In the rapidly evolving world of cryptocurrency, security isn’t just a feature; it’s the bedrock upon which trust, financial stability, and brand reputation are built. For millions of users worldwide, Coinbase stands as a leading gateway to digital assets, making the question “What authenticator does Coinbase use?” not merely a technical query, but a critical concern for personal finance and digital security. This article delves deep into Coinbase’s multi-factor authentication (MFA) strategies, exploring the technologies they leverage, the implications for user safety, and how these choices reflect on the platform’s brand in the high-stakes realm of digital currency.
At its core, Coinbase, like all reputable financial platforms, understands that passwords alone are insufficient to protect valuable assets. The platform primarily relies on Time-Based One-Time Password (TOTP) applications for its strongest form of two-factor authentication (2FA), though it also supports SMS-based verification and, for advanced users, hardware security keys. Understanding these options, their strengths, weaknesses, and how to effectively implement them is paramount for anyone navigating the crypto landscape.
Understanding the “Why”: The Imperative of Multi-Factor Authentication in Crypto
The digital asset space is unique in its blend of innovation, decentralization, and inherent risks. Unlike traditional banking, where chargebacks and institutional safeguards often exist, cryptocurrency transactions are largely irreversible, placing a heightened emphasis on individual account security. This environment makes robust multi-factor authentication not just a recommendation, but an absolute necessity.
The Volatile Landscape of Digital Assets
The inherent value and pseudonymous nature of cryptocurrencies attract a wide array of threats. Phishing attacks, where malicious actors attempt to trick users into divulging their credentials on fake websites, are rampant. SIM swap attacks, where fraudsters gain control of a user’s mobile number to intercept SMS codes, pose a significant risk to accounts relying solely on phone-based verification. Malware, credential stuffing (using leaked passwords from other breaches), and various social engineering tactics constantly target crypto holders. The instantaneous and irreversible nature of blockchain transactions means that once funds are compromised, recovery is often impossible. This stark reality underscores why an extra layer of security beyond a mere password is indispensable for protecting one’s digital wealth.
Beyond Passwords: The Flaws of Single-Factor Security
For decades, passwords have been the primary gatekeepers of our digital lives. However, their limitations are increasingly evident. They can be guessed, stolen, phished, or brute-forced. A single compromised password can grant an attacker full access to an account, potentially leading to devastating financial losses, especially when substantial sums are stored on an exchange like Coinbase. Multi-factor authentication addresses this vulnerability by requiring at least two distinct forms of verification before granting access. These typically fall into three categories: something you know (like a password), something you have (a phone, a hardware key), and something you are (a fingerprint, facial scan). By requiring a combination of these factors, MFA dramatically increases the difficulty for unauthorized individuals to gain entry, even if they manage to acquire a user’s password.
Coinbase’s Commitment to Security: A Brand Imperative
For a platform like Coinbase, which handles billions in digital assets and serves millions of customers, security is not just a technical feature; it’s a core component of its brand strategy and a crucial driver of trust. In an industry often plagued by scams and hacks, a strong security posture differentiates Coinbase, reassuring users that their investments are protected. Any significant security breach could inflict catastrophic damage to the brand’s reputation, lead to a mass exodus of users, and incur substantial financial liabilities. Therefore, Coinbase invests heavily in security measures, including robust MFA options, sophisticated fraud detection systems, and dedicated security teams. By advocating for and integrating advanced authentication methods, Coinbase not only safeguards user assets but also reinforces its image as a reliable and responsible leader in the cryptocurrency space, directly impacting its market position and long-term viability. This commitment to user protection is a cornerstone of its overall brand narrative, fostering the confidence necessary for sustained growth in a volatile market.
Coinbase’s Preferred Authenticators: A Deep Dive into Technology and User Experience
Coinbase employs a multi-layered approach to security, but its primary recommendations for two-factor authentication revolve around specific technologies designed to offer superior protection. Understanding these options is key to making informed decisions about how you secure your own account.
