In the ever-evolving landscape of technology, understanding specialized terminology is not just a matter of curiosity but a crucial component of effective engagement, problem-solving, and innovation. The word “occluded,” while seemingly simple, carries significant weight and diverse applications within the tech sphere. It refers to something being hidden, blocked, or obscured from view, often by something else. This concept permeates various technological domains, from the physical limitations of sensors and optical systems to the abstract challenges of data visibility and security. To truly grasp what “occluded” signifies in a tech context, we must delve into its manifestations across different areas, exploring its implications and the innovative ways the industry addresses it.
Occlusion in Sensing and Imaging: The Physical Barriers
One of the most direct and tangible applications of “occluded” in technology relates to sensors and imaging systems. These technologies are designed to perceive and interpret the physical world, and their effectiveness is directly impacted by anything that obstructs their line of sight or the signals they rely upon.
Line of Sight and Sensor Limitations
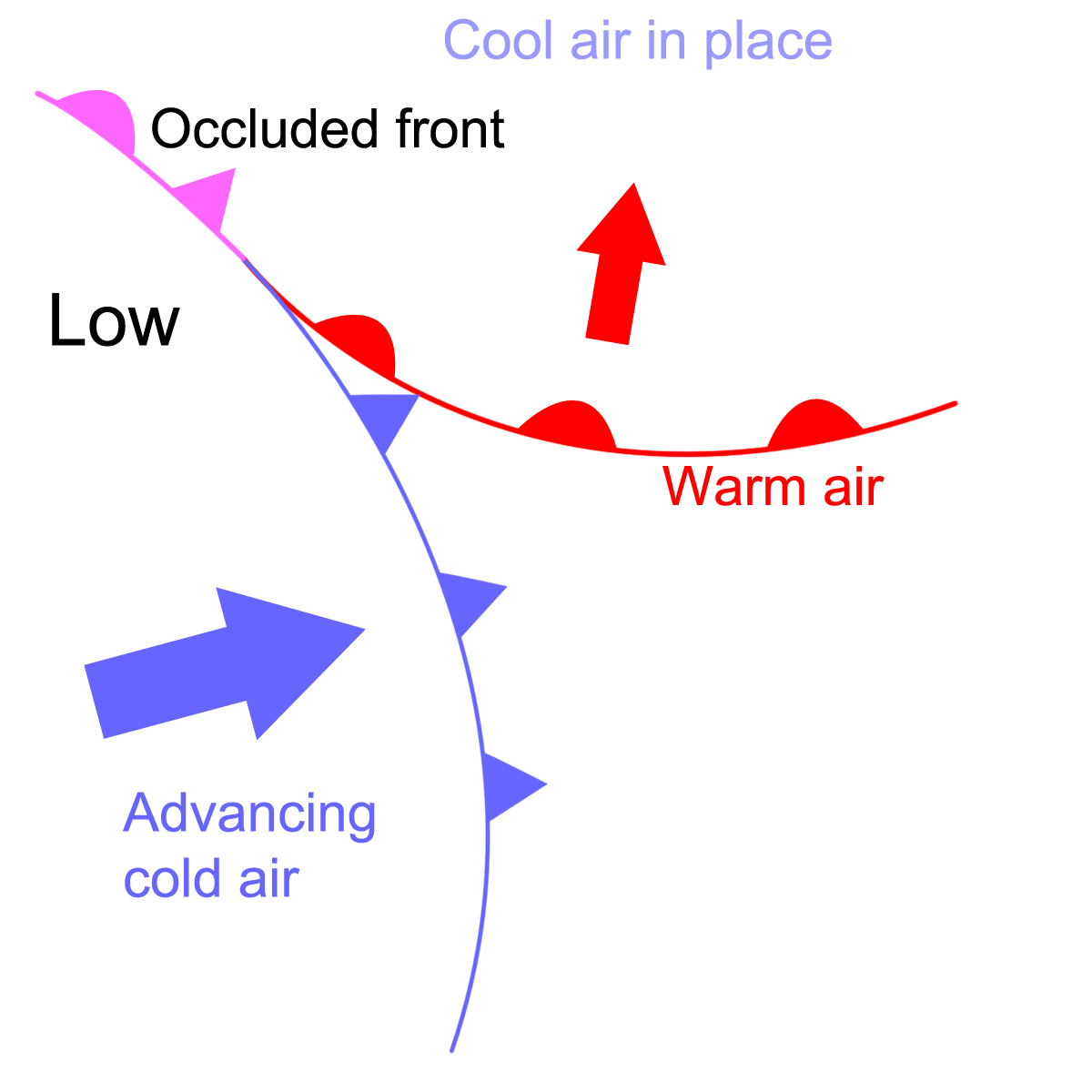
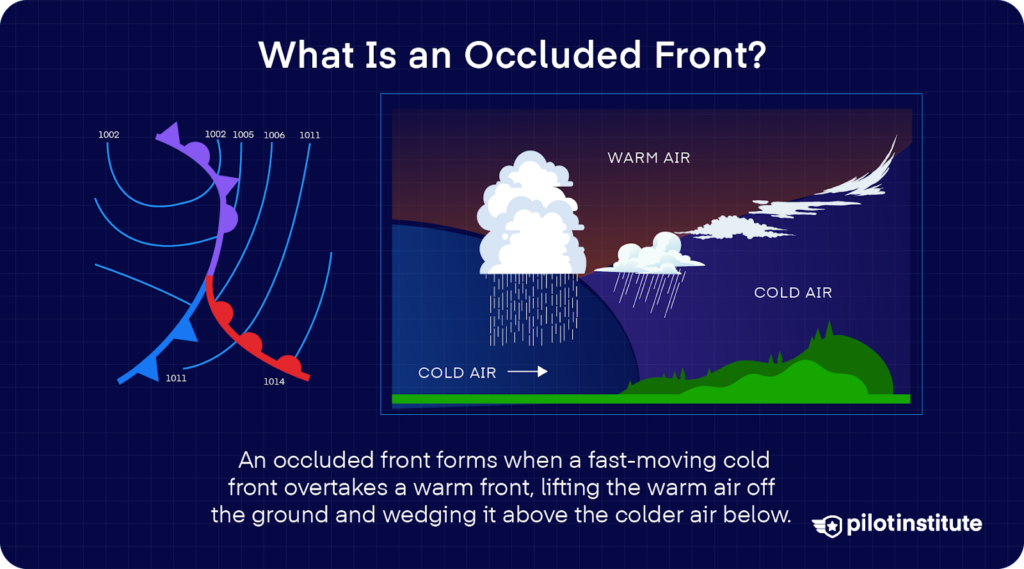
At its core, many sensors, particularly those relying on optical or radio wave communication, operate on the principle of a clear line of sight. A camera, for instance, needs an unobstructed view to capture an image. Similarly, radar systems require a direct path for their radio waves to bounce off an object and return. When an object comes between the sensor and its target, the target becomes occluded. This can range from a tree obscuring a drone’s view of a target location to a building blocking a Wi-Fi signal.
