In an increasingly digital world, the concept of a “wallet” has expanded far beyond its traditional leather-bound form. Today, asking “which wallet is this?” is less about identifying a brand of physical accessory and more about navigating a complex ecosystem of digital tools designed to store, manage, and transact with our ever-growing array of digital assets. From cryptocurrencies to contactless payments, identities, and even digital collectibles, the modern wallet is a crucial interface between us and the digital economy.
Understanding the different types of digital wallets, their underlying technologies, security protocols, and use cases is no longer just for tech enthusiasts; it’s a fundamental aspect of digital literacy. Whether you’ve stumbled upon an unfamiliar interface, are trying to secure your cryptocurrency holdings, or simply want to optimize your mobile payment experience, being able to identify and comprehend “which wallet this is” empowers you to make informed decisions and protect your digital footprint. This article will delve into the diverse landscape of digital wallets, offering a comprehensive guide to their identification, functionality, and the critical factors that differentiate them, all within the purview of technology.
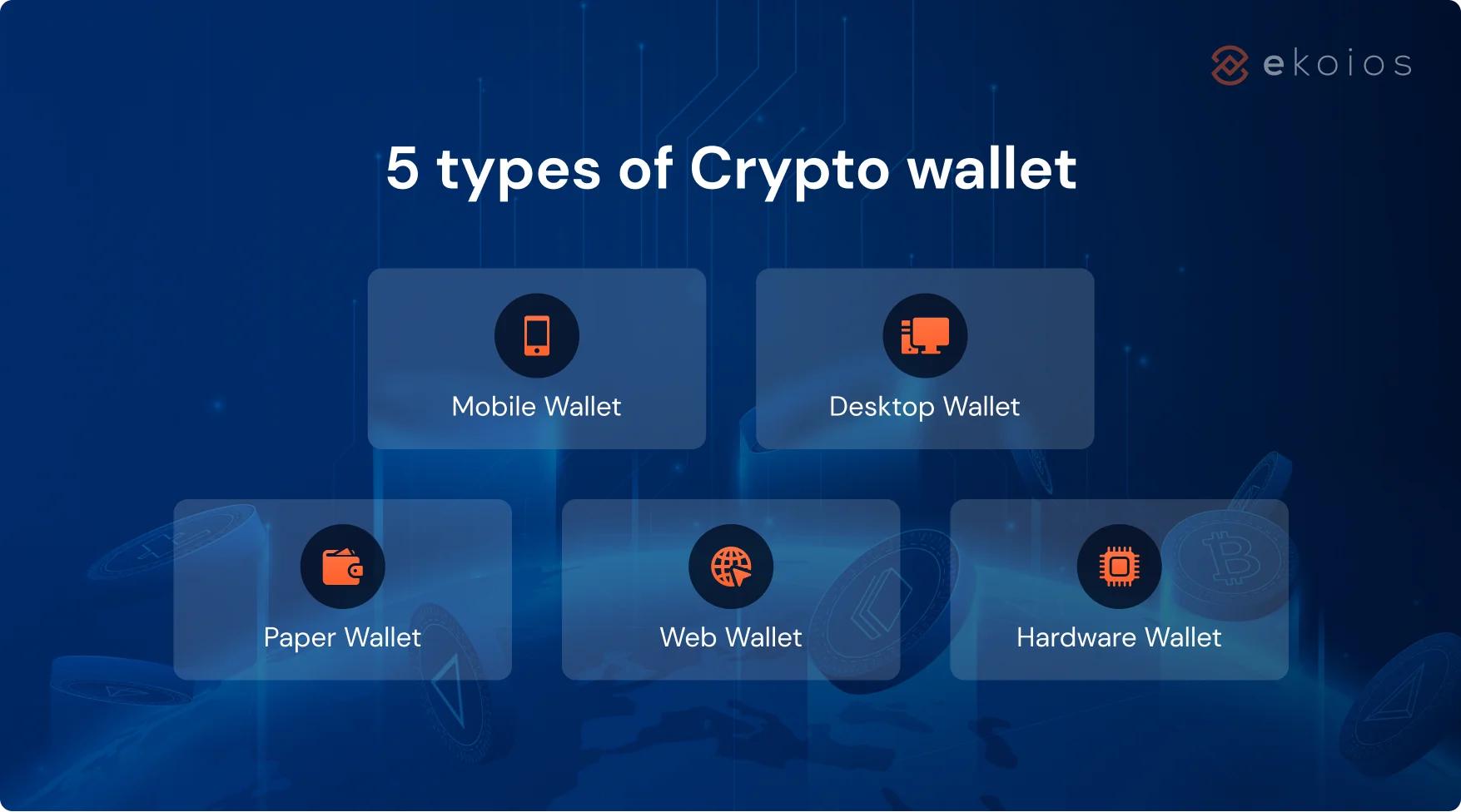
The Diverse World of Digital Wallets: A Categorization
The term “digital wallet” is an umbrella covering a variety of technological solutions, each designed with specific purposes, security models, and levels of user interaction. Recognizing these distinctions is the first step in answering “which wallet is this?”
