In the vast and ever-evolving landscape of technology, databases stand as the silent powerhouses underpinning nearly every digital interaction. From banking transactions to social media feeds, e-commerce orders to intricate scientific simulations, data is the lifeblood, and its integrity and management are paramount. Within the sophisticated architecture of SQL (Structured Query Language) databases, a powerful yet often misunderstood mechanism exists: the trigger. More than just a simple command, a trigger is an automated, event-driven action that can profoundly impact data quality, system security, and operational efficiency. For anyone navigating the complexities of modern software development, digital security, or even the nuanced world of financial data, understanding SQL triggers is not merely a technical detail—it’s a critical insight into robust data management.
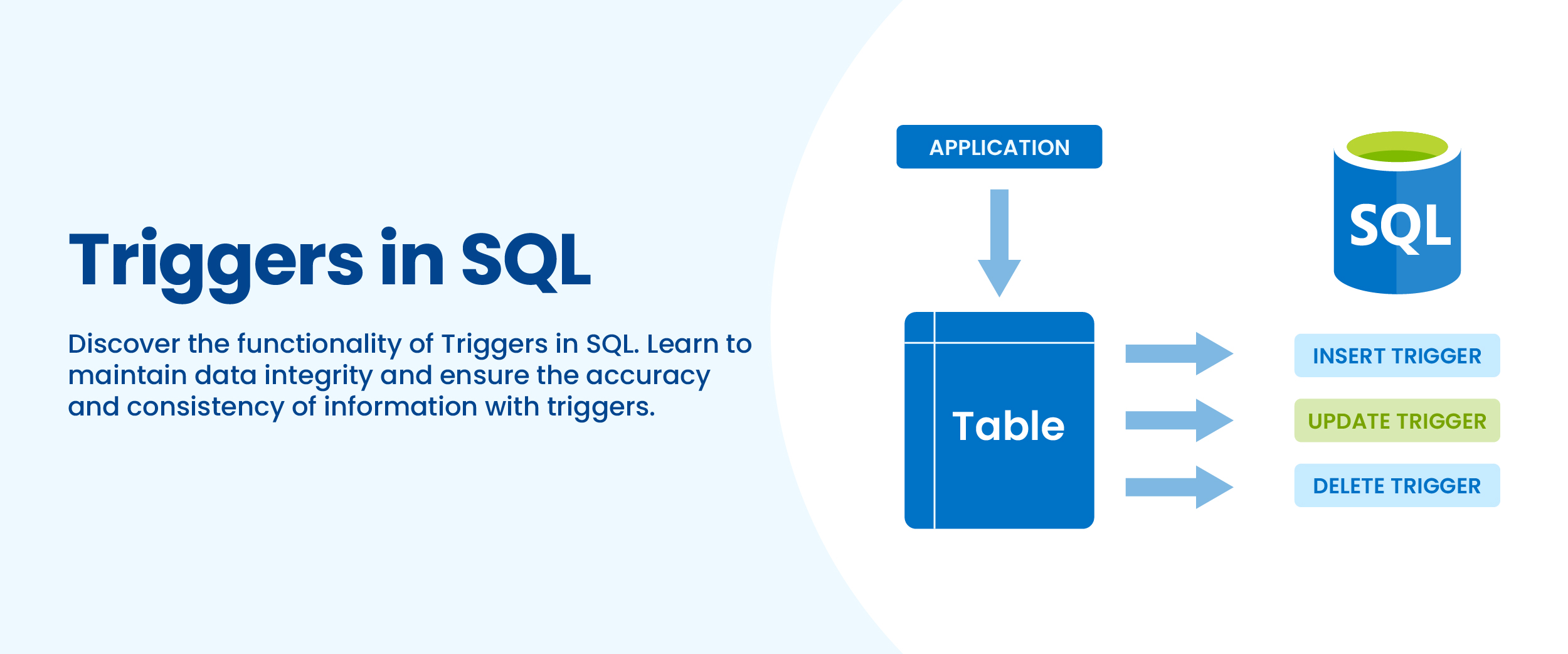
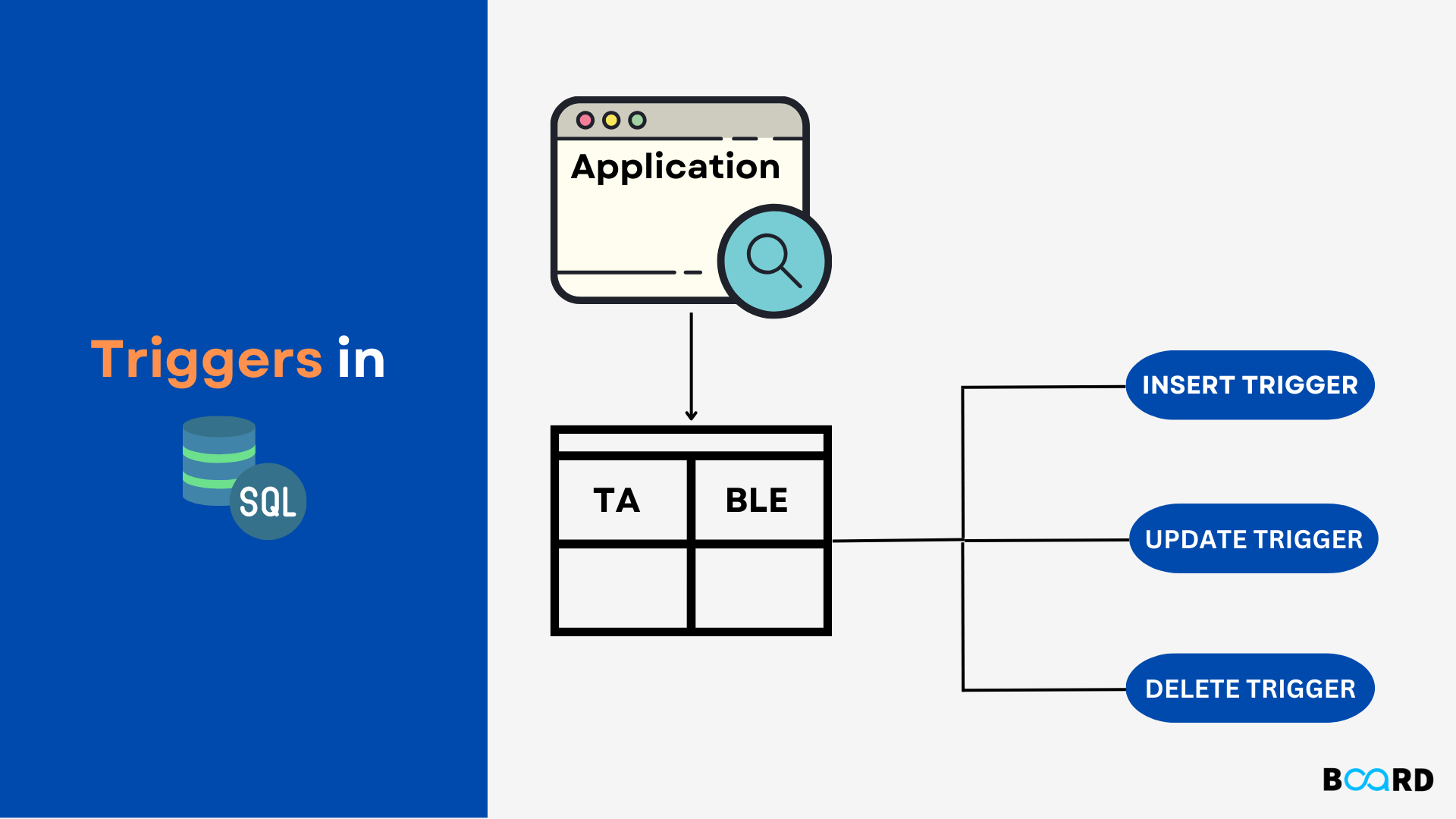
At its core, a SQL trigger is a special type of stored procedure that automatically executes or “fires” when a specific event occurs in the database. Unlike regular stored procedures that must be explicitly called, triggers are implicitly invoked by database events, such as an INSERT, UPDATE, or DELETE operation on a table, or even DDL (Data Definition Language) events like CREATE, ALTER, or DROP statements. They act as vigilant guardians, ensuring that predefined rules and actions are consistently enforced without requiring manual intervention from applications or users. This intrinsic automation makes them invaluable tools for maintaining data integrity, implementing complex business logic, and bolstering the overall reliability of database systems.
