In an increasingly digital world, social media platforms like Instagram have become central to how we share our lives, connect with others, and even build professional brands. A common query that surfaces in this landscape, often fueled by curiosity or a misunderstanding of platform mechanics, is “how to install private Instagram photos.” This phrasing might seem perplexing to those familiar with Instagram’s robust privacy architecture, but it encapsulates a fundamental desire: to view or access content that isn’t publicly available.
This article aims to demystify the concept, address the ethical and technical realities of accessing private Instagram content, and guide users toward responsible digital citizenship. Far from offering a backdoor to private profiles, we will explore legitimate pathways, highlight critical digital security concerns, and underscore the importance of respecting personal boundaries in the online realm. For anyone keen on understanding Instagram’s privacy settings, protecting their own digital footprint, or navigating the ethical considerations of online interactions, this guide offers essential insights. We’ll delve into the technological safeguards Instagram employs, the perils of third-party tools promising illicit access, and the profound impact of online actions on one’s personal brand and financial security.
The Reality of Instagram’s Privacy Features
Instagram, like many leading social media platforms, is built with a tiered privacy system designed to give users control over who sees their content. This system is not merely a suggestion; it’s a foundational element of the user experience and a cornerstone of digital security. Understanding how these features work is the first step in comprehending why the idea of “installing private Instagram photos” in an unauthorized manner is fundamentally misguided and often impossible.
How Instagram’s Private Accounts Work
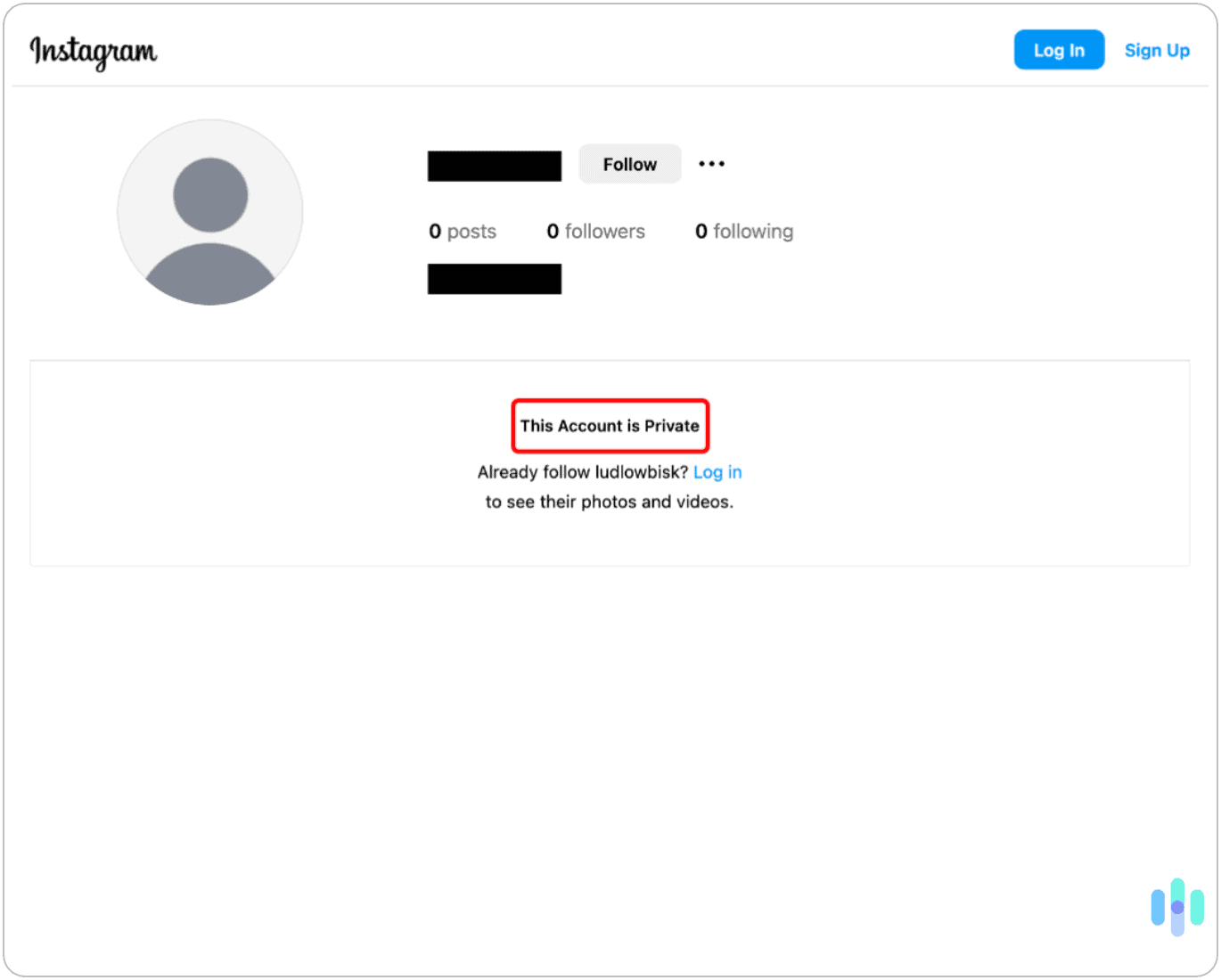
When a user opts to make their Instagram account “private,” they are essentially putting up a digital gate. This gate ensures that only approved followers can view their posts, stories, and reels. Any new user wishing to see their content must send a “follow request,” which the account owner then has the option to accept or decline. This mechanism is incredibly effective because it places the power directly in the hands of the individual user, allowing them to curate their audience and maintain a desired level of privacy.
From a technical standpoint, Instagram’s servers do not serve private content to non-followers. The data stream for private posts is encrypted and permission-gated at the server level. This means that without explicit authorization granted by the account owner (i.e., accepting a follow request), the content simply isn’t delivered to your device. It’s not a matter of finding a hidden link or circumventing a simple firewall; it’s about a fundamental access control system. This robust framework is a testament to Instagram’s commitment to user privacy, which aligns with broader technology trends emphasizing data security and user control. For individuals and brands alike, leveraging this feature responsibly is crucial for managing their online presence and digital security, helping to protect personal information and maintain reputation.
