In our increasingly interconnected world, understanding the fundamental building blocks of the internet is paramount. Among these, the Internet Protocol (IP) address stands out as a critical yet often misunderstood component. Frequently depicted in media as a direct link to a person’s identity, the reality of an IP address – what it is, what information it reveals, and what can truly be done with it – is far more nuanced. For anyone navigating the digital landscape, from tech enthusiasts to business strategists and individuals concerned about personal finance and online security, demystifying the IP address is an essential step towards informed digital citizenship.
This article delves into the multifaceted nature of IP addresses, exploring their legitimate and beneficial uses in technology, marketing, and security, as well as the potential for misuse that raises significant privacy and security concerns. We’ll examine how IP addresses underpin everything from simple website browsing to sophisticated cybersecurity measures and targeted advertising campaigns. By understanding the capabilities and limitations associated with an IP address, individuals and businesses can better protect themselves, optimize their digital strategies, and navigate the complex web of online interactions with greater confidence and awareness.
Understanding IP Addresses: The Basics of Digital Identity
Before we can explore what can be done with an IP address, it’s crucial to grasp what it fundamentally represents and how it functions within the vast architecture of the internet. Think of it as a digital address label, vital for guiding data packets to their correct destination.
What Exactly is an IP Address?
An IP address (Internet Protocol address) is a unique numerical label assigned to every device connected to a computer network that uses the Internet Protocol for communication. This includes everything from your smartphone and laptop to web servers and smart home devices. Its primary function is twofold: identification and location addressing. It identifies a device on a network and provides the mechanism for that device to be located and communicated with by other devices.
There are two main types of IP addresses in use today:
- IPv4 (Internet Protocol version 4): This is the older and more common version, consisting of four sets of numbers separated by dots (e.g.,
192.168.1.1). With approximately 4.3 billion unique addresses, IPv4 is slowly running out due to the explosion of internet-connected devices. - IPv6 (Internet Protocol version 6): Developed to address the exhaustion of IPv4 addresses, IPv6 uses a longer, alphanumeric format (e.g.,
2001:0db8:85a3:0000:0000:8a2e:0370:7334). It offers an astronomically larger address space, capable of supporting the billions of devices expected to come online in the future.
Without an IP address, data packets wouldn’t know where to go, making internet communication impossible. Every time you send an email, stream a video, or browse a website, your IP address is involved in routing that data.
Dynamic vs. Static IPs
Another important distinction lies between dynamic and static IP addresses:
- Dynamic IP Addresses: Most home and small business users have dynamic IP addresses. These are temporarily assigned by your Internet Service Provider (ISP) from a pool of available addresses. They can change periodically (e.g., when you restart your router, or your lease expires). This is cost-effective for ISPs and offers a basic layer of privacy as your public IP isn’t permanently tied to your specific device. However, it doesn’t prevent tracking over shorter periods.
- Static IP Addresses: These are fixed and never change. They are typically used by businesses hosting their own websites, email servers, or other services that require a consistent address for reliability and accessibility. While offering stability, static IPs can also make it easier to link persistent online activity to a specific entity or location.
The Information an IP Address Reveals (and What It Doesn’t)
While an IP address is a unique identifier, it’s crucial to understand its limitations regarding personal information. What an IP address can typically reveal includes:
- Geographic Location: It can pinpoint the general vicinity of your internet connection – usually down to the city, region, and country, but rarely your precise street address or specific building. This information is derived from databases that map IP addresses to physical locations, often based on the ISP’s infrastructure.
- Internet Service Provider (ISP): The IP address identifies the company that provides your internet service.
- Network Information: It can indicate the type of network you are on (e.g., corporate, residential, mobile data).
What an IP address typically does not directly reveal (without additional information or specific legal action) includes:
- Your Name, Home Address, or Phone Number: An IP address itself is not linked to your personal identity in publicly accessible databases. ISPs hold this direct customer information, but it is private and protected by privacy policies and often requires a legal warrant or subpoena to be disclosed.
- Your Personal Browsing History (unless logged by a specific service): While an IP address is part of your online activity, it doesn’t inherently expose your full browsing history to a third party simply by knowing your IP. Websites you visit log your IP, but not your overall internet usage.
- The Specific Device: While it identifies a connection point, it doesn’t distinguish between multiple devices (like a laptop, tablet, or smart TV) sharing the same public IP address on a home network.