Understanding the Fundamentals of SQL Triggers
To truly harness the power of SQL triggers, one must first grasp their fundamental mechanics and classifications. These underlying principles dictate how and when triggers operate, directly influencing their effectiveness in various database scenarios.
What is a Trigger?
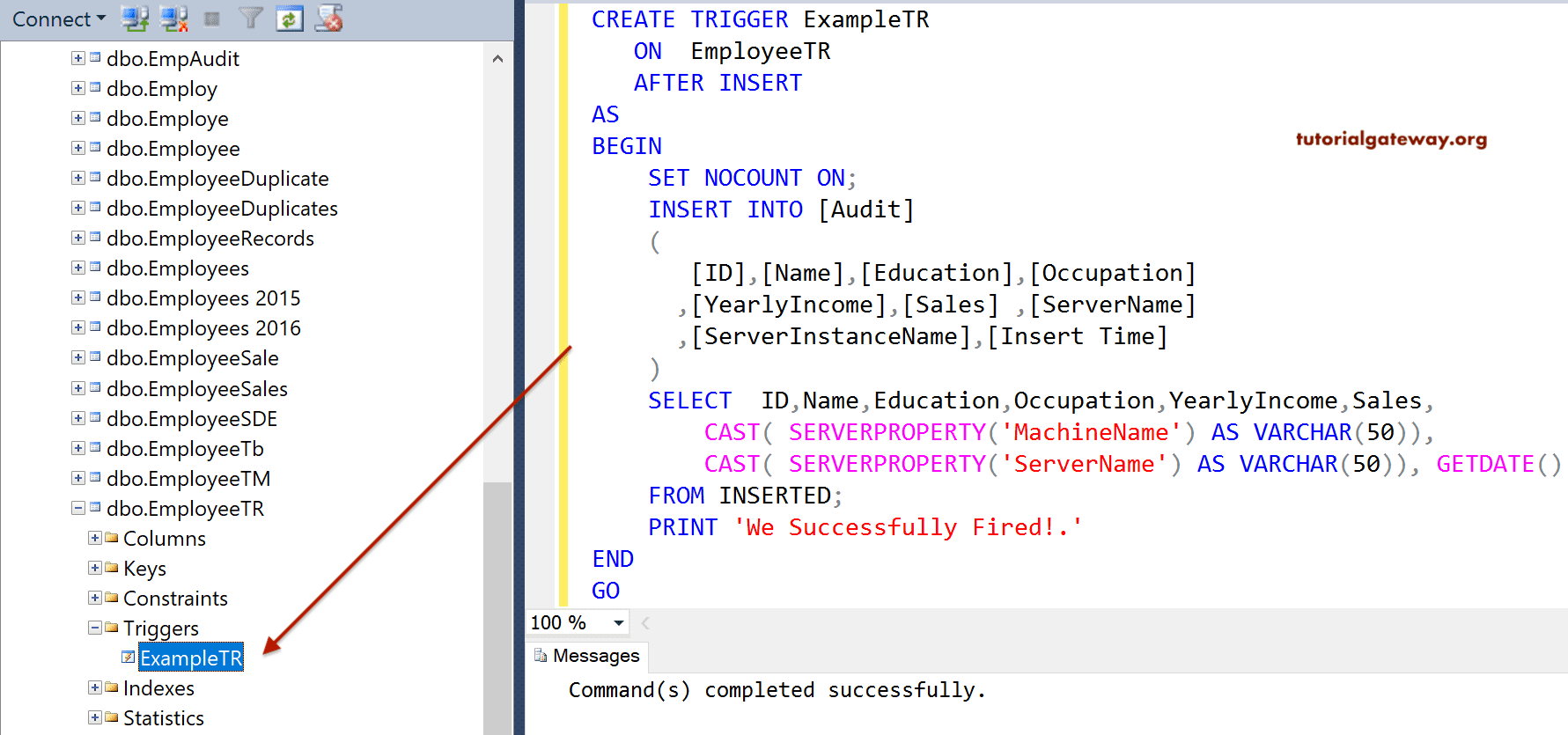
A trigger, in the context of SQL, is essentially a piece of procedural code (written in a language like T-SQL for SQL Server, PL/SQL for Oracle, or PostgreSQL’s PL/pgSQL) that is associated with a specific table or view. It’s designed to react to particular data manipulation events. Imagine a security camera that automatically records footage whenever motion is detected; a trigger works similarly. When a specified event occurs on its associated table—for instance, a new row is inserted, an existing row is updated, or a row is deleted—the trigger “fires,” executing the code defined within it. This code can perform a wide array of tasks, from validating new data to updating related tables, logging changes, or even preventing an action from completing if certain conditions aren’t met. The key characteristic is their automatic, event-driven nature, making them distinct from other database objects that require explicit invocation.
