In the early days of corporate networking, digital security was often compared to a medieval castle. Organizations built high walls (firewalls) and deep moats (intrusion prevention systems) to keep attackers out. This “perimeter-based” security model operated on a simple premise: anything outside the network was untrusted, and everything inside was trusted. However, as cyber threats evolved and the corporate landscape shifted toward cloud computing and remote work, this model proved fatally flawed. Once an attacker breached the perimeter, they had “flat” access to the entire interior of the network.

Enter micro-segmentation. As a foundational pillar of modern digital security and Zero Trust architecture, micro-segmentation represents a paradigm shift in how we protect data and applications. Rather than relying on a single hardened exterior, micro-segmentation creates granular zones within the network to isolate workloads from one another and secure them individually.
The Mechanics of Micro-segmentation: Moving Beyond the Perimeter
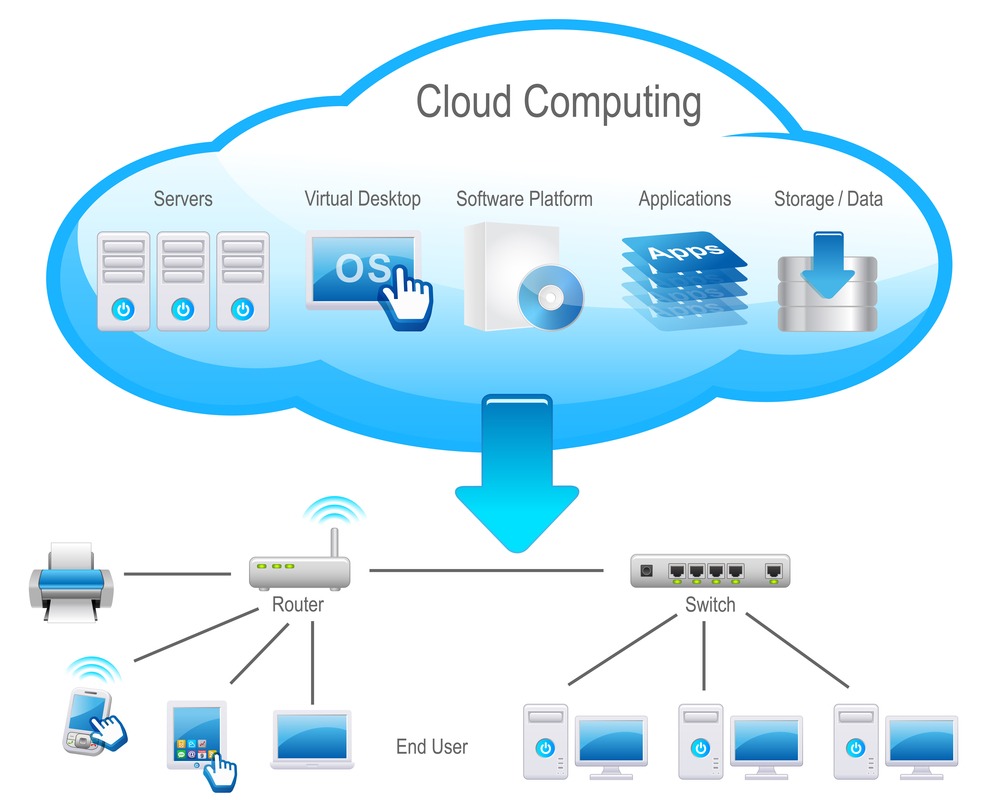
To understand micro-segmentation, one must first understand the distinction between “North-South” and “East-West” network traffic. Traditional firewalls are designed to monitor North-South traffic—data moving in and out of the data center to the internet. However, in modern virtualized environments, the vast majority of traffic (often upwards of 80%) is East-West, meaning it moves laterally between servers, containers, and applications within the data center or cloud.
From Macro to Micro: The Evolution of Network Security
Standard network segmentation usually involves Virtual Local Area Networks (VLANs) or subnets. While effective for broad categorization, these macro-segments are often too large and static. If a company segments its “Finance Department” into one VLAN, a breach of one desktop in that department could still lead to the compromise of the entire finance server. Micro-segmentation takes this further by applying security policies to the individual workload level—down to a single virtual machine (VM), container, or even a specific process.