Understanding these fundamentals is the first step towards appreciating the dual potential of IP addresses – as a powerful tool for connectivity and analysis, but also as a point of vulnerability if mishandled.
Legitimate Uses of IP Addresses: Beyond Simple Identification
The primary purpose of IP addresses is to facilitate communication across networks, but their utility extends far beyond simple packet routing. Businesses, cybersecurity professionals, and network administrators leverage IP data for a multitude of legitimate and beneficial purposes, aligning closely with Tech, Brand, and Money aspects of digital operations.
Enhancing Digital Security and Preventing Fraud
For businesses and individuals alike, IP addresses are a cornerstone of robust digital security strategies. In the realm of Tech and Digital Security:
- Threat Detection and Blocking: Cybersecurity systems constantly monitor IP addresses for signs of malicious activity. If an IP address is known to be associated with spamming, malware distribution, or hacking attempts (e.g., from botnets or known attack vectors), it can be added to blocklists (blacklists) to prevent further access to networks or services. This is crucial for protecting corporate networks, sensitive data, and customer information.
- Fraud Prevention: In financial transactions and online banking, IP address analysis is a key tool in preventing fraud. Unusual login attempts from geographically disparate locations, multiple failed login attempts from a single IP, or transactions originating from high-risk countries can trigger security alerts, protecting both users and the Money institutions. For e-commerce, linking a transaction’s IP to the billing address region helps flag potentially fraudulent orders.
- DDoS Protection: Distributed Denial of Service (DDoS) attacks overwhelm a server with traffic from numerous compromised machines (often identified by their IP addresses). Security services use IP data to identify and filter out malicious traffic, ensuring legitimate users can still access services.
- Geo-Blocking and Content Licensing: Many online services, especially streaming platforms and gaming companies, use IP addresses to enforce content licensing agreements. This ensures that copyrighted material is only accessible in approved geographic regions, protecting content creators and their Brand value while also maintaining legal compliance.
Geo-Targeting and Content Customization
The ability to determine a user’s general geographic location based on their IP address is invaluable for marketing and user experience, contributing significantly to Brand Strategy and Marketing:
- Localized Content Delivery: Websites can automatically display content relevant to a user’s region, such as local news, weather forecasts, or currency information. E-commerce sites can show local pricing and shipping options. This personalizes the user experience and improves engagement.
- Targeted Advertising: Advertisers leverage IP-based location data to deliver geographically specific advertisements. This allows businesses to reach potential customers in their service area, optimizing ad spend and improving campaign effectiveness, directly impacting Money through improved ROI for Brand marketing.
- Language Preference: While often set by browser settings, IP location can serve as a fallback or confirmation for delivering content in the appropriate language, enhancing user experience and accessibility.
- Legal and Regulatory Compliance: Certain online services or products may only be legally offered in specific jurisdictions. IP-based geo-targeting helps companies comply with these regulations, mitigating legal risks and protecting their Corporate Identity and reputation.
Network Management and Troubleshooting
Within the realm of Tech and network administration, IP addresses are fundamental for maintaining and optimizing network performance:
- Diagnosing Network Issues: Network administrators use IP addresses to identify and troubleshoot connectivity problems, pinpointing where data flow is interrupted or slow. This is crucial for maintaining uptime and productivity.
- Load Balancing: For large websites and online services, IP addresses help distribute incoming traffic across multiple servers. This “load balancing” prevents any single server from becoming overwhelmed, ensuring reliable service and optimal performance for users.
- Server Logs and Analytics: Web servers log the IP addresses of visitors, along with other information like the pages viewed and time spent. These logs are vital for website analytics, helping businesses understand user behavior, identify popular content, and optimize website design and functionality – feeding into Brand insights and Online Income strategies.
Analytical Insights for Businesses
Beyond basic network functions, aggregated and anonymized IP data provides powerful analytical insights that benefit Brand Strategy and Business Finance:
- Understanding User Demographics: While not revealing personal identities, IP data allows businesses to understand the geographic distribution of their user base. This insight can inform market expansion strategies, product development, and localized marketing efforts.
- Website Performance Optimization: By analyzing traffic patterns associated with different IP ranges, businesses can identify bottlenecks, optimize server locations (Content Delivery Networks), and improve overall website speed and responsiveness.
