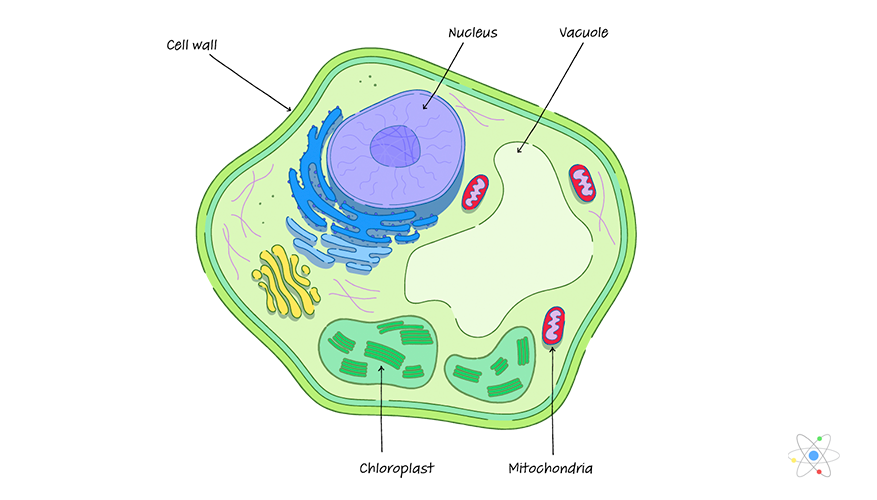
In biology, the cell wall serves as a rigid structural layer surrounding certain types of cells, providing them with structural support and protection. In the rapidly evolving landscape of information technology, we have adopted this biological imperative as a foundational principle for digital safety. The “cell wall” of a tech ecosystem—comprising firewalls, sandboxing protocols, and Zero Trust architectures—serves a nearly identical purpose: it defines the boundaries of the system, protects the sensitive “organelles” (data and processes) within, and regulates the exchange of information with the outside world.
As cyber threats become more sophisticated, understanding the purpose and evolution of these digital perimeters is no longer just a task for network engineers; it is a critical strategic requirement for any organization operating in the digital age. This article explores the multi-faceted roles of the digital cell wall, from its traditional roots in network security to its modern incarnation in cloud-native environments and AI-driven defense systems.
The Architectural Necessity: Defining the Perimeter in an Interconnected World
At its most basic level, the purpose of a digital cell wall is to create a distinction between the “internal” and the “external.” In the early days of computing, this was a relatively straightforward task. A company’s servers lived in a physical room, and the network was bounded by physical cables. However, in the era of hyper-connectivity, the perimeter has become fluid, necessitating a more robust and intelligent form of structural integrity.
From Hardware Barriers to Cloud-Native Security
The first generation of digital cell walls were primarily hardware-based firewalls. These devices acted as the gatekeepers of the network, using static rules to determine which packets of data were allowed to enter or exit. While effective for their time, these rigid structures struggled to adapt to the rise of cloud computing and remote work.
Today, the “cell wall” has transitioned into a software-defined perimeter (SDP). This transition allows security protocols to move with the workload. Whether a process is running on a local server or a distributed cloud instance, the digital cell wall ensures that the same level of structural protection is applied. This flexibility is the hallmark of modern tech infrastructure, allowing companies to scale their digital operations without leaving their internal “cytoplasm” exposed to the vacuum of the open internet.
The Role of Packet Filtering and Stateful Inspection
Just as a biological cell wall is selectively permeable, a digital perimeter must be able to distinguish between vital nutrients (legitimate traffic) and toxins (malicious data). This is achieved through sophisticated packet filtering and stateful inspection. Modern firewalls do not just look at where a packet is coming from; they analyze the context of the communication.
By maintaining a “state table” of active connections, the digital cell wall can recognize if an incoming packet is part of an established, safe conversation or a rogue attempt to breach the system. This level of granular control is the primary purpose of the network perimeter, ensuring that the system remains open for business while remaining closed to intruders.
Structural Integrity: Sandboxing, Containerization, and Process Isolation
While the external perimeter protects the organization as a whole, the concept of a “cell wall” is also applied internally through isolation technologies. In a complex software ecosystem, if one component is compromised, the goal is to prevent that compromise from spreading to the rest of the system. This is the digital equivalent of compartmentalization.
