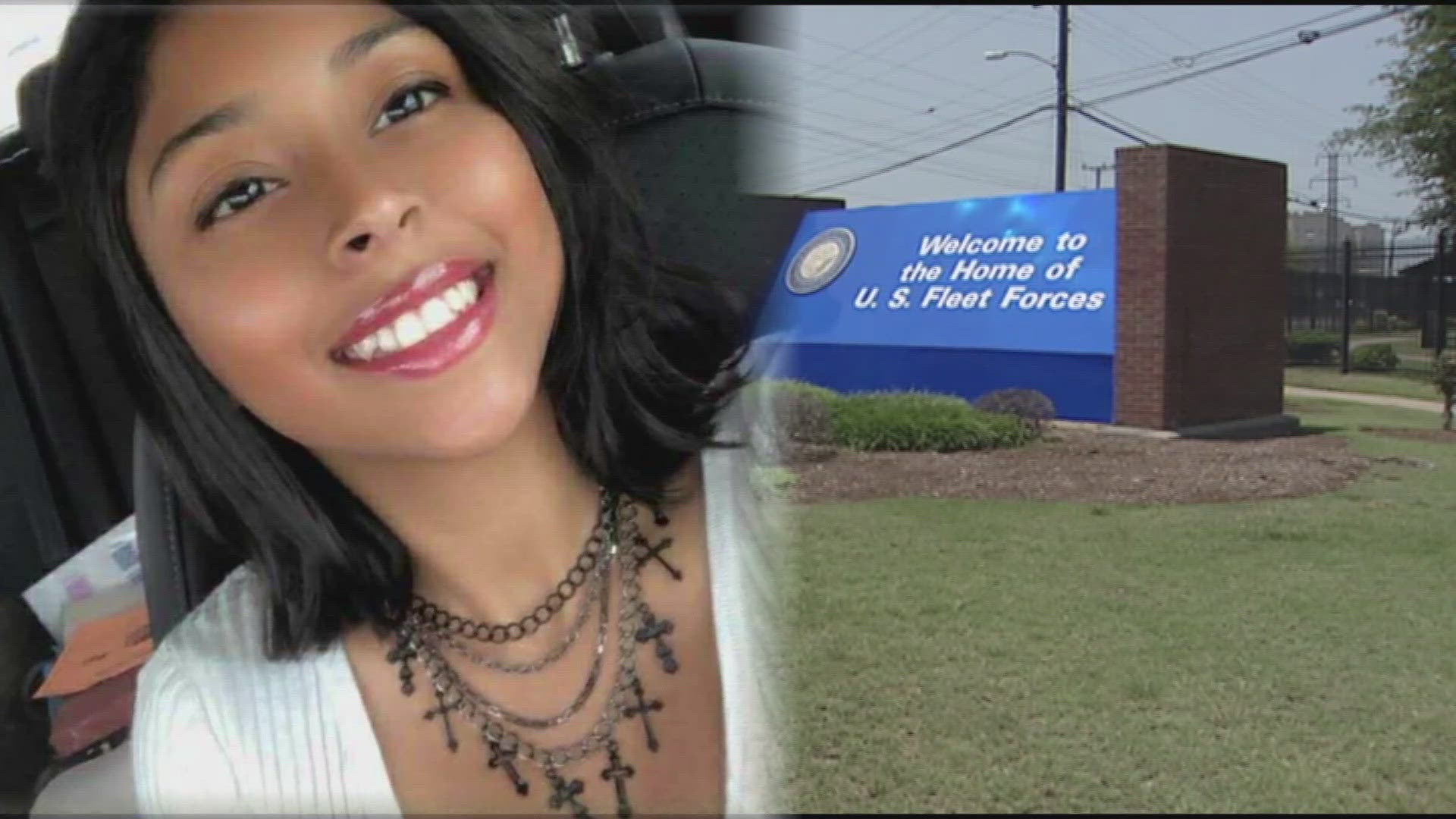
The phrase “what happened to Angelina Resendiz” has become more than just a query about a missing person; it has evolved into a case study on how technology, social media algorithms, and digital forensics intersect in the modern age. In an era where every individual leaves behind a complex trail of data, the disappearance or mystery surrounding an individual quickly transitions from a local police matter to a global digital investigation. Understanding the technical infrastructure behind such searches provides deep insight into how we monitor, find, and protect individuals in the 21st century.

