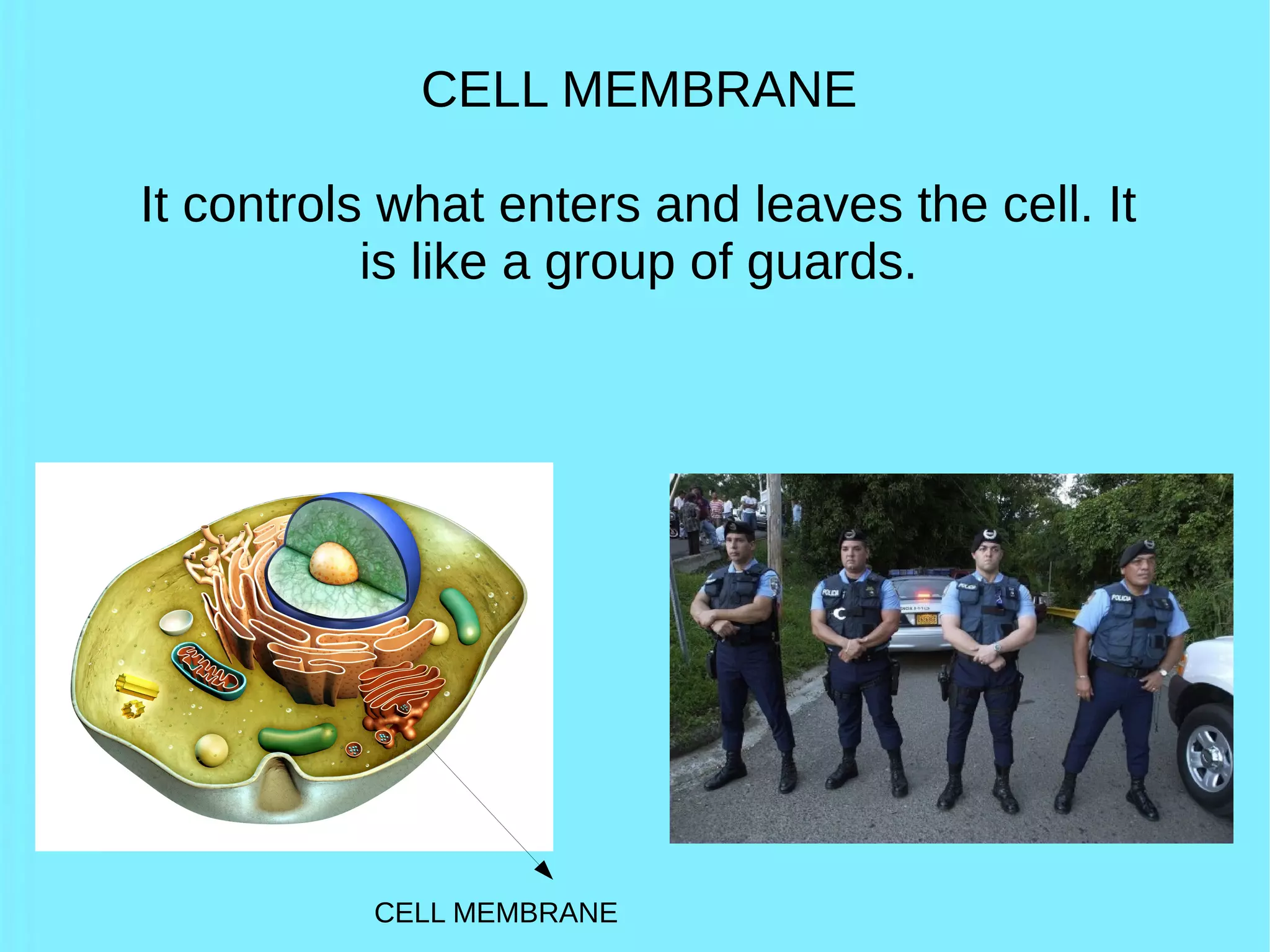
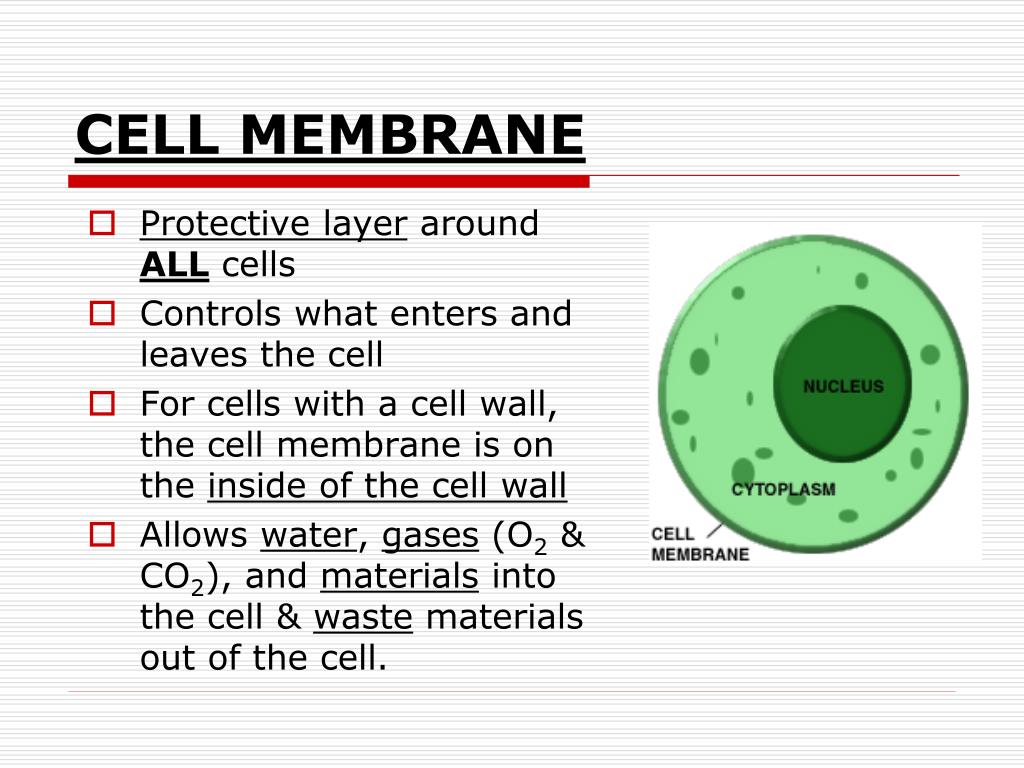
In the biological world, the plasma membrane serves as the ultimate gatekeeper, a semi-permeable barrier that ensures the survival of the organism by regulating the passage of nutrients and the expulsion of waste. In the rapidly evolving landscape of information technology, we have mirrored this biological necessity through a complex web of cybersecurity protocols, firewalls, and encryption layers. Just as a biological cell would perish if it allowed every molecule to enter, a digital “cell”—whether it be a single server, a cloud container, or an enterprise database—faces existential threats if it does not strictly control what enters and leaves its perimeter.

As we move deeper into the era of cloud computing, edge networks, and decentralized data, understanding the mechanisms of digital gatekeeping is no longer just the concern of IT specialists; it is a fundamental pillar of modern business continuity.
The Virtual Membrane: Redefining the Digital Perimeter
In the early days of computing, the “membrane” was simple: a rigid perimeter firewall that separated a trusted internal network from an untrusted external one. Today, the perimeter has dissolved. With the rise of remote work and the Internet of Things (IoT), the “cell” is now a fluid entity.
From Firewalls to Zero Trust Architecture
The traditional firewall was designed to monitor incoming and outgoing network traffic based on predetermined security rules. However, modern tech trends have shifted toward a “Zero Trust” model. In this framework, the digital membrane does not assume that anything inside the network is