Types of Triggers: DML, DDL, and LOGON
Triggers are primarily categorized by the type of event they respond to. The most common and widely utilized are Data Manipulation Language (DML) triggers, which react to changes in data.
- DML Triggers: These are the workhorses of database automation.
INSERTtriggers activate when new rows are added to a table. A typical use case might be automatically populating an audit trail table with details of newly added records or calculating derived values immediately upon insertion.UPDATEtriggers fire when data in an existing row is modified. They are frequently used to enforce business rules (e.g., ensuring a price cannot be updated below cost), track changes to sensitive fields, or synchronize data across related tables.DELETEtriggers execute when rows are removed from a table. These are crucial for maintaining referential integrity (e.g., cascading deletes to child tables, or preventing deletion if dependent records exist) and for logging deleted information for archival or compliance purposes.
Beyond DML, other less common but equally powerful trigger types exist:
- DDL Triggers: Data Definition Language triggers respond to events related to the database schema itself, such as
CREATE,ALTER, orDROPstatements for tables, views, functions, or procedures. These are invaluable for database administrators to monitor and control schema changes, enforce naming conventions, or prevent unauthorized structural modifications, thereby bolstering digital security and consistency. - LOGON Triggers: Found in some database systems like SQL Server, LOGON triggers fire in response to a
LOGONevent. They can be used to audit login activity, restrict users from logging in based on certain criteria (e.g., time of day, IP address), or even set specific session configurations for different user groups, adding another layer to digital security and resource management.
Before vs. After Triggers
Another critical distinction lies in the timing of trigger execution relative to the event that caused them to fire.
- BEFORE Triggers: These execute before the triggering DML event (INSERT, UPDATE, or DELETE) is committed to the database. BEFORE triggers are exceptionally useful for validating data before it’s written. For example, a BEFORE INSERT trigger could check if an entered email address is in a valid format or if a product quantity is non-negative. If the validation fails, the trigger can prevent the original DML operation from completing, thus ensuring data integrity from the outset.
- AFTER Triggers: Also known as FOR triggers, these execute after the triggering DML event has successfully completed. AFTER triggers are ideal for actions that depend on the data having already been written to the table. Common uses include updating related tables based on a change, logging the final state of an affected row into an audit table, or initiating complex business logic that relies on the new or modified data. For instance, an AFTER INSERT trigger might calculate a customer’s total order value after a new item is added to their cart.
Understanding these distinctions allows developers and database administrators to strategically implement triggers, choosing the right type and timing to achieve specific goals related to data validation, automation, and system reliability.
The Power and Practical Applications of SQL Triggers
The true value of SQL triggers becomes apparent when examining their practical applications across diverse scenarios. They serve as foundational elements for robust database management, touching upon data integrity, complex automation, and even security.
