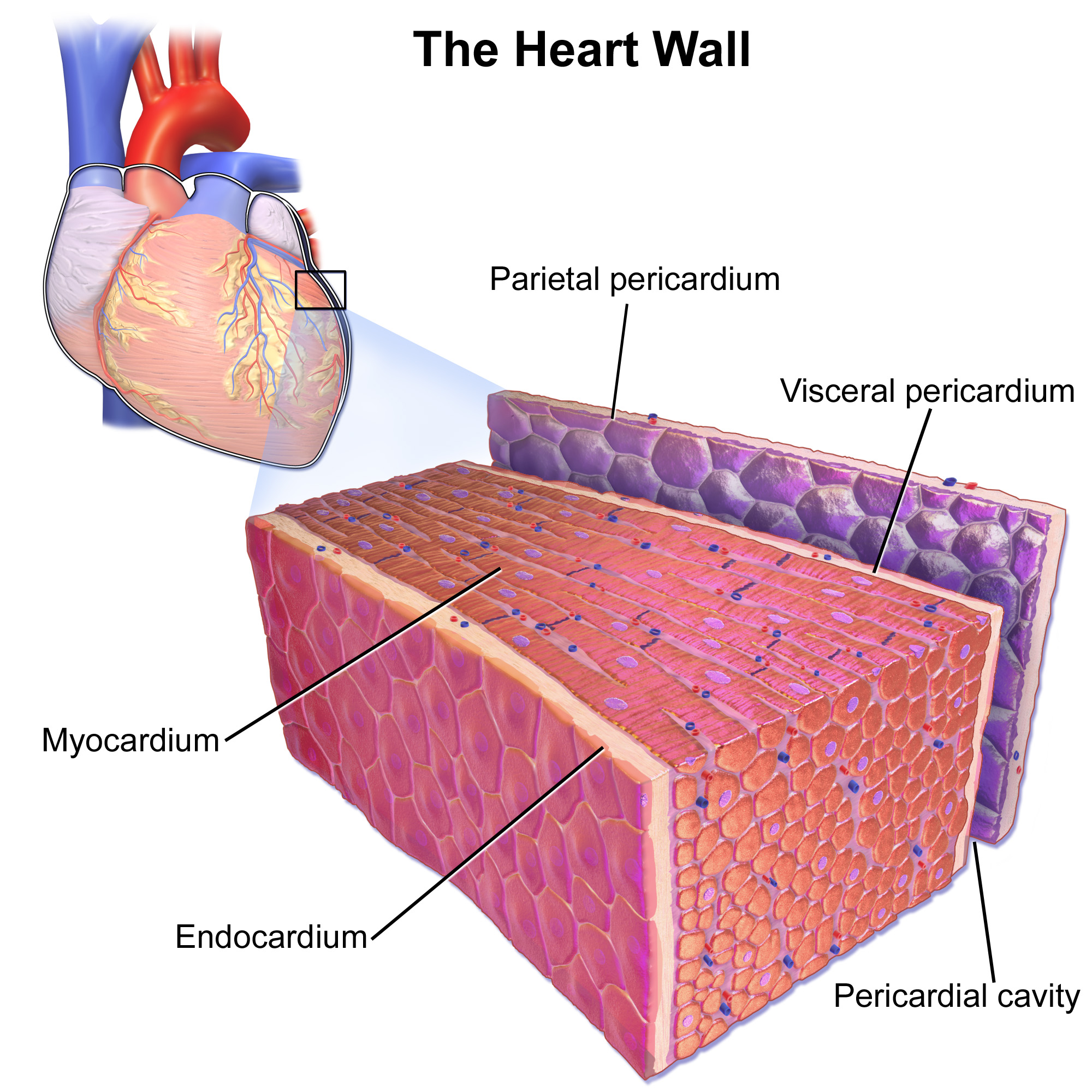
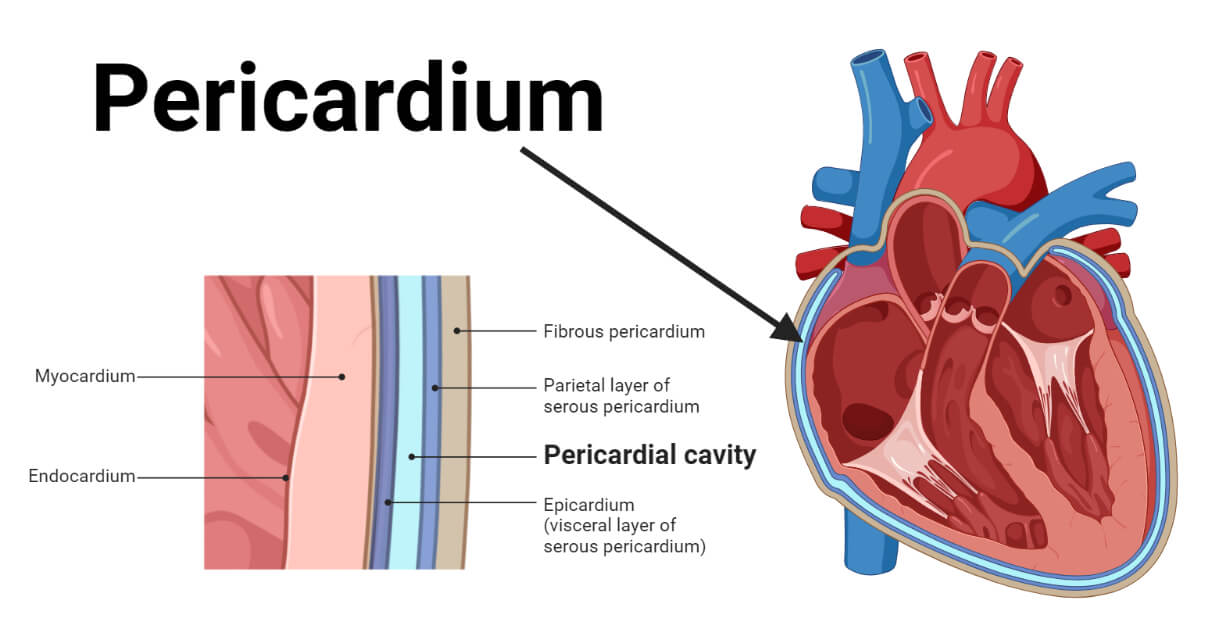
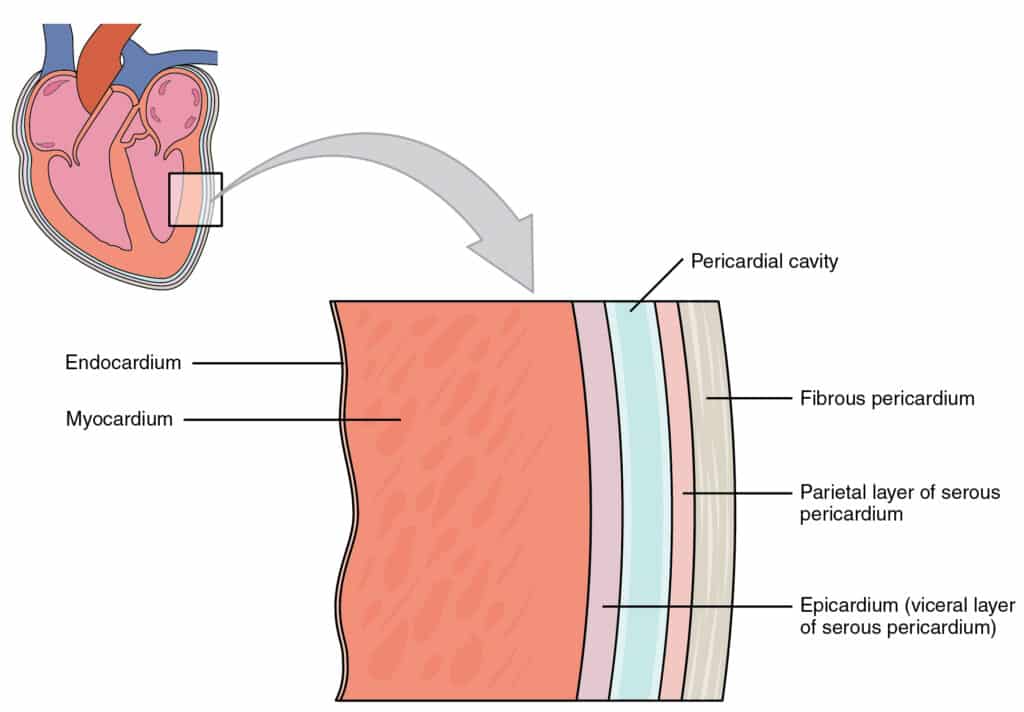
In the biological world, the pericardial cavity is the fluid-filled space between the layers of the pericardium that surrounds the heart, providing lubrication and protection against infection while allowing the heart the freedom to expand and contract. In the rapidly evolving landscape of technology, we have begun to mirror this biological masterstroke. When we ask “What is the pericardial cavity?” in a technological context, we are referring to the specialized, protective environments—both hardware and software—that encapsulate a system’s most vital components to ensure operational integrity, security, and performance.
