In the realm of computer science and software development, understanding fundamental concepts is paramount. Among these, the representation of “nothing” or an invalid address is a recurring theme, often expressed in hexadecimal notation. When encountered, especially in error messages or debugging output, the string “0x0” frequently appears. This seemingly simple sequence of characters holds significant meaning, particularly within the context of memory management and data representation. This article will delve into the technical implications of “0x0,” exploring its role as a null pointer, its significance in programming languages, and its impact on system behavior and security.
The Essence of Zero: A Foundation in Computing
At its core, the hexadecimal representation “0x0” is simply the decimal number zero, expressed in base-16. This is a standard convention in computing to represent numerical values, especially when dealing with memory addresses, raw data, or bitwise operations. Hexadecimal is often preferred over decimal for its compactness and its direct mapping to binary representations. Each hexadecimal digit corresponds to four binary digits (bits), making it easier to work with bytes and larger chunks of data.
Binary and Hexadecimal: A Tangible Connection
To fully grasp “0x0,” it’s helpful to understand its binary equivalent. Decimal zero is represented as all zeros in binary: 00000000. In hexadecimal, this is also zero, denoted as 0. The 0x prefix is a common indicator in many programming languages (like C, C++, Java, Python, and JavaScript) to signify that the following number is a hexadecimal literal. Therefore, “0x0” is the unambiguous way to write the hexadecimal representation of zero.
Zero as a Sentinel Value
In programming, zero often serves as a sentinel value. This means it’s used to indicate a specific condition or state, frequently the absence of a valid value or the termination of a sequence. While zero itself can be a valid data point in many contexts (e.g., a count of zero items), when interpreted as a memory address or a pointer, it takes on a special meaning.
“0x0” as a Null Pointer: The Absence of a Target
The most prevalent and critical technical interpretation of “0x0” in programming is its representation of a null pointer. A pointer, in essence, is a variable that stores the memory address of another variable. It’s like a street address that tells the computer where to find a piece of data. A null pointer, therefore, is a pointer that does not point to any valid memory location.
The Concept of Null
The concept of “null” is fundamental to preventing undefined behavior and ensuring program stability. When a pointer is initialized or explicitly set to a null value, it signals that it doesn’t currently reference any data. This is crucial for several reasons:
- Initialization: When a pointer is declared but not yet assigned a valid memory address, it’s often initialized to null. This prevents it from pointing to an arbitrary, potentially occupied memory location, which could lead to data corruption or crashes.
- Termination: In data structures like linked lists, the last node’s “next” pointer is typically set to null to indicate the end of the list.
- Error Handling: Functions that are expected to return a pointer to a resource might return a null pointer if the resource cannot be found or created due to an error.
Why 0x0 Specifically?
While different programming languages and environments might use slightly different internal representations for null, “0x0” has become a widely recognized and conventional representation, particularly in low-level programming and debugging. The reasoning behind this convention is rooted in how memory addresses are managed. The address zero is typically reserved and is not used for allocating regular program data. Therefore, assigning the address zero to a pointer effectively makes it point to a non-existent or invalid location.
- System Reserved Memory: In many operating systems, the lower memory addresses, including address zero, are reserved for the operating system’s internal use or are simply considered invalid for application use. Accessing memory at address zero would often result in a segmentation fault or a similar access violation error.
- Convention and Simplicity: Using “0x0” is a simple and straightforward way to represent this invalid state. It’s easy to recognize and implement.
Implications of Dereferencing a Null Pointer
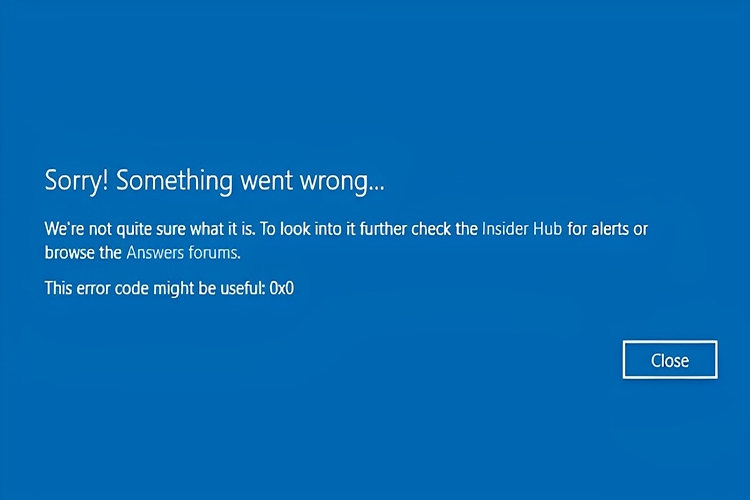
The most common and problematic scenario involving a null pointer is dereferencing it. Dereferencing a pointer means trying to access the data located at the memory address stored in the pointer. If that pointer is “0x0” (a null pointer), the program attempts to read or write to an invalid memory location.
This action almost invariably leads to a program crash. Operating systems are designed to detect such attempts and terminate the offending program to prevent potential system instability or security breaches. Debugging these crashes often involves tracing back to the point where a null pointer was dereferenced, and the debugger might report the null pointer as “0x0” or a similar value.
“0x0” in Different Programming Contexts
The significance and manifestation of “0x0” can vary slightly depending on the programming language and the specific context within which it appears.
C and C++: The Classic Null Pointer
In C and C++, NULL is a macro that is typically defined as (void*)0 or simply 0. When used as a pointer type, it resolves to the memory address zero, which is interpreted as a null pointer. The nullptr keyword introduced in C++11 provides a more type-safe way to represent null pointers, but the underlying principle and the potential for encountering “0x0” in older code or during low-level debugging remain.
Example:
int* ptr = nullptr; // Or int* ptr = 0;
<p style="text-align:center;"><img class="center-image" src="https://cryptobites.cc/wp-content/uploads/2023/10/What-is-0x0-1-1024x518.jpg" alt=""></p>
if (ptr == nullptr) {
// ptr is a null pointer, handle accordingly
std::cout << "Pointer is null." << std::endl;
}
// This would likely crash the program:
// int value = *ptr;
Java: The null Keyword
Java uses the keyword null to represent a null reference. Internally, null is a special literal that represents the absence of an object reference. While Java abstracts away direct memory addresses, the concept of a null reference pointing to nothing is analogous to a null pointer. When a Java program throws a NullPointerException, it’s often because an attempt was made to access a member of an object that is null. The underlying representation is managed by the Java Virtual Machine (JVM).
Python: The None Object
Python uses the keyword None to represent the absence of a value or an object. None is a singleton object in Python. Similar to Java, Python’s object model abstracts away direct memory addresses. However, if a variable is expected to hold an object and instead holds None, operations that assume the presence of an object will fail, typically with an AttributeError.
Assembly Language and Debugging
At the lowest level of computing, in assembly language, “0x0” is directly representative of the memory address zero. When debugging a program using a debugger, you might see registers or memory locations displaying “0x0” when they contain a null pointer value. This provides invaluable insight into the program’s state and helps developers pinpoint the source of errors related to invalid memory access.
Beyond Null Pointers: Other Interpretations and Misconceptions
While the null pointer is the most common meaning of “0x0” in a technical context, it’s worth considering if there are other, less frequent interpretations, or common misconceptions.
Zero as a Valid Data Value
It’s crucial to reiterate that “0x0” is simply the numerical value zero. In many programming scenarios, zero is a perfectly valid and meaningful data value. For instance:
- Counters: A counter can legitimately reach zero.
- Numerical Calculations: Zero can be the result of a calculation.
- Array Indices: While not a valid address, array indices can be zero (e.g.,
myArray[0]).
The distinction lies in the context in which “0x0” is presented. If it appears as a value within a data structure, it’s likely a data value. If it appears in the context of memory addresses, pointer variables, or error messages related to memory access, it’s highly probable that it signifies a null pointer.
Potential for Confusion with Other Hexadecimal Values
The 0x prefix is standard, but beginners might sometimes confuse “0x0” with other hexadecimal numbers, especially those with leading zeros. For example, “0x0A” is decimal 10, and “0xFF” is decimal 255. However, the simplicity of “0x0” makes it distinct.
“0x0” in Network Protocols or Data Formats
While less common, in specific low-level network protocols or custom data formats, “0x0” might be used as a specific flag, command, or delimiter. However, without context, these are highly specialized interpretations. In general computing discussions, the null pointer interpretation is overwhelmingly dominant.
Safeguarding Against Null Pointer Issues
The prevalence of null pointer issues, often manifesting as “0x0” in debugging, highlights the importance of robust programming practices and defensive coding.
Defensive Programming Techniques
- Always Initialize Pointers: Ensure that pointers are initialized to a known state, preferably
nullptrorNULL. - Check for Null Before Dereferencing: Before accessing the data pointed to by a pointer, always check if it’s
nullptrorNULL. - Return Null Explicitly: When a function cannot fulfill its contract and is expected to return a pointer, make sure it returns
nullptrorNULLto signal failure. - Use Smart Pointers (C++): C++ offers smart pointers (like
std::unique_ptrandstd::shared_ptr) that automatically manage memory and help prevent dangling pointers and null pointer dereferences. - Utilize Language-Specific Null Handling: Leverage the null handling mechanisms provided by the programming language being used (e.g., Java’s
Optionalclass, Python’sNonechecks).
The Role of Static Analysis and Testing
Static analysis tools can often detect potential null pointer dereferences before runtime. Thorough unit testing and integration testing are also crucial for uncovering bugs related to null pointers in various execution paths.
Conclusion
The seemingly simple notation “0x0” is a powerful indicator within the technical landscape of computing. It most commonly signifies a null pointer, a fundamental concept representing the absence of a valid memory address. Understanding “0x0” is not merely an academic exercise; it’s essential for developers to write stable, reliable, and secure software. By recognizing its meaning and implementing defensive programming practices, developers can mitigate the risks associated with null pointer dereferences, leading to more robust applications and a deeper appreciation for the intricate mechanisms that govern how software operates. Whether you encounter it in a compiler error, a debugger’s output, or a technical discussion, “0x0” serves as a reminder of the careful management of memory and the importance of handling “nothing” correctly in the world of code.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.