Why Direct “Installation” of Private Photos Isn’t Possible (or Ethical)
The idea of “installing private Instagram photos” typically implies gaining unauthorized access to content from a private account and downloading it to your device. From a technical perspective, this is not feasible through legitimate means. Instagram’s architecture is designed to prevent such unauthorized data extraction. The platform doesn’t offer a “download” button for public photos, let alone private ones, except for content you’ve posted yourself. Any method claiming to “install” or download private photos without the account owner’s explicit permission or approval is either a scam, a highly sophisticated (and illegal) exploit, or a misunderstanding of how the platform operates.
Ethically, attempting to bypass privacy settings and access someone’s private content without their consent is a serious violation of their privacy. It demonstrates a lack of respect for personal boundaries and can have significant social and even legal repercussions. In an era where digital ethics are increasingly scrutinized, engaging in such practices can severely damage one’s personal brand and online reputation. For businesses, any association with such unethical practices could lead to a massive loss of trust, a blow to corporate identity, and potential financial penalties. Therefore, it is imperative to approach digital interactions with integrity and respect for others’ privacy settings, acknowledging that their choices about who sees their content are their own.
Ethical and Legitimate Ways to View Private Instagram Content
While unauthorized access is firmly out of bounds, there are entirely legitimate and ethical ways to view content from an Instagram account that has been set to private. These methods all revolve around one core principle: consent. By respecting the user’s choice to keep their profile private, you engage with the platform in a way that upholds digital ethics and fosters trust.
The Power of the “Follow” Request
The most straightforward and universally accepted method to view a private Instagram account’s content is to send a “follow request.” When you do this, you are formally asking the account owner for permission to view their posts. They receive a notification and can then decide whether to accept or decline your request.
- How it works:
- Navigate to the private Instagram profile you wish to follow.
- Tap the “Follow” button.
- Your request will be sent, and the button will change to “Requested.”
- If the user accepts, you will become a follower and gain access to their private content. If they decline or ignore the request, you will not be able to see their posts.
