In the rapidly evolving landscape of telecommunications, the transition from traditional hardware-based systems to software-defined networking has fundamentally altered how businesses communicate. At the heart of this transformation lies SIP Trunking. For the uninitiated, the term can sound like dense technical jargon, but it represents one of the most significant leaps in communication technology since the invention of the digital switch. As legacy copper-wire networks—known as the Public Switched Telephone Network (PSTN)—are phased out globally, understanding the mechanics, architecture, and technical advantages of SIP Trunks is essential for any modern enterprise.
Decoding the Mechanics of SIP Trunking
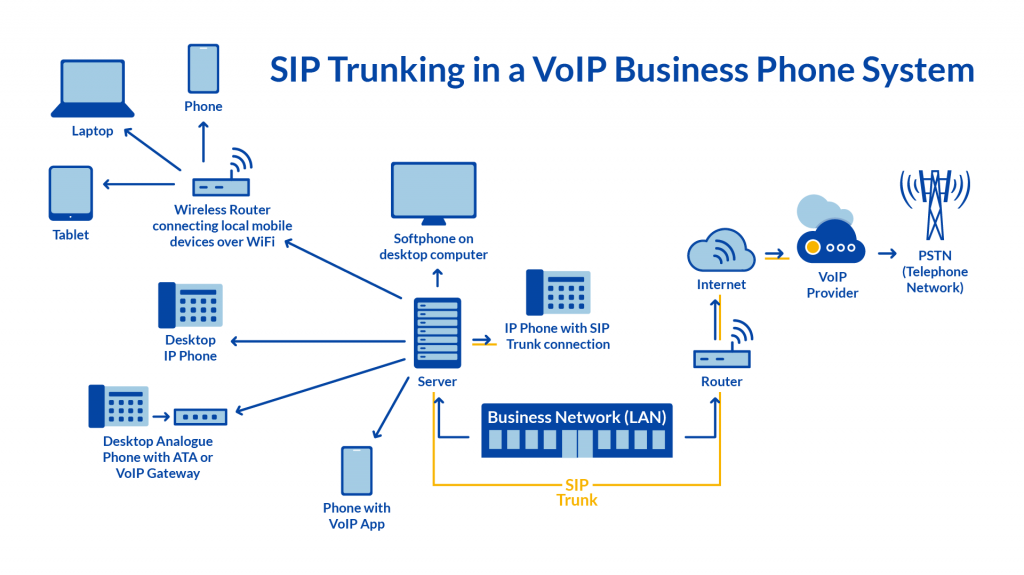
To understand what a SIP trunk is, one must first break down the acronym. SIP stands for Session Initiation Protocol. It is an application-layer protocol that facilitates the initiation, maintenance, and termination of real-time sessions that include voice, video, and messaging applications. A “trunk,” in historical telecom terms, referred to a physical line that carried multiple signals simultaneously. In the digital age, a SIP trunk is a virtual version of an analog phone line, allowing a Private Branch Exchange (PBX) to send and receive calls over the internet.
The Role of Session Initiation Protocol (SIP)
SIP is the signaling foundation of Voice over IP (VoIP). Unlike the protocols that actually carry the voice data, SIP’s primary job is “handshaking.” It locates the user, determines their availability, and establishes the parameters of the connection. Once the “session” is initiated, other protocols like RTP (Real-time Transport Protocol) take over to deliver the actual audio packets. SIP’s flexibility is its greatest technical strength; it doesn’t just handle voice—it can manage any media that can be transmitted digitally, making it the standard for multimedia communication.
From Analog to Packets: How Voice Becomes Data
Traditional telephony relies on Circuit Switching, where a dedicated physical path is opened for the duration of a call. SIP Trunking utilizes Packet Switching. When you speak into a handset connected to a SIP-enabled system, your voice is sampled and converted into digital data packets. These packets are labeled with headers containing destination information and sent across the IP network. Because these packets can take different routes to reach the destination and are reassembled in the correct order at the receiving end, the process is far more efficient than maintaining a dedicated physical circuit.
