In the world of enterprise technology, we often speak of “growth,” “innovation,” and “scaling.” However, we rarely discuss the more painful, yet necessary, counterpart to growth: extraction. In a technical sense, a “tooth extraction” refers to the surgical removal of legacy systems, decayed codebases, or obsolete hardware that threatens the health of the overall digital ecosystem. Just as a dentist must remove a severely decayed molar to prevent sepsis or structural damage to the jaw, a Chief Technology Officer (CTO) must occasionally perform an “extraction” of tech debt to ensure the survival of the business.

But what does the healing process look like after such a significant technical intervention? It is not instantaneous. Just as biological healing follows a predictable sequence—clotting, granulation, and bone regeneration—the recovery of a tech stack after the removal of a core component follows a specific trajectory. Understanding what this healing looks like is essential for managing stakeholder expectations and ensuring long-term system stability.
The Diagnosis: When Legacy Systems Become the “Infected Tooth”
Before we can understand healing, we must understand the necessity of the extraction. In technology, “infection” manifests as tech debt—outdated software, unpatched security vulnerabilities, or monolithic architectures that no longer support modern API integrations.
Identifying the Point of No Return
Not every outdated piece of software needs extraction; many can be “filled” with patches or “crowned” with new wrappers. However, an extraction is required when the cost of maintenance exceeds the cost of replacement, or when the system poses a systemic risk. This is often seen in legacy banking systems or aging COBOL-based infrastructures where the “root” of the system is so decayed that it can no longer support the weight of modern digital demands.
The Surgical Plan: Mapping Dependencies
A biological tooth extraction is risky because of nerve proximity; a technical extraction is risky because of dependencies. Before the “tooth” is pulled, architects must map every integration point. If you remove an aging authentication server, what happens to the secondary apps relying on its handshake? This phase is the “pre-op,” where the “surgical site” is cleaned and prepared through redundant backups and sandbox testing.
Phase One: The Immediate Post-Extraction Period (24–72 Hours)
In clinical terms, the first stage of healing is the formation of a blood clot. In the tech world, this translates to immediate system stabilization. When a legacy system is switched off (the extraction), the immediate goal is to ensure the “wound” doesn’t bleed—meaning, we must prevent cascading failures across the network.
Stabilizing the Network “Clot”
The first 24 to 72 hours after removing a major software component are the most critical. This is the period of heightened monitoring. Engineers look for “socket” stability—ensuring that the new microservice or the cloud-native replacement is handling the traffic that the old system once managed. Healing at this stage looks like a stabilized dashboard: error rates may spike briefly but should plateau as load balancers and traffic-shaping rules take effect.
Managing the “Pain” of User Friction
Just as a patient feels discomfort once the anesthesia wears off, users often feel the “pain” of a tech extraction through changed interfaces or temporary latency. Professional tech management during this phase involves high-frequency communication. A “healing” tech infrastructure is one where the support tickets are being resolved faster than they are being created, signaling that the initial shock of the removal is being managed successfully.
Phase Two: Granulation and Digital Integration (Weeks 1–3)
Once the initial shock of the extraction has passed, the body begins to produce granulation tissue—a scaffold for new growth. In a tech ecosystem, this is the phase where the new solution begins to weave itself into the existing fabric of the company’s digital strategy.
Rebuilding the Middleware Scaffold
During weeks one through three, the “healing” looks like the successful deployment of middleware and APIs that bridge the gap left by the old system. If a monolithic database was extracted and replaced with a distributed NoSQL solution, this is the time when data synchronization reaches a state of “confluence.” We see the new system beginning to “talk” fluently with the rest of the stack.
Automated Patching and Refinement
A healthy recovery involves continuous integration and continuous deployment (CI/CD) pipelines working overtime. As the “digital tissue” grows, developers will find small bugs—the “inflammation” of the tech world. A healing system doesn’t hide these bugs; it identifies them through robust observability tools (like Datadog or New Relic) and patches them rapidly. This is the period where the system’s “immune response” (its automated testing suites) is most active, ensuring that the new code is being accepted by the host environment.
Phase Three: Structural Hardening and Final Maturation (Months 1–6)
In a physical tooth extraction, it takes months for the jawbone to fully regrow and fill the void. In a corporate tech environment, the final stage of healing is structural hardening. This is where the temporary “bridge” is replaced by permanent, high-performance architecture.
From Vulnerability to Scalability
A healed tech stack is one that is stronger than it was before the extraction. By the three-to-six-month mark, the new system should be fully optimized. The “void” left by the legacy software has been filled with scalable, cloud-native components that allow for faster iteration. Healing at this stage is measured by performance metrics: reduced latency, lower server costs, and higher uptime. The “scar tissue” has vanished, and the new infrastructure feels like a natural part of the organism.
The Security Audit: A “Post-Op” Checkup
No extraction is complete without a final verification. In tech, this is the comprehensive security audit or penetration test. This ensures that the removal of the old system hasn’t left any “exposed nerves”—security holes that hackers could exploit. A fully healed system passes these audits with flying colors, proving that the digital “extraction” has not only removed a problem but has also reinforced the perimeter of the entire enterprise.