The Gold Standard: Time-Based One-Time Password (TOTP) Apps
For the vast majority of its users, Coinbase strongly recommends and primarily supports Time-Based One-Time Password (TOTP) applications as the most secure and convenient form of 2FA. These apps, such as Google Authenticator, Authy, Microsoft Authenticator, and Duo Mobile, generate unique, temporary codes that change every 30 or 60 seconds.
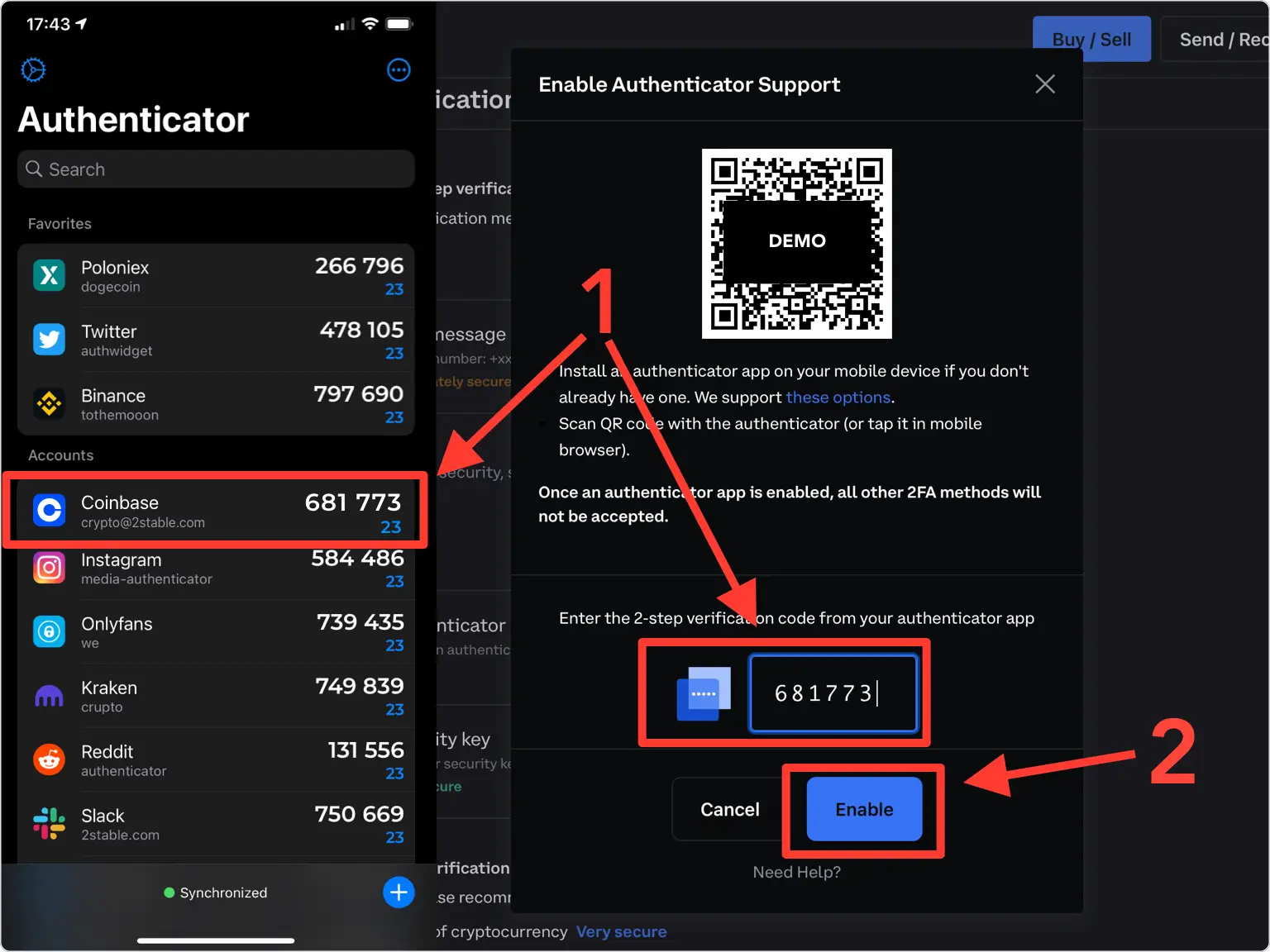
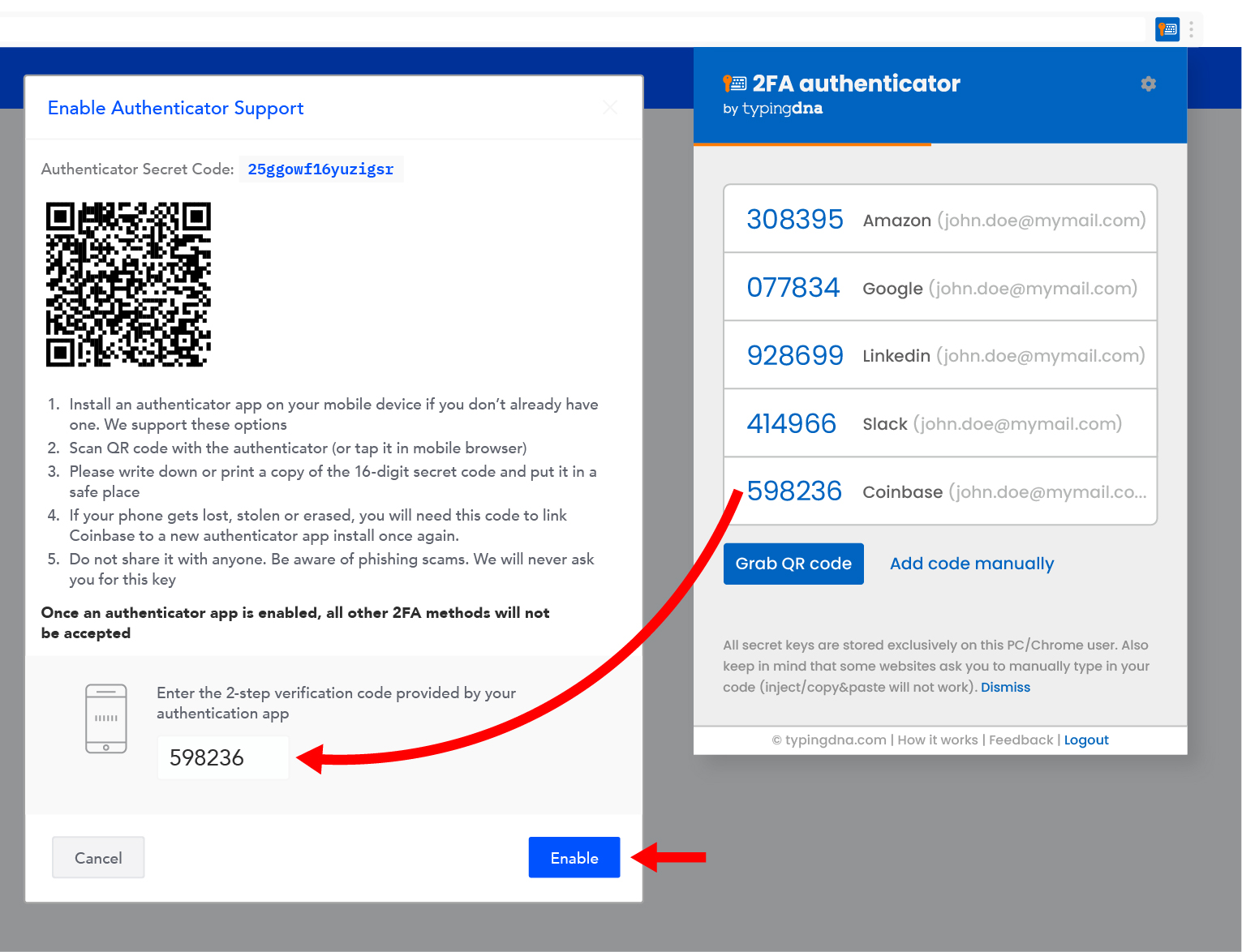
- How They Work: When you enable TOTP on Coinbase, you’re provided with a unique secret key, often in the form of a QR code. This key is shared between your chosen authenticator app and Coinbase’s servers. Both use this secret key, combined with the current time, to generate the same six-digit code simultaneously. When you log in, after entering your password, you open your authenticator app, retrieve the current code, and enter it into Coinbase.
