When users encounter unwanted or inappropriate content on Apple devices and services, they have a mechanism to report it. This reporting feature, often labelled as “Report Junk,” “Report Junk/Spam,” or similar phrasing, is a crucial component of Apple’s ongoing efforts to maintain a safe and functional ecosystem. But what precisely happens when a user clicks that button? The process involves a multi-faceted approach, blending automated systems with human oversight to identify, assess, and act upon reported content. Understanding Apple’s response to reported junk offers insight into their commitment to user experience, digital security, and the overall integrity of their platforms.
The Initial Triage: Automated Detection and Filtering
The first line of defense against reported junk is a sophisticated, automated system. This technology is designed to quickly process a high volume of reports and identify patterns that suggest malicious or undesirable activity. The goal is not just to react to individual reports but to proactively identify and flag content that exhibits characteristics of spam, phishing, scams, or other forms of abuse.
Pattern Recognition and Machine Learning
Apple leverages advanced machine learning algorithms to analyze the characteristics of reported content. This includes examining text for common spam phrases, suspicious URLs, unusual sender information, and deviations from expected communication patterns. For instance, in iMessage, the system can identify a sudden surge of messages from unknown senders with identical, often unsolicited, content. Similarly, in the App Store, it can flag apps with misleading descriptions, review manipulation, or a history of violating App Store guidelines.
Identifying Malicious Links and Attachments
A significant portion of reported junk involves attempts to trick users into clicking malicious links or downloading harmful attachments. Apple’s automated systems are trained to detect known phishing URLs, identify suspicious domain registrations, and scan for malware signatures within attachments. This proactive scanning helps to prevent users from being exposed to threats even before they actively report them. The system continuously updates its databases of known malicious entities, drawing from a vast pool of global threat intelligence.
Categorization and Prioritization of Reports
Not all reported junk is created equal. Some reports might pertain to minor annoyances, while others could indicate serious security risks. Apple’s automated systems categorize incoming reports based on the perceived severity and type of the issue. This categorization allows for efficient prioritization, ensuring that critical threats are addressed with greater urgency. For example, a report indicating a potential phishing attempt aiming to steal Apple ID credentials would be flagged with a higher priority than a report about unsolicited promotional messages.
The Human Element: Expert Review and Content Moderation
While automation is essential for scalability and speed, it is not infallible. Apple understands that nuanced situations and evolving tactics employed by malicious actors require human intervention. A dedicated team of content moderators and security experts plays a vital role in reviewing reported content, making judgment calls, and taking decisive action.
Investigating Flagged Content
When automated systems flag content as potentially problematic, or when reports are deemed complex enough to warrant further scrutiny, human reviewers step in. These individuals are trained to analyze the context of the reported content, cross-reference it with Apple’s policies and guidelines, and assess the intent behind it. This can involve examining message threads, app descriptions, website content, or other relevant data associated with the report.
Decision Making and Enforcement
Based on their investigation, human reviewers make a determination on whether the reported content violates Apple’s terms of service or guidelines. If a violation is confirmed, appropriate enforcement actions are taken. These actions can range from warning the sender to permanently banning them from Apple services. For egregious violations, such as those involving illegal activities or significant security threats, Apple may cooperate with law enforcement agencies.
The Role of User Feedback
User reports are a critical source of data for Apple’s content moderation efforts. They act as an early warning system, alerting Apple to emerging threats and vulnerabilities that their automated systems might not yet have encountered. The volume and nature of user reports help Apple refine their algorithms, update their threat intelligence, and improve their overall detection capabilities. This continuous feedback loop is essential for staying ahead of the curve in the ever-evolving landscape of online abuse.
Actions Taken Against Reported Junk
The ultimate goal of reporting junk is to mitigate its impact and prevent it from affecting other users. Apple employs a range of actions to achieve this, tailored to the specific type of junk and the platform on which it appears. These actions are designed to be effective while also striving for fairness.