- Best practices: When sending a follow request, especially to someone you don’t know well, ensure your own profile is not suspicious. A complete profile with a profile picture and some public posts can make you seem more trustworthy. If your profile is also private, the user might be more inclined to accept, knowing you also value privacy. This interaction is a direct digital equivalent of asking for permission and respecting boundaries, crucial for maintaining a positive personal brand online.
Direct Communication and Consent
Sometimes, a direct conversation outside of Instagram can be the most effective approach. If you know the person in real life, or have a mutual connection, consider reaching out through another channel (e.g., text message, email, another social media platform, or in person).
- How to approach: Politely explain why you’re interested in following their Instagram. Perhaps you’re a friend, a family member, or someone with a legitimate connection. A simple message like, “Hey [Name], I’d love to follow your Instagram to see your posts. I sent a request – no worries if you prefer to keep it just for close friends!” can go a long way.
- The importance of “no”: Be prepared to accept “no” as an answer. If someone declines your follow request or doesn’t respond to your message, respect their decision. Repeatedly sending requests or trying to find alternative ways to view their content after being denied is considered harassment and can have negative consequences for your online reputation. Respecting consent isn’t just an ethical standard; it’s a fundamental aspect of digital security and maintaining healthy online relationships. For individuals building a personal brand, demonstrating this respect is paramount.
Utilizing Shared Content (with permission)
Another legitimate way to “see” private content without directly following the account is if the owner explicitly shares it with you through other means.
- Direct Messaging: A private account owner can choose to send specific photos or videos from their private feed directly to you via Instagram’s Direct Message (DM) feature, even if you don’t follow them. This is a common way for friends or family to share content selectively.
- Sharing on Other Platforms: They might also choose to share certain content on a different social media platform where you are connected, or even send photos via email or messaging apps.
- Live Events or In-Person Sharing: Sometimes, the “installation” is simply seeing the photo on their phone during an in-person interaction.
In all these scenarios, the key element is that the content is being shared with their permission. You are not bypassing any security measures; you are receiving content that the user has chosen to share with you. This emphasizes the importance of consent and respectful interaction within digital communities, aligning with sound digital security practices and preserving one’s brand integrity.
The Dark Side: Understanding and Avoiding “Private Instagram Viewer” Scams
The persistent desire to access private Instagram content has unfortunately given rise to a predatory ecosystem of scam websites and applications. These entities promise to provide a shortcut to viewing private profiles without permission, often luring unsuspecting users with claims of sophisticated “hacks” or “viewer tools.” However, engaging with such services is a perilous endeavor, fraught with significant digital security risks, potential financial loss, and severe damage to one’s online reputation. Understanding these threats is crucial for safeguarding your digital life.
Common Tactics of Scam Websites and Apps
These fraudulent services typically employ a range of deceptive tactics to ensnare users:
- Grand Promises: They boast immediate, guaranteed access to any private Instagram profile with just a few clicks. These promises are always too good to be true because Instagram’s security infrastructure is designed to prevent such unauthorized access.
- Fake User Testimonials: Many scam sites feature fabricated reviews or comments from “satisfied users” praising their efficacy. These are designed to build a false sense of credibility and trust.
- Demands for Personal Information: Before supposedly granting access, these sites often demand an array of personal data, ranging from your Instagram login credentials (a major red flag!) to your email address, phone number, or even credit card details for a “verification” fee.
- Survey Traps and Malware Downloads: Instead of delivering the promised content, users might be redirected to endless surveys designed to generate ad revenue for the scammers, or worse, prompted to download suspicious software. This software is almost always malware, spyware, or adware.
- Urgency and FOMO (Fear Of Missing Out): Scammers often create a sense of urgency, suggesting that their “tool” is a limited-time offer or that the target’s profile might become unavailable soon, pressuring users into hasty decisions.
These tactics are sophisticated, preying on curiosity and a lack of technical understanding. Recognizing them is your first line of defense against becoming a victim.
Digital Security Risks: Malware, Phishing, and Data Breaches
The real danger in using “private Instagram viewer” tools extends far beyond simply not getting what you paid for. The digital security risks are profound:
- Malware and Viruses: The “software” or “apps” you’re asked to download are almost guaranteed to contain malware. This malicious code can infect your device, steal your personal files, track your activities, or even turn your device into part of a botnet.
