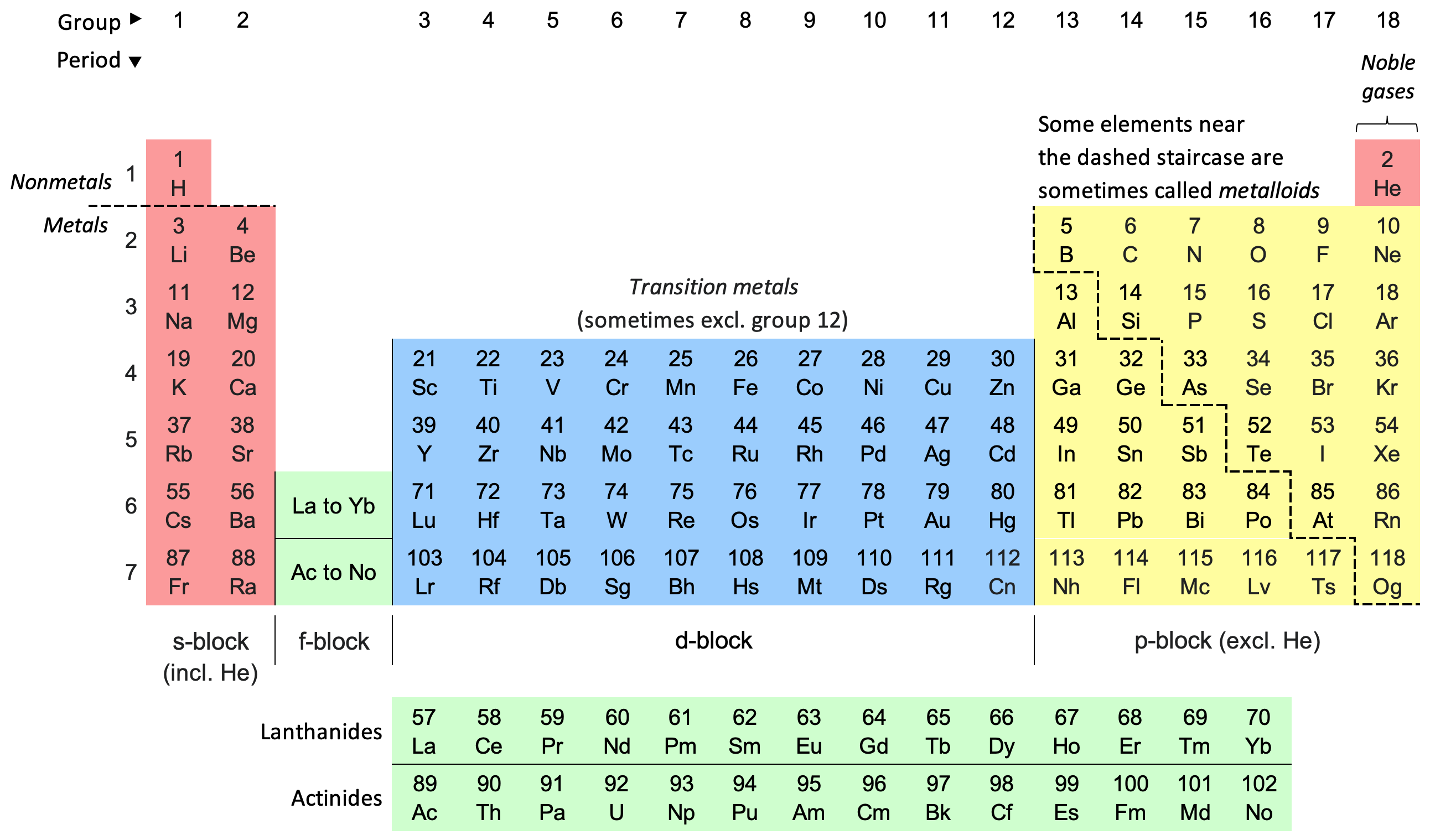
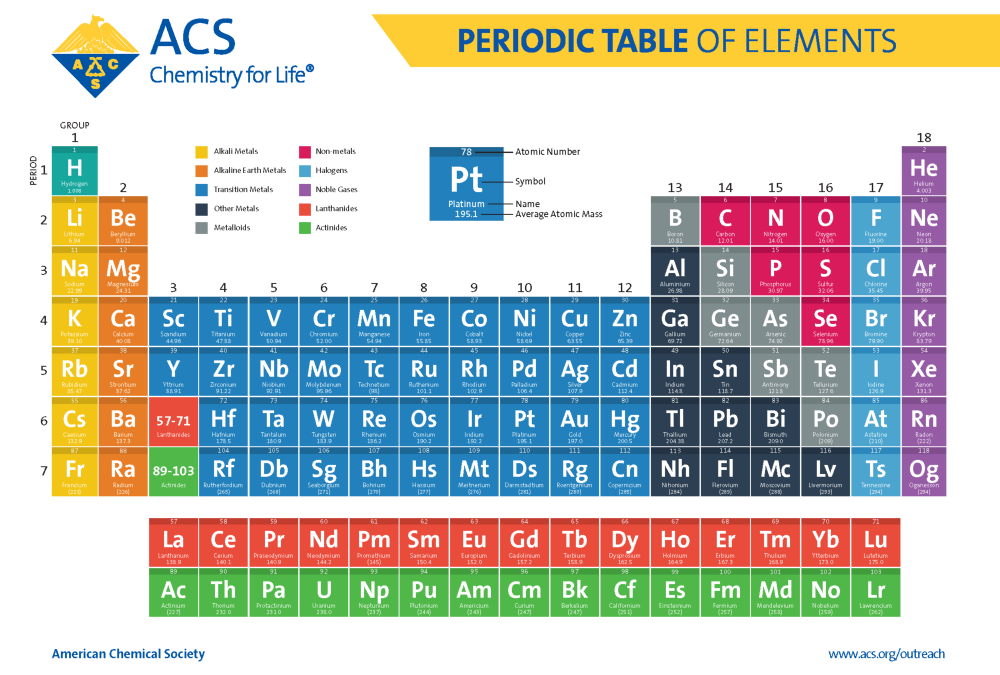
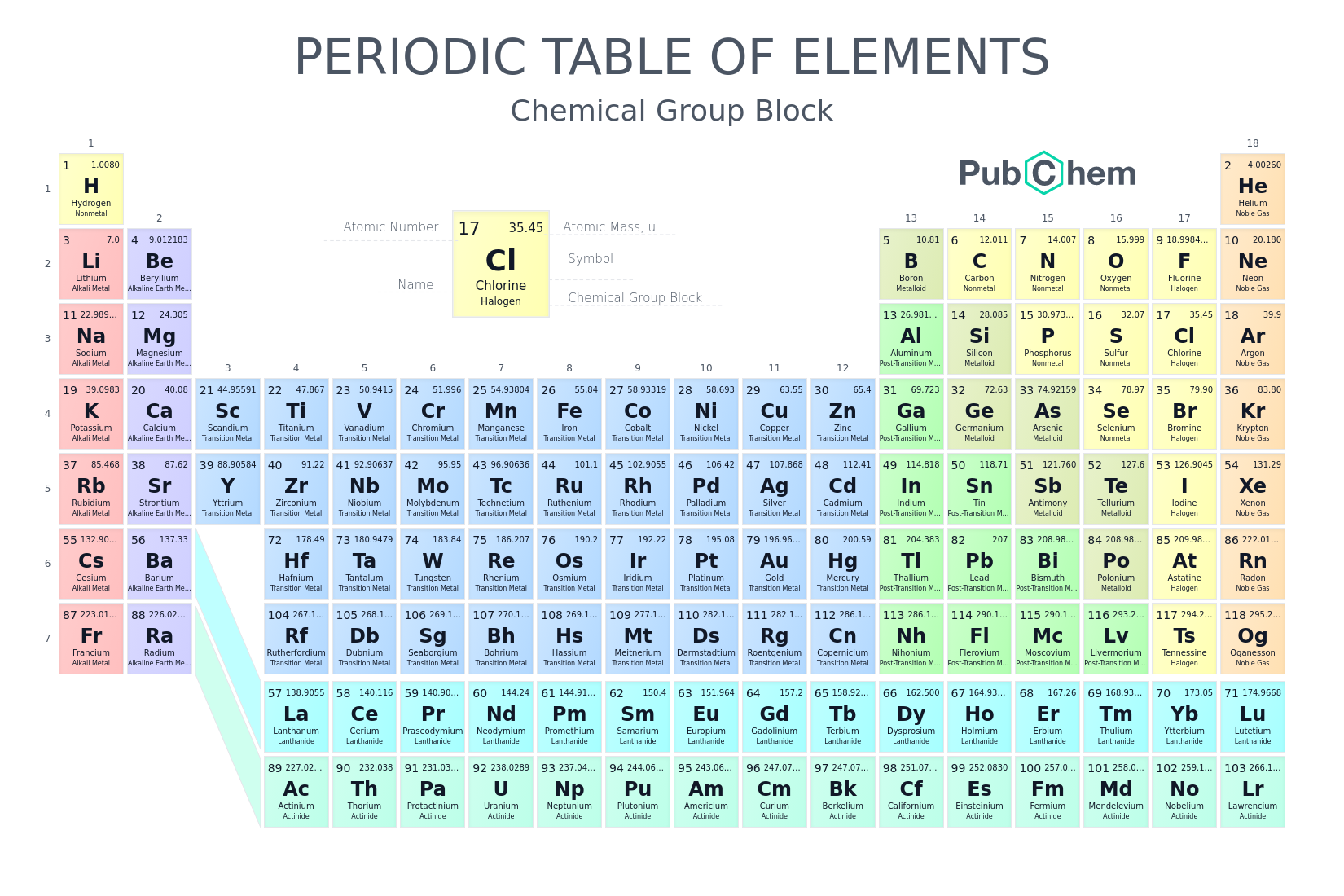
In the ever-expanding universe of technology, we are constantly bombarded with data, code, and concepts that can feel overwhelming. To navigate this digital cosmos, we rely on systems of organization, frameworks that bring order to chaos and allow for comprehension. While the scientific community has long embraced the elegant simplicity of the Periodic Table of Elements for understanding chemical properties, the digital realm, particularly within the technology sector, is also replete with its own implicit and explicit “periodic tables” of information. This article will explore how these organizational structures manifest within technology, shaping our understanding of software, AI, and digital security, and how grasping these “periodic tables” is crucial for anyone seeking to thrive in the modern tech landscape.
The Pillars of Tech: Fundamental Constructs and Their Organization
