In the history of the internet, few platforms have ignited as much controversy or technical scrutiny as Ashley Madison. Launched in 2001, the site carved out a unique, albeit polarizing, niche in the burgeoning world of online dating. While its tagline—”Life is short. Have an affair”—focused on social taboos, its legacy is fundamentally rooted in the evolution of technology, digital security, and the ethics of data management. To understand what Ashley Madison was, one must look past the headlines of infidelity and examine the platform as a case study in specialized software architecture, the catastrophic failure of cybersecurity protocols, and the subsequent transformation of how tech companies handle user privacy.

The Engineering Behind Discretion: How the Platform Functioned
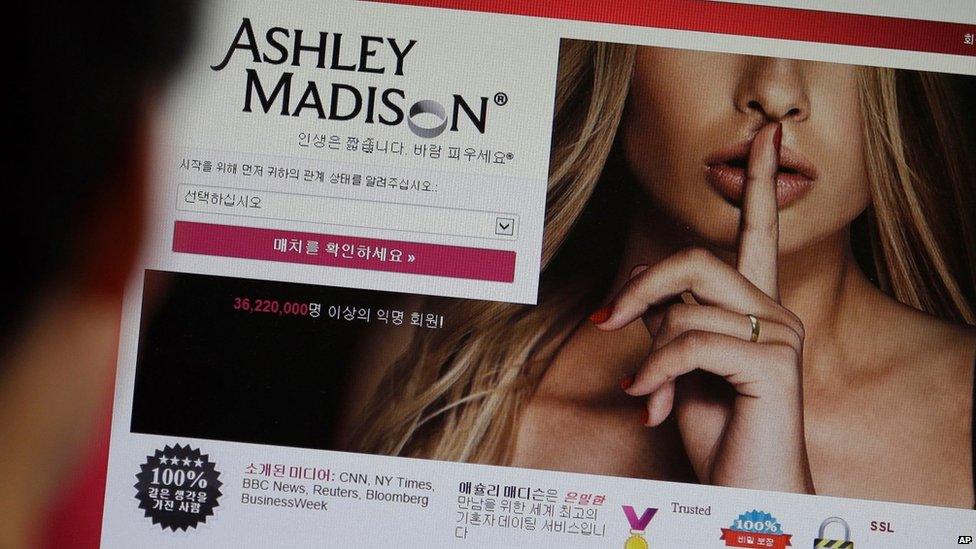
At its core, Ashley Madison was a highly specialized social networking site designed with a “privacy-first” technical mandate—or at least, the appearance of one. Unlike mainstream platforms like Facebook or Match.com, which encouraged transparency and cross-platform integration, Ashley Madison was built as a digital silo. Its architecture had to solve a specific engineering problem: how to facilitate high-volume user interaction while ensuring that the digital footprint remained invisible to anyone outside the platform.
The Credit-Based Monetization Engine
Unlike many contemporary Software-as-a-Service (SaaS) models that rely on monthly subscriptions, Ashley Madison utilized a complex credit-based system. From a technical standpoint, this required a robust transactional backend capable of micro-payments and real-time ledger updates. Users—primarily men—purchased “credits” to initiate conversations or read messages. This architecture was designed to prevent recurring “Ashley Madison” labels on bank statements, which led to the development of sophisticated payment masking scripts. The backend had to seamlessly integrate with various third-party payment processors while maintaining a layer of obfuscation, a feat of financial tech engineering that was ahead of its time for the early 2010s.
Proprietary Matching Algorithms and User Interface
The user interface (UI) of Ashley Madison was intentionally utilitarian. It lacked the “flash” of modern apps, focusing instead on search filters that allowed for granular anonymity. Users could “mask” their photos using built-in editing tools—a feature that, in the early 2010s, was a significant server-side processing task. The matching algorithms were not built for long-term compatibility but for proximity and specific “kink” tagging, requiring a database structure that prioritized geolocation data while attempting to keep that data encrypted at rest.
The Great Exposure: Analyzing the 2015 Data Breach
The defining moment in the history of Ashley Madison was not a feature rollout or a user milestone, but the 2015 data breach. This event remains one of the most significant cautionary tales in the history of information technology. It transformed the site from a niche platform into a global symbol of digital vulnerability.