safe. Every request, whether it originates from outside or inside the system, must be authenticated, authorized, and continuously validated. This is the digital equivalent of a cell membrane using active transport—specifically identifying every “molecule” (data packet) before allowing it to pass.
The Role of API Gateways as Selective Barriers
In the world of software development, Application Programming Interfaces (APIs) are the primary channels through which different “cells” of code communicate. An API Gateway acts as the selective barrier for these interactions. It manages traffic, enforces rate limiting to prevent Distributed Denial of Service (DDoS) attacks, and ensures that only properly formatted and authorized requests can reach the internal microservices. Without an API gateway, the internal logic of a software application would be exposed to the “osmotic pressure” of the open internet, leading to inevitable crashes or data breaches.
Software-Defined Perimeters (SDP)
Software-Defined Perimeters provide an additional layer of control by hiding the infrastructure from the public eye. By using a “black cloud” approach, the SDP ensures that the “cell” is invisible to anyone who has not been pre-authenticated. This mimics the protective camouflage found in some biological systems, where the cell’s receptors are only visible to specific, compatible ligands.
Authentication and Authorization: The Biological Keys of Data Integrity
If the membrane is the physical barrier, then authentication and authorization are the chemical signals that determine entry. In a tech context, these processes ensure that data only moves when the correct “keys” are presented.