- Competitor Analysis: In some cases, businesses might analyze IP ranges associated with competitors to understand their online presence or identify potential areas of overlap or market opportunity.
- Ad Campaign Effectiveness: By linking ad clicks or conversions to the originating IP address (often in an aggregated, anonymous way), marketers can gauge the effectiveness of their campaigns in different regions or demographics, allowing for more efficient allocation of Marketing budgets and maximizing Online Income.
In essence, IP addresses are much more than just numbers; they are foundational to the internet’s operation and provide a wealth of data that, when used responsibly and ethically, can drive innovation, enhance security, and inform strategic business decisions.
The Dark Side: Malicious and Illegitimate Uses of IP Addresses
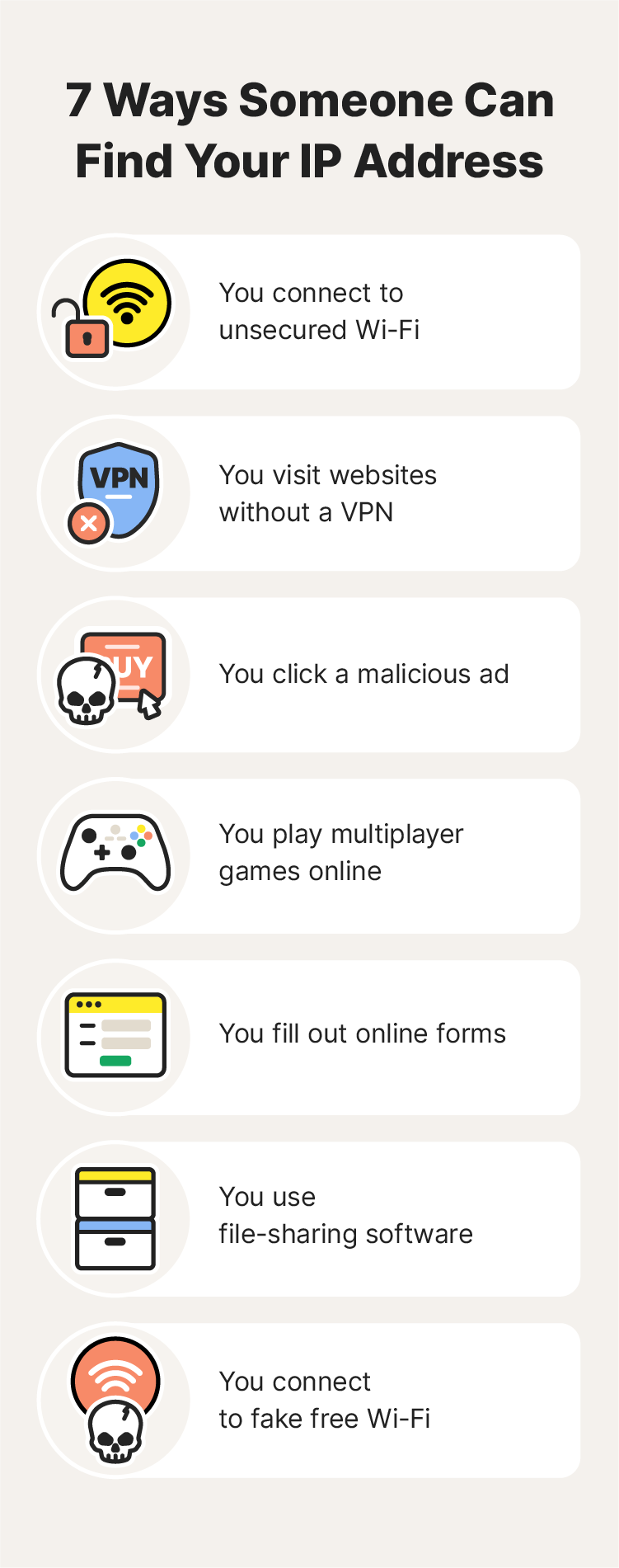
While IP addresses serve many legitimate and beneficial functions, their ability to identify a device’s connection point and general location also makes them a target for malicious actors. Understanding these risks is crucial for anyone interested in Digital Security and protecting their Personal Branding and Money.