Ensuring Data Integrity and Consistency
One of the most paramount roles of SQL triggers is to enforce data integrity beyond the standard constraints (like PRIMARY KEY, FOREIGN KEY, UNIQUE, CHECK, and NOT NULL). While these constraints handle basic rules, triggers excel at enforcing more complex, cross-table, or conditional business rules. For example, a trigger can ensure that an employee’s salary update doesn’t exceed a specific percentage increase, or that an order cannot be placed if the inventory level is insufficient, checking against another table. They can also maintain referential integrity in complex scenarios where simple foreign key constraints might fall short, such as when dealing with historical data or auditing requirements where deleted parent records need to be archived before removal. By automatically preventing invalid data from entering or modifying the database, triggers ensure that the information remains reliable and consistent, which is crucial for accurate reporting and sound decision-making, directly impacting brand trust and financial analysis.
Automating Complex Business Logic
Modern businesses operate on intricate rules and workflows, many of which involve data manipulation. Triggers offer an elegant solution for automating these complex business logic processes directly within the database layer, rather than scattering them across various application codebases. Consider a scenario where updating a customer’s address automatically needs to update the address in all their associated orders that are still pending. An AFTER UPDATE trigger on the customer table can efficiently handle this cascading update logic. Similarly, triggers can automatically calculate derived values (e.g., total order amount, customer loyalty points) upon insertion or update of related data, eliminating the need for application-level calculations and reducing potential discrepancies. This automation streamlines operations, reduces manual errors, and ensures that business rules are applied uniformly and consistently across all data interactions, leading to increased operational efficiency and potential cost savings.
Auditing and Security
In an era defined by data breaches and regulatory compliance, auditing capabilities are non-negotiable. SQL triggers are exceptionally powerful tools for implementing comprehensive auditing mechanisms. An AFTER INSERT, UPDATE, or DELETE trigger can automatically record every change made to sensitive data, capturing details such as who made the change, when it occurred, what the old value was, and what the new value is. This audit trail is invaluable for debugging, recovering from accidental data loss, and, critically, for meeting compliance requirements like GDPR, HIPAA, or financial regulations.
From a digital security standpoint, triggers can also act as an early warning system or a preventative measure. A DDL trigger, for instance, could log or even prevent unauthorized attempts to DROP a critical table. A DML trigger could be designed to detect suspicious activity, such as a large number of updates from an unusual IP address, and either alert administrators or temporarily block further modifications. While not a standalone security solution, triggers provide an essential layer of internal control and accountability within the database ecosystem.
Optimizing Performance and Resource Management
While triggers are potent, their impact on performance must be carefully considered. When designed efficiently, triggers can contribute to performance optimization by consolidating logic at the database level, potentially reducing network round trips between the application and the database. For example, rather than an application making multiple calls to update related tables, a single DML statement can fire a trigger to handle all subsequent related updates. However, poorly written or overly complex triggers can introduce significant overhead. Triggers that perform intensive calculations, query large tables, or involve numerous updates on other tables can lead to deadlocks, increased transaction times, and overall database slowdowns. Therefore, judicious use, careful testing, and optimization are crucial to ensure triggers enhance rather than hinder system performance. Resource management also comes into play as triggers, by automating tasks, free up application server resources and developer time, allowing them to focus on core business logic rather than repetitive data maintenance tasks.
Triggers in the Modern Tech Landscape
The role of SQL triggers extends beyond traditional database administration, finding relevance in contemporary tech trends such as AI integration, robust software development, and advanced digital security.
Supporting Robust Software Development
In modern software development, the focus is increasingly on building resilient, scalable, and maintainable applications. SQL triggers contribute significantly to this goal by centralizing critical data-related logic within the database itself. This approach ensures that business rules are consistently applied regardless of which application, microservice, or user interface interacts with the data. For instance, if multiple applications (e.g., web, mobile, API backend) access the same database, implementing data validation or cascading updates via triggers guarantees uniform behavior across all entry points, reducing the likelihood of data inconsistencies caused by divergent application logic. This centralization enhances the overall reliability and maintainability of the software system, making it easier to debug, update, and scale, which are key considerations for any tech-focused brand. Triggers act as a robust safety net, catching potential errors before they propagate throughout the system.