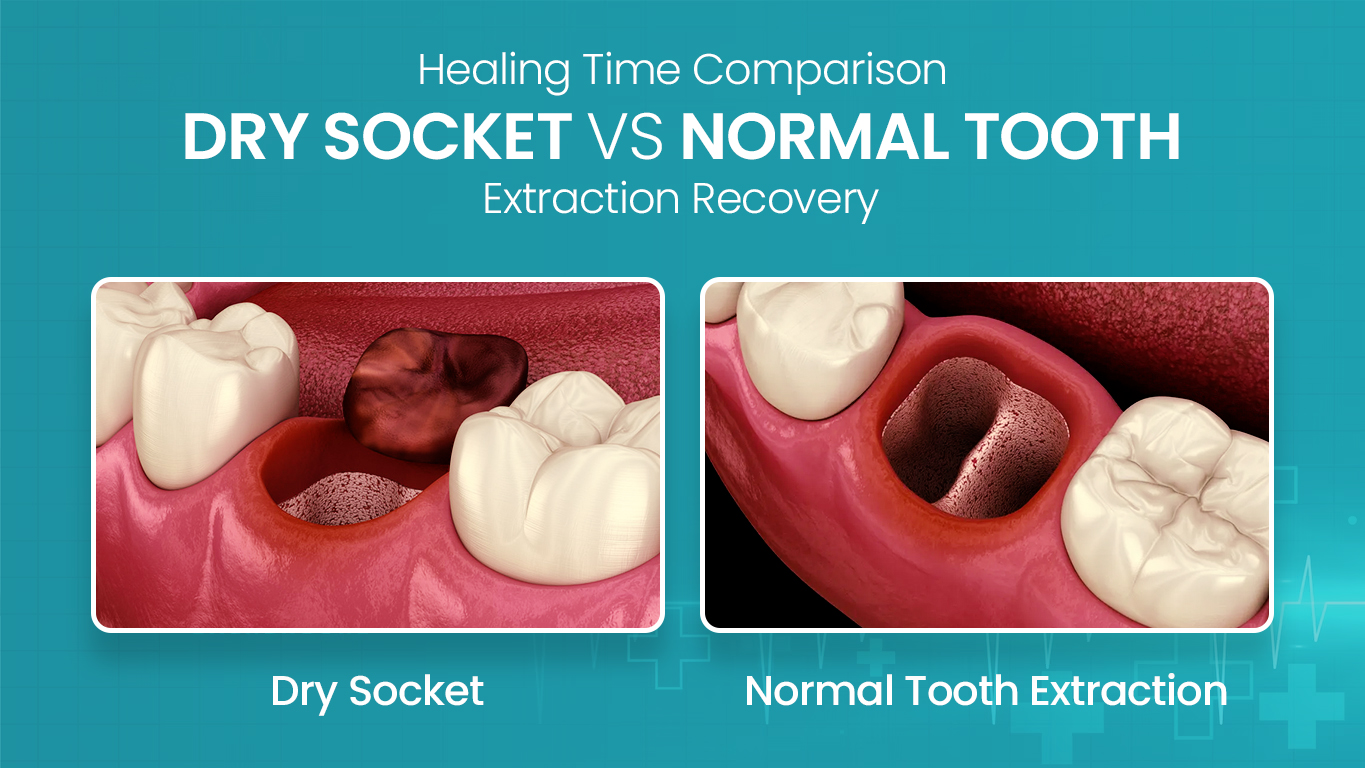
Avoiding the “Dry Socket” of Software Development: Risk Mitigation Strategies
In dentistry, a “dry socket” occurs when the blood clot is dislodged, exposing the bone and causing intense pain. In technology, a “digital dry socket” occurs when a legacy system is removed, and the replacement fails, leaving a functional vacuum that halts business operations.
The Importance of Observability Tools
To prevent a digital dry socket, organizations must invest in “imaging”—or, in tech terms, deep observability. Real-time telemetry allows engineers to see if the “clot” (the initial replacement) is holding. If a service begins to fail, automated “irrigation” (rollback scripts or failover clusters) must be triggered immediately to prevent the “infection” from spreading to the rest of the network.
Transitioning from “Triage” to “Growth”
The ultimate sign of a successful tooth extraction healing process is when the organization stops talking about the “removal” and starts talking about “capabilities.” When the focus shifts from “how do we survive without the old Mainframe?” to “how do we leverage our new AI-integrated cloud environment?”, the healing is complete. The extraction was successful, the recovery was managed with precision, and the digital organism is now healthier, faster, and more resilient than ever before.

Conclusion: The Necessity of Professional Intervention
What does a tooth extraction healing look like? In the tech world, it looks like a disciplined transition from fragility to agility. It is a process that requires patience, the right set of diagnostic tools, and a clear vision of the final “smile”—a tech infrastructure that is free of decay and ready for the future. By following a structured “post-operative” plan, businesses can ensure that their technical extractions lead not to systemic failure, but to a new era of digital health.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.