In the vast architecture of the internet, we often focus on the high-level components we interact with daily—IP addresses, domain names, and web browsers. However, beneath the surface of every data packet sent across a local area network (LAN) lies a fundamental protocol that ensures information reaches its physical destination. This protocol is the Address Resolution Protocol, or ARP.
Without ARP, your computer might know the logical address of a printer or another server, but it would have no way of physically communicating with it. In the world of technology and digital infrastructure, ARP serves as the bridge between the network layer and the data link layer, acting as a translator between IP addresses and MAC addresses. This article explores the mechanics of ARP, its various types, its critical security implications, and its evolving role in a world transitioning to modern networking standards.

How ARP Works: The Mechanics of Local Networking
To understand ARP, one must first distinguish between the two types of addresses used in networking: the Internet Protocol (IP) address and the Media Access Control (MAC) address. An IP address is a logical address assigned by software to identify a device on a network. A MAC address, conversely, is a unique physical identifier hardcoded into a device’s Network Interface Card (NIC) by the manufacturer.
While routers use IP addresses to move data across different networks, local hardware uses MAC addresses to deliver data within the same physical segment. ARP is the mechanism that maps these two layers together.
The ARP Request and Reply Cycle
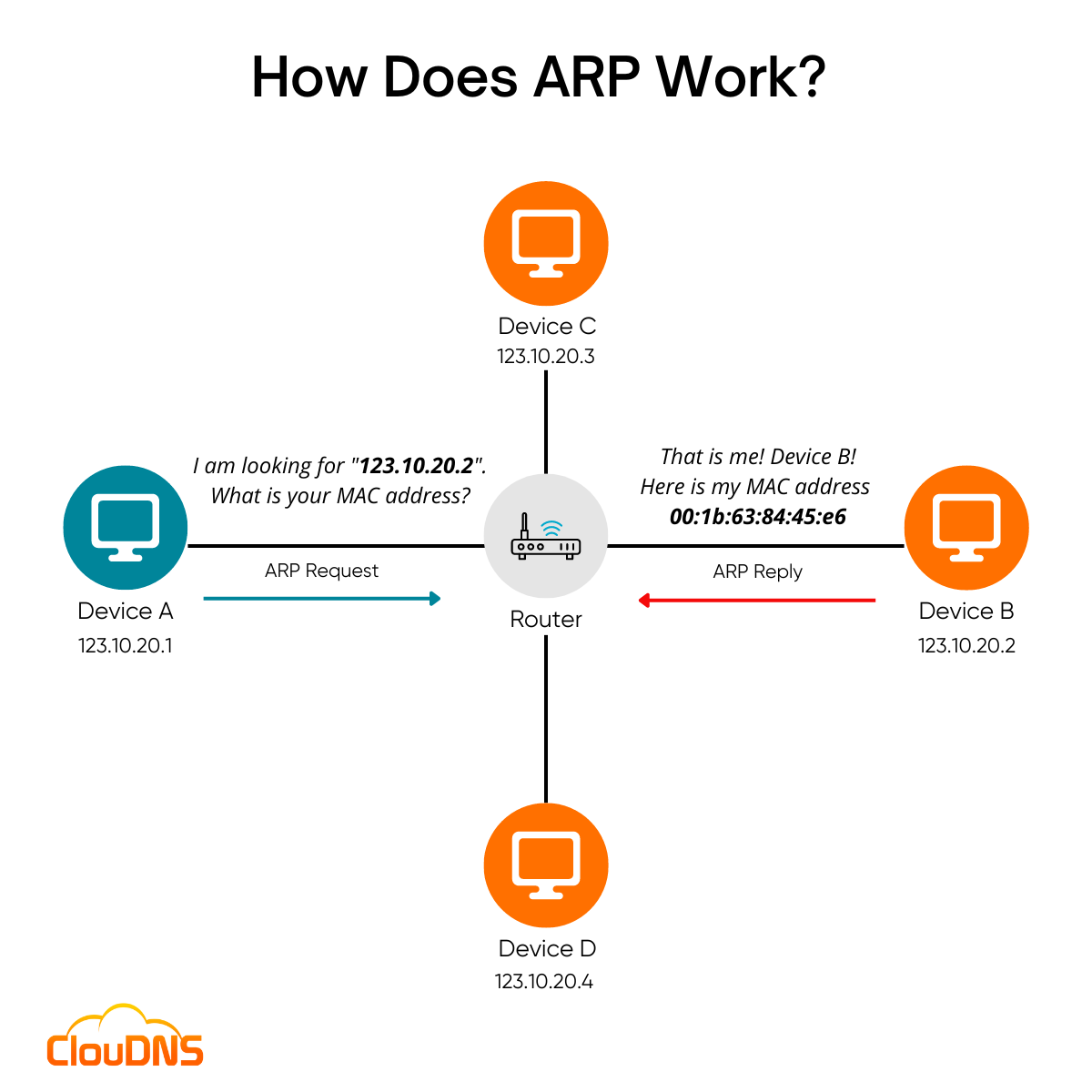
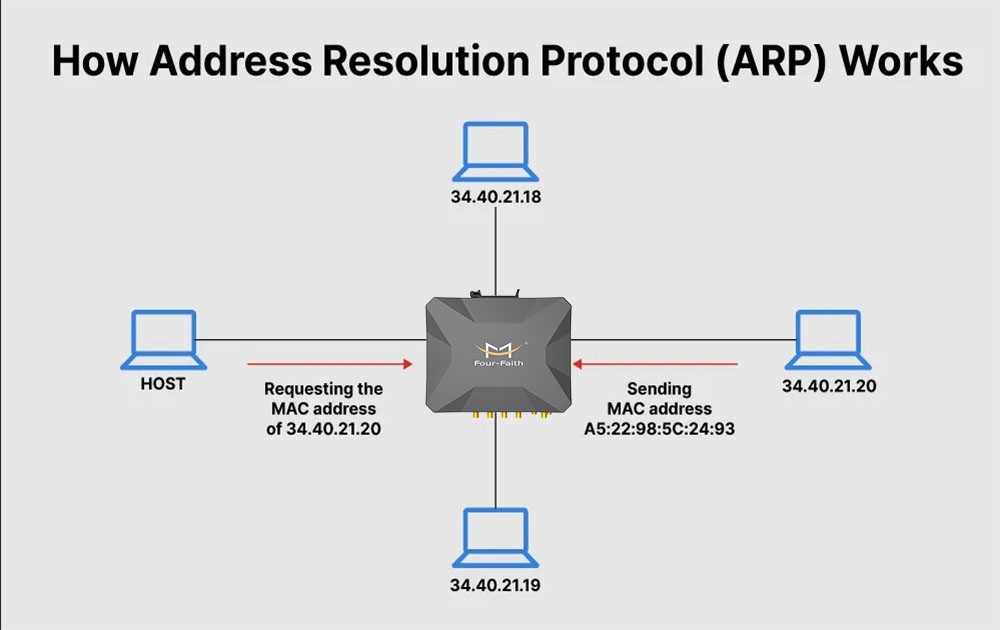
When a device (the “source”) wants to send data to another device (the “target”) on the same local network, it first checks its internal memory, known as the ARP cache. If the MAC address for the target IP is not found, the source initiates an ARP request.
