In the fast-paced ecosystem of Silicon Valley and the global technology sector, names are rarely accidental. When an engineer asks, “What’s the hurricane called?” they might not be inquiring about a meteorological event in the Atlantic. Instead, they are likely referring to a high-stakes internal project, a devastating cybersecurity breach, or a disruptive new algorithm designed to sweep through the market. In the tech world, naming is a critical component of the development lifecycle, serving as a bridge between abstract code and tangible identity.
From the codenames used by Intel and Apple to the complex taxonomies used by cybersecurity firms to identify threat actors, the “name” of a technological “hurricane” defines its impact, its lifecycle, and its place in history. This article explores the intricate world of tech naming conventions, the digital infrastructure used to track literal and figurative storms, and why the identity of a project is as important as the code itself.
The Logic of the Codename: From Silicon to Software
Before a product reaches a consumer’s hands, it exists for years under a shroud of secrecy, identified only by a codename. These names are the internal “hurricanes” of development—intense, focused bursts of energy that aim to change the landscape of the industry. The practice of using codenames serves multiple purposes: security, internal alignment, and cultural momentum.
Security Through Obscurity and Professionalism
In the early days of computing, codenames were often used to prevent industrial espionage. If a competitor overheard a developer talking about “Project Blue,” they would have no indication whether the company was working on a new database architecture or a peripheral device. Today, while corporate espionage remains a concern, the primary tech-driven reason for codenames is to prevent “leak culture” from spoiling a marketing launch. By using a name that has no semantic connection to the final product, companies like Apple and Google can maintain a level of technical abstraction that protects their intellectual property during the testing phases.
Building Internal Culture and Focus
A codename acts as a rallying cry for engineering teams. When a project is named after a powerful force of nature or a majestic geographic landmark—such as Intel’s “Lake” series (Tiger Lake, Alder Lake) or macOS’s transition from “Big Cats” to “California Landmarks”—it creates a sense of scale and ambition. These names help developers visualize the scope of the “hurricane” they are building. A name like “Project Titan” (Apple’s rumored car project) carries a different weight and expectation than “Project 123.” The naming convention provides a psychological framework that guides the development philosophy, ensuring that every line of code contributes to the specific “identity” of that release.
Digital Storms: The Architecture of Cybersecurity Naming Conventions
While internal project names represent creative energy, the tech world also has to “name” destructive forces. In the realm of digital security, “hurricanes” take the form of Advanced Persistent Threats (APTs), malware strains, and global vulnerabilities. Identifying “what the hurricane is called” in a cybersecurity context is the first step toward mitigation and defense.
The Taxonomy of Threat Actors
Cybersecurity firms have developed sophisticated systems to name the “storms” they track across the web. For instance, Microsoft recently overhauled its naming convention for threat actors to align with weather patterns. Under this system, state-sponsored groups are assigned weather-themed names: “Typhoon” for Chinese-origin actors, “Sandstorm” for Iranian-origin actors, and “Blizzard” for Russian-origin actors.
When a security analyst asks “What’s the hurricane called?”, they are looking for a specific designation like “Storm-0558.” This nomenclature isn’t just for flair; it is a data-driven approach to categorization. By associating a specific “weather event” with a set of Tactics, Techniques, and Procedures (TTPs), the tech community can rapidly share intelligence. If a system identifies a “Blizzard” signature, the automated defense protocols know exactly which firewall rules and patch sets to prioritize.
Vulnerability Databases and the CVE System
Beyond the actors themselves, the “storms” of the tech world include software vulnerabilities. The industry relies on the Common Vulnerabilities and Exposures (CVE) system, which provides a standardized “name” for every security flaw discovered. While “CVE-2023-XXXX” isn’t as evocative as “Hurricane Katrina,” it serves the same purpose in a tech environment: it creates a singular point of reference. In a world where software stacks are incredibly complex, having a universal name for a flaw ensures that developers, IT administrators, and automated security tools are all speaking the same language when a “hurricane” of exploits begins to circulate.