Just as the Periodic Table organizes elements by atomic number and chemical properties, the technology sector relies on fundamental constructs that are similarly categorized and understood. These pillars form the bedrock of digital innovation, and their organization dictates how we approach development, problem-solving, and even conceptualization.
1. The Software Stack: Layers of Abstraction and Functionality
The concept of a “software stack” is perhaps one of the most universally recognized “periodic tables” in tech. It’s a layered system where each layer builds upon the one below it, providing increasing levels of abstraction and functionality. Understanding these layers is essential for comprehending how applications are built, how they interact, and where potential issues might arise.
a. The Hardware Foundation: The Physical Bedrock
At the very bottom of the stack lies the hardware. This includes the physical components of a computer system: processors, memory (RAM), storage devices (SSDs, HDDs), network interface cards, and input/output devices. While often abstracted away in higher-level development, the capabilities and limitations of this hardware fundamentally dictate what is possible at every subsequent layer. Understanding basic computer architecture, CPU types (x86, ARM), and memory management is akin to understanding the basic properties of hydrogen or helium – the fundamental building blocks.
b. The Operating System (OS): The Conductor of the Digital Orchestra
Sitting atop the hardware is the operating system. This is the software that manages the computer’s resources and provides a platform for other applications to run. Think of operating systems like Windows, macOS, Linux, Android, or iOS. They handle tasks such as process management, memory allocation, file system management, and device drivers. Different OS families, like the Unix-like systems (Linux, macOS) or the Windows family, have their own sets of conventions and APIs, creating distinct “groups” within the broader OS category. Understanding the kernel, system calls, and the file system hierarchy are crucial here.