The Impact Team and Technical Vulnerabilities
In July 2015, a group calling itself “The Impact Team” gained unauthorized access to the servers of Avid Life Media (ALM), the parent company of Ashley Madison. The hackers did not just steal a few passwords; they performed a wholesale extraction of the company’s entire digital infrastructure. This included the source code for the website, internal executive emails, and the personal identifiable information (PII) of over 32 million users.
From a tech perspective, the breach revealed systemic failures in the site’s security stack. The “Impact Team” allegedly gained access through an internal vulnerability—potentially a compromised employee credential or an unpatched server-side exploit. Once inside, they found that the company’s data silos were poorly segmented. Lateral movement within the network was relatively easy for the attackers, allowing them to bypass what should have been multi-layered defense-in-depth protocols.
Lessons in Database Encryption and Personal Identifiable Information (PII)
When the data was eventually dumped onto the dark web—totaling roughly 25 gigabytes—the technical community was shocked by the lack of adequate encryption. While some passwords were hashed using bcrypt (a strong hashing function), other sensitive data points, such as GPS coordinates, real names linked to credit cards, and “secret” sexual preferences, were significantly more accessible.
The breach also exposed the “Full Delete” lie. Ashley Madison had charged users a $19 fee for a “Full Delete” service, promising to wipe their data from the servers. The leak proved that the company had retained the data anyway, likely to maintain their user-count metrics. This highlighted a massive failure in data lifecycle management—a technical discipline that dictates how and when data should be purged from a system.
The “Fembot” Phenomenon: Algorithmic Deception in Early AdTech
Perhaps the most fascinating technical revelation following the 2015 hack was the discovery of “fembots.” Data analysts who combed through the leaked source code found that the platform was populated by thousands of sophisticated automated scripts designed to mimic female users.
Automating Engagement via Scripted Profiles
These were not mere static fake profiles. The “fembots” were programmed with “engager” code—algorithms designed to message new male users automatically. When a man signed up, a script would trigger a message from a nearby “female” profile, enticing him to buy credits to reply. The code for these bots included randomized delay timers to make the responses appear human and “personality” scripts that rotated through various greeting styles.
This was an early and malicious application of what we now call “engagement bots.” From a software engineering perspective, it was an efficient way to solve the “cold start problem” (where a platform lacks enough active users to keep new users engaged). However, it was built on a foundation of technical fraud, using code to manipulate human psychology for financial gain.
The Ethics of AI and Automated Interactions
The Ashley Madison bot scandal served as a precursor to modern debates regarding AI ethics and transparency. It raised the question: what is the responsibility of a developer when creating an automated agent? The Ashley Madison codebases showed that the bots were programmed to stop communicating once a user had spent a certain amount of credits, or to avoid talking to “paid” users who might catch on to the ruse. This level of algorithmic manipulation set the stage for later regulations regarding “bot disclosure” in various jurisdictions.
Cybersecurity Post-Ashley Madison: A Paradigm Shift for the Tech Industry
The fallout of Ashley Madison’s tech failure was so immense that it forced an industry-wide rethink of digital security. No longer was security seen as a “cost center”; it became a core business requirement.
From Reactive to Proactive Security Protocols
Before the 2015 breach, many companies viewed cybersecurity as a reactive measure—something you addressed after a virus or a minor leak. The Ashley Madison event proved that a single breach could be an extinction-level event for a brand. This led to the widespread adoption of “Security by Design.”
Developers began integrating security into the earliest stages of the Software Development Life Cycle (SDLC). We saw a surge in the use of:
- Zero-Trust Architecture: Assuming that any user or system, even those inside the network, could be compromised.
- Mandatory Multi-Factor Authentication (MFA): Moving away from simple password-based logins.
- Advanced Hashing: Making bcrypt and Argon2 the industry standards for password storage.
The Legacy of Anonymity in a Traceable World
Today, Ashley Madison still exists, but it operates in a vastly different technological landscape. It has been forced to adopt extreme transparency regarding its security measures, undergoing regular third-party audits and employing much more sophisticated encryption methods.
The story of “what was Ashley Madison” is ultimately the story of the end of digital innocence. It taught the tech world that data is a liability, not just an asset. It highlighted that “deleting” data must be a physical and logical reality, not just a UI button. For modern developers and IT professionals, the Ashley Madison breach remains the ultimate case study in why the integrity of the backend is just as important as the functionality of the frontend. In an era where AI and automated scripts are becoming the norm, the lessons of the Ashley Madison “fembots” and their flawed security architecture continue to inform how we build, secure, and trust the digital tools we use every day.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.