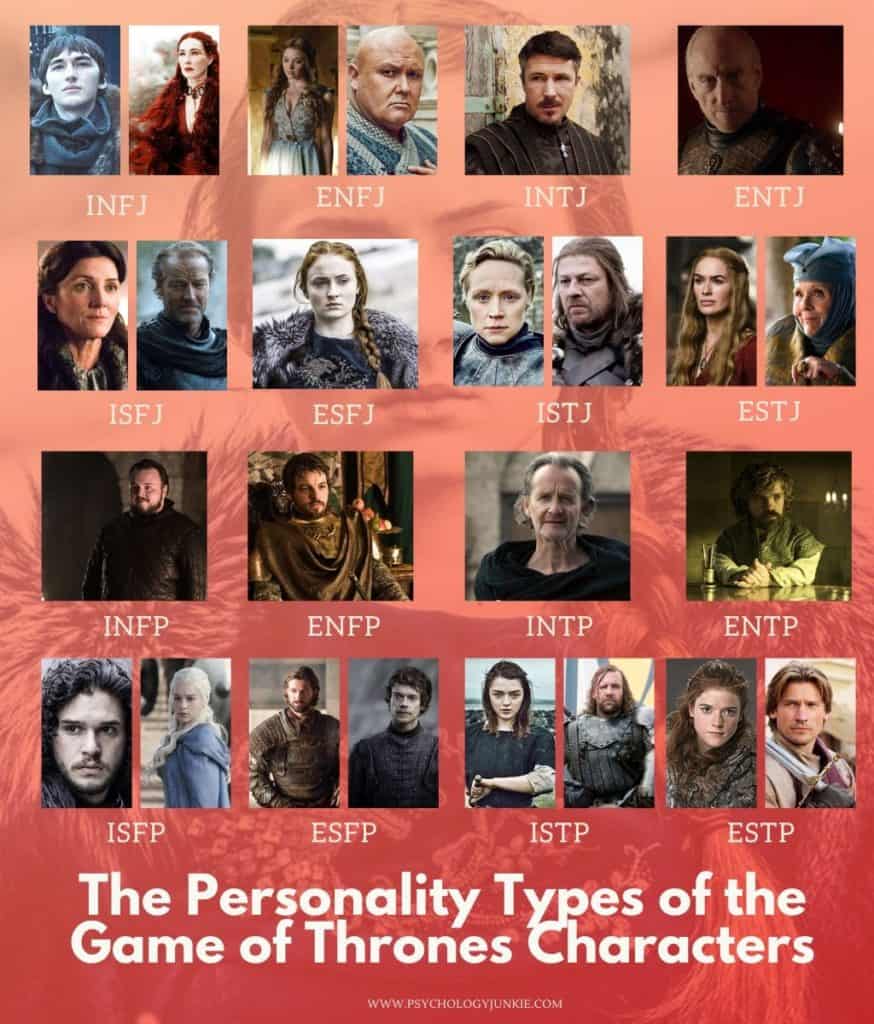
The allure of Westeros and its complex tapestry of characters has captivated audiences worldwide. Beyond the dragons and political intrigue, the individuals inhabiting this fictional realm represent distinct archetypes, each with unique motivations, strengths, and weaknesses. While the question “What character in Game of Thrones are you?” often serves as a lighthearted personality quiz, its deeper implications can be explored through a Tech lens. In the digital age, understanding these character archetypes offers valuable insights into how we navigate our professional lives, interact with technology, and even how we might be perceived in the vast, interconnected landscape of the internet. This article delves into how key Game of Thrones characters embody distinct digital archetypes, examining their traits through the prism of technology trends, software applications, AI tools, and the ever-evolving digital security landscape.

The Strategist: Navigating the Digital Battlefield
Characters like Tyrion Lannister and Varys epitomize strategic thinking, a crucial trait in both Westeros and the tech world. Their ability to analyze complex situations, anticipate threats, and devise intricate plans mirrors the sophisticated strategies employed in cybersecurity, software development, and data analysis.
The Master of Whispers: Information Gathering and Network Analysis
Varys, the self-proclaimed “Spider,” is the ultimate information broker. His vast network of informants and his skill in piecing together disparate fragments of information directly correlate with advanced data aggregation and analysis techniques used in technology.
- AI-Powered Intelligence Gathering: In the modern tech landscape, artificial intelligence is revolutionizing information gathering. Just as Varys utilized his “little birds,” AI algorithms can scour the internet, social media, and databases to collect vast amounts of data. This can range from market research and competitive analysis to identifying emerging technological trends. Tools like sophisticated web scrapers and natural language processing (NLP) engines can sift through unstructured data, identifying patterns and insights that would be impossible for humans to detect manually. Think of AI as Varys’s ultimate digital network, constantly monitoring and reporting.
