumption that extraneous solutions will happen. This is where robust exception handling comes in. Rather than letting a system guess what to do when it encounters an illogical state, it should be programmed to “fail fast.” By crashing or throwing a clear error as soon as a solution appears that doesn’t fit the original parameters, the system prevents the extraneous solution from propagating and causing deeper, more expensive damage.
In conclusion, an extraneous solution in technology is a reminder that logic is only as good as the constraints we place upon it. Whether we are building simple mobile apps or complex AI models, our goal as creators is to ensure that every result produced by our systems is not just a mathematical possibility, but a valid, useful, and secure reality. Understanding the “extraneous” allows us to refine the “essential.”
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.