The ARP request is a “broadcast” packet sent to every device on the network. It essentially asks, “Who has IP address 192.168.1.50? Please tell me your MAC address.” Every device receives this request, but only the one assigned that specific IP address responds. The target device sends an ARP reply—this time as a “unicast” message directly back to the source—stating, “I have that IP address, and my MAC address is 00:1A:2B:3C:4D:5E.”
ARP Caching and Efficiency
To prevent the network from being overwhelmed by constant broadcast requests, devices utilize an ARP cache. This table stores the mapping of IP addresses to MAC addresses for a short period. When a device successfully resolves an address, it saves it in the cache. The next time it needs to communicate with that specific device, it bypasses the broadcast phase and pulls the MAC address directly from memory.
Cache entries are not permanent. They typically stay for a few minutes before “aging out.” This ensures that if a device leaves the network or its IP address changes, the network can dynamically update itself. This efficiency is what allows modern office networks to support hundreds of devices without significant latency issues caused by address resolution overhead.
The Different Types of Address Resolution Protocols
While the standard ARP process handles most day-to-day networking, several specialized versions of the protocol exist to handle complex routing scenarios and legacy systems.
Proxy ARP
Proxy ARP occurs when a device, usually a router, answers an ARP request on behalf of another machine. This is common in scenarios where two devices are on different subnets but appear to be on the same local segment. The router “proxies” the request, providing its own MAC address to the requester. This trick allows the source to send packets to the router, which then assumes the responsibility of forwarding them to the actual destination on the other side. This is particularly useful in VPN configurations and specific firewall setups.