The Evolution of Digital Investigations and OSINT
When a case like that of Angelina Resendiz captures the public’s attention, the first line of defense—and often the primary source of leads—is Open Source Intelligence (OSINT). In the past, investigations relied on physical evidence and eyewitness testimony. Today, the digital landscape offers a much more granular view of a person’s final known movements and intentions.
OSINT: The New Frontier in Search and Rescue
OSINT refers to the collection and analysis of data gathered from open sources to produce actionable intelligence. In the context of investigating what happened to Angelina Resendiz, tech experts and “digital detectives” utilize specialized tools to scrape public data. This includes social media activity on platforms like TikTok, Instagram, and X (formerly Twitter), as well as public records and forum mentions.
Sophisticated OSINT tools can map out a person’s social graph—identifying who they interacted with most frequently and at what times. This technological approach allows investigators to bypass traditional bureaucratic hurdles, providing a real-time snapshot of an individual’s digital life. The challenge, however, lies in the sheer volume of data, necessitating advanced filtering algorithms to separate credible leads from digital “noise.”
Leveraging Geolocation and Metadata in Modern Forensics
Every photo uploaded and every “check-in” recorded carries a hidden layer of data known as EXIF (Exchangeable Image File Format) metadata. This data can reveal the exact GPS coordinates, the device used, and the precise timestamp of an event. For tech-focused investigators, reconstructing the timeline of Angelina Resendiz involves a meticulous analysis of this metadata.
Beyond public posts, the use of IP (Internet Protocol) tracking and cellular triangulation plays a pivotal role. When a mobile device pings a cell tower, it creates a geographical record. By analyzing the “handshake” between a smartphone and various towers, technicians can create a “heat map” of movement, providing a more accurate trajectory than physical sightings ever could.
Social Media as a Real-Time Tracking and Information Tool
The viral nature of the question “what happened to Angelina Resendiz” is a direct result of how social media platforms prioritize engagement. Technology has transformed the “missing person poster” into a dynamic, global broadcast. However, this transition brings both unprecedented power and significant technical challenges.
The Viral Nature of Missing Persons Algorithms
Platforms like TikTok and Instagram use recommendation engines that prioritize high-engagement content. When a case goes viral, the algorithm pushes the information to millions of users within hours. This “crowdsourced” investigation can lead to the rapid identification of sightings or the discovery of relevant digital footprints that might have been overlooked by local authorities.
From a tech perspective, this is a double-edged sword. While the reach is massive, the algorithm does not distinguish between fact and speculation. The “echo chamber” effect can lead to the spread of misinformation, which can inadvertently hinder professional digital forensic efforts. Developers are currently looking into “verified alert” tags that would allow tech platforms to prioritize official law enforcement data over speculative user-generated content.
Privacy vs. Public Safety: The Ethical Tech Dilemma
The search for Angelina Resendiz also highlights the ongoing debate regarding end-to-end encryption (E2EE). Many messaging apps, such as WhatsApp and Signal, encrypt data so that only the sender and receiver can read it. While this protects user privacy, it creates “digital dead ends” for investigators.
Tech companies face the difficult task of balancing the fundamental right to digital privacy with the need for law enforcement to access data in life-and-death situations. The technical solution often involves “warrant-compatible” access or the analysis of unencrypted backups stored in the cloud. How these companies manage this data often determines the speed at which a digital investigation can progress.
Data Integrity and the Preservation of Digital Evidence
In any investigation involving a digital trail, the integrity of the data is paramount. Once the question of “what happened” is raised, the race begins to preserve data before it is deleted, overwritten, or lost to the “bit rot” of the internet.