The High-Performance Computing Behind Real-Time Hurricane Data
The intersection of technology and naming is perhaps most literal when we look at how meteorologists and data scientists name and track actual hurricanes. The process of identifying “what the hurricane is called” is now a high-tech endeavor involving supercomputers, satellite arrays, and AI-driven predictive modeling.
Predictive Modeling and Supercomputing
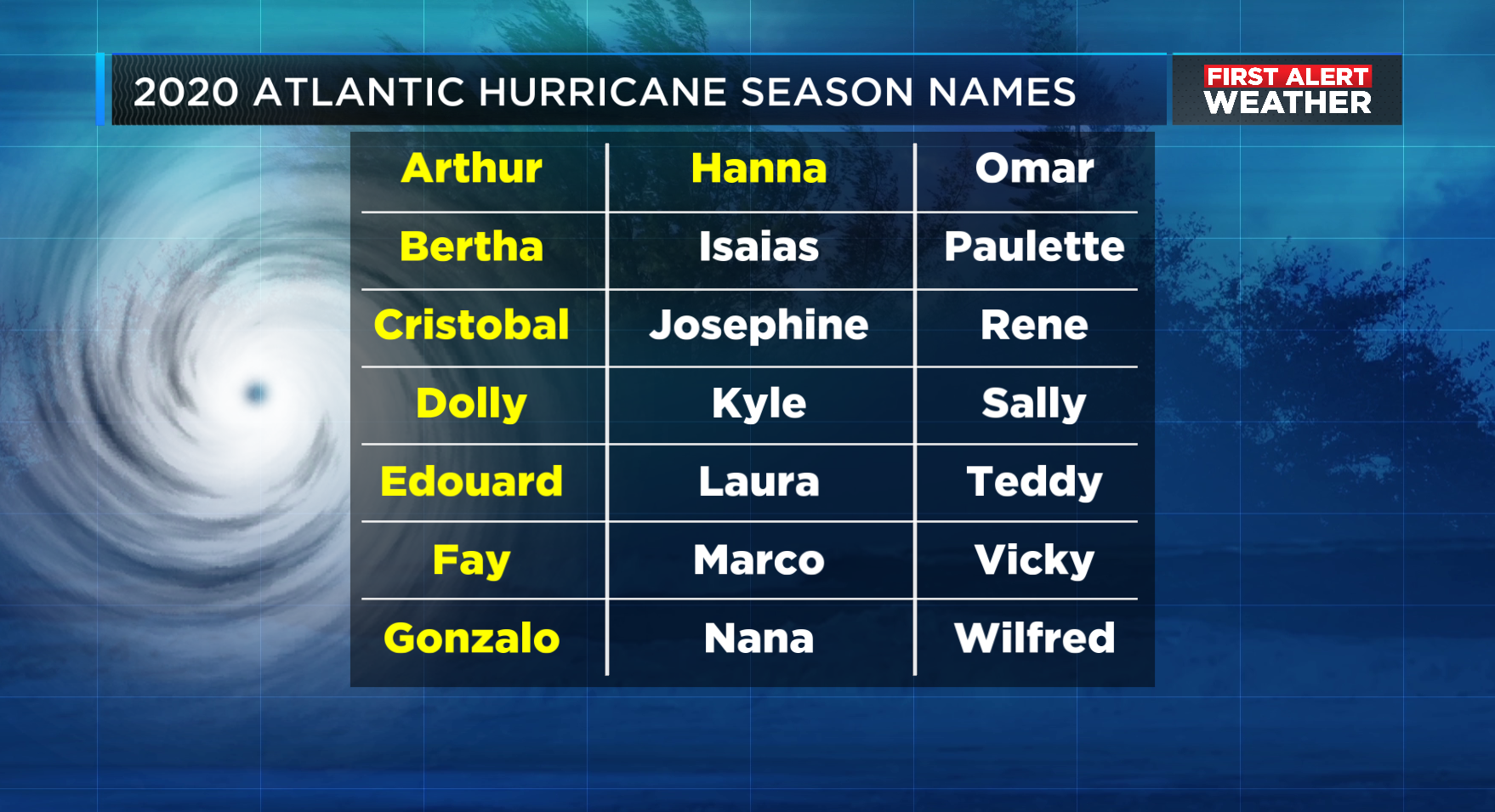
The World Meteorological Organization (WMO) manages the lists of names for tropical cyclones, but the decision of when to apply a name depends on sophisticated data thresholds. Meteorologists use High-Performance Computing (HPC) clusters to process petabytes of data from the Global Observing System. These computers run numerical weather prediction models—such as the European Center for Medium-Range Weather Forecasts (ECMWF) or the Global Forecast System (GFS)—to determine if a weather disturbance has the organized rotation and wind speed to be “named.”