- Advantages: TOTP apps offer significant security benefits. They are highly resistant to SIM swap attacks because the codes are generated on your device, not sent via SMS. They also provide protection against certain phishing attacks, as even if an attacker gets your password, they still need physical access to your device to get the TOTP code. Crucially, these apps work offline, meaning you don’t need a cellular signal or internet connection to generate a code, making them reliable even in connectivity-challenged situations.
- Disadvantages: The main drawbacks include the risk of losing the device where the app is installed, which can complicate account recovery. Users must also diligently back up their secret keys or enable cloud backup features (if available and trusted) to prevent losing access.
- Practical Advice: Setting up TOTP on Coinbase is straightforward. Navigate to your security settings, enable 2FA, and choose “Authenticator App.” You’ll be presented with a QR code to scan with your app. Crucially, always save the secret key (a string of characters provided alongside the QR code) in a secure, offline location. This key is your backup if you lose your phone.
The Convenience vs. Security Debate: SMS Authentication
SMS authentication involves sending a one-time passcode to your registered mobile phone number. While widely used and convenient for many services, Coinbase generally positions SMS verification as a less secure option, often suggesting it as a fallback or for less sensitive actions rather than the primary 2FA method for account access.
- What It Is: After entering your password, Coinbase sends a numerical code via text message to your phone. You then enter this code to complete the login process.
- Advantages: Its primary advantage is ease of use and ubiquity. Most users have a mobile phone, and receiving an SMS code requires no additional app installation or setup. It’s often the default for many services due to its low barrier to entry.
- Major Disadvantages: SMS is notoriously vulnerable to SIM swap attacks. In such an attack, criminals trick your mobile carrier into transferring your phone number to a new SIM card under their control. Once they control your number, they can intercept all incoming texts, including 2FA codes, and easily gain access to your Coinbase account if they also have your password. It’s also susceptible to phishing where users are tricked into entering SMS codes on fake websites.
- Coinbase’s Stance: While supported for certain actions or as an initial 2FA method, Coinbase actively encourages users to upgrade from SMS to TOTP apps or hardware keys for superior protection against sophisticated attacks. They often default to SMS if no other 2FA is set up, but their security recommendations heavily lean away from it for primary account access.
Hardware Security Keys: The Ultimate Defense
For users seeking the highest level of security, Coinbase supports hardware security keys, such as those compliant with the FIDO2/U2F standards (e.g., YubiKey, Ledger, Trezor). These physical devices offer unparalleled protection against phishing and account takeover.
- What They Are: A hardware security key is a small physical device, often resembling a USB stick, that you plug into your computer’s USB port or connect wirelessly (via NFC or Bluetooth) to your mobile device.
- How They Work: When logging into Coinbase, after entering your password, you are prompted to touch or interact with your hardware key. The key then cryptographically verifies your identity, proving that you physically possess the device. This process leverages advanced cryptographic protocols (like FIDO2 or U2F) that are inherently resistant to phishing. The key verifies the legitimacy of the Coinbase website, ensuring you’re not interacting with a fake site.
- Advantages: Hardware keys are considered the gold standard for authentication. They are immune to phishing, as the key itself verifies the legitimacy of the website. They also offer the strongest protection against SIM swaps and most forms of malware, as the authentication process happens on the key itself, isolated from your computer or phone’s operating system. They are incredibly user-friendly once set up.
- Disadvantages: The main drawbacks are the initial cost of purchasing the key(s) and the need to physically carry and manage them. Losing all your registered hardware keys without proper recovery methods can lock you out of your account.
- Coinbase’s Support: Coinbase highly recommends hardware security keys for advanced users and those holding substantial cryptocurrency amounts, offering them as the most robust layer of protection available.
Biometric Authentication (Device-Level)
While not a standalone 2FA method for initial account login on its own, biometric authentication (such as Face ID or fingerprint scanning) plays a significant role in securing the Coinbase mobile app experience.