Recovery of Deleted Data from Cloud-Based Ecosystems
Even when a user or a third party attempts to erase a digital footprint, traces often remain. Cloud computing has changed the nature of data deletion. When a file is deleted from a device, it often persists in cloud backups or server-side caches for 30 to 90 days.
Digital forensic specialists use specialized software to perform “logical” and “physical” extractions of data. In the case of Angelina Resendiz, this would involve searching for “orphaned” data fragments—pieces of information that the operating system no longer recognizes as a file but that still exist on the storage medium. These fragments can often be reconstructed to reveal deleted messages, browsing history, or location logs.
The Role of Decentralized Data and Blockchain
Emerging technologies like blockchain are beginning to play a role in how we view digital identity and evidence. While not yet standard in missing persons cases, the concept of a decentralized, immutable ledger could eventually be used to verify the authenticity of digital evidence. In the future, “proof of life” or “proof of location” could be verified through secure, cryptographically signed data packets that cannot be tampered with by outside parties, providing a higher level of certainty in complex investigations.
AI and Predictive Analytics in Behavioral Tracking
The most cutting-edge aspect of modern technology in investigating disappearances involves Artificial Intelligence (AI) and Machine Learning (ML). These tools are moving beyond simple data collection and into the realm of predictive modeling.
Using Machine Learning to Model Human Patterns
AI can analyze years of an individual’s digital behavior—what time they usually log on, their common travel routes, and their typical language patterns—to establish a “behavioral baseline.” When a deviation from this baseline occurs, such as in the case of Angelina Resendiz, AI can highlight specific anomalies that human investigators might miss.
For instance, if a social media post is made that doesn’t match the user’s typical linguistic “fingerprint” (syntax, vocabulary, or emoji usage), an AI model can flag it as potentially fraudulent or coerced. This level of technical scrutiny is becoming a standard part of high-stakes digital forensics.
Facial Recognition and Surveillance Infrastructure
The integration of AI with public and private surveillance systems—such as Ring doorbells, city-wide CCTV, and automated license plate readers (ALPR)—creates a vast net of visual data. AI-powered facial recognition can scan thousands of hours of footage in minutes to find a match for a specific individual.
The technical challenge here is “interoperability”—getting different systems from different manufacturers to talk to one another. Tech startups are currently working on centralized platforms that allow law enforcement to request access to private camera streams (with owner consent) to create a seamless visual timeline during the critical first 24 hours of a disappearance.
The Future of Digital Safety and Personal Security Tech
As the public continues to follow the story of Angelina Resendiz, the tech industry is responding with new tools designed to prevent such mysteries from occurring in the first place.
Wearable Tech and Passive Safety Features
We are seeing a shift from “reactive” tech to “proactive” safety. Smartwatches and wearable devices now include features like “Fall Detection,” “Emergency SOS,” and “Check-in” timers. These devices can automatically transmit a user’s location and biometric data (like heart rate) to emergency contacts if a pre-set condition isn’t met. This creates an immediate digital alert, potentially shortening the window between an incident and an investigation.

Digital Legacies and the Right to Be Found
Finally, the concept of a “Digital Legacy” is evolving. Tech giants like Apple and Google now allow users to appoint “Legacy Contacts” who can access their data in the event of an emergency or death. This technical provision ensures that if an individual goes missing, their family has a legal and technical pathway to access the data that might explain what happened, bypassing the lengthy legal battles that have plagued past investigations.
In conclusion, the inquiry into “what happened to Angelina Resendiz” serves as a powerful reminder of our total immersion in the digital world. While technology presents challenges in terms of privacy and the spread of misinformation, it also provides an unprecedented suite of tools—from OSINT and metadata analysis to AI-driven predictive modeling—that offer the best hope for finding answers in an increasingly complex society. The digital trail never truly ends; it merely requires the right technological expertise to follow it to its conclusion.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.