- Phishing Attacks: By asking for your Instagram login credentials, these sites are essentially conducting a phishing attack. Once they have your username and password, they can gain full access to your Instagram account, change your password, lock you out, post spam, or steal your identity. This compromises your tech security entirely.
- Data Breaches and Identity Theft: Providing any personal information—email, phone number, or credit card details—to these fraudulent sites puts you at severe risk of data breaches. This information can be sold on the dark web, used for identity theft, or exploited for further scams, leading to significant financial loss and credit fraud.
- Ransomware: In some extreme cases, malware might lock your files or even your entire device, demanding a ransom payment to restore access.
The lure of viewing a private profile pales in comparison to the potential devastation of these digital security threats. Protecting your devices and personal data should always be the top priority, making such “viewer” tools an absolute no-go.
Protecting Your Personal Brand and Financial Well-being
Beyond the immediate technical threats, engaging with illicit “private Instagram viewer” services carries significant implications for your personal brand and financial well-being.
- Reputational Damage: Even the attempt to bypass someone’s privacy settings, if discovered, can severely damage your personal reputation and professional brand. It signals a lack of ethical judgment and disrespect for others’ boundaries. In today’s interconnected world, a damaged online reputation can have long-lasting consequences, impacting job prospects, social standing, and business relationships.
- Financial Loss: Direct financial loss can occur through “verification fees” charged by scam sites, unauthorized credit card charges, or the costs associated with cleaning malware from your devices or recovering from identity theft. These seemingly small initial costs can snowball into substantial financial burdens. Furthermore, if your compromised account is used for illicit activities, you could be held liable, leading to further financial and legal troubles. For individuals looking to build online income or manage personal finance, falling prey to such scams can be a devastating setback.
- Legal Consequences: Depending on the jurisdiction and the nature of the “hack,” attempting to gain unauthorized access to someone’s private information can carry legal penalties. Cybercrime laws are becoming increasingly stringent, and ignorance is rarely an excuse.
In essence, the risk-reward ratio for attempting to “install private Instagram photos” through unauthorized means is overwhelmingly negative. The trivial curiosity is met with monumental threats to your digital security, personal brand, and financial stability. Responsible online behavior, guided by ethical considerations and a strong emphasis on digital security, is always the superior path.
Taking Control: Making Your Own Instagram Photos Private
While the initial query might have focused on viewing others’ private content, an equally crucial aspect of digital security and personal branding on Instagram is understanding how to protect your own content. Making your Instagram profile private is a powerful way to control your audience, manage your online presence, and safeguard your personal information. It’s about “installing” privacy settings for your photos, rather than trying to access others’.
Step-by-Step Guide to Activating Private Account Settings
Setting your Instagram account to private is a straightforward process that takes mere moments:
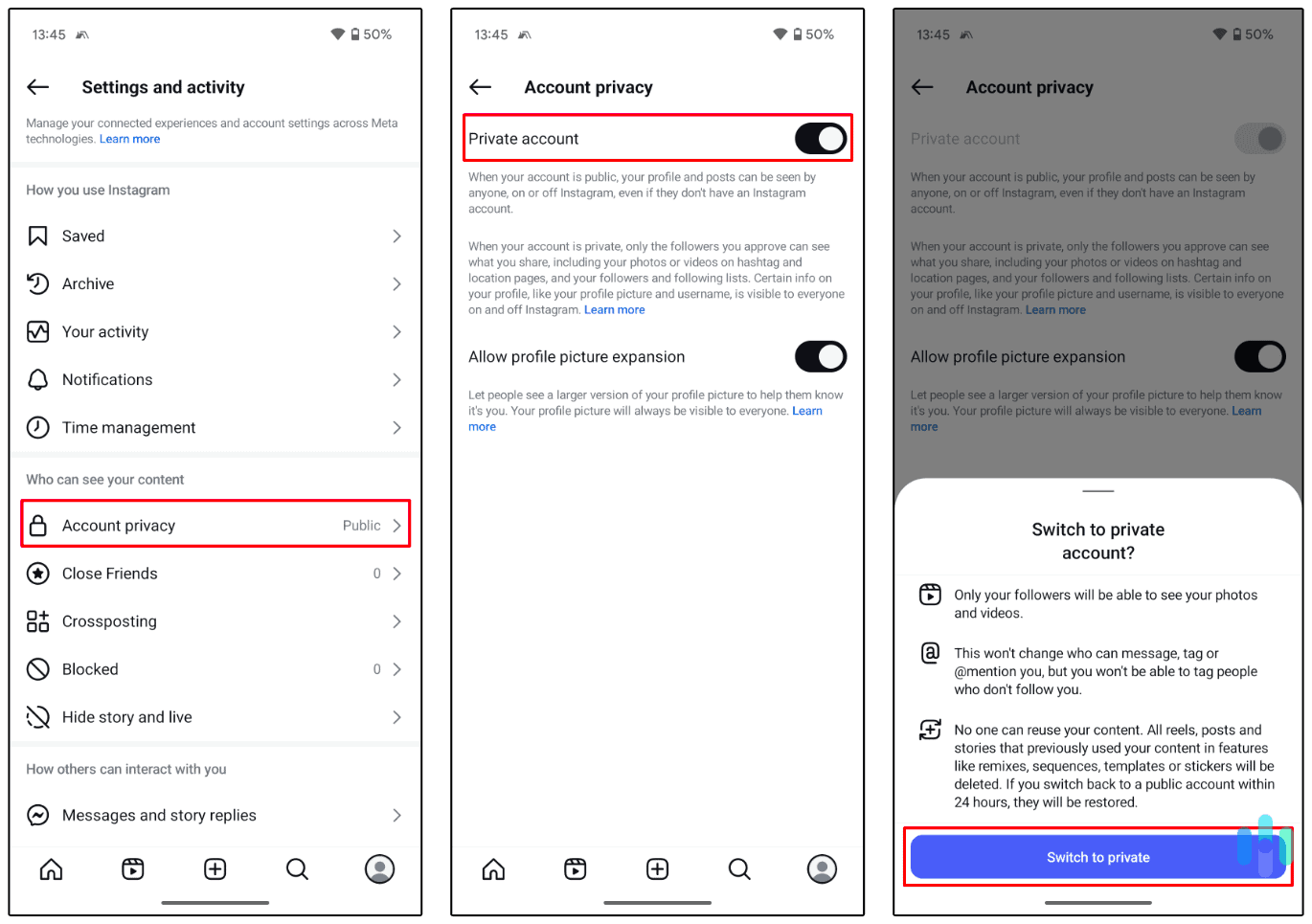
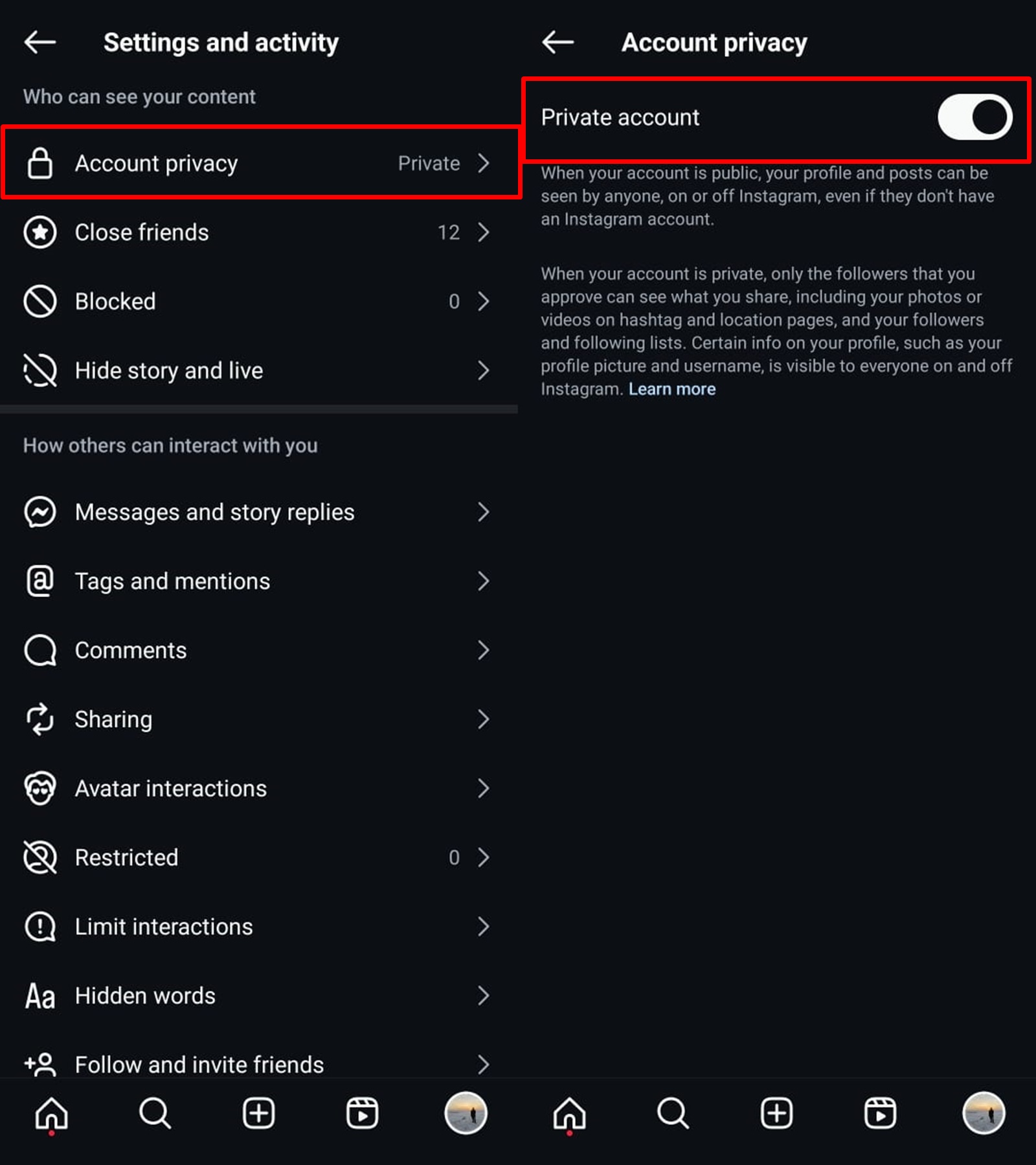
- Open Instagram: Launch the Instagram app on your mobile device.
- Go to Your Profile: Tap on your profile icon in the bottom right corner of the screen.