Interfacing with AI and Analytics
The rise of AI and machine learning tools relies heavily on high-quality, real-time data. SQL triggers play a subtle yet important role in preparing and maintaining this data. For example, triggers can automatically clean or standardize data upon insertion, ensuring that the information fed into AI models is consistent and accurate, thereby improving model performance. They can also facilitate real-time analytics by triggering updates to materialized views or summary tables whenever underlying data changes. This allows business intelligence dashboards and AI applications to always operate with the most current information, which is critical for timely financial analysis, market trend prediction, and operational insights. Imagine an inventory management system where an AFTER UPDATE trigger on stock levels immediately updates an aggregated data store, providing real-time inventory visibility for an AI-driven supply chain optimization tool. This direct data flow, enabled by triggers, minimizes latency and enhances the responsiveness of AI-powered solutions.
Digital Security Implications
As digital security threats grow more sophisticated, layering defenses becomes paramount. SQL triggers, while not a primary firewall, offer a powerful line of defense at the database level. Beyond basic auditing, triggers can be configured to detect and react to suspicious patterns of database activity. For example, an AFTER UPDATE trigger could monitor a high volume of changes to financial records within a short period by a single user, flagging it as potential insider threat activity and alerting security teams. A LOGON trigger could restrict access to the database during non-business hours for certain user roles, mitigating risks associated with stolen credentials. Furthermore, DDL triggers can prevent unauthorized schema modifications that could open vulnerabilities or introduce backdoors. By integrating trigger-based security measures, organizations add a crucial layer of internal control and anomaly detection, bolstering their overall digital security posture and protecting sensitive assets.
The Business and Financial Impact of SQL Triggers
Beyond the technical efficiencies, the strategic implementation of SQL triggers has tangible business and financial benefits, influencing everything from operational costs to brand reputation.
Boosting Operational Efficiency and Cost Savings
Automation is a cornerstone of modern business strategy, and SQL triggers are powerful agents of automation within the database. By automatically enforcing business rules, validating data, and performing cascading updates, triggers significantly reduce the need for manual intervention or complex application-level coding. This automation translates directly into boosted operational efficiency. Less time is spent on correcting data errors, manually updating related records, or debugging inconsistent application logic. For businesses, this means fewer labor hours dedicated to routine data management tasks, which in turn leads to significant cost savings. Furthermore, by ensuring data accuracy from the point of entry, triggers minimize the costly impact of flawed data on business processes, customer relations, and decision-making, contributing directly to a leaner and more agile financial operation.
Enhancing Data Quality for Financial Decisions
In the realm of finance, data quality is not just a preference; it’s an absolute necessity. Financial decisions, from investment strategies to budgeting and risk assessment, are only as sound as the data they are based on. SQL triggers play a crucial role in enhancing this data quality by automatically enforcing financial rules and validations. For instance, a trigger can ensure that all financial transactions adhere to predefined accounting principles, that budget allocations are not exceeded, or that foreign exchange rates are always applied correctly at the time of a transaction. By guaranteeing the integrity and consistency of financial data, triggers provide a trustworthy foundation for reporting, auditing, and analytical tools. This high-quality data empowers executives and financial analysts to make more informed, data-driven decisions, mitigate financial risks, and ultimately drive profitability, positioning triggers as a critical financial tool.
Mitigating Risks and Protecting Revenue
Data integrity directly correlates with risk mitigation and revenue protection. Data errors or inconsistencies can lead to incorrect invoices, delayed deliveries, regulatory fines, or even reputational damage, all of which impact the bottom line. Triggers act as proactive safeguards against these risks. By preventing invalid data entry or ensuring that critical business processes (like inventory updates or order fulfillments) are always executed correctly, triggers help minimize operational errors that could otherwise lead to lost revenue or increased costs. In areas like fraud detection, a trigger can monitor suspicious transaction patterns in real-time and alert personnel or even halt transactions, directly protecting against financial losses. The ability to automatically log all data changes for audit trails also aids in quickly identifying the root cause of issues, facilitating faster recovery and preventing recurrence, thereby safeguarding the company’s financial health and market standing.