- How It Integrates: Biometrics like Face ID or fingerprint unlock your Coinbase mobile app after it’s installed on your device. This provides a convenient and secure way to access the app without constantly re-entering your password. However, it’s crucial to understand that this is a device-level security feature that unlocks the app, not a direct replacement for the 2FA required for account access during login from a new device or web browser. Your primary 2FA method (TOTP, hardware key, or SMS) remains essential for truly securing your account against unauthorized access from different devices or situations where your primary device is compromised. It adds a layer of convenience and local security to your app, but doesn’t override the need for robust account-level 2FA.

Implementing and Managing Your Coinbase Security: Best Practices for Tech-Savvy Users and Investors
Securing your Coinbase account goes beyond simply enabling a 2FA method; it involves understanding best practices for setup, recovery, and ongoing digital hygiene. As an investor, protecting your digital assets requires a proactive and informed approach.
Prioritizing Your Authenticators: A Tiered Approach
Given the options, it’s essential to understand the hierarchy of security and make choices that align with your risk tolerance and the value of your assets.
- Recommendation: Hardware Key > TOTP App > SMS. This hierarchy reflects the increasing levels of security offered by each method.
- Hardware Keys: The ultimate protection, especially against sophisticated phishing and SIM swap attacks. Ideal for anyone serious about crypto investing.
- TOTP Apps: An excellent balance of security and convenience, offering strong protection against common threats like SIM swaps. This should be the minimum standard for all users.
- SMS Authentication: While convenient, it’s the least secure and should be avoided as your primary 2FA method if possible, due to its vulnerability to SIM swap attacks. If it’s your only option, be hyper-vigilant about phone security and phishing attempts.
Setting Up and Backing Up Your Authenticators
Proper setup and diligent backup are critical to preventing both unauthorized access and self-inflicted lockouts.
- For TOTP Apps:
- Scan the QR Code: When enabling TOTP on Coinbase, use your chosen authenticator app to scan the provided QR code.
- Save the Secret Key: Crucially, Coinbase will also display a “secret key” (a long string of characters). Write this down and store it in multiple secure, offline locations (e.g., a physically locked safe, encrypted drive, or password manager’s secure notes). This key allows you to restore your TOTP authenticator on a new device if your original device is lost or damaged.
- Test It: Always test your 2FA immediately after setup to ensure it’s working correctly.
- For Hardware Keys:
- Register Multiple Keys: If affordable, register at least two hardware keys with Coinbase: one for daily use and one stored securely as a backup.
- Keep Them Safe: Treat your hardware keys like physical keys to your wealth. Store them in a safe place.
- Understand Recovery: Familiarize yourself with Coinbase’s recovery process for hardware keys, which often involves using a backup key or going through an identity verification process.
What to Do If You Lose Your Authenticator or Device
Losing your phone with your authenticator app or misplacing your hardware key can be a stressful experience, but preparation can ease the process.
- Proactive Backup is Key: If you saved your TOTP secret key, you can simply re-add it to a new authenticator app on a new device. If you have a backup hardware key, you can use that.
- Coinbase Account Recovery: If you lose all your 2FA methods and haven’t backed them up, you will need to initiate Coinbase’s account recovery process. This is intentionally rigorous and slow to prevent unauthorized access, involving extensive identity verification. It can take several days or even weeks. Be prepared to provide ID, potentially submit video verification, and be patient. This slow process, while frustrating, is a critical security measure.
Beyond Authenticators: A Holistic Approach to Digital Security
While strong authenticators are vital, they are part of a larger security ecosystem.
- Strong, Unique Passwords: Always use a complex, unique password for your Coinbase account. A password manager is highly recommended to generate and store these.
- Secure Your Email: Your email is often the gateway to all your online accounts. Enable 2FA on your email account (preferably TOTP or a hardware key, not SMS). Use a unique password for your email that is different from your Coinbase password.
- Phishing Awareness: Be perpetually vigilant. Always double-check URLs, verify sender identities, and never click suspicious links. Coinbase will never ask for your password or 2FA codes via email or text.
- Device Security: Keep your operating systems, browsers, and applications updated. Use antivirus software and a firewall. Avoid accessing Coinbase on public Wi-Fi networks without a VPN.