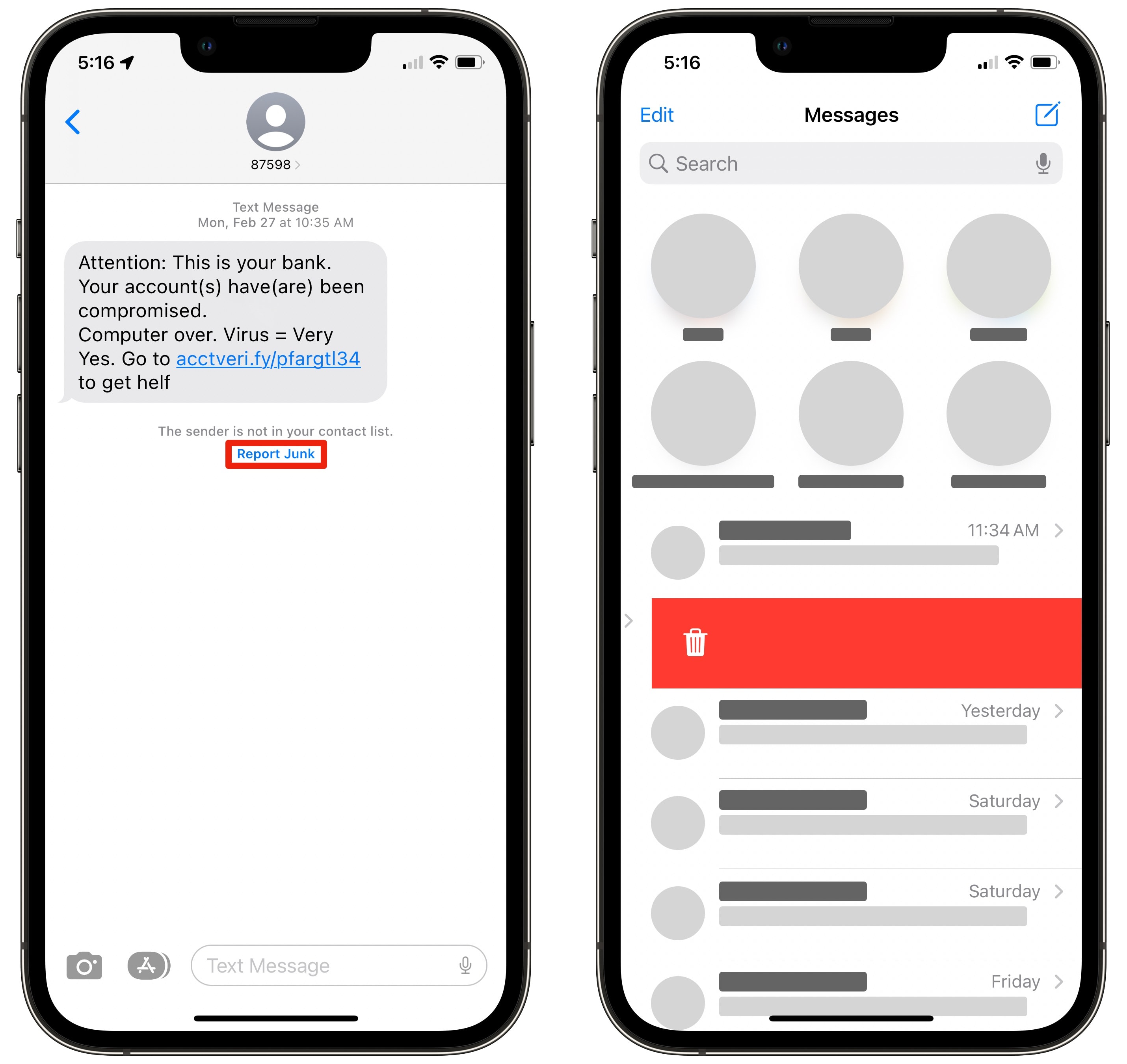
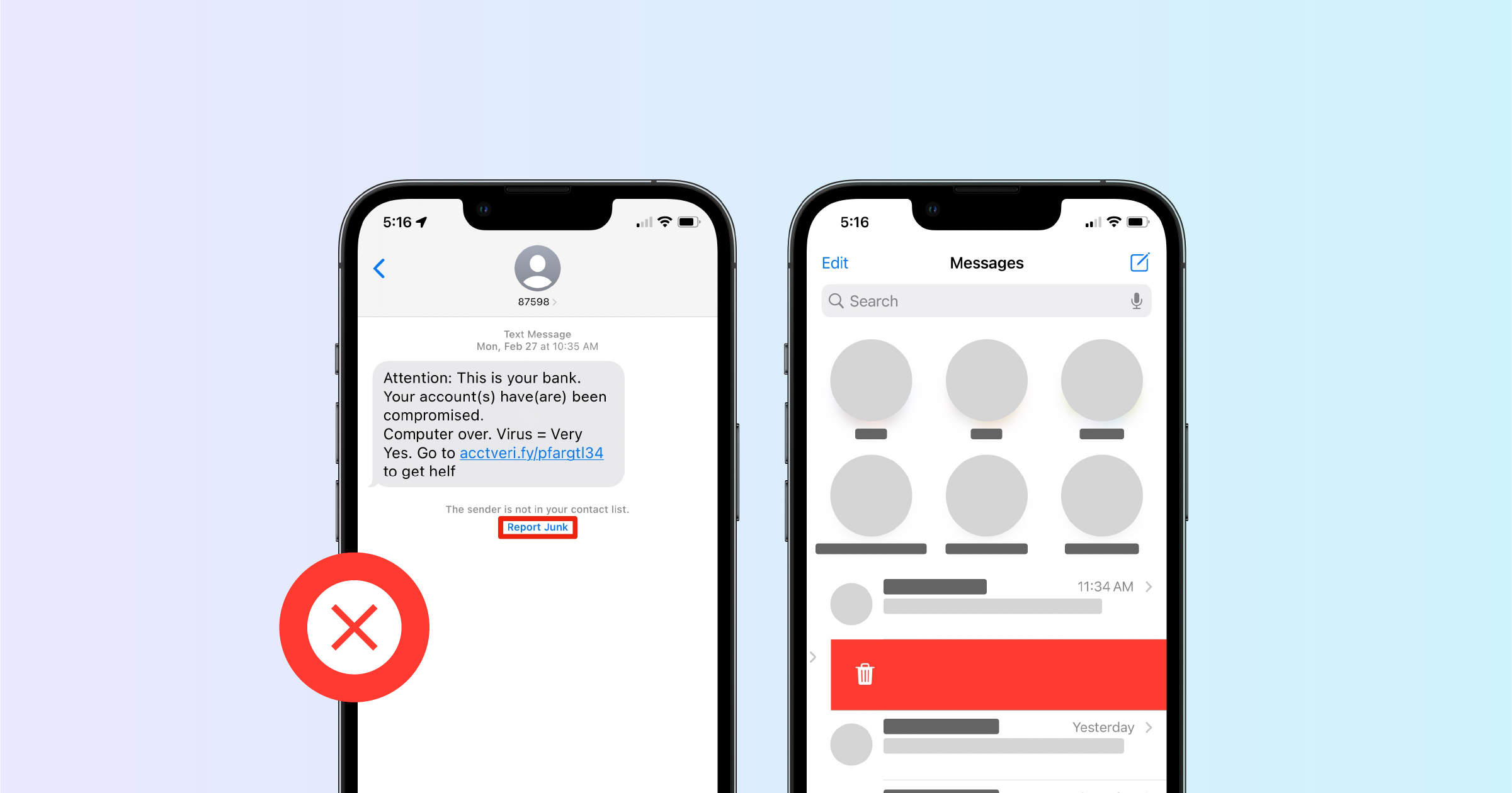
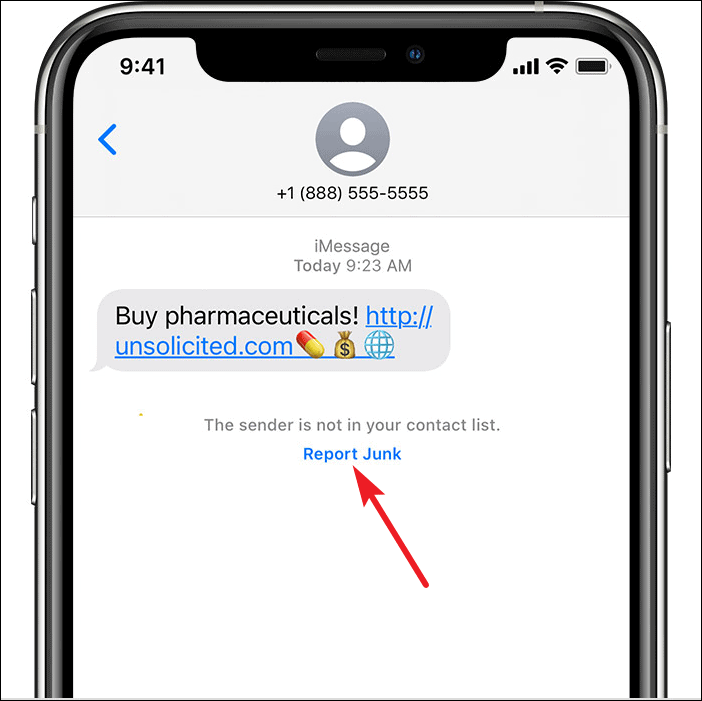
Blocking and Filtering
For individual users, reporting junk often triggers immediate personal action. When you report a message as junk in iMessage, for example, you are typically given the option to block the sender. This prevents future messages from that specific contact from reaching your device. Similarly, in Mail, reporting spam automatically filters similar messages into the Junk folder, and Apple’s systems learn from these actions to improve future filtering.
Content Removal and Service Suspension
Beyond individual blocking, Apple takes action against the source of the junk. This can involve removing offending content from their platforms, such as a malicious app from the App Store or spam comments from a community forum. In more severe cases, the accounts of users who repeatedly engage in abusive behavior or who are responsible for distributing widespread junk can be suspended or permanently terminated from Apple services. This serves as a deterrent and helps maintain the integrity of the platform.
Refining Security Measures and Educating Users