Building Brand Trust Through Reliable Data
A brand’s reputation is built on trust, and in the digital age, trust is heavily influenced by the reliability and consistency of customer interactions. Flawed data—leading to incorrect personalized offers, delayed customer service responses, or erroneous billing—can quickly erode customer confidence and damage a brand’s image. SQL triggers contribute to building brand trust by ensuring that the data underpinning customer experiences is always accurate and consistent. When a customer updates their address, and a trigger ensures it’s instantly reflected across all relevant systems, their experience is seamless and reliable. When a product inventory is accurate due to trigger-enforced updates, customers receive correct availability information. This underlying data reliability translates into a perception of competence and trustworthiness, fostering stronger customer relationships and enhancing brand loyalty. In essence, the diligent, unseen work of SQL triggers contributes significantly to a positive corporate identity and a sterling brand reputation.
Best Practices and Considerations for Using Triggers
While powerful, triggers require careful consideration and adherence to best practices to avoid common pitfalls and maximize their benefits.
Performance Implications and Debugging Challenges
As mentioned, triggers execute automatically, and their performance impact can be substantial if not managed correctly. Overly complex triggers that perform extensive queries or modify many rows in other tables can lead to slow transactions, increased contention, and even deadlocks, severely affecting overall database performance. It’s crucial to write triggers that are as efficient as possible, limiting their scope and avoiding unnecessary operations. Debugging triggers can also be challenging because they are implicitly invoked. Errors within a trigger might manifest as an application failing to update data without a clear error message from the application itself, requiring deeper database-level investigation. Thorough testing in development environments and robust error handling within trigger code are essential.
When to Use Triggers (and When Not To)
The decision to use a trigger should be strategic. Triggers are best suited for tasks that must occur consistently at the database level, regardless of the application interacting with the data. This includes:
- Enforcing complex business rules that span multiple tables or cannot be handled by standard constraints.
- Implementing robust auditing and logging for compliance or security.
- Automating cascading actions that ensure data integrity across related tables.
- Maintaining derived data (e.g., aggregate values) that needs to be updated in real-time.
However, triggers are not a panacea. Avoid using them for:
- Simple data validation that can be handled by
CHECKconstraints or application logic (to keep database logic lean). - Long-running processes that could block transactions. These are better handled by asynchronous tasks or scheduled jobs.
- Logic that truly belongs in the application layer, as over-reliance on triggers can make application code less portable and harder to understand.
- Complex reporting queries that should be handled by views, stored procedures, or reporting tools.
The guiding principle should be: if the logic is critical to data integrity and needs to be enforced universally at the database level, a trigger might be appropriate. Otherwise, explore other solutions.
Documentation and Maintenance
Like any piece of critical code, triggers require thorough documentation. Clear explanations of what each trigger does, why it exists, what events it responds to, and what side effects it might have are vital for future maintenance and troubleshooting. As business rules evolve, triggers may need to be updated or refactored. Without proper documentation, understanding and modifying existing triggers can become a daunting and error-prone task. Maintenance plans should include regular reviews of triggers to ensure they remain relevant, performant, and aligned with current business requirements and database schema. This proactive approach ensures that triggers continue to be assets rather than liabilities within the database environment.
Conclusion
SQL triggers, though often operating silently in the background, are indispensable components in the architecture of robust and reliable database systems. They embody the principle of automated vigilance, ensuring data integrity, enforcing complex business rules, and fortifying digital security without requiring explicit command. From the perspective of technology, triggers empower developers to build more resilient software, streamline data preparation for AI and analytics, and enhance overall digital security postures. On the business and financial fronts, their ability to boost operational efficiency, ensure data quality for critical financial decisions, mitigate risks, and ultimately build stronger brand trust makes them a strategic asset.
However, like any powerful tool, triggers demand careful consideration, strategic implementation, and ongoing maintenance. Adherence to best practices, a keen awareness of their performance implications, and clear documentation are paramount to harnessing their full potential. In an increasingly data-driven world where accuracy, efficiency, and security are non-negotiable, understanding and effectively utilizing SQL triggers is not just a technical skill—it’s a fundamental aspect of building the trustworthy, high-performing digital infrastructure that defines successful brands and drives financial growth.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.