Identity and Access Management (IAM) as the Nucleus of Control
Identity and Access Management (IAM) is the central nervous system of digital security. It defines who has access to what resources and under what conditions. A robust IAM strategy uses Role-Based Access Control (RBAC) to ensure that users only have the minimum level of access necessary to perform their jobs. This concept of “Least Privilege” is vital; if a single cell component (a user account) is compromised, the damage is contained because the “gatekeeper” prevents the intruder from moving laterally through the system.
Multi-Factor Authentication (MFA): Adding Layers of Protection
Relying on a single password is like having a cell membrane with only one type of receptor—it is too easy to bypass. Multi-Factor Authentication (MFA) requires two or more pieces of evidence to grant access. This might include something the user knows (a password), something the user has (a physical token or smartphone), or something the user is (biometrics like fingerprints or facial recognition). By requiring multiple points of verification, organizations create a high-security “lock and key” system that is significantly harder to spoof.
Biometrics and the Evolution of Digital Identity
As AI and sensor technology advance, biometrics are becoming the gold standard for controlling digital entry. Facial recognition, iris scanning, and even behavioral biometrics (the way a person types or moves their mouse) provide a unique digital signature. This represents the ultimate convergence of biology and technology, where the physical characteristics of the human “cell” become the primary controller for digital access.
Deep Packet Inspection and Data Flow Monitoring
Controlling what enters a cell is only half the battle; controlling what leaves is equally critical for preventing data exfiltration and maintaining regulatory compliance.
Intrusion Detection Systems (IDS) and Prevention Systems (IPS)
To truly control a digital environment, IT administrators use Intrusion Detection and Prevention Systems. These tools perform “Deep Packet Inspection,” looking inside the data packets as they travel across the network. If a packet contains malicious code or displays “behavioral anomalies” that suggest a cyber-attack, the IPS can automatically block the traffic. This is the digital equivalent of an immune response, where the system identifies a pathogen and neutralizes it before it can cause systemic damage.
Managing Egress Traffic: Preventing Data Exfiltration
Many organizations focus heavily on what enters their network while ignoring what leaves it. Egress filtering is the practice of monitoring and limiting the data that exits a network. This is crucial for preventing “data exfiltration,” where a piece of malware or a disgruntled employee attempts to send sensitive information (like credit card numbers or intellectual property) to an external server. By strictly controlling the “exit ports,” a company ensures that its “cytoplasm”—its valuable internal data—stays within its own boundaries.
Data Loss Prevention (DLP) Tools
DLP tools are specialized software suites designed to identify and block the movement of sensitive information. They scan outgoing emails, cloud uploads, and even USB transfers. If a user attempts to send a document containing “Social Security Numbers” or “Internal Only” tags, the DLP system triggers an alert or blocks the transfer entirely. This provides a granular level of control over the “metabolic waste” versus the “vital proteins” of the digital organization.
The Future of Digital Boundaries: AI and Machine Learning
As cyber threats become more sophisticated, static rules are no longer sufficient to control the digital cell. The future of tech security lies in adaptive, intelligent systems that can learn and evolve in real-time.
Predictive Analysis in Traffic Management
Artificial Intelligence (AI) is now being used to predict threats before they materialize. By analyzing vast amounts of historical traffic data, AI can identify patterns that precede an attack. For example, if a specific type of data request usually precedes a ransomware injection, the AI can “tighten” the digital membrane in anticipation. This proactive stance shifts security from a reactive model to a predictive one, much like an organism developing antibodies after its first exposure to a virus.
Adaptive Security Postures for Dynamic Environments
In modern cloud environments, servers are created and destroyed in seconds (ephemeral infrastructure). Static security rules cannot keep up with this pace. Adaptive security uses machine learning to automatically adjust security policies based on the current environment. If a “cell” (a server) is under high load or is communicating with a new, unknown external node, the system can automatically increase the level of scrutiny required for any data passing through its gates.
The Role of Quantum Cryptography
Looking further ahead, quantum computing presents both a threat and a solution to digital gatekeeping. While quantum computers could potentially break current encryption methods (the “locks” on our digital gates), quantum cryptography offers a new way to secure data. Quantum Key Distribution (QKD) uses the laws of physics to ensure that any attempt to intercept or observe data as it enters or leaves a system will be immediately detected. This would create an unbreakable “membrane” for the most sensitive digital assets in the world.
In conclusion, the question of “what controls what enters and leaves a cell” finds its modern answer in the sophisticated layers of cybersecurity technology. From the initial barrier of the firewall to the intelligent scrutiny of AI-driven monitors, the digital membrane is a testament to our ability to replicate biological wisdom in the virtual world. By treating our data networks with the same rigor that nature treats the biological cell, we can ensure the integrity, safety, and longevity of our most vital digital ecosystems.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.