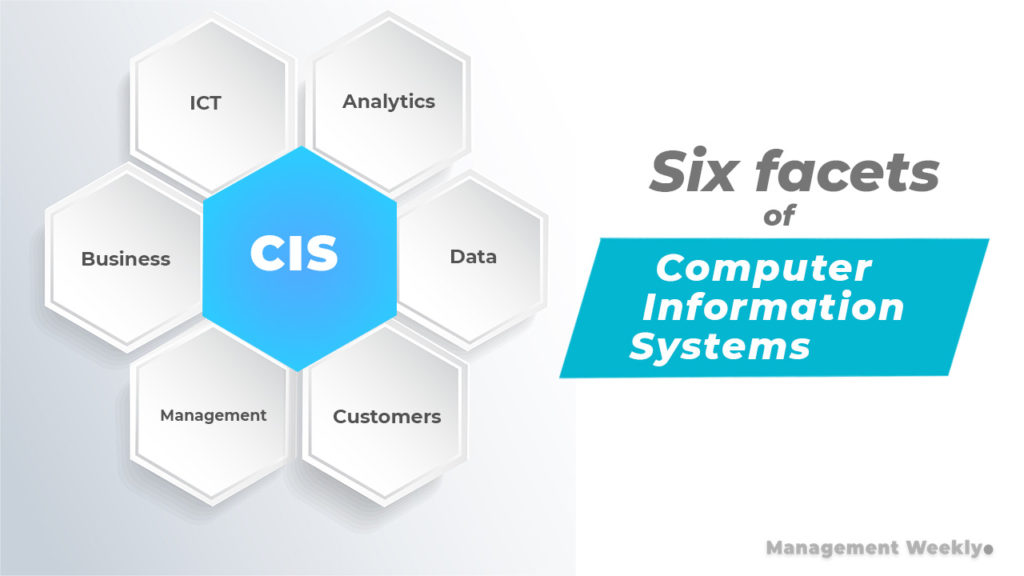
In the current digital landscape, the term “computerized information system” (CIS) represents far more than a simple collection of hardware and software. It is the sophisticated central nervous system of any modern organization, facilitating the flow of data, the execution of complex algorithms, and the delivery of actionable insights. As we move deeper into the era of big data and artificial intelligence, understanding the architecture and functionality of a CIS is essential for anyone navigating the technology sector. A computerized information system is an integrated set of components designed to collect, store, and process data, and to provide information, knowledge, and digital products to support decision-making and operational control.

The Core Components of a Computerized Information System
To understand how a CIS operates, one must look beneath the surface at the various layers that comprise its architecture. A functional information system is not a singular entity but a synergy of five primary components: hardware, software, data, procedures, and people. Each plays a critical role in ensuring that the system is efficient, scalable, and secure.
Hardware: The Physical Foundation
Hardware constitutes the tangible aspect of the system. This includes everything from high-performance servers in centralized data centers to the end-user devices such as laptops, tablets, and smartphones. In the context of modern tech trends, hardware also encompasses networking equipment—routers, switches, and fiber-optic cabling—that facilitates the high-speed transfer of data. The evolution of hardware, characterized by Moore’s Law, has allowed computerized information systems to process trillions of operations per second, enabling real-time analytics that were impossible a decade ago.
Software: The Intelligence Layer
If hardware is the body, software is the mind. Software in a CIS is generally categorized into system software and application software. System software, such as operating systems (Windows, Linux, macOS) and database management systems (DBMS like PostgreSQL or Oracle), manages the hardware resources and provides a platform for applications. Application software, on the other hand, consists of the specific programs designed to perform tasks—ranging from enterprise resource planning (ERP) suites to specialized AI-driven diagnostic tools.
Data: The Vital Fuel
Data is arguably the most valuable asset within a CIS. It represents the raw facts and figures that the system processes. In a modern tech environment, data is no longer just text and numbers; it includes images, video streams, sensor readings from IoT devices, and logs from user interactions. The challenge for contemporary systems lies in managing “Big Data”—the volume, velocity, and variety of information—and converting it into a structured format that can be leveraged for competitive advantage.
Procedures and People: The Human-System Interface
Often overlooked, procedures are the rules and guidelines for using a CIS. These include security protocols, data entry standards, and system maintenance schedules. Without clear procedures, the technology remains dormant or, worse, becomes a liability. Finally, the “people” component includes the users who interact with the system and the IT professionals (developers, sysadmins, and data scientists) who design and maintain it. The interface between human intuition and machine logic is where the true value of an information system is realized.
Types of Computerized Information Systems in Today’s Tech Ecosystem
Not all information systems are created equal. Depending on their intended use and the level of management they support, CIS architectures vary significantly. Understanding these distinctions is vital for tech professionals tasked with implementing or optimizing these systems.
Transaction Processing Systems (TPS)
A Transaction Processing System is the most basic level of CIS. Its primary function is to record the routine transactions that occur in a business environment. Examples include point-of-sale (POS) systems, payroll processing, and inventory tracking. The hallmark of a TPS is its ability to handle high volumes of data with extreme accuracy and speed. In the modern tech world, these systems are increasingly cloud-based, allowing for instantaneous updates across global networks.
