In the modern era of hyper-connectivity, we often take for granted the seamless exchange of data that occurs when we send an instant message, stream a high-definition video, or refresh a webpage. Behind these daily digital interactions lies a complex infrastructure of protocols and hardware. At the very heart of this infrastructure is a concept fundamental to software engineering and network administration: the network socket.
Understanding what a socket is, how it functions, and why it is essential is critical for anyone looking to navigate the fields of software development, cybersecurity, or system architecture. Simply put, if the internet is a global highway system, sockets are the specific loading docks where data is packed, sent, received, and unpacked.
Understanding the Fundamentals: What Exactly is a Socket?
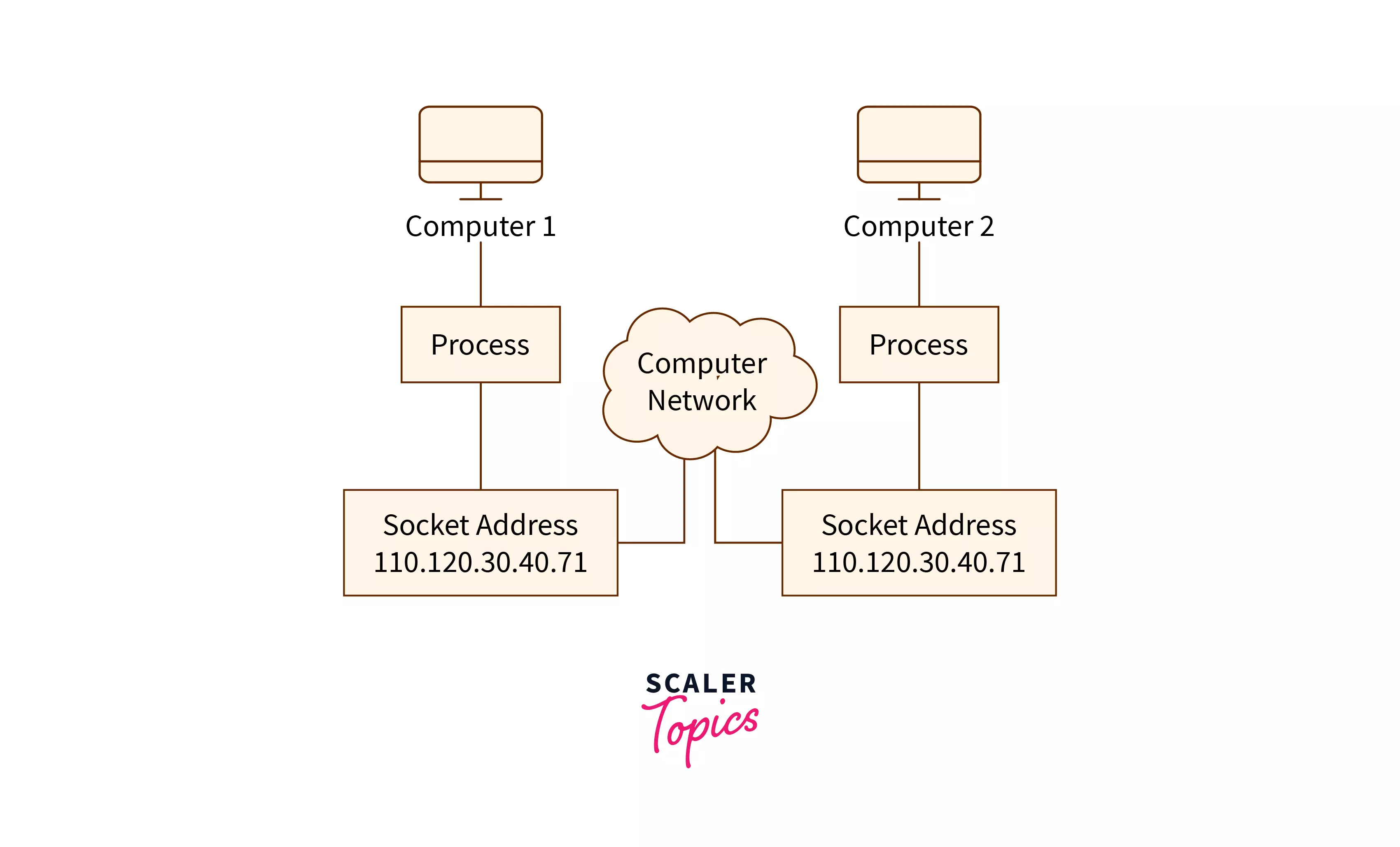
To understand a socket, one must first look at how two computers “talk” to one another. In the realm of networking, a socket is one endpoint of a two-way communication link between two programs running on the network. A socket is bound to a port number so that the TCP layer can identify the application that data is destined to be sent to.