Software Wallets: Accessibility and Convenience
Software wallets, often referred to as “hot wallets” because they are connected to the internet, are the most common and accessible form of digital wallet. They exist as applications on your computer, smartphone, or as browser extensions. Their primary advantage is convenience; they allow for quick and easy transactions.
- Desktop Wallets: These are applications installed directly onto a computer. They offer a good balance of security and usability, as your private keys are stored locally on your machine, providing more control than web wallets. Examples include Exodus and Atomic Wallet.
- Mobile Wallets: Designed for smartphones, these apps provide on-the-go access to digital assets. They often integrate with device features like QR code scanning and NFC for contactless payments. Popular examples include MetaMask (for Ethereum-based assets), Trust Wallet, and specific apps for Bitcoin like BlueWallet.
- Web Wallets: These wallets are accessed via a web browser, often hosted by a third-party service (e.g., cryptocurrency exchanges like Coinbase, Binance). While convenient, they are generally considered less secure as you entrust the management of your private keys to the service provider, making them vulnerable to exchange hacks or service outages.
- Browser Extension Wallets: These are specific types of software wallets that integrate directly into your web browser (e.g., Chrome, Firefox). They allow seamless interaction with decentralized applications (dApps) and web3 platforms. MetaMask is a prime example, crucial for interacting with the Ethereum ecosystem.
Hardware Wallets: The Pinnacle of Security
Hardware wallets, or “cold wallets,” are physical electronic devices designed to store your private keys offline, completely isolated from internet connections. This offline storage is their defining security feature, making them highly resistant to online threats like malware and phishing attacks. When you need to make a transaction, the device signs it internally and then broadcasts the signed (but not the private key) transaction to the network.
- USB-Stick Style Wallets: These typically resemble a USB drive and connect to your computer via a USB port. Ledger Nano S/X and Trezor Model T/One are the most well-known examples, supporting a vast array of cryptocurrencies.
- Specialized Devices: Some hardware wallets have more advanced features, screens, and buttons for transaction verification directly on the device, further enhancing security by preventing computer viruses from altering transaction details. These are often the preferred choice for serious investors and those holding significant amounts of digital assets.
Paper Wallets: The Analog Backup
A paper wallet is simply a physical printout of your public and private keys (often represented as QR codes). It’s an ultra-cold storage method as it’s entirely offline. However, they come with their own set of risks, such as physical damage (fire, water), loss, or accidental disposal. They also require careful handling to import keys correctly when you wish to spend the assets. While less common now due to the rise of user-friendly hardware wallets, they were once a popular method for long-term storage of cryptocurrencies.
Mobile Payment Wallets: Everyday Transactions
Distinct from cryptocurrency wallets, mobile payment wallets are primarily designed for fiat currency transactions. These are the apps that allow you to make contactless payments at point-of-sale terminals or online without needing a physical card.
- Integrated Mobile Wallets: Apple Pay, Google Pay, and Samsung Pay are prime examples. They store digitized versions of your credit/debit cards, loyalty cards, and sometimes even tickets, enabling transactions via NFC (Near Field Communication) or QR codes.
- Proprietary Payment Apps: Starbucks app, PayPal, Venmo, Cash App, and various banking apps often include their own in-app wallet functionalities for specific services or peer-to-peer transfers. While they facilitate digital transactions, they usually do not provide direct access to underlying crypto assets unless integrated as a separate feature.
Key Factors in Identifying and Choosing a Digital Wallet
Beyond simply categorizing, truly understanding “which wallet this is” involves evaluating its characteristics against a set of critical criteria. These factors also guide your decision-making when selecting a wallet for your own use.
Security Features: Protecting Your Digital Assets
Security is paramount in the digital asset space. Different wallets employ various mechanisms to protect your funds.
- Private Key Management: Is the wallet custodial (third-party holds keys) or non-custodial (you hold your own keys)? Non-custodial wallets offer greater control but place the full responsibility of security on the user.
- Encryption and Authentication: Does the wallet use robust encryption for stored data? What authentication methods are supported (password, PIN, biometrics like fingerprint/face ID, 2-Factor Authentication)?
- Open-Source vs. Proprietary: Open-source wallets allow the community to audit the code for vulnerabilities, often leading to more robust security over time. Proprietary software relies solely on the developer’s internal auditing.
- Seed Phrase/Recovery Phrase: Almost all non-custodial wallets provide a mnemonic seed phrase (typically 12 or 24 words) which is the master key to your funds. Understanding how this is generated, stored, and used for recovery is crucial.
Usability and User Experience: Seamless Interaction
A wallet’s design and ease of use significantly impact its practicality.

- Interface Intuition: Is the interface clear, easy to navigate, and user-friendly, especially for beginners?