- Access Settings: Tap the three horizontal lines (hamburger menu) in the top right corner of your profile. From the menu that appears, select “Settings and privacy.”
- Navigate to Account Privacy: Scroll down and under “Who can see your content,” tap on “Account privacy.”
- Toggle Private Account: You will see a toggle switch labeled “Private account.” Tap this switch to turn it on.
- Confirm: A pop-up will appear asking you to confirm if you want to switch to a private account. Tap “Switch to Private.”
Once activated, your account is now private. Only your current followers will retain access to your posts. Any new users wishing to follow you will need your explicit approval. You’ll receive follow requests that you can then accept or decline, giving you complete control over your audience. This simple tech tutorial is fundamental for anyone looking to bolster their digital security.
The Benefits of a Private Profile for Personal and Professional Branding
Activating a private profile offers numerous advantages, particularly for managing your personal brand and digital security:
- Enhanced Privacy and Security: The most obvious benefit is increased privacy. You control who sees your content, significantly reducing the risk of unwanted attention, cyberstalking, or your personal photos being misused by strangers. This is a vital component of robust digital security.
- Curated Audience: For individuals, a private account allows for a more intimate and curated online space, often preferred for sharing personal moments with a trusted circle of friends and family. This can enhance the authenticity of your personal brand within that select group.
- Protection from Data Scraping: Public profiles are susceptible to data scraping, where bots collect publicly available information. A private profile significantly reduces this risk, safeguarding your data from being harvested for marketing, scams, or other unwanted purposes.