Gratuitous ARP
A Gratuitous ARP is an ARP request or reply that is not prompted by a specific query. Essentially, a device broadcasts its own IP-to-MAC mapping to the entire network. Why would it do this? There are two primary reasons. First, it helps detect IP address conflicts; if a device sends a Gratuitous ARP and receives a response, it knows another machine is using its IP. Second, it is used in “High Availability” clusters. If a primary server fails and a backup takes over, the backup sends a Gratuitous ARP to tell the network switches to update their tables and send traffic to the new hardware.
Reverse ARP (RARP) and Inverse ARP
Reverse ARP was designed for diskless workstations that knew their physical MAC address but needed to find their assigned IP address from a server. While RARP is largely obsolete today—replaced by DHCP (Dynamic Host Configuration Protocol)—it laid the groundwork for how we manage dynamic IP assignment. Inverse ARP, on the other hand, is used in Frame Relay and ATM networks to find an IP address associated with a specific virtual circuit identifier.
ARP and Digital Security: Understanding Vulnerabilities
Because ARP was designed in an era of trust, it lacks inherent security features. The protocol does not require authentication; a device will generally accept an ARP reply even if it never sent a request. This fundamental design flaw has made ARP a prime target for cyberattacks, specifically “ARP Spoofing.”
ARP Spoofing and Poisoning
ARP Spoofing, also known as ARP Cache Poisoning, is a technique where an attacker sends falsified ARP messages onto a local area network. The goal is to associate the attacker’s MAC address with the IP address of a legitimate server or the default gateway.
Once the target’s ARP cache is “poisoned” with the wrong MAC address, the target will unknowingly send all its data packets to the attacker instead of the intended destination. This allows the attacker to intercept, modify, or block data moving across the network.
Man-in-the-Middle (MITM) Attacks
The most common outcome of ARP spoofing is a Man-in-the-Middle attack. By positioning themselves between two communicating parties (such as a user and their router), an attacker can capture sensitive information like passwords, financial data, and session cookies. Because the attacker usually forwards the traffic to the actual gateway after snooping, the victim often has no idea their connection is being monitored, as their internet access remains functional.
Defending Against ARP Attacks
For IT professionals and security experts, defending against ARP-based threats is a top priority. Several technologies have been developed to mitigate these risks:
- Dynamic ARP Inspection (DAI): This is a security feature on high-end network switches. DAI intercepts all ARP requests and replies, verifying them against a trusted database (usually the DHCP snooping table). If a packet is deemed illegitimate, the switch drops it.
- Static ARP Entries: For critical infrastructure, admins can manually map IP addresses to MAC addresses in the ARP table. This prevents the system from accepting dynamic updates, though it is difficult to manage at scale.
- VPNs and Encryption: While these do not stop ARP spoofing at the network layer, they encrypt the data being sent. Even if an attacker intercepts the packets, the information remains unreadable.
The Future of ARP in an IPv6 World
As the tech world slowly migrates from IPv4 to IPv6, the role of ARP is changing. IPv4 relies on 32-bit addresses and utilizes ARP for resolution. IPv6, however, uses 128-bit addresses and does not use ARP at all.
Neighbor Discovery Protocol (NDP)
In the IPv6 universe, the functions of ARP have been absorbed into a more robust framework called the Neighbor Discovery Protocol (NDP). NDP operates at the ICMPv6 layer and provides much more than just address resolution; it handles router discovery, prefix discovery, and parameter discovery. NDP is more efficient because it uses multicast instead of the “noise-heavy” broadcasts used by ARP, reducing the processing load on every device on the network.
Why ARP Remains Relevant Today
Despite the rise of IPv6, ARP is not going away anytime soon. Millions of legacy systems, IoT devices, and corporate networks still run exclusively or primarily on IPv4. Even in “Dual Stack” environments where IPv4 and IPv6 coexist, ARP remains the primary method for resolving addresses for half of the network traffic. Understanding ARP is not just a lesson in tech history; it is a requirement for anyone managing modern digital infrastructure, securing local networks, or troubleshooting connectivity issues.
Conclusion
The Address Resolution Protocol is a classic example of a “set it and forget it” technology. It operates silently in the background of billions of devices, facilitating the essential handoff between software-based networking and physical hardware. From its simple request-reply mechanism to the complex security challenges posed by ARP spoofing, the protocol remains a cornerstone of computer science and IT operations.
As we move toward more secure and efficient protocols like NDP in the IPv6 era, the legacy of ARP continues to shape how we understand local data transmission. For tech enthusiasts, network administrators, and security professionals, mastering the nuances of ARP is vital to ensuring that our digital connections remain fast, reliable, and secure. Even as the “glue” of the internet evolves, the need for seamless communication between the logical and the physical will always remain.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.