The IP Address and Port Combination
A socket is defined by a unique combination of two critical components: an IP address and a port number. While the IP address identifies a specific machine on a network (much like a street address identifies a building), the port number identifies a specific process or service running on that machine (much like a specific apartment number within that building).
When a program wants to communicate, it opens a socket. This socket acts as a software interface that allows the application to plug into the network. Without the port number, the incoming data would reach the computer but wouldn’t know which application (e.g., Chrome, Zoom, or Spotify) should receive it.
The Analogy of the Apartment Building
To visualize this, imagine a large apartment complex. The street address (123 Tech Lane) is the IP address. If you send a letter to that address, it arrives at the building’s lobby. However, the letter cannot be delivered to the final recipient unless it includes an apartment number (e.g., Apt 4B). In this scenario, Apt 4B is the port. The “socket” is the actual doorway of Apartment 4B—the point where the package is handed from the hallway (the network) into the private residence (the application).
How Sockets Facilitate Two-Way Communication
Communication is rarely a one-way street. Sockets are designed for “full-duplex” communication, meaning data can flow in both directions simultaneously. When a connection is established between a client (your browser) and a server (a website’s host), two sockets are involved: one on your machine and one on the remote server. This pairing allows for a continuous stream of requests and responses.
The Anatomy of Socket Communication: TCP vs. UDP
In the world of technology, not all data is treated equally. Some data must arrive perfectly intact, while for other types, speed is more important than perfection. This lead to the development of two primary types of socket-based communication protocols.
Stream Sockets (TCP) – Reliability First
Stream sockets use the Transmission Control Protocol (TCP). These are “connection-oriented” sockets. Before any data is sent, a formal “handshake” occurs between the sender and the receiver to ensure both parties are ready.
TCP sockets are designed for reliability. If a packet of data goes missing or arrives out of order, the protocol automatically requests a retransmission. This makes TCP sockets the gold standard for applications where data integrity is non-negotiable, such as web browsing (HTTP/HTTPS), file transfers (FTP), and email (SMTP).
Datagram Sockets (UDP) – Speed and Efficiency
Datagram sockets use the User Datagram Protocol (UDP). Unlike TCP, UDP is “connectionless.” It does not establish a formal handshake or check if the receiver is ready; it simply sends the data packets (datagrams) into the network.
While this may sound unreliable, it is incredibly fast because it lacks the overhead of error checking. Datagram sockets are essential for real-time applications where a slight delay is worse than a minor data loss. Examples include online gaming, live video streaming, and Voice over IP (VoIP). In a fast-paced shooter game, you care more about where your opponent is now than receiving a delayed packet about where they were two seconds ago.
Raw Sockets – For the Specialized Network Engineer
Beyond the standard TCP and UDP, there are “Raw Sockets.” These bypass the usual transport layer formatting and allow an application to communicate directly with the lower levels of the network stack. Raw sockets are typically used by security professionals for packet sniffing, network monitoring, or developing custom protocols. They provide a level of control that is powerful but requires significant expertise to manage securely.
The Lifecycle of a Socket Connection
For a developer or a network engineer, understanding the lifecycle of a socket is key to troubleshooting connectivity issues. The process differs slightly depending on whether the machine is acting as a “Server” (waiting for data) or a “Client” (requesting data).
The Server-Side Workflow: Listen, Bind, and Accept
A server must always be ready to receive. The process follows these steps:
- Socket Creation: The server initializes a new socket.
