In the rapidly evolving landscape of information technology, the metaphors we borrow from biological health are becoming increasingly relevant. We talk about “viruses,” “infections,” and “digital hygiene” as common parlance. However, just as a hospital distinguishes between a quick wipe-down and a pressurized autoclave, IT professionals must distinguish between different levels of system maintenance and security.
Understanding the difference between cleaning, disinfecting, and sterilizing in a digital context is not just a matter of semantics—it is a critical framework for cybersecurity, system performance, and data privacy. In this guide, we will explore how these three tiers of “sanitation” apply to software, hardware, and network environments to ensure peak operational integrity.

Digital Cleaning: The Maintenance of System Performance and Efficiency
In the world of technology, “cleaning” is the most fundamental level of maintenance. Much like physical cleaning removes visible dirt and dust, digital cleaning focuses on removing “bloat”—the non-essential data, temporary files, and redundant code that accumulate over time. While cleaning does not necessarily remove malicious threats, it is essential for the “health” and speed of a system.
The Role of Cache Management and Temporary Files
Every time a user browses the web or runs a complex software suite like Adobe Creative Cloud or a CAD program, the system generates temporary files. These files are designed to speed up immediate tasks, but when left unchecked, they become “digital dust.”
Digital cleaning involves the systematic removal of:
- Browser Caches: Stale data that can cause rendering errors or slow down load times.
- System Logs: Log files that have grown to unmanageable sizes, consuming valuable disk space.
- Temporary Directories: Files left behind by installers or crashed applications.
By performing regular cleaning, organizations reduce their “Technical Debt.” A clean system responds faster, experiences fewer application conflicts, and provides a clearer baseline for monitoring more serious issues.
Code Refactoring and Database Optimization