Isolating Processes via Virtualization and Sandboxing
Sandboxing is one of the most effective uses of a digital cell wall in software development and security. By creating a restricted environment—a “sandbox”—a program can be executed without the risk of it affecting the underlying operating system or other applications. This is a critical purpose of modern browser architecture and mobile operating systems.
When you open a suspicious attachment or run an unverified app, the digital cell wall of the sandbox ensures that any malicious code is “contained.” It can see the resources it needs to function, but it cannot breach the walls to access the core memory or file system. This isolation is what keeps modern computing environments stable and resilient in the face of constant software vulnerabilities.
Kubernetes and the Microservices Mesh
In the world of enterprise DevOps, the “cell wall” has taken the form of containers. Technologies like Docker and orchestration platforms like Kubernetes allow developers to wrap their code in a protective layer that includes everything the application needs to run.
These containers act as individual cells within a larger organism. If one microservice fails or is attacked, the containerization ensures that the failure is isolated. The “purpose” here is two-fold: security and stability. By enforcing strict boundaries between different parts of an application, tech architects can ensure that the “organism” as a whole continues to function even if individual cells are undergoing maintenance or experiencing issues.
Defense-in-Depth: The Evolution of Zero Trust Architecture
For decades, the philosophy of IT security was “crunchy on the outside, soft on the middle.” Once you bypassed the “cell wall” of the firewall, you had free rein over the network. Modern technology has moved away from this flawed model toward “Zero Trust,” where the purpose of the cell wall is replicated at every single layer of the stack.
Moving Beyond the Traditional Perimeter
The traditional perimeter is no longer sufficient because the “inside” of the network is no longer a safe zone. Employees access data from coffee shops, and third-party vendors plug into corporate APIs. In this environment, the purpose of the cell wall shifts from being a single outer shell to becoming a series of internal membranes.
Zero Trust operates on the principle of “never trust, always verify.” Every user, device, and application must prove its identity and authorization every time it requests access to a resource. In this context, the “wall” is not a physical or even a network barrier, but a logical one. It is a continuous enforcement of policy that prevents unauthorized lateral movement within the system.
Identity as the New Perimeter
In the modern tech stack, identity has become the most important component of the digital cell wall. Multi-factor authentication (MFA), Single Sign-On (SSO), and Identity and Access Management (IAM) systems serve as the sophisticated sensors of the cell wall.
These tools verify that the entity attempting to cross the boundary is who they claim to be. By focusing on identity, organizations can maintain a “cell wall” that is both highly secure and completely transparent to the user. This represents the pinnacle of modern digital architecture: a barrier that is invisible to legitimate users but impenetrable to attackers.
The Adaptive Membrane: AI-Driven Security and the Future of Defense
As we look toward the future, the purpose of the digital cell wall is evolving from a static barrier into an adaptive, “living” membrane. The integration of Artificial Intelligence (AI) and Machine Learning (ML) into security protocols is changing how we define and defend digital boundaries.
Real-Time Threat Detection and Autonomous Response
A biological cell wall can sometimes repair itself or change its permeability based on environmental stress. AI-driven security systems are bringing this capability to technology. Modern “Extended Detection and Response” (XDR) platforms use AI to monitor traffic patterns across the entire digital ecosystem.
When the system detects an anomaly—such as a sudden exfiltration of data or a login attempt from an unusual location—it can autonomously “harden” the cell wall in real-time. It might shut down specific ports, isolate affected containers, or require additional authentication factors. The purpose of the wall here is not just to block, but to react and adapt to threats as they emerge, often before a human administrator is even aware of the problem.
The Intersection of Machine Learning and Network Protection
The future of the digital cell wall lies in predictive defense. By analyzing vast amounts of historical data, machine learning models can predict where a breach is likely to occur and reinforce those specific “membranes” in advance.
This move from reactive to proactive security is the ultimate fulfillment of the “cell wall” metaphor. It provides a structural integrity that is not just a passive shield, but an active participant in the health and survival of the digital organism. As we move deeper into the era of the Internet of Things (IoT) and edge computing, these intelligent, decentralized cell walls will be the only thing standing between a secure global network and digital chaos.
In conclusion, the purpose of a cell wall in the tech world is to provide the structure, isolation, and protection necessary for complex systems to thrive. From the early days of simple firewalls to the future of AI-driven, self-healing perimeters, the “wall” remains the most fundamental concept in system architecture. By understanding and implementing these layers of defense, tech leaders can ensure that their digital assets remain secure, resilient, and ready for the challenges of tomorrow.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.