Modern computing systems have moved away from monolithic structures toward compartmentalized architectures. Just as the heart cannot function if it is fused to the chest wall, a modern software application or a secure processing unit cannot function optimally if it is directly exposed to the friction and vulnerabilities of the general operating environment. This article explores the “digital pericardial cavity” through the lenses of containerization, hardware-level security enclaves, and the future of isolated computing.
The Software Pericardium: Containerization and Virtualization
The most direct technological equivalent to the pericardial cavity is found in the realm of software architecture, specifically through containerization and abstraction layers. In traditional computing, an application ran directly on the Operating System (OS). If the application crashed or was compromised, the friction could cause the entire system to fail. Today, we use “cavities” to prevent this.
The Rise of Docker and Kubernetes as Protective Layers
Docker revolutionized the way we think about the environment in which an application lives. By creating a “container,” developers provide a specific, isolated space that contains everything the software needs to run—code, runtime, system tools, and libraries. This container acts as the visceral layer of the pericardium, moving with the application wherever it goes.
Kubernetes, on the other hand, acts as the broader system of management. It ensures that these containers (the “hearts” of the digital service) have the necessary space to breathe, scale, and recover. This isolation ensures that even if one service experiences a surge in “heart rate” (traffic spikes), it does not disrupt the neighboring services, effectively maintaining the systemic equilibrium of the entire cloud infrastructure.
Sandboxing as a Defensive Barrier
Beyond enterprise-level containers, sandboxing represents a critical “pericardial” layer for consumer tech. When you open a PDF in a modern browser or run an app on a smartphone, the system places that process in a sandbox. This is a restricted environment where the application can execute its functions without having permission to access the “vital organs” of the device, such as the core file system or the microphone, unless specifically authorized. This digital fluid—the restrictions and protocols of the sandbox—prevents malicious code from “infecting” the rest of the system.
Microservices and the Decoupling of Logic
The move from monolithic software to microservices is essentially the biological evolution of a complex organism. By breaking a large program into smaller, independent services, engineers create multiple “cavities” of operation. Each service is isolated, meaning a failure in the “payment service” (the pericardial equivalent of a localized issue) does not necessarily lead to a total “cardiac arrest” of the entire e-commerce platform.
Hardware Enclaves: The Physical Membrane of Security
While software provides a logical cavity, hardware manufacturers have developed physical “pericardial” structures to protect sensitive data at the silicon level. In an era of rampant cyber-warfare, protecting data while it is “at rest” (stored) or “in transit” (moving across networks) is no longer enough; we must protect data while it is “in use.”
Trusted Execution Environments (TEEs)
A Trusted Execution Environment is a secure area of a main processor. It provides an isolated environment that runs alongside, but is separate from, the main Operating System. Think of this as the ultimate pericardial cavity for data. Even if a hacker gains total control over your Android or Windows OS, they cannot “reach through the membrane” into the TEE. This is where your biometric data (fingerprints, face ID) and encryption keys are stored. The TEE ensures that the “heart” of your identity remains untouched by the vulnerabilities of the general-purpose processing environment.
Apple’s Secure Enclave and Intel SGX
Apple’s “Secure Enclave” is perhaps the most famous consumer-facing version of this technology. It is a dedicated coprocessor that handles the most sensitive cryptographic operations. Similarly, Intel Software Guard Extensions (SGX) allow developers to partition their code into “enclaves,” which are protected areas of execution in memory. These enclaves are invisible to the OS, the BIOS, and even the hypervisor. By creating this physical and logical gap, hardware designers have built a literal pericardium for bits and bytes, ensuring that the most critical computations remain lubricated and protected from external interference.