- Bind: The socket is “bound” to a specific IP and port (e.g., port 80 for a web server).
- Listen: The server enters a passive state, listening for incoming connection requests from clients.
- Accept: When a request arrives, the server “accepts” it, creating a new dedicated socket to handle that specific client while the original socket goes back to listening.
The Client-Side Workflow: Create and Connect
The client (such as your smartphone) initiates the action:
- Socket Creation: The client initializes its own socket.
- Connect: The client sends a request to the server’s specific IP and port. If using TCP, this initiates the three-way handshake (SYN, SYN-ACK, ACK).
The Data Exchange and Termination Phase
Once the connection is established, both parties use send and receive (or read and write) functions to move data back and forth. When the task is complete—for example, when a webpage has finished loading—the sockets are “closed.” This releases the port and the memory resources back to the operating system. If a socket is not closed properly, it can lead to “resource leaks,” which can eventually crash a system.
Real-World Applications and the Role of Sockets in Modern Tech
Sockets are not just a theoretical concept; they are the engine under the hood of every modern software application. As technology trends shift toward the cloud and distributed systems, the importance of efficient socket management has only grown.
Powering the World Wide Web (HTTP/HTTPS)
Every time you enter a URL, your browser opens a socket to connect to a web server. While we now use higher-level abstractions like REST APIs or GraphQL, these are all ultimately built on top of standard TCP sockets. The transition from HTTP/1.1 to HTTP/2 and HTTP/3 has focused heavily on how sockets are managed, allowing multiple requests to be multiplexed over a single socket to increase loading speeds.
Real-Time Applications: WebSockets
A major trend in modern web development is the move away from “stateless” connections to “persistent” ones. Standard HTTP sockets close after a single request. However, “WebSockets” allow for a persistent, open connection between a browser and a server. This is what allows a chat app to show “User is typing…” in real-time or a stock market dashboard to update prices instantly without the user needing to refresh the page.
API Development and Microservices Architecture
In modern tech environments, monolithic applications are being replaced by microservices—hundreds of small programs that need to talk to each other. These services often reside on different servers or containers. Sockets (specifically Inter-Process Communication or IPC sockets) are the primary way these microservices exchange data, ensuring that a “purchase” service can talk to an “inventory” service instantly and securely.
Sockets and Digital Security: Protecting the Endpoints
From a digital security perspective, every open socket is a potential doorway into a system. If a developer leaves a socket open on a port that isn’t properly monitored or encrypted, it becomes a vulnerability.
The Risks of Exposed Ports
Hackers use tools like Nmap to perform “port scanning.” This process involves sending requests to various ports to see which ones have “listening” sockets. An exposed socket on a sensitive port (like port 22 for SSH or port 3389 for Remote Desktop) can be a goldmine for attackers looking to gain unauthorized access. System administrators must use firewalls to ensure that only necessary sockets are reachable from the public internet.
Implementing Secure Sockets (SSL/TLS)
Because standard sockets send data in “cleartext,” anyone sitting between the sender and receiver could potentially intercept and read the data. This is why the Tech industry moved toward Secure Sockets Layer (SSL) and its successor, Transport Layer Security (TLS). These protocols wrap standard socket communication in a layer of encryption, ensuring that even if the data is intercepted, it remains unreadable.
Best Practices for Developers
For those building software, modern security dictates a “least privilege” approach to sockets. Developers should:
- Only open sockets when necessary.
- Ensure all socket communication is encrypted via TLS.
- Implement timeouts to prevent “slowloris” attacks, where an attacker opens many sockets but sends data very slowly to exhaust the server’s resources.
- Regularly audit which ports are listening on their production servers.
Conclusion
The network socket is one of the most elegant and enduring concepts in computer science. By combining the identity of a machine (IP) with the identity of a process (Port), sockets provide a universal method for disparate systems to collaborate. Whether it is the reliability of a TCP stream ensuring your bank transfer is accurate, or the speed of a UDP datagram enabling a lag-free gaming experience, sockets are the invisible threads that weave the modern internet together. As we move further into the era of AI, IoT, and edge computing, the mastery of socket-based communication remains a foundational skill for any tech professional.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.