The data gathered from reported junk is invaluable for improving Apple’s overall security posture. By analyzing the tactics and techniques used in reported junk, Apple can proactively update its security protocols, patch vulnerabilities, and enhance its detection systems. Furthermore, Apple uses these insights to educate users about common scams and how to protect themselves. This includes providing tips on identifying phishing attempts, securing Apple IDs, and recognizing the signs of malware. While the focus is on the action Apple takes, the ultimate aim is to create a more secure environment for everyone.
Continuous Improvement and the Future of Junk Reporting
The fight against digital junk is an ongoing battle. As technology evolves and bad actors adapt their methods, Apple must continuously innovate and refine its approach to reporting and mitigating junk. The effectiveness of their current systems is a testament to their commitment, but the landscape of online threats is constantly shifting.
Evolving Threat Landscape and Adaptive Systems
The nature of junk and spam is not static. New forms of social engineering, sophisticated phishing campaigns, and evolving malware are constantly emerging. Apple’s reporting systems must be adaptive, capable of identifying and responding to these new threats in near real-time. This requires ongoing research and development, ensuring that their machine learning models and human moderation strategies remain cutting-edge.
The Role of AI in Enhanced Detection
Artificial intelligence will undoubtedly play an even more significant role in the future of junk reporting. Advanced AI can analyze vast datasets to identify subtle patterns and anomalies that might be missed by current systems. This could lead to even more precise and proactive detection of malicious content, reducing the burden on users to report issues and minimizing the window of opportunity for attackers.
User Education and Empowerment
While Apple focuses on the technical aspects of junk reporting, empowering users with knowledge is equally important. A well-informed user base is a powerful first line of defense. Continued efforts in user education, highlighting best practices for digital security and providing clear guidance on how to identify and report suspicious activity, will remain a cornerstone of Apple’s strategy. The synergy between robust technical systems and an educated user community is the most effective way to combat the persistent challenge of reported junk.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.