For software developers and database administrators, cleaning takes the form of refactoring and indexing. Code “smells”—redundant loops, unused variables, and deprecated libraries—act as clutter. Refactoring is the process of cleaning the internal structure of the code without changing its external behavior.
Similarly, database cleaning (or “scrubbing”) involves removing duplicate entries and optimizing indexes. Without this level of cleaning, queries become sluggish, and the system’s energy consumption increases. In the era of Green Computing, regular digital cleaning is a primary strategy for reducing the carbon footprint of data centers.
Digital Disinfecting: Targeted Remediation of Security Threats
If cleaning is about performance, “disinfecting” is about safety. In a tech ecosystem, disinfecting refers to the identification and removal of malicious software (malware), viruses, and unauthorized scripts that have compromised a system’s integrity. Unlike cleaning, which targets harmless clutter, disinfecting targets active threats that intend to steal data or disrupt service.
Malware Removal and System Remediation
When a system is “infected” with a Trojan or a worm, a simple cleaning of temporary files will not suffice. Disinfecting requires specialized tools—such as Endpoint Detection and Response (EDR) platforms—that can scan the deep layers of the operating system.
The process of disinfecting involves:
- Identification: Using heuristic analysis to find patterns of malicious behavior.
- Quarantine: Isolating the infected file or process to prevent it from spreading to the rest of the network.
- Neutralization: Deleting the malicious code while attempting to repair the damage done to the original host files.
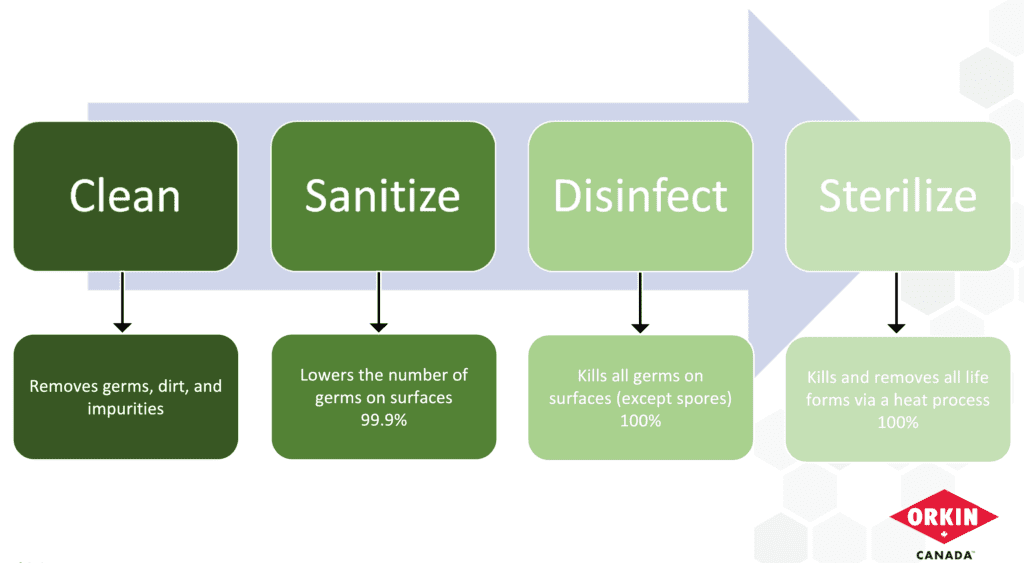
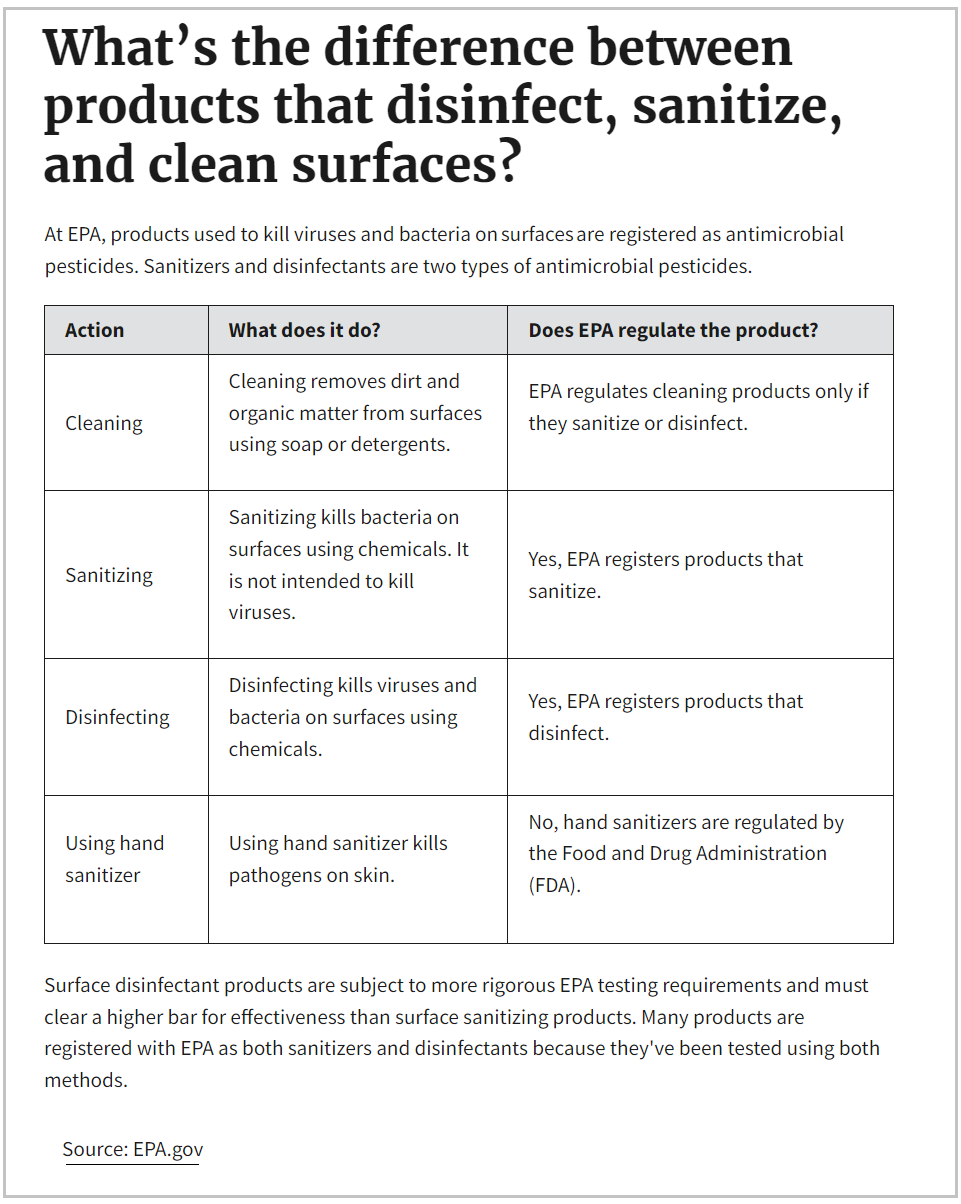
It is important to note that disinfecting is often an “imperfect” science. Just as a biological disinfectant might kill 99.9% of germs, a digital disinfectant might remove the primary malware but leave behind “hooks” in the registry or modified system settings. This is why disinfecting is usually followed by a rigorous audit to ensure the threat has been fully neutralized.