In autonomous systems, such as self-driving cars, occlusion is a critical challenge. LiDAR sensors, cameras, and radar systems must constantly be aware of what might be hidden behind other vehicles, buildings, or even dense foliage. A pedestrian stepping out from behind an occluding vehicle can represent a sudden and severe risk. Therefore, sophisticated algorithms are developed to predict potential occlusions and the objects that might emerge from them, often by inferring movement patterns and probabilities based on contextual information.
The Impact on Data Acquisition and Quality
Occlusion directly affects the quality and completeness of data acquired by technological systems. In computer vision, an occluded object means only a partial view is available, making recognition and tracking more difficult. This is a significant hurdle in applications like object detection for surveillance, where a partially visible face or vehicle is harder to identify accurately.
In medical imaging, occlusion can be a diagnostic challenge. For example, an ultrasound probe’s view of an internal organ might be occluded by bone or air. Advanced imaging techniques, such as those employing multiple sensor arrays or sophisticated signal processing, are employed to mitigate these effects, striving to reconstruct a comprehensive picture even in the presence of physical obstructions. The goal is to ensure that critical diagnostic information is not lost due to these physical limitations.
Occlusion in Digital Information and Security: The Abstract Barriers
Beyond the physical realm, the concept of occlusion extends into the digital and informational aspects of technology. Here, it often refers to the deliberate or unintentional hiding of data, access, or functionality, posing challenges for transparency, security, and user experience.