Cyberattacks and Harassment
Malicious individuals can leverage IP addresses to orchestrate various forms of cyberattacks and online harassment:
- DDoS Attacks (Targeted): While broader DDoS attacks aim to shut down a service, a more targeted attack might use an individual’s IP address to specifically overwhelm their home network, disrupting their internet service. This can be a form of online harassment or a precursor to other attacks.
- Doxxing and Swatting (as a starting point): An IP address can be the initial piece of information used in a “doxxing” attempt, where attackers try to uncover more detailed personal information (like names, home addresses, phone numbers) associated with an individual. In extreme cases, this can escalate to “swatting,” where false reports are made to emergency services, leading to armed police (SWAT teams) being dispatched to an unsuspecting victim’s home. This is a severe threat to Digital Security and personal safety.
- Targeting Network Vulnerabilities: Knowing an IP address allows an attacker to scan that specific network for open ports or known software vulnerabilities. If successful, they could potentially gain unauthorized access, steal data, or install malware, directly impacting an individual’s Digital Security and potentially their Personal Finance if banking details are compromised.
- Online Harassment and Tracking: Persistent online harassers can use an IP address to roughly track a victim’s location, making them feel unsafe or exposed. While not precise, even approximate location data can be distressing and enable further stalking behaviors.
Unauthorized Tracking and Privacy Invasion
The collection and use of IP addresses for tracking, especially without explicit user consent, raise significant privacy concerns:
- Persistent Tracking Across Websites: While cookies are the primary tool for web tracking, IP addresses can also be used, especially to link different browsing sessions or devices, even if cookies are cleared. This allows companies (or malicious entities) to build more comprehensive profiles of user behavior, sometimes for purposes beyond simple analytics. This data can be sold or misused, impacting Digital Security and Personal Branding if sensitive behaviors are exposed.
- Creating User Profiles: By correlating IP addresses with other available data (such as browser type, operating system, visit times, and pages viewed), data brokers and advertisers can construct detailed profiles of individuals’ online habits, interests, and even inferred demographics. While not directly revealing identity, these profiles can be used for highly targeted advertising or even discriminatory practices. This practice directly relates to the ethics of Brand Strategy and how companies manage Corporate Identity in data handling.
- Data Harvesting: Malicious bots and scripts can sweep websites to collect IP addresses, often with the intent of using them for spamming, phishing, or other illicit activities. This kind of data harvesting poses a risk to any Brand or individual whose IP is collected.
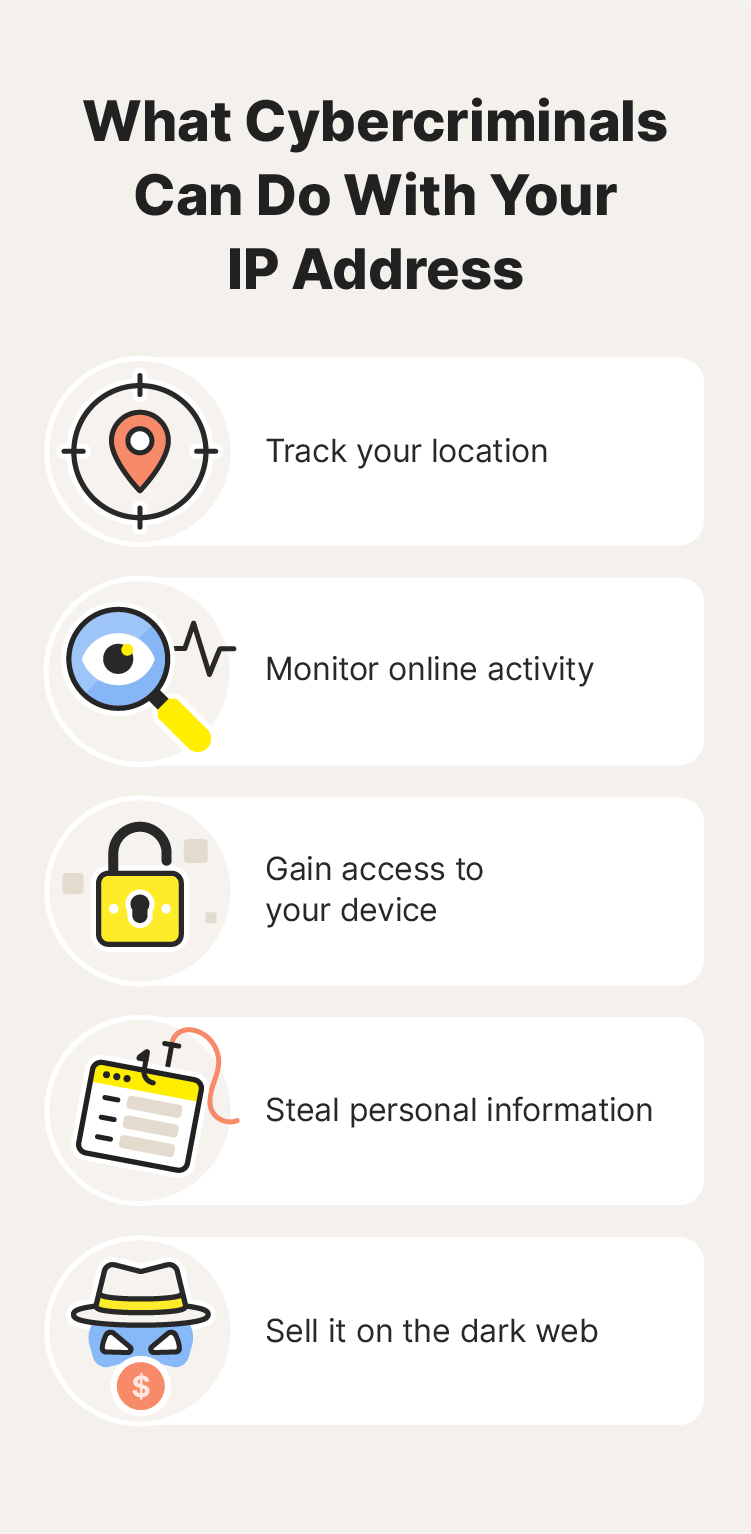