Patching Vulnerabilities as a Preventive Disinfectant
In many ways, software patching acts as a proactive disinfectant. When a vendor like Microsoft or Apple releases a security patch, they are effectively “disinfecting” a known vulnerability before it can be exploited.
Organizations that fail to implement a robust Patch Management lifecycle are essentially leaving their digital surfaces “unwashed,” making them breeding grounds for exploits. Disinfecting in the tech world is a constant cycle of monitoring for new vulnerabilities (CVEs) and applying the necessary “antidotes” to keep the environment safe from lateral movement by hackers.
Digital Sterilizing: Total Data Erasure and Secure Wiping
In the medical world, sterilization is the total elimination of all microbial life. In the technology sector, “sterilizing” refers to the absolute destruction of data on a storage medium so that it can never be recovered. This is a critical step for hardware decommissioning, compliance with data privacy laws (like GDPR or HIPAA), and high-security environments.
The Difference Between Deleting and Sterilizing
Many users mistakenly believe that hitting “Delete” or formatting a hard drive is equivalent to sterilization. In reality, these actions merely remove the “pointers” to the data, leaving the actual bits and bytes intact on the disk. A technician with basic data recovery software can easily “resurrect” this data.
Digital sterilization, often called “Data Wiping” or “Sanitization,” uses sophisticated algorithms to overwrite the entire drive multiple times. Common standards include:
- Zero-Fill: Overwriting every bit with a ‘0’.
- DoD 5220.22-M: A three-pass process that overwrites data with zeros, ones, and random characters.
- NIST SP 800-88: The current gold standard for media sanitization, which includes methods like “Purge” and “Destroy.”
Sterilizing ensures that even if the hardware falls into the hands of a sophisticated state actor or a data thief, there is no “digital DNA” left to recover.
Physical Destruction and Cryptographic Erasure
In cases where the data is extremely sensitive, sterilization may move from software-based wiping to physical destruction. This includes degaussing (using high-powered magnets to disrupt the drive’s magnetic field) or physical shredding of the SSD or HDD into tiny particles.
A more modern approach to sterilization is Cryptographic Erasure (Crypto-Erase). In this method, the data on the drive is encrypted by default. To “sterilize” the drive, the encryption key is permanently deleted (shredded). Without the key, the data on the drive becomes mathematically impossible to recover, effectively rendering the drive sterile for any future user. This is particularly useful in cloud computing environments where physical destruction of a shared server is not possible.
Implementing a Comprehensive Hygiene Strategy in Your Tech Stack
To maintain a resilient IT infrastructure, a business cannot choose just one of these processes; they must implement all three as part of a tiered maintenance strategy. A failure to distinguish between these levels can lead to either wasted resources or catastrophic security breaches.
Automation and AI in the Sanitation Lifecycle
The modern tech stack is too large for manual cleaning and disinfecting. High-performing organizations utilize automation to handle these tasks:
- Automated Cleaning: Using scripts or tools like CCleaner Cloud or native OS maintenance tasks to clear logs and temp files weekly.
- Continuous Disinfecting: Utilizing AI-driven Security Information and Event Management (SIEM) systems that detect and disinfect threats in real-time, often before a human analyst is even aware of the breach.
- Policy-Driven Sterilization: Implementing MDM (Mobile Device Management) policies that allow for “Remote Wipe” capabilities. If an employee loses a corporate laptop, the IT department can remotely “sterilize” the device to protect corporate secrets.
Scaling Hygiene for Cloud and Distributed Systems
As companies move toward serverless architectures and microservices, the concepts of cleaning, disinfecting, and sterilizing change. In a “containerized” environment (like Docker or Kubernetes), instead of disinfecting an infected container, the standard practice is to “kill” it and spin up a new, “clean” one from a golden image.
This “disposable infrastructure” approach is the ultimate form of digital hygiene. It assumes that systems will eventually become cluttered or compromised, and rather than spending hours cleaning or disinfecting them, the system is designed to be “sterilized” and replaced instantly.
Conclusion: The Hierarchy of Digital Health
Understanding the difference between cleaning, disinfecting, and sterilizing is fundamental to modern technical literacy.
- Cleaning keeps your systems fast and efficient, preventing the “digital rot” that slows down productivity.
- Disinfecting protects your systems from active threats, ensuring that your data remains uncorrupted and your operations remain secure.
- Sterilizing provides the ultimate level of privacy and compliance, ensuring that when data or hardware reaches its end-of-life, it leaves no trace behind.
By applying these three levels of care to your technology ecosystem, you move beyond mere “IT support” and into the realm of true digital resilience. Whether you are managing a single workstation or a global network of data centers, practicing rigorous digital hygiene is the only way to ensure long-term stability in an increasingly complex tech world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.