East-West Traffic and the Rise of Lateral Movement
The primary goal of micro-segmentation is to prevent “lateral movement.” In a typical sophisticated cyberattack, a hacker gains an initial foothold through a low-priority asset, such as an employee’s laptop or a vulnerable IoT device. From there, they move laterally through the network to find high-value targets like customer databases or intellectual property. Micro-segmentation stops this journey by ensuring that even if one segment is compromised, the attacker is trapped in a tiny “cell” with no way to jump to neighboring systems.
The Role of Virtualization and Software-Defined Networking (SDN)
Micro-segmentation is largely made possible by Software-Defined Networking. In a hardware-centric world, creating thousands of tiny segments would require an impossible amount of physical cabling and manual firewall configuration. In a software-defined environment, security policies are decoupled from the physical hardware. They are delivered via software (often through hypervisors or host-based agents), allowing security rules to follow the workload even if it moves across different physical servers or cloud providers.
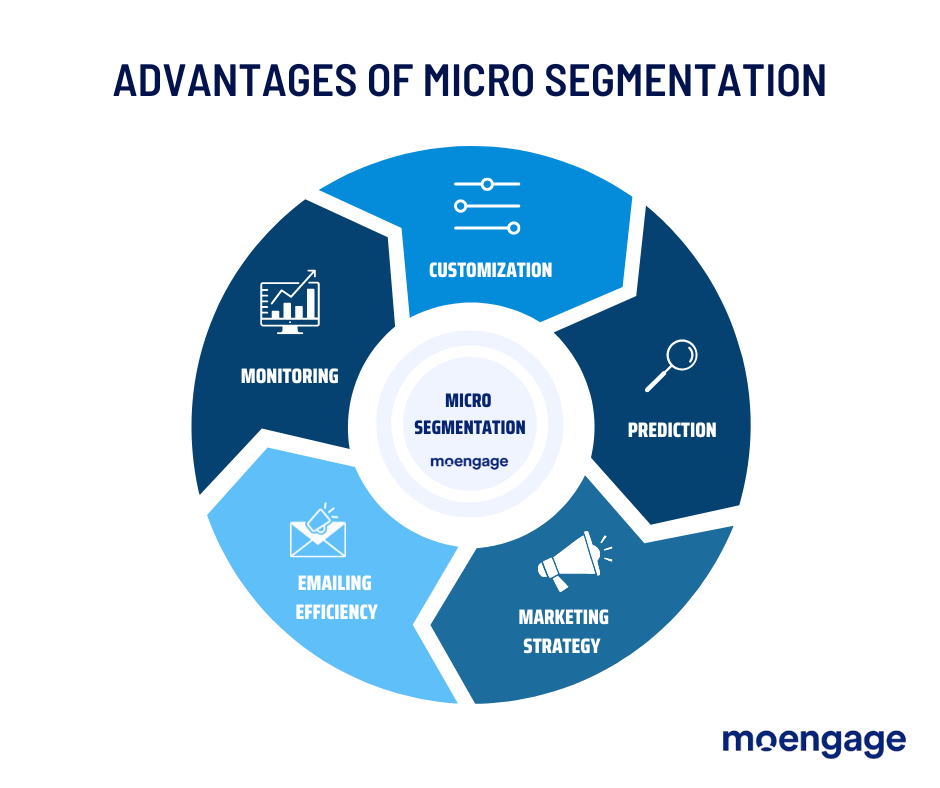
Core Benefits of Implementing Micro-segmentation
As organizations undergo digital transformation, the complexity of their environments grows. Micro-segmentation provides the surgical precision required to manage this complexity while significantly hardening the security posture.
Reducing the Attack Surface
The “attack surface” is the total sum of all points where an unauthorized user can try to enter or extract data. By dividing the network into hundreds or thousands of isolated zones, micro-segmentation dramatically shrinks this surface. A vulnerability in a web server no longer provides a gateway to the SQL database unless specifically permitted by a granular policy.
Containing the Blast Radius
In the event of a successful breach, micro-segmentation acts as a system of “bulkheads” on a ship. If one compartment takes on water, the bulkheads prevent the entire vessel from sinking. By containing the “blast radius” of an attack, IT teams can isolate the infected segment, perform forensics, and remediate the issue without having to take the entire corporate network offline.
Enhancing Compliance and Regulatory Alignment
For industries governed by strict data privacy laws—such as healthcare (HIPAA) or finance (PCI-DSS)—micro-segmentation is a powerful tool. It allows organizations to isolate systems that handle sensitive data into highly secure “clean rooms.” This simplifies the audit process, as the organization only needs to prove the security of the specific segments where regulated data resides, rather than the entire enterprise infrastructure.