c. Middleware and Run-times: Bridging the Gap
Between the operating system and the application layer, we find middleware and run-times. Middleware acts as a translator or intermediary, facilitating communication between different applications or components. Examples include web servers (Apache, Nginx), application servers (Tomcat, JBoss), and message queues (Kafka, RabbitMQ). Run-times, such as the Java Virtual Machine (JVM) or the .NET Common Language Runtime (CLR), provide an environment for specific programming languages to execute. These layers are like the transition metals in the periodic table, facilitating interactions between different sets of elements.
d. Applications and User Interfaces (UI/UX): The Tangible Output
At the apex of the software stack are the applications themselves – the programs we interact with daily. This includes everything from web browsers and productivity suites to mobile apps and games. This layer also encompasses the User Interface (UI) and User Experience (UX) design. The UI is how the user interacts with the application, while UX focuses on the overall satisfaction and ease of use. Different application categories (e.g., enterprise software, consumer apps, games) and their underlying architectural patterns (e.g., monolithic, microservices) represent distinct “families” within this top layer.
The AI Landscape: A Constellation of Learning Paradigms
The field of Artificial Intelligence is a vast and rapidly evolving domain, and like the periodic table, it can be best understood by categorizing its core components and approaches. Rather than atomic numbers, AI’s organization is based on learning paradigms, data requirements, and problem domains.
1. Machine Learning Paradigms: The Core Learning Mechanisms
Machine Learning (ML) is the engine driving much of modern AI. Different ML paradigms are suited to different types of problems and data.
a. Supervised Learning: Learning from Labeled Examples
This is the most common form of ML. Here, algorithms are trained on datasets where the input data is paired with the desired output (labels). Think of training an image recognition system with thousands of images labeled as “cat” or “dog.” Key algorithms include linear regression, logistic regression, support vector machines (SVMs), and decision trees. The quality and quantity of labeled data are paramount, similar to how elemental properties are intrinsic.
b. Unsupervised Learning: Discovering Hidden Patterns
In unsupervised learning, algorithms are given unlabeled data and tasked with finding inherent structures or patterns. This includes clustering (grouping similar data points) and dimensionality reduction (simplifying complex datasets). Algorithms like K-means clustering and Principal Component Analysis (PCA) fall into this category. This is akin to discovering new elements and their properties without prior knowledge of their chemical reactions.
c. Reinforcement Learning: Learning through Trial and Error
Reinforcement learning involves an agent that learns to make decisions by performing actions in an environment and receiving rewards or penalties. This is how systems learn to play games like Chess or Go, or how autonomous robots navigate. Algorithms like Q-learning and Deep Q-Networks (DQN) are prominent here. This is like exploring the reactivity of elements under different conditions to discover stable compounds.
d. Deep Learning: The Power of Neural Networks
Deep learning is a subfield of ML that utilizes artificial neural networks with multiple layers (hence “deep”). These networks can automatically learn hierarchical representations of data. Deep learning has been transformative for tasks like image recognition, natural language processing (NLP), and speech recognition. Architectures like Convolutional Neural Networks (CNNs) for image data and Recurrent Neural Networks (RNNs) for sequential data are akin to specific groups of elements with specialized properties.
2. AI Applications and Domains: Where Intelligence Meets Reality
Beyond the learning paradigms, AI systems are also categorized by the problems they aim to solve and the domains they operate in.
a. Natural Language Processing (NLP): Understanding Human Language
NLP focuses on enabling computers to understand, interpret, and generate human language. This includes tasks like sentiment analysis, machine translation, chatbots, and text summarization. Language models like GPT-3 and its successors are prime examples of advancements in this domain. Different languages and their grammatical structures can be seen as distinct families of “elements” within NLP.
b. Computer Vision: Empowering Machines to “See”
Computer vision allows computers to “see” and interpret visual information from the world, such as images and videos. Applications include facial recognition, object detection, autonomous driving, and medical imaging analysis. The ability to process different visual features, akin to electron configurations, is key.
c. Robotics and Automation: Bringing Intelligence to the Physical World
This domain focuses on designing, building, and operating robots and automated systems that can perform tasks intelligently. This often involves a combination of computer vision, sensor data processing, and decision-making algorithms. The interplay of sensors and actuators can be viewed as complex chemical interactions.