- Transaction Speed and Fees: How quickly are transactions processed, and what are the associated network fees? Some wallets offer customizable fee settings.
- Integration with dApps and Services: For crypto wallets, how well does it integrate with decentralized applications, exchanges, and other Web3 services?
Supported Assets and Compatibility: What Can It Hold?
Not all wallets support all digital assets. This is a critical factor when determining “which wallet this is” in the crypto context.
- Specific Blockchain Support: Some wallets are built for a single blockchain (e.g., Bitcoin-only wallets), while others support multiple chains (e.g., Ethereum and its ERC-20 tokens, Solana, Polygon).
- Token Standards: Does it support specific token standards (e.g., ERC-20 for fungible tokens, ERC-721/ERC-1155 for NFTs on Ethereum)?
- Fiat On/Off Ramps: Can you easily buy or sell crypto with fiat currency directly within the wallet or through integrated services?
Recovery Options and Backup Mechanisms
What happens if you lose your device or forget your password? A robust wallet will have clear recovery procedures.
- Seed Phrase Recovery: The standard for non-custodial crypto wallets. Understanding how to securely back up and use your seed phrase is paramount.
- Cloud Backup/Restore: Some mobile payment wallets or custodial crypto services offer cloud backup or account recovery through email/phone verification.
Common Scenarios: When “Which Wallet Is This?” Becomes Critical
The question “which wallet is this?” often arises in specific, practical situations where identifying the nature of the wallet is crucial for security, functionality, or problem-solving.
Encountering an Unfamiliar Wallet Interface
You might come across a screenshot, a link, or even a physical device and wonder what kind of wallet it is. By applying the categorization and factor analysis above, you can often deduce its type. For instance, if it’s a browser extension, it’s likely a software wallet for interacting with dApps. If it’s a small, screen-equipped USB device, it’s almost certainly a hardware wallet. Understanding its type helps you assess its potential use cases and security implications.
Assessing a New Cryptocurrency Project
When exploring new blockchain projects or decentralized applications (dApps), they will often recommend or require a specific type of wallet for interaction. Knowing “which wallet is this” in the context of their recommendations allows you to choose the most compatible and secure option for engaging with their ecosystem. For example, if a project is on the Solana blockchain, you’ll need a wallet like Phantom or Solflare, not a MetaMask which is primarily Ethereum-centric.
Recovering Lost or Forgotten Access
Whether you’ve lost your phone, forgotten your password, or your computer crashed, identifying the type of wallet you were using is the first step in recovery. If it was a mobile payment wallet like Apple Pay, you’d typically rely on your device’s cloud backup or customer support. If it was a non-custodial crypto wallet, your seed phrase is the only way to regain access, underscoring the vital importance of secure backup.
Identifying Scam or Phishing Attempts
A common tactic used by scammers is to create fake wallet interfaces or prompt users to connect to malicious “wallets.” Asking “which wallet is this?” in such situations—and verifying its legitimacy—can prevent you from compromising your private keys. Always check URLs, verify app authenticity, and be wary of unsolicited requests to link your wallet. Genuine wallets from reputable developers will have consistent branding and security features.
The Future of Digital Wallets: Evolution and Integration
The digital wallet landscape is far from static. Continuous innovation is shaping its evolution, promising even more sophisticated functionalities and integrations.
Biometrics and Advanced Authentication
Expect to see a greater reliance on advanced biometric authentication methods beyond fingerprints and facial recognition. This includes behavioral biometrics and potentially even more sophisticated hardware-based identity verification, making wallets both more secure and user-friendly by reducing reliance on complex passwords.
Cross-Chain Compatibility and DeFi Integration
As the blockchain ecosystem fragments into multiple specialized chains, wallets are evolving to offer seamless cross-chain compatibility. The ability to manage assets and interact with dApps across different blockchains from a single interface will become standard. Furthermore, tighter integration with Decentralized Finance (DeFi) protocols, allowing users to earn, lend, and borrow directly from their wallets, will transform them into comprehensive financial hubs.

Regulatory Landscapes and Standardization
Governments and regulatory bodies worldwide are increasingly looking to standardize and regulate digital asset custody. This will likely lead to wallets incorporating more robust KYC (Know Your Customer) and AML (Anti-Money Laundering) features, potentially impacting the anonymity traditionally associated with certain digital assets. Standardization efforts will also aim to improve interoperability and user protection across different wallet providers. The advent of Self-Sovereign Identity (SSI) wallets, allowing users to control their digital identities and share verifiable credentials selectively, is another major trend on the horizon, moving beyond just financial assets to encompass personal data.
In conclusion, the question “which wallet is this?” serves as a gateway to understanding a critical piece of modern technology. By distinguishing between software, hardware, paper, and mobile payment wallets, and by evaluating them against key criteria like security, usability, and asset support, users can confidently navigate the digital landscape. As technology continues to advance, our digital wallets will become even more integral to our financial and personal lives, making continuous education and informed choices absolutely essential.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.