- Regular Security Reviews: Periodically review your Coinbase security settings, check your login history for suspicious activity, and ensure your recovery options are up to date.
The Brand Impact: How Coinbase’s Security Posture Shapes Trust and Market Position
In the highly competitive and often volatile cryptocurrency market, an exchange’s security measures are not just technical specifications; they are fundamental pillars of its brand identity, directly influencing user trust, regulatory standing, and long-term success.
Building User Confidence in a High-Stakes Environment
For Coinbase, maintaining a reputation for impregnable security is paramount. Cryptocurrencies represent real financial value, and users entrust the platform with their hard-earned assets. Any perceived weakness in security, or worse, an actual breach, could shatter user confidence, leading to a mass exodus of funds and severe damage to its brand. By actively promoting and integrating robust authenticators like TOTP apps and hardware keys, Coinbase signals to its users that it prioritizes their safety. This proactive approach fosters a sense of security, which is critical for attracting new users and retaining existing ones in a market where trust is often fragile. A brand synonymous with security gains a significant competitive advantage, differentiating itself from less scrupulous or less technologically advanced platforms. This assurance is a powerful marketing tool, converting security features into a tangible value proposition for its customer base.
Navigating Regulatory Scrutiny and Industry Standards
The cryptocurrency industry faces increasing scrutiny from regulators worldwide, who are concerned about consumer protection, anti-money laundering (AML), and counter-terrorist financing (CTF). Exchanges like Coinbase are expected to meet and often exceed stringent security standards. Coinbase’s commitment to advanced authentication methods demonstrates its adherence to, and leadership in, best practices for digital asset security. By offering and encouraging strong 2FA, Coinbase aligns itself with regulatory expectations, which can smooth its path through licensing processes and help it navigate complex legal landscapes. This proactive stance not only protects its users but also protects Coinbase itself from potential legal and financial repercussions that could arise from inadequate security. Its choices in authenticators are a testament to its commitment to operating as a compliant and responsible financial institution in the digital age, a critical aspect of its corporate identity.
The Long-Term Value Proposition: Protecting Assets, Protecting Reputation
The financial and reputational costs of a security breach are immense. Beyond the direct loss of funds, a breach can trigger expensive investigations, legal battles, regulatory fines, and a prolonged period of brand rehabilitation. For Coinbase, which has aspirations of becoming a mainstream financial services provider for the digital economy, such a setback could be catastrophic. By prioritizing state-of-the-art authentication technologies, Coinbase makes a long-term investment in its brand equity. It’s a strategic decision that protects its users’ money, which in turn protects its own financial stability and its standing as a reputable player in the global financial system. The continuous evolution of its security protocols, including its selection of authenticators, reflects an ongoing commitment to staying ahead of threats. This dedication to security reinforces Coinbase’s value proposition not just as an exchange, but as a trusted partner in the decentralized financial future, building a brand identity that emphasizes safety, reliability, and innovation.
Conclusion
The question “What authenticator does Coinbase use?” leads us to a crucial understanding of digital asset security. While Coinbase supports various authentication methods, its strong recommendation and primary reliance are on Time-Based One-Time Password (TOTP) applications like Google Authenticator or Authy, offering robust protection against common cyber threats. For the most discerning users, hardware security keys represent the apex of security, providing unparalleled defense against sophisticated phishing attacks. SMS authentication, though convenient, is recognized as the least secure option and generally not recommended for primary account access.
Ultimately, securing your Coinbase account is a shared responsibility. Coinbase provides the tools and the framework, but users must actively choose and correctly implement the strongest authentication methods available to them. By opting for TOTP apps or, ideally, hardware security keys, coupled with vigilant cybersecurity practices, users can significantly reduce their risk of falling victim to account takeovers. This proactive approach not only safeguards personal financial investments but also reinforces Coinbase’s brand as a secure and trustworthy platform in the high-stakes world of cryptocurrency. As the digital landscape continues to evolve, staying informed and adopting best practices in multi-factor authentication will remain the cornerstone of protecting your digital wealth.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.