Exploiting Vulnerabilities and Identity Theft
An IP address can be a gateway for more serious cybercrimes, particularly when combined with other methods:
- Port Scanning and Exploitation: Attackers can use an IP address to scan for open ports on a device or network. Open ports can indicate services running on the system, some of which might have known vulnerabilities. For example, an open, unsecure remote desktop port could allow an attacker to gain full control of a computer.
- As a Step in Identity Theft: While an IP address alone doesn’t grant access to personal identity, it can be a crucial initial step. By identifying an ISP and approximate location, attackers might employ social engineering tactics (e.g., calling the ISP pretending to be the victim) to gain more information. If they manage to breach a network associated with that IP, they could potentially access personal files, financial records, or other data that facilitates Identity Theft, leading to significant Financial Tools misuse and personal Money loss.
- Facilitating Malware Delivery: Once an IP address’s vulnerabilities are identified, it can be specifically targeted for malware delivery. This could include ransomware (demanding Money for data release), spyware (stealing information), or botnet infections (turning the device into part of an attack network).
The potential for misuse of IP addresses underscores the critical importance of strong Digital Security practices, understanding privacy settings, and utilizing tools designed to protect one’s online footprint.
Protecting Your IP Address and Digital Privacy
In light of both the legitimate and malicious uses of IP addresses, safeguarding your digital privacy and enhancing your online security has become more important than ever. For individuals and businesses alike, understanding and implementing protective measures is key to managing Digital Security risks and maintaining a strong Brand reputation.
The Role of VPNs and Proxies
One of the most effective ways to obscure your real IP address and enhance your privacy is through the use of Virtual Private Networks (VPNs) and proxy servers, which are vital Tech tools for Digital Security:
- How They Work: When you use a VPN or proxy, your internet traffic is routed through a server operated by the VPN/proxy provider. Your IP address then appears as the IP address of that server, effectively masking your true location and identity from the websites and services you visit.
- Benefits of VPNs:
- Privacy: VPNs encrypt your internet traffic, preventing your ISP or other third parties from monitoring your online activities. This is crucial for protecting your browsing history, communications, and sensitive data.
- Security: By encrypting your data, VPNs make it much harder for cybercriminals to intercept and exploit your information, especially when using public Wi-Fi networks.
- Geo-Unblocking: VPNs can bypass geo-restrictions, allowing you to access content and services that might be unavailable in your actual geographic location. This can be beneficial for travelers or those wishing to access content library variations.