Management Information Systems (MIS)
While a TPS records data, a Management Information System (MIS) organizes it. An MIS takes the raw data from various transaction systems and converts it into comprehensive reports. These reports help middle management monitor performance and predict future trends. For instance, a tech startup might use an MIS to track software development sprints, bug resolution rates, and resource allocation, ensuring that the project remains on schedule.
Decision Support Systems (DSS)
A Decision Support System is a more advanced iteration of CIS that focuses on “what-if” scenarios. Unlike an MIS, which provides standardized reports, a DSS is interactive and flexible. It utilizes mathematical models and data mining techniques to help users analyze complex problems. For example, a data scientist might use a DSS to simulate the impact of a new algorithm update on user engagement metrics before deploying the code to a live environment.
Executive Support Systems (ESS)
At the highest level of an organization, Executive Support Systems (ESS) provide a bird’s-eye view of the entire digital ecosystem. These systems integrate internal data with external information, such as market trends, regulatory changes, and competitor activity. ESS platforms often feature highly visual dashboards and “drill-down” capabilities, allowing executives to see the health of the entire tech infrastructure at a glance.

The Evolution of CIS: From Mainframes to Cloud and AI
The history of computerized information systems is a narrative of constant transformation. We have moved from the era of massive, isolated mainframes to a world of hyper-connected, intelligent ecosystems.
The Shift to Cloud-Native Architectures
In the past, a CIS required significant on-site infrastructure. Today, the trend is overwhelmingly toward cloud-native architectures. By leveraging providers like AWS, Azure, or Google Cloud, organizations can deploy information systems that are infinitely scalable. Cloud computing has democratized access to powerful CIS tools, allowing even small dev teams to utilize enterprise-grade databases and processing power without the upfront cost of physical hardware.
Integrating Artificial Intelligence and Machine Learning
The most significant trend in current CIS development is the integration of Artificial Intelligence (AI) and Machine Learning (ML). Modern systems are no longer just passive repositories of data; they are becoming proactive. AI-enhanced CIS can identify patterns in data that are invisible to the human eye, automate routine coding tasks, and even predict system failures before they occur. This shift from “deterministic” systems (where A leads to B) to “probabilistic” systems (where the system learns and adapts) is redefining the boundaries of technology.
The Rise of Real-Time Data Processing
Latency is the enemy of the modern information system. The demand for real-time data processing has led to the rise of technologies like Apache Kafka and Spark. Whether it is a fintech app processing a trade or an autonomous vehicle reacting to its environment, the CIS must process and act on data in milliseconds. This push for speed has necessitated advancements in “edge computing,” where data is processed closer to its source rather than being sent back to a central server.
Security and Resilience in Computerized Information Systems
As our reliance on CIS grows, so does the risk associated with its failure or compromise. Digital security is no longer an afterthought; it is a fundamental pillar of CIS design.
Protecting Data Integrity and Privacy
A computerized information system is only as good as the data it holds. Ensuring data integrity—the accuracy and consistency of data over its entire lifecycle—is a primary technical challenge. Furthermore, with the rise of regulations like GDPR and CCPA, CIS must be designed with “privacy by design” principles. This involves implementing robust encryption standards, both at rest and in transit, to ensure that sensitive information remains confidential.
Cybersecurity Frameworks for CIS
Modern information systems face a barrage of threats, from ransomware and DDoS attacks to sophisticated social engineering. To counter these, tech professionals employ multi-layered security frameworks. This includes Zero Trust Architecture (ZTA), where no user or device is trusted by default, even if they are inside the network perimeter. Implementing Multi-Factor Authentication (MFA), advanced firewalls, and Intrusion Detection Systems (IDS) are now standard requirements for any robust CIS.
Disaster Recovery and Business Continuity
Resilience is the ability of a CIS to withstand and recover from catastrophic events. This involves creating redundant systems and frequent data backups. In a cloud-centric world, this often means “multi-region” or “multi-cloud” strategies, where the information system is mirrored across different geographic locations. If one data center goes offline due to a cyberattack or natural disaster, the system can failover to another, ensuring minimal downtime.
The Future of CIS: Towards Autonomous Information Ecosystems
Looking ahead, the trajectory of computerized information systems points toward a future where these systems are increasingly autonomous and self-healing.
Edge Computing and IoT Integration
The Internet of Things (IoT) is expanding the reach of CIS into the physical world. With billions of connected devices—from smart thermostats to industrial sensors—the volume of data is exploding. The future of CIS lies in “edge computing,” where the system’s processing power is distributed to the very edges of the network. This reduces bandwidth usage and allows for near-instantaneous decision-making, which is critical for the next generation of smart cities and automated manufacturing.
The Impact of Quantum Computing on Data Processing
While still in its infancy, quantum computing represents the next frontier for computerized information systems. A quantum-ready CIS would be capable of solving problems that are currently computationally impossible for classical computers. This includes complex cryptography, advanced molecular modeling, and the optimization of massive logistics networks. As quantum technology matures, it will necessitate a complete overhaul of how we think about data encryption and processing speed within a CIS.
In conclusion, a computerized information system is the fundamental infrastructure upon which the modern tech world is built. From the physical hardware that anchors it to the AI algorithms that give it foresight, the CIS is a dynamic, evolving entity. For tech enthusiasts and professionals alike, staying ahead of the trends in CIS architecture, security, and integration is not just an advantage—it is a necessity in an increasingly digital future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.