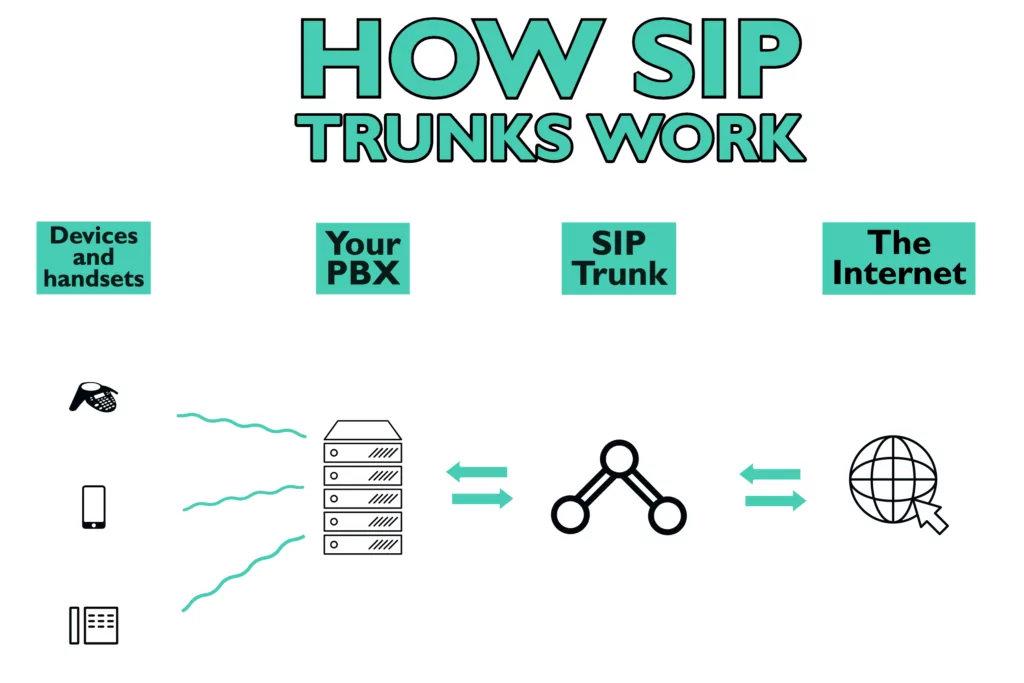
The Infrastructure: PBX and the IP Network
The architecture of a SIP setup typically involves three main components: a PBX (Private Branch Exchange), a SIP Trunk provider, and a robust internet connection. The PBX acts as the central switching system for an organization. In a SIP environment, this is often an “IP-PBX.” The SIP trunk acts as the bridge between the internal IP-PBX and the outside world. By eliminating the need for a physical connection to a local phone company, businesses can consolidate their voice and data traffic onto a single network interface, simplifying the hardware stack significantly.
Key Technical Benefits for the Modern Enterprise
The move to SIP Trunking is rarely just about replacing old wires; it is about unlocking technical capabilities that were impossible under the constraints of analog or ISDN (Integrated Services Digital Network) systems.
Infinite Scalability and Flexibility
In the world of traditional telephony, adding capacity meant physical installation. If a company needed ten more lines, a technician had to arrive, pull copper wire, and install new hardware interfaces (like T1 cards). SIP trunks are “elastic.” Because they are virtual, scaling capacity is often as simple as updating a software configuration or license. A business can scale from 10 to 1,000 concurrent calls almost instantly, providing a level of technical agility that matches the speed of modern software-as-a-service (SaaS) environments.
Direct Inward Dialing (DID) and Local Presence
Technically, SIP trunks allow for a sophisticated decoupling of geography from identity. Through Direct Inward Dialing (DID), a company can assign individual phone numbers to employees without needing a physical line for each. Furthermore, because SIP trunks operate over the internet, a server located in New York can host a “local” phone number in London or Tokyo. This is achieved by the SIP provider routing calls through local gateways in those regions and delivering the data packets to the central PBX via the cloud.
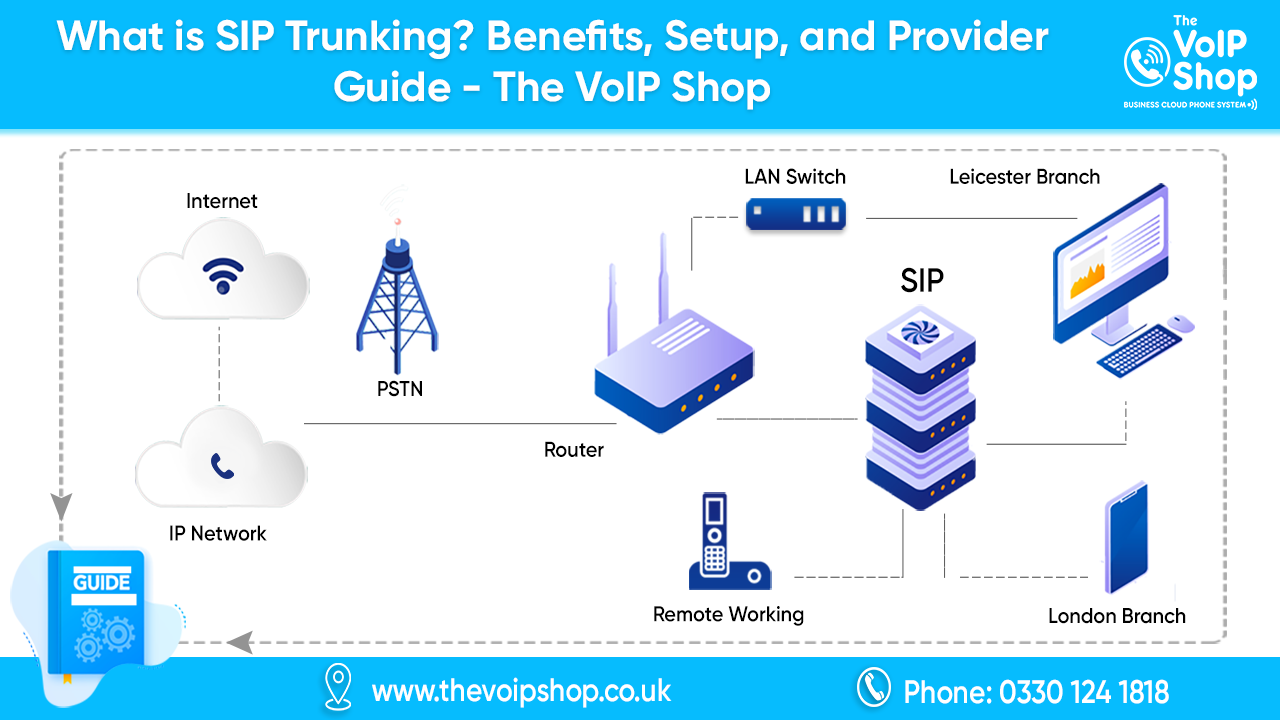
Disaster Recovery and Business Continuity
One of the most critical technical advantages of SIP is its inherent support for redundancy. In an analog setup, if the physical line to the building is cut, communication is severed. In a SIP configuration, call routing is handled at the network level. If the primary office loses power or internet, the SIP provider can instantly re-route traffic to a secondary IP address, a mobile application, or a backup data center. This level of failover is a cornerstone of modern digital infrastructure resilience.