In this context, the name is a data flag. Once a disturbance is named, it enters a different tier of the global data infrastructure. API calls increase, satellite imagery frequency rises, and the “storm” becomes a tracked object in thousands of digital systems. The tech behind the name allows for “ensemble forecasting,” where dozens of different scenarios are simulated simultaneously to predict the hurricane’s path with surgical precision.
AI and the Future of Automated System Identification
The next frontier in naming and tracking these storms is Artificial Intelligence. Machine learning models are now being trained to identify the “signatures” of a developing hurricane hours or even days before traditional models. By analyzing sea surface temperature, atmospheric pressure, and cloud formation patterns, AI can suggest when a tropical depression is likely to escalate into a named storm. This “Automated Identification” technology reduces the time between a threat emerging and a warning being issued, proving that in the modern world, the name of the storm is the key that unlocks a global response network.
From Development to Deployment: The Shift to Consumer Branding
The final stage of a “tech hurricane” is the transition from its internal identity to its public persona. This is where the engineering-focused codename is replaced by the consumer-facing brand. However, the tech used to arrive at these names has become increasingly sophisticated.
Data-Driven Naming and Semantic Analysis
Tech companies no longer rely solely on creative intuition to name their products. They utilize “naming tech”—software suites that perform semantic analysis, linguistic screening, and sentiment testing across dozens of languages. When a company like Google or Meta launches a new AI model (like “Gemini” or “Llama”), the name has undergone a digital gauntlet. Algorithms check for trademark conflicts, phonetic ease, and cultural connotations to ensure the “hurricane” of the new launch doesn’t cause an accidental storm of controversy.
The Role of AI in Creative Ideation
Generative AI is also changing how tech products are named. Large Language Models (LLMs) are now used by product managers to brainstorm thousands of potential names based on specific technical parameters. An LLM can be prompted to “Generate 100 names for a high-speed cloud-based data storage solution that evoke stability, speed, and the atmosphere.” This tech-driven approach to naming ensures that by the time a consumer asks, “What’s that new app called?”, the answer has been optimized for search engines (SEO), app store algorithms (ASO), and human psychology.

The Essential Power of the Name in the Digital Age
Whether it is a project codename like “Longhorn” (the infamous predecessor to Windows Vista), a cybersecurity threat like “Heartbleed,” or a literal hurricane tracked by NOAA’s supercomputers, the name is the most important metadata an object can possess. In the technology sector, a name provides order to the chaos of data. It allows humans to interface with complex systems and enables machines to categorize threats and opportunities.
Understanding “what the hurricane is called” is about more than just a label—it is about understanding the origin, the intent, and the technological framework behind the event. As we move deeper into an era defined by AI and hyper-connectivity, the names we give our digital and physical storms will continue to serve as the vital link between raw information and actionable knowledge. In the world of tech, the right name isn’t just a choice; it’s a strategic asset.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.