Data Obscurity and Privacy
In the context of data, “occluded” can refer to information that is deliberately hidden or made inaccessible, often for privacy or security reasons. This is fundamental to data encryption, where the underlying data is occluded (scrambled) into an unreadable format unless the correct decryption key is applied. The data itself is not gone; it is merely rendered imperceptible and unusable without the proper authorization.
Furthermore, privacy-preserving technologies often employ techniques that occlude personal information while still allowing for its use in aggregate or anonymized forms. For instance, differential privacy adds noise to datasets to obscure individual records while enabling statistical analysis. This is a delicate balance, ensuring that while individual identities are protected, valuable insights can still be derived.
Security Threats and Vulnerabilities
Occlusion can also be a tactic employed by malicious actors to hide their activities or gain unauthorized access. In cybersecurity, malware can attempt to occlude its presence on a system, hiding its processes from detection by antivirus software. This might involve techniques like rootkits or polymorphic code that constantly change their signature, making them difficult to “see” and identify.
Similarly, attackers might use proxies or VPNs to occlude their origin IP address, making it harder to trace their digital footprint. This form of informational occlusion is a constant cat-and-mouse game between security professionals and cybercriminals. Understanding how attackers attempt to occlude their tracks is vital for developing more robust defense mechanisms.
Overcoming Occlusion: Technological Solutions and Strategies
The challenges posed by occlusion, both physical and digital, have spurred significant innovation within the tech industry. Engineers and researchers are continuously developing sophisticated solutions to overcome these barriers and ensure the reliability and effectiveness of technological systems.
Advanced Imaging and Sensor Fusion
To combat physical occlusion, the development of advanced imaging techniques and sensor fusion plays a pivotal role. Multi-spectral cameras can capture information beyond the visible spectrum, potentially “seeing” through certain occlusions like fog or camouflage. Furthermore, combining data from multiple sensor types – such as cameras, LiDAR, and radar – through sensor fusion allows for a more comprehensive understanding of the environment. If one sensor is occluded or its data is compromised, the system can rely on information from others to maintain situational awareness.
In robotics and autonomous vehicles, techniques like simultaneous localization and mapping (SLAM) are enhanced with algorithms that predict and account for occlusions. By building a map of the environment and tracking the robot’s position within it, systems can infer the presence of objects that are temporarily out of view.
Data Augmentation and Reconstruction Techniques
For digital occlusion, particularly in machine learning and computer vision, data augmentation techniques are employed to simulate occluded scenarios during training. By artificially occluding parts of training images, models become more robust and better equipped to handle real-world situations where objects are partially obscured.
Furthermore, various reconstruction algorithms are used to infer missing data. In 3D reconstruction, for example, if a portion of a scanned object is occluded, algorithms can use surrounding data and geometric principles to predict and fill in the missing geometry. This is crucial for applications ranging from virtual reality to manufacturing.

Cryptographic and Security Protocols
In the realm of digital security, the development of sophisticated cryptographic algorithms and secure protocols is the primary means of combating informational occlusion by unauthorized parties. End-to-end encryption ensures that data is occluded during transit, accessible only to the intended recipients. Zero-knowledge proofs are another advanced technique that allows one party to prove the truth of a statement to another without revealing any information beyond the validity of the statement itself, thus occluding the underlying sensitive data.
Moreover, anomaly detection systems are designed to identify unusual patterns that might indicate occluded malicious activity. By constantly monitoring system behavior and flagging deviations from the norm, security professionals can uncover threats that are attempting to hide their presence.
In conclusion, the term “occluded” in technology signifies a fundamental challenge: that of obscured visibility, access, or understanding. Whether it’s a physical barrier impeding a sensor’s view, or an abstract layer hiding sensitive data, the implications are significant. The continuous pursuit of technological solutions – from advanced imaging and sensor fusion to robust encryption and intelligent data reconstruction – highlights the industry’s commitment to overcoming these limitations, ensuring that our increasingly complex technological systems can perceive, process, and protect information with greater accuracy, reliability, and security. Understanding what “occluded” means is not just about defining a word; it’s about appreciating the intricate efforts to unveil and manage the hidden facets of our digital and physical worlds.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.