Security Architectures in SIP Deployment
As with any technology that operates over the public internet, SIP Trunking introduces specific security challenges. Protecting the integrity of voice data and preventing unauthorized access to the network requires a multi-layered security architecture.
Encryption and TLS/SRTP
Unencrypted SIP packets are sent in plain text, making them vulnerable to “packet sniffing” or interception. To secure the signaling layer, engineers utilize Transport Layer Security (TLS), which encrypts the SIP messages between the PBX and the provider. For the actual voice traffic, Secure Real-time Transport Protocol (SRTP) is employed. SRTP ensures that even if voice packets are intercepted, they cannot be reconstructed into audible speech without the proper cryptographic keys.
Session Border Controllers (SBCs) as Gatekeepers
An SBC is a specialized device (or software) that sits at the edge of the network, acting as a firewall specifically designed for VoIP traffic. While a standard firewall might struggle to process the complex timing and port requirements of SIP, an SBC is “SIP-aware.” It inspects every packet, manages “NAT traversal” (ensuring packets find their way through internal network addresses), and hides the internal network topology from the outside world. This prevents attackers from identifying the specific IP addresses of internal handsets.
Mitigating DDoS and Toll Fraud
SIP systems are frequent targets for Distributed Denial of Service (DDoS) attacks and toll fraud—where hackers hijack a SIP trunk to make expensive international calls. Modern SIP security involves implementing rate-limiting (limiting the number of packets per second) and behavioral analytics. If a system suddenly attempts to make 500 concurrent calls to a high-cost destination, the SBC or the provider’s automated system can flag and kill the session in real-time based on predefined security protocols.
The Evolution Toward Unified Communications (UCaaS)
SIP Trunking is not the endgame of telecommunications; rather, it is the foundational layer for Unified Communications as a Service (UCaaS). By converting voice into data, SIP allows communication to be integrated into the broader software ecosystem of a company.
Beyond Voice: Integrating Video and Messaging
Because the SIP protocol is media-agnostic, it allows for the convergence of various communication channels. A single “session” can begin as an instant message, escalate to a voice call, and then transition into a high-definition video conference—all using the same underlying SIP signaling. This technical convergence eliminates the “silos” of communication, allowing data to flow seamlessly between different applications like CRM software, email clients, and collaboration tools.
The Impact of 5G and Edge Computing
The rollout of 5G networks is set to further enhance SIP performance. One of the main technical hurdles for VoIP has always been latency and jitter (the variation in packet arrival time). 5G’s ultra-low latency and high bandwidth mean that SIP trunks can maintain “carrier-grade” voice quality even over wireless connections. Furthermore, Edge Computing allows for SIP processing to happen closer to the user, reducing the distance data packets must travel and further improving the real-time nature of the communication.
AI-Driven Analytics in SIP Streams
As SIP traffic moves through a digital environment, it creates a wealth of metadata. Artificial Intelligence and Machine Learning tools can now analyze SIP streams in real-time. This can be used for everything from live transcription and sentiment analysis during a call to predictive maintenance of the network itself. By analyzing the “quality of service” (QoS) metrics—such as packet loss and latency—AI can automatically reroute traffic through more stable network paths before a human user even notices a degradation in call quality.
In conclusion, SIP Trunking is much more than a simple replacement for traditional phone lines. It is a sophisticated, protocol-driven technology that bridges the gap between legacy hardware and the future of cloud-native communication. By leveraging the power of IP networks, businesses can achieve a level of scalability, security, and integration that was previously unimaginable, ensuring that their communication infrastructure is as dynamic and resilient as the rest of their digital stack.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.