- Network Security and Vulnerability Assessment: Varys’s ability to understand the intricate power dynamics and hidden weaknesses within Westeros is analogous to network security professionals identifying vulnerabilities in complex digital systems. They map out networks, analyze potential entry points, and develop strategies to defend against threats. Penetration testing tools, intrusion detection systems (IDS), and security information and event management (SIEM) platforms all function as digital equivalents of Varys’s espionage, constantly watching for anomalies and potential breaches.
- Predictive Analytics in Software Development: The art of anticipating future outcomes is paramount in software development and product management. Varys’s foresight in political maneuvering can be seen as a precursor to predictive analytics. By analyzing past trends and current data, developers and product managers can predict user behavior, potential bug occurrences, and the future success of new features. Machine learning models are trained on historical data to forecast these outcomes, allowing for proactive problem-solving and more efficient development cycles.
The Cunning Advisor: Strategic Decision-Making and Algorithm Design
Tyrion Lannister, despite his physical stature, wields immense intellectual power. His strategic acumen, particularly in times of crisis, highlights the importance of effective decision-making algorithms and strategic software design.
- Algorithmic Strategy in Gaming and Simulation: The strategic depth of Game of Thrones, with its shifting alliances and complex political landscapes, can be directly translated into the world of gaming and simulations. AI algorithms are used to create intelligent non-player characters (NPCs) that can strategize, adapt, and even deceive players, mirroring the cunning of characters like Tyrion. These algorithms are designed to optimize player engagement and create challenging, dynamic gameplay experiences. Similarly, complex simulations in fields like economics or disaster management rely on sophisticated algorithms to model intricate scenarios and test strategic responses, much like Tyrion would weigh various courses of action.
- Business Intelligence and Data Visualization Tools: Tyrion’s ability to distill complex information into actionable insights for his rulers is akin to the role of business intelligence (BI) tools. These platforms aggregate data from various sources, analyze it, and present it in easily understandable formats, such as dashboards and charts. This allows leaders to make informed strategic decisions, identify areas for improvement, and allocate resources effectively. Imagine Tyrion using a modern BI dashboard to understand the economic impact of a dragon attack or the morale of the Westerosi populace.
- Personalized User Experience (UX) Design: Tyrion’s understanding of people and their motivations, which he often leveraged to his advantage, translates into the principles of user experience (UX) design. Effective UX design aims to understand the user’s needs, preferences, and behaviors to create intuitive and engaging digital products. This involves extensive user research, prototyping, and iterative testing, all aimed at crafting a personalized experience that caters to individual user archetypes, much like Tyrion would tailor his advice to the specific personality of the person he was advising.
The Warrior and The Innovator: Driving Force and Technological Advancement
Characters like Jon Snow and Daenerys Targaryen embody the drive for change and the relentless pursuit of their goals, often necessitating the adoption and development of new technologies. Their actions can be seen as metaphors for innovation cycles and the disruptive potential of new tech.
The Leader of Men: Mobilization, Collaboration, and Project Management
Jon Snow, the reluctant leader, consistently rallies people to a common cause. His ability to inspire loyalty and unite disparate groups for a singular objective mirrors the principles of modern project management and collaborative software platforms.
- Collaborative Software and Team Communication Tools: Jon’s efforts to unite the Night’s Watch and later the Northern houses against existential threats find a parallel in the proliferation of collaborative software. Platforms like Slack, Microsoft Teams, and Asana are designed to facilitate seamless communication, task management, and shared document access, enabling teams to work efficiently towards a common goal, even across vast distances. These tools are the digital battlegrounds where collective action is orchestrated.
- Agile Project Management Methodologies: The dynamic and often unpredictable nature of Jon’s campaigns, where plans had to adapt rapidly to changing circumstances, reflects the principles of Agile project management. Agile methodologies, such as Scrum and Kanban, emphasize iterative development, flexibility, and continuous feedback, allowing teams to respond quickly to unforeseen challenges and deliver value incrementally. This mirrors Jon’s ability to adapt his strategies on the fly, from fighting the White Walkers to negotiating with Wildlings.
- Digital Twin Technology in Large-Scale Operations: In large-scale operations, whether military or industrial, the concept of a “digital twin” is increasingly relevant. This is a virtual replica of a physical asset or system that is updated in real-time with data from sensors. Jon’s leadership in coordinating defenses against the White Walkers, where understanding troop movements, enemy positions, and terrain was critical, is akin to utilizing a digital twin for strategic planning. Such technology allows for real-time monitoring, simulation of scenarios, and optimization of resource allocation, ensuring that leaders have a comprehensive and up-to-the-minute understanding of their operational environment.
The Breaker of Chains: Disruptive Innovation and Emerging Technologies
Daenerys Targaryen, with her dragons and her ambition to reshape the world, represents disruptive innovation. Her arrival in Westeros, a force that fundamentally alters the existing power structures, is akin to the impact of revolutionary technologies that disrupt established industries.