- Anonymity: While not truly anonymous, a VPN significantly increases your online privacy by obfuscating your real IP address.
- Proxies: Proxy servers offer a similar function by acting as an intermediary, but they typically offer less robust encryption and security features than a full VPN. They are often used for specific tasks like accessing geo-restricted content or circumventing simple network filters.
For businesses, VPNs are also critical for secure remote access, allowing employees to connect to corporate networks safely from anywhere, thus protecting sensitive business data and maintaining productivity.
Best Practices for Online Security
Beyond using VPNs, a holistic approach to Digital Security involves several best practices:
- Keep Software Updated: Regularly update your operating system, web browsers, antivirus software, and all applications. Updates often include critical security patches that fix vulnerabilities attackers could exploit.
- Use Strong, Unique Passwords: Employ complex passwords for all your online accounts and use a password manager to keep track of them. Enable two-factor authentication (2FA) wherever possible, adding an extra layer of security.
- Be Wary of Phishing and Suspicious Links: Exercise caution with emails, messages, or pop-ups that request personal information or ask you to click on unfamiliar links. Phishing attempts are designed to trick you into revealing sensitive data.
- Install and Maintain Antivirus/Anti-Malware Software: Reputable security software can detect and remove malicious programs that might attempt to capture your IP address or exploit network vulnerabilities.
- Configure Your Firewall: A firewall acts as a barrier between your device/network and the internet, controlling incoming and outgoing traffic. Ensure your operating system’s firewall is enabled and properly configured. For business networks, robust firewalls are indispensable.
- Limit Public Information Sharing: Be mindful of the personal information you share online, especially on social media. The less information available, the harder it is for malicious actors to correlate your IP address with your identity. This is key for Personal Branding and avoiding doxxing.
- Review Privacy Settings: Regularly check and adjust the privacy settings on your social media accounts, web browsers, and apps to control what data is collected and shared.
Understanding Data Privacy Laws
The legal landscape around IP addresses and data privacy is evolving, with significant implications for both individuals and Brands:
- GDPR (General Data Protection Regulation): In the European Union, GDPR considers IP addresses as personal data when they can be used to identify an individual. This places strict requirements on how businesses collect, process, and store IP addresses, demanding consent and providing individuals with rights over their data. Compliance is crucial for Corporate Identity and avoiding hefty fines.
- CCPA (California Consumer Privacy Act): Similar to GDPR, CCPA in California grants consumers more control over their personal information, including IP addresses, and imposes obligations on businesses regarding data handling and disclosure.
- Impact on Businesses: Companies that collect IP addresses for analytics, marketing, or security must ensure their practices align with these and other regional privacy laws. This involves clear privacy policies, obtaining explicit consent where necessary, and implementing robust data protection measures. Non-compliance can severely damage a Brand’s Reputation and incur significant Financial penalties. This highlights the importance of integrating Digital Security and privacy into overall Brand Strategy.
By embracing these protective measures and staying informed about the evolving digital landscape, individuals can significantly mitigate the risks associated with their IP address, while businesses can build trust and ensure legal compliance.
Conclusion
The IP address, a seemingly innocuous string of numbers, stands as a cornerstone of the internet’s functionality. It is simultaneously an essential technical utility, enabling global communication and countless digital services, and a potent piece of information with profound implications for privacy and security. From allowing web servers to deliver content to the correct device to facilitating geo-targeted marketing campaigns that fuel Brand Strategy and Online Income, its legitimate uses are vast and indispensable. In the realm of Tech, IP addresses are the backbone of network management, cybersecurity defenses, and data analytics that drive modern innovation.
However, as with any powerful tool, the IP address carries a “dark side.” Its ability to pinpoint a general location and identify an internet connection makes it a potential target for cyberattacks, unauthorized tracking, and various forms of online harassment. The risks to Digital Security, Personal Finance through fraud, and even physical safety through actions like swatting, underscore the critical need for vigilance.
For individuals, understanding what an IP address reveals and, more importantly, what it doesn’t, is the first step towards empowered digital citizenship. Employing tools like VPNs and adhering to best practices in online security – strong passwords, software updates, and cautious online behavior – are no longer optional but essential safeguards for one’s Personal Branding and well-being.
For businesses, the responsible handling of IP addresses is paramount. Compliance with stringent data privacy laws like GDPR and CCