For most users, a Subscriber Identity Module—commonly known as a SIM card—is nothing more than a tiny piece of plastic inserted into a smartphone to enable calling and data. However, from a technological standpoint, the SIM card is a sophisticated microcomputer with its own operating system, processor, and secure storage. It acts as a digital passport, authenticating your device to a global network of cellular towers.
As mobile technology shifts from 4G to 5G and transitions from physical cards to integrated eSIMs, understanding the data stored within these chips is crucial for understanding digital security and mobile connectivity. This article explores the specific categories of information contained within a SIM card and why this data is the backbone of the modern telecommunications industry.
1. Core Identification and Authentication Data
The primary function of a SIM card is to identify the subscriber to the network. To do this, it holds unique identifiers that are hard-coded during the manufacturing process or programmed by the carrier. This information ensures that when you make a call, the network knows exactly who is making it and who to bill.
ICCID: The Serial Number of the Card
The Integrated Circuit Card Identifier (ICCID) is the unique 19- or 20-digit serial number printed on the back of the physical SIM card. It is the primary identifier for the hardware itself. The ICCID includes an industry identifier (usually 89 for telecommunications), a country code, a network code, and a unique individual account identification number. Think of the ICCID as the SIM card’s fingerprint; while you can transfer your phone number to a new SIM, the ICCID remains fixed to the specific piece of hardware.
IMSI: The Network Identity
While the ICCID identifies the card, the International Mobile Subscriber Identity (IMSI) identifies the user within the cellular network. The IMSI is rarely shared with the user but is transmitted by the phone to the nearest cell tower to request access. It consists of three parts:
- Mobile Country Code (MCC): Identifies the home country of the subscriber.
- Mobile Network Code (MNC): Identifies the specific carrier (e.g., AT&T, T-Mobile, Vodafone).
- Mobile Subscription Identification Number (MSIN): The unique number assigned to the specific user account.
The Authentication Key (Ki)
The most sensitive piece of data on a SIM card is the Authentication Key, or Ki. This is a 128-bit value used to authenticate the SIM card on the network. For security reasons, the Ki is never transmitted over the air. Instead, the network sends a random challenge to the SIM, which uses the Ki to calculate a response. If the response matches the network’s calculation, the device is granted access. This cryptographic handshake is what prevents unauthorized devices from “spoofing” your phone number.
2. Network Configuration and Service Data
Beyond identification, a SIM card stores a variety of operational data that allows your phone to communicate efficiently with local and international cellular infrastructure. This data ensures that your device knows which frequencies to use and how to behave when you are away from your home network.
Location Area Identity (LAI)
To conserve battery and optimize signal strength, the SIM card stores the Location Area Identity (LAI). This is a snapshot of the current network state, including the specific “location area” of the cell tower the phone last connected to. When a phone is turned off and back on, it checks the LAI on the SIM card to quickly reconnect to the same tower rather than scanning the entire frequency spectrum, which would consume significant power.
Service Provider Name (SPN) and Preferred Roaming List (PRL)
The SIM card contains a string of text that tells your phone which carrier name to display on the lock screen (the Service Provider Name). More importantly, it contains the Preferred Roaming List (PRL). The PRL is a database of radio frequencies and service providers that your carrier has “roaming” agreements with. If you travel to a rural area or another country, the SIM card uses this list to determine which partner network it is allowed to connect to and in what order of priority.
SMS and Contact Storage (Legacy Data)
In the early days of GSM (2G) technology, the SIM card was the primary storage medium for user data. Most SIM cards have a storage capacity between 64KB and 128KB. Historically, this was used to store:
- Contact Lists: Usually limited to 250 contacts (name and one number).
- SMS Messages: Usually limited to 20–50 text messages.
While modern smartphones primarily store contacts and messages in the phone’s internal memory or the cloud (Google Account or iCloud), the SIM card still retains the capability to hold this data for backwards compatibility.
3. Hardware Architecture: The SIM as a Microcomputer

It is a common misconception that a SIM card is just a flash drive. In reality, it is a secure “Smart Card” that functions as a self-contained computer. It contains several hardware components that manage the data mentioned above.
CPU and Operating System
Every SIM card has a tiny Central Processing Unit (CPU) that executes cryptographic algorithms for authentication. It also runs a specialized operating system, often based on Java Card—a subset of the Java programming language designed for secure, small-memory environments. This allows carriers to run small “applets” on the SIM card, such as mobile payment triggers or specialized security protocols.
Memory Divisions: RAM, ROM, and EEPROM
The SIM card divides its tiny storage into three types:
- ROM (Read-Only Memory): Contains the SIM’s operating system and permanent manufacturer data.
- RAM (Random Access Memory): Used for temporary data processing during the authentication handshake.
- EEPROM (Electrically Erasable Programmable Read-Only Memory): This is where your personal data, the IMSI, and network settings are stored. Unlike ROM, this can be updated “over the air” (OTA) by your carrier to change roaming lists or update network protocols.
4. Security Protocols: PINs, PUKs, and Encryption
Because the information on a SIM card is so vital to identity, it is protected by several layers of security hardware and software. These protocols prevent unauthorized users from accessing your network services or stealing your identity via “SIM cloning.”
PIN and PUK Codes
The Personal Identification Number (PIN) is the first line of defense. If enabled, the SIM will not communicate with the network until the PIN is entered. If a user enters the wrong PIN too many times (usually three), the SIM card “locks” itself to prevent brute-force attacks. To unlock it, the user needs the PUK (Personal Unblocking Key), a unique 8-digit code provided by the carrier. If the PUK is entered incorrectly ten times, the SIM card becomes permanently disabled (permanently “bricked”) and must be replaced.
The Rise of SIM Swapping and Identity Theft
In the modern tech landscape, the most significant threat isn’t physical theft of the card, but “SIM Swapping.” This is a social engineering attack where a hacker convinces a carrier to move your IMSI and phone number to a new SIM card in their possession. Since the SIM card contains the “key” to your phone number, the attacker can then intercept Two-Factor Authentication (2FA) codes sent via SMS, gaining access to bank accounts and email. This highlights that while the data inside the SIM is encrypted, the management of that data by carriers is a critical security link.
5. The Future: From Physical SIMs to eSIM and iSIM
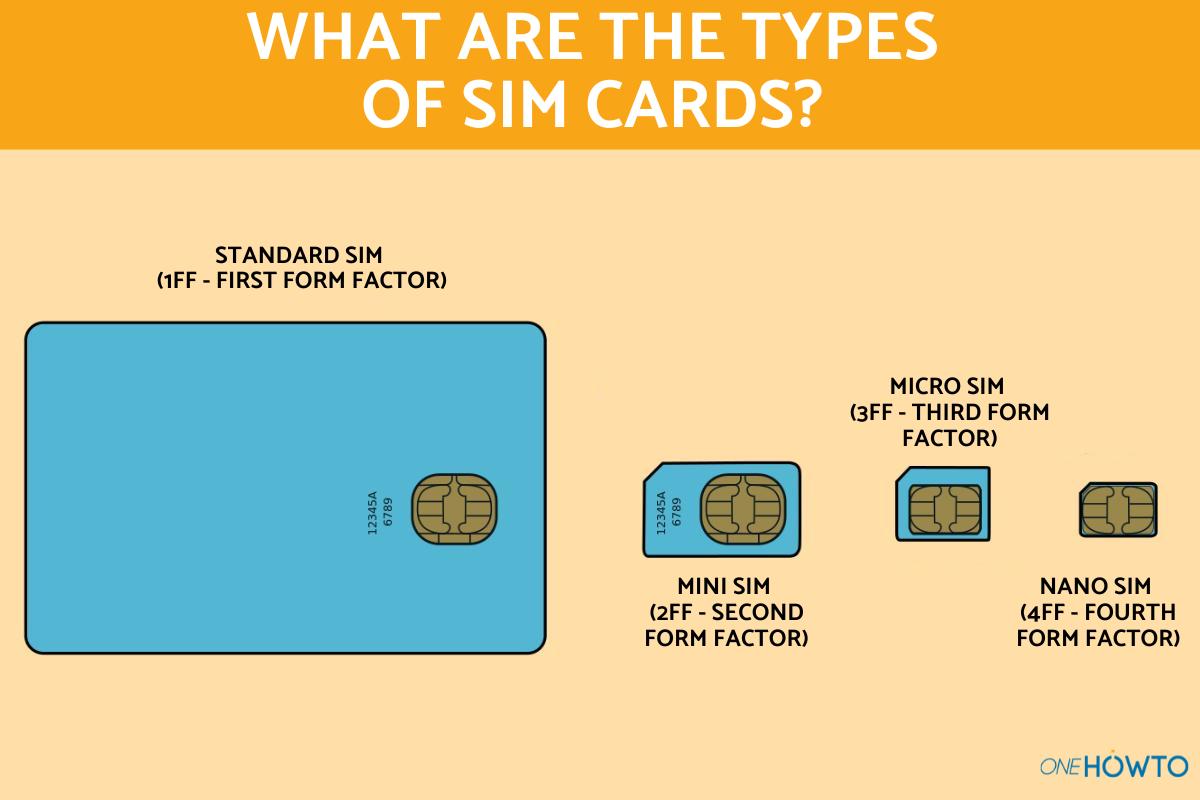
The physical nature of the SIM card is rapidly evolving. The transition from Mini-SIM to Micro-SIM and Nano-SIM was purely a matter of reducing plastic to save space for larger batteries. However, the move to eSIM (Embedded SIM) and iSIM (Integrated SIM) represents a fundamental shift in how SIM data is stored and managed.
What is an eSIM?
An eSIM is a small chip soldered directly onto the smartphone’s motherboard. It contains all the same information as a traditional SIM—ICCID, IMSI, and Ki—but it is “rewritable.” Instead of swapping a physical card, users download a “carrier profile” over the internet. This technology allows for multiple profiles on one device, making it easier for tech-savvy travelers to switch networks without needing physical hardware.
iSIM: The Next Frontier
The iSIM takes this a step further by integrating the SIM functionality directly into the device’s main processor (the System on a Chip or SoC). This removes the need for a dedicated SIM chip entirely. For the user, the “information” remains the same, but the hardware becomes even more secure and energy-efficient. This is particularly important for Internet of Things (IoT) gadgets, where space is at a premium and battery life is critical.
Conclusion
The SIM card is a masterpiece of compact engineering. While it may appear simple, it houses the essential cryptographic keys, network identifiers, and configuration data that make global mobile communication possible. From the ICCID that identifies the hardware to the IMSI that identifies the subscriber, the SIM card acts as the ultimate gatekeeper for our digital lives.
As we move toward a future dominated by eSIMs and 5G connectivity, the physical card may disappear, but the core data it contains will remain the foundation of mobile security. Understanding what is on your SIM card is not just a matter of technical curiosity—it is a vital part of managing your digital identity and staying secure in an increasingly connected world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.