- Strategic Branding for Professionals: While many professionals use public profiles for broad reach, a private profile can also be a strategic choice. For instance, a consultant might use a private profile for close industry connections, sharing nuanced insights with a vetted network. This can foster a sense of exclusivity and deeper engagement within a specific niche, strengthening a specialized brand identity.
- Reputation Management: For those in public-facing roles, a private account can serve as a separate, personal space, allowing them to maintain a highly professional public image on other platforms while still enjoying personal sharing on Instagram without public scrutiny. This meticulous approach to managing online presence is a hallmark of strong brand strategy.
In essence, embracing Instagram’s private account feature empowers you to be proactive about your digital footprint. It’s a fundamental aspect of modern digital security and a powerful tool for strategic brand management, ensuring your online narrative is shared precisely as you intend it to be.
The Broader Implications: Digital Ethics and Responsible Online Behavior
The discussion around “installing private Instagram photos” goes beyond technical limitations and security risks; it delves into the core principles of digital ethics and responsible online behavior. In an age where our lives are increasingly intertwined with digital platforms, understanding and upholding these principles is paramount for fostering a respectful, secure, and productive online environment.
Respecting Digital Boundaries and Consent
At the heart of ethical online interaction is the concept of consent, mirroring its importance in offline relationships. Just as you wouldn’t physically enter someone’s private space without an invitation, attempting to bypass digital privacy settings is a violation of boundaries.
- The Golden Rule Online: Treat others’ digital spaces as you would want your own treated. If you value your privacy, you should extend the same respect to others. Instagram’s private account feature is an explicit declaration of a boundary; respecting it is a fundamental act of digital empathy.
- Building Trust: Relationships, both personal and professional, are built on trust. Attempting to circumvent privacy settings erodes trust and can damage connections. Conversely, respecting digital boundaries reinforces trust and contributes to a healthier online ecosystem. This applies significantly to brand strategy, where trust is a critical currency.
- The Principle of Least Harm: Ethical digital behavior adheres to the principle of causing the least harm. Trying to access private content without permission can cause distress, feelings of violation, and could expose individuals to risks they have actively tried to avoid.
In a world where digital security is a constant concern, advocating for and practicing consent in all online interactions is not just good manners; it’s a foundational element of a safe and ethical digital society.
Building a Secure and Trustworthy Online Presence
For individuals and brands alike, cultivating a secure and trustworthy online presence is essential. This involves not only protecting your own data but also demonstrating responsible behavior that contributes positively to your digital reputation and financial well-being.
- Proactive Digital Security: This includes using strong, unique passwords, enabling two-factor authentication, being wary of suspicious links and emails (phishing), and regularly reviewing your privacy settings across all platforms. For tech-savvy users, staying updated on digital security trends is an ongoing commitment.
- Mindful Content Sharing: Be judicious about what you share publicly online. Assume that anything posted publicly could potentially be seen by anyone, anywhere, forever. This helps in maintaining a coherent and positive personal brand. For businesses, this translates to rigorous content guidelines and brand strategy.
- Ethical Tool Usage: Use only legitimate, reputable tools and services. Avoid any third-party applications that promise to bypass security features or offer “hacks.” Such tools are often vectors for malware and scams, leading to significant financial loss and compromising your overall digital security. Investing in reliable financial tools and online income methods means avoiding shortcuts that could lead to scams.
- Education and Awareness: Stay informed about common online scams, privacy best practices, and the evolving landscape of cyber threats. Education is your best defense against exploitation.
- Reputation as Currency: In the digital age, your online reputation is a form of social and sometimes financial currency. Engaging in unethical practices can devalue this currency, making it harder to establish professional connections, secure employment, or even maintain personal relationships. Conversely, a reputation built on respect and integrity can open doors and foster opportunities.
Ultimately, the query “how to install private Instagram photos” serves as a potent reminder of the importance of digital literacy, ethical conduct, and robust digital security. By understanding Instagram’s privacy features, respecting others’ boundaries, and prioritizing safe online practices, we contribute to a more secure, trustworthy, and respectful digital world for everyone. This approach not only protects us from harm but also empowers us to build a strong, positive, and resilient online presence for ourselves and our brands.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.