- AI-Powered Automation and Industrial Revolution 4.0: Daenerys’s vision for a new world, free from the constraints of the old order, can be linked to the transformative power of AI-driven automation and the ongoing Industrial Revolution 4.0. AI is automating tasks previously thought to be solely within human capacity, from manufacturing and logistics to customer service and creative content generation. This technological shift has the potential to fundamentally reshape economies and societies, much like Daenerys’s arrival challenged the existing feudal system.
- Blockchain and Decentralized Technologies: The concept of “breaking chains” and establishing a new order also resonates with the principles of blockchain and decentralized technologies. These technologies aim to create systems that are more transparent, secure, and resistant to centralized control. Imagine Daenerys utilizing a decentralized ledger to record land ownership or establish a fairer system of trade, free from the manipulative practices of the old lords. Cryptocurrencies and decentralized autonomous organizations (DAOs) are embodiments of this disruptive potential.
- The Rise of New Platforms and Ecosystems: Daenerys’s conquest was about establishing a new dominion, much like how dominant technology platforms create their own ecosystems. Companies like Apple and Google have built vast empires by creating integrated hardware, software, and service ecosystems that are difficult for competitors to penetrate. The “App Store” or “Google Play Store” are digital realms where innovation flourishes, but also where dominance is established, mirroring Daenerys’s aim to control the narrative and the flow of power in Westeros.
The Guardians: Maintaining Order and Ensuring Digital Security
Characters like Ned Stark and Brienne of Tarth embody a strong moral compass and a commitment to duty and protection. Their steadfastness and integrity translate into the critical role of digital security and the ethical considerations within the tech industry.
The Hand of the King: Principled Leadership and Ethical Tech Development
Ned Stark, though ultimately tragic, represented unwavering integrity and a commitment to justice. His principled stand, even when facing overwhelming opposition, highlights the importance of ethical considerations in technology development and leadership.
- Ethical AI and Algorithmic Bias Detection: Ned’s pursuit of truth and fairness, even at personal cost, aligns with the growing imperative for ethical AI development. As AI systems become more pervasive, concerns about algorithmic bias, privacy violations, and job displacement are paramount. Tools and methodologies are being developed to detect and mitigate bias in AI algorithms, ensuring that these technologies are developed and deployed responsibly. This is the digital equivalent of Ned investigating corruption in King’s Landing.
- Data Privacy and Security Best Practices: Ned’s inherent sense of duty and his commitment to upholding the law directly relate to the principles of data privacy and security. In an era where personal data is a valuable commodity, organizations have a responsibility to protect it. Implementing robust security measures, adhering to privacy regulations like GDPR, and fostering a culture of data stewardship are essential. Think of Ned as a digital gatekeeper, ensuring that sensitive information is not misused or compromised.
- Transparency and Accountability in Software Engineering: Ned’s desire for an honest and just kingdom mirrors the increasing demand for transparency and accountability in software engineering. Open-source software, where the code is publicly available, allows for community review and identification of vulnerabilities. Similarly, clear documentation, robust testing, and traceable development processes contribute to building more trustworthy and secure software.
The Shield of the Realm: Cybersecurity and Protective Technologies
Brienne of Tarth, fiercely loyal and dedicated to protecting the innocent, embodies the spirit of cybersecurity professionals. Her unwavering commitment to her oaths and her willingness to defend those in her charge parallel the constant vigilance required to safeguard digital assets and user data.
- Threat Detection and Incident Response Systems: Brienne’s readiness to confront any danger, from common bandits to formidable knights, reflects the proactive and reactive nature of cybersecurity. Threat detection systems continuously monitor networks for malicious activity, while incident response teams are prepared to act swiftly and decisively when an attack occurs. These systems and teams are the digital knights, standing guard against cyber threats.
- Endpoint Security and Multi-Factor Authentication (MFA): Protecting individual users, the “innocent” of the digital realm, is crucial. Endpoint security solutions, such as antivirus software and firewalls, act as individual shields for devices. Multi-factor authentication (MFA) adds an extra layer of defense, ensuring that only authorized individuals can access their accounts, much like Brienne’s personal vigilance would ensure no one could harm those under her protection.
- Digital Forensics and Cybercrime Investigation: When a breach does occur, the work of digital forensic investigators mirrors Brienne’s dedication to seeking justice. They meticulously collect and analyze digital evidence to understand how an attack happened, identify the perpetrators, and prevent future incidents. This painstaking process of uncovering the truth is vital for maintaining order and security in the digital world.
In conclusion, the characters of Game of Thrones, through their distinct personalities and actions, offer a rich tapestry of archetypes that can be meaningfully analyzed within the Tech domain. By understanding how these fictional figures embody strategic thinking, disruptive innovation, and the principles of guardianship, we gain a deeper appreciation for the complexities of the digital world and our roles within it. Whether you identify with the cunning strategist, the driven innovator, or the steadfast guardian, your approach to technology, your engagement with digital tools, and your commitment to digital security all reflect a unique character in the ongoing narrative of our interconnected lives.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.