Digital Security: The Guardians of the Digital Realm
In the realm of digital security, the “periodic table” is less about fundamental building blocks and more about threat vectors, vulnerabilities, and defense mechanisms. Understanding this landscape is crucial for protecting data, systems, and individuals.
1. Threat Actors and Their Motivations: The “Elements” of Malice
Just as the periodic table categorizes elements by their properties, digital threats can be categorized by the actors behind them and their objectives.
a. Cybercriminals: The Pursuit of Financial Gain
These are individuals or groups motivated by money. Their activities include ransomware attacks, phishing scams, credit card theft, and malware distribution for financial exploitation. Their methods are diverse, ranging from opportunistic attacks to highly sophisticated, targeted campaigns.
b. Nation-State Actors: Espionage and Sabotage
These actors are often affiliated with governments and engage in cyber warfare, espionage, and sabotage. Their motives can be political, economic, or strategic, aiming to disrupt critical infrastructure, steal state secrets, or influence geopolitical events.
c. Hacktivists: Ideologically Driven Attacks
Hacktivists use cyberattacks to promote their political or social agendas. Their targets are often organizations or governments whose actions they oppose, and their methods can include website defacement, data leaks, and denial-of-service (DoS) attacks.
d. Insiders: Threats from Within
These are individuals within an organization who pose a security risk, either intentionally or unintentionally. Malicious insiders might steal data or disrupt systems, while unintentional insiders might compromise security through negligence or human error.
2. Vulnerabilities and Attack Vectors: The “Reactions” that Lead to Breach
Understanding the weaknesses in systems and the pathways attackers exploit is critical for defense.
a. Software Vulnerabilities: Flaws in the Code
These are errors or weaknesses in software design, implementation, or configuration that can be exploited by attackers. Examples include buffer overflows, SQL injection flaws, and cross-site scripting (XSS) vulnerabilities. These are akin to inherent properties of elements that make them reactive.
b. Network Vulnerabilities: Weaknesses in Connectivity
These relate to the security of network infrastructure, such as unpatched routers, weak firewall configurations, or unsecured Wi-Fi networks. Attackers can exploit these to gain unauthorized access to internal systems.
c. Human Vulnerabilities: The Weakest Link
Human error, social engineering tactics (like phishing), and a lack of security awareness can be significant vulnerabilities. These are often the easiest entry points for attackers.
d. Physical Vulnerabilities: Access to the Hardware
Compromising physical security, such as gaining unauthorized access to server rooms or stealing devices, can bypass many digital security measures.
3. Defense Mechanisms: The “Compounds” of Security
Just as elements combine to form stable compounds, various security measures are combined to create robust defenses.
a. Authentication and Authorization: Verifying Identity and Access
This involves verifying who a user is (authentication) and what they are allowed to do (authorization). Multi-factor authentication (MFA), strong password policies, and role-based access control (RBAC) are key examples.
b. Encryption: Scrambling Sensitive Data
Encryption scrambles data, making it unreadable to unauthorized individuals. This is used for data at rest (stored data) and data in transit (data being sent across networks).
c. Firewalls and Intrusion Detection/Prevention Systems (IDS/IPS): Network Guardians
Firewalls act as barriers, controlling network traffic, while IDS/IPS monitor networks for malicious activity and can take action to prevent attacks.
d. Security Awareness Training: Empowering the Human Element
Educating users about security threats and best practices is crucial for mitigating human vulnerabilities.
By understanding these implicit “periodic tables” within technology – the structured organization of software stacks, the diverse paradigms of AI, and the threat landscape of digital security – we equip ourselves with the knowledge to not just comprehend the digital world, but to actively build, secure, and innovate within it. These frameworks provide the essential language and structure for navigating the complexities and opportunities that define the modern technological era.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.