Hardware Security Modules (HSM) in the Cloud
For large-scale enterprises and financial institutions, the “pericardial cavity” takes the form of Hardware Security Modules. These are physical devices that safeguard and manage digital keys for strong authentication. In a cloud environment like AWS or Azure, an HSM provides a dedicated space where the “heart” of a company’s security—its root keys—can operate without ever being exposed to the multi-tenant environment of the public cloud.
Zero Trust and the Pericardial Defense Strategy
In cybersecurity, the concept of a “pericardial cavity” is being applied through a philosophy known as Zero Trust. In the past, security was like a “shell” around a building; once you were inside, you had access to everything. Today’s tech landscape assumes the perimeter is already breached, requiring every component to have its own individual protective layer.
Micro-segmentation of Networks
Micro-segmentation is the practice of dividing a data center or cloud environment into small, distinct security segments down to the individual workload level. Instead of one large cavity for all servers, each server gets its own “pericardium.” If a breach occurs in one segment, the “infection” is physically and logically prevented from spreading to the others. This strategy mimics how the pericardial sac prevents an infection in the lungs from easily migrating to the heart.
Identity as the New Perimeter
In a world of remote work and decentralized apps, the “location” of a user no longer provides security. The new protective membrane is Identity. Through Multi-Factor Authentication (MFA) and Identity and Access Management (IAM), tech systems create a dynamic cavity around the user’s session. Every time a user tries to access a resource, the “membrane” checks their credentials, their device health, and their location before allowing the “beat” of data transmission to occur.
Data Encapsulation and Policy-Based Access
Modern data protection involves “wrapping” data in its own security policy. When data is encapsulated, the rules for who can see it and what they can do with it are attached directly to the data object. This is a “pericardial” approach to information; the protection isn’t just in the database (the room), but around the data itself (the heart).
The Future: AI-Driven and Quantum-Resistant Cavities
As we look toward the future of technology, the complexity of our “digital hearts” is increasing, necessitating even more advanced protective structures. The emergence of Artificial Intelligence and Quantum Computing presents both a threat and an opportunity for digital encapsulation.
AI-Managed Protective Layers
In the future, the “digital pericardium” will not be a static set of rules but a dynamic, AI-driven entity. Predictive analytics will allow the system to sense “friction” or potential threats before they manifest. An AI-managed cavity could theoretically change its “fluidity”—adjusting encryption strengths or isolating sub-systems—in real-time based on the threat landscape. This creates a self-healing architecture that mimics the biological body’s ability to respond to stress.
Quantum-Resistant Encapsulation
The advent of quantum computing threatens to shatter current encryption methods. To counter this, technologists are developing “Quantum-Resistant” algorithms. These will form the next generation of the pericardial membrane, ensuring that even the most powerful computers cannot pierce the cavity and access the sensitive data within. This evolution is critical for maintaining the “heartbeat” of global finance and national security in the decades to come.
Edge Computing and Localized Isolation
As processing moves to the “edge” (IoT devices, autonomous vehicles, smart sensors), the need for localized pericardial cavities grows. An autonomous car’s braking system must be isolated from its infotainment system. If the music player crashes, the “heart” of the car (the safety systems) must remain protected within its own execution cavity. This decentralized protection will be the hallmark of the next generation of smart infrastructure.
Conclusion
The biological pericardial cavity is an elegant solution to a complex problem: how to protect a vital, moving organ while allowing it the freedom to function. Technology has adopted this same wisdom. Whether through Docker containers, hardware secure enclaves, or Zero Trust network segments, we are building “digital pericardiums” to safeguard the core of our modern world.
As we continue to integrate technology more deeply into our lives—from the clouds that store our memories to the chips that might one day sit within our own bodies—the importance of these protective cavities cannot be overstated. By understanding “what is the pericardial cavity” in a technical sense, we gain insight into the sophisticated architecture required to keep our digital hearts beating safely in an increasingly complex and often hostile environment. The future of tech lies not just in the power of the core, but in the strength and resilience of the cavity that surrounds it.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.