The Strategic Pillars of a Micro-segmentation Framework
Implementing micro-segmentation is not a “set-it-and-forget-it” task. It requires a strategic approach that combines deep visibility with automated policy enforcement.
Visibility and Application Dependency Mapping
You cannot protect what you cannot see. The first step in any micro-segmentation project is “discovery.” Modern tech tools use automated mapping to visualize how applications communicate. This reveals the “hidden” dependencies between services. For example, a web application might need to talk to a specific authentication API and a legacy database. Understanding these flows is essential to ensure that when you “turn on” segmentation, you don’t inadvertently break the business processes.
Policy Formulation and Automation
Once the communication flows are understood, security teams must define policies. In a micro-segmented environment, policies are typically “identity-based” rather than “IP-based.” Instead of saying “Allow IP 192.168.1.1 to talk to 192.168.1.5,” a micro-segmentation policy says “Allow the ‘Web-Front-End’ group to talk to the ‘Production-DB’ group via encrypted HTTPS.” Because environments change rapidly, these policies must be automated so that new workloads automatically inherit the correct security posture as they are spun up.
Continuous Monitoring and Refinement
The threat landscape is dynamic. Micro-segmentation platforms provide real-time alerts when a workload attempts to communicate in a way that violates established policy. This serves as an early warning system for potential breaches. Over time, these insights allow tech teams to refine their policies, tightening security as they gain more data on legitimate traffic patterns.
Integrating Micro-segmentation into a Zero Trust Architecture
Micro-segmentation is often described as the practical implementation of “Zero Trust.” Zero Trust is a strategic initiative that prevents data breaches by eliminating the concept of trust from an organization’s network architecture.
The “Never Trust, Always Verify” Principle
In a Zero Trust model, identity is the new perimeter. Whether a request comes from inside the office or from a coffee shop in another country, the network treats it with the same level of scrutiny. Micro-segmentation provides the technical mechanism to enforce this. By placing a “micro-perimeter” around every workload, the system forces every interaction to be verified against a security policy before access is granted.
Identity-Based vs. Traditional Segmentation
Traditional segmentation relies on network addresses (IPs), which are easily spoofed and change frequently in cloud environments. Micro-segmentation utilizes unique identifiers—such as software tags, UUIDs, or cryptographic identities. This ensures that security is tied to the workload itself, not just the location where it happens to be running. This is a critical distinction for modern DevOps teams who utilize ephemeral containers that may only exist for a few minutes.
Challenges and Best Practices for Deployment
While the benefits are clear, micro-segmentation is a complex technical undertaking. Organizations often struggle with “policy bloat” or the fear of disrupting critical services.
Managing Complexity in Multi-Cloud Environments
Most modern enterprises use a mix of on-premises data centers, private clouds, and multiple public cloud providers (like AWS, Azure, or Google Cloud). Each of these environments has its own native security groups. The challenge is maintaining a consistent security policy across all these silos. The best practice is to use a “vendor-agnostic” micro-segmentation tool that provides a single pane of glass for policy management across the entire hybrid-cloud estate.
Prioritizing Critical Assets (The “Crown Jewels”)
Attempting to micro-segment an entire global network at once is a recipe for failure. Instead, tech leaders should follow a phased approach. Start by identifying the “Crown Jewels”—the most critical data and applications that, if compromised, would cause the most damage to the organization. Secure these high-value segments first, refine the process, and then expand the segmentation to the rest of the environment.
Bridging the Gap Between Security and Operations
Micro-segmentation requires close collaboration between security teams (who define the rules) and IT operations/DevOps teams (who manage the applications). If security teams work in a vacuum, they risk creating policies that cause application outages. Integrating security into the CI/CD pipeline—often called DevSecOps—ensures that micro-segmentation is baked into the software development lifecycle from day one.
Conclusion: The New Standard for Digital Security
As we move further into a world of hyper-connectivity, the vulnerabilities of the past cannot be ignored. Micro-segmentation has evolved from a niche networking concept into a mandatory requirement for any organization serious about digital security. By moving security closer to the workload, companies can achieve a level of resilience that was previously impossible.
Though the journey to a fully micro-segmented environment requires careful planning and the right technological tools, the reward is a robust, “Zero Trust” infrastructure. In this new era, security is no longer just a wall around the network; it is an intelligent, granular, and pervasive layer that protects every individual piece of the digital puzzle. As cyber threats become more sophisticated, the ability to isolate, contain, and monitor every interaction within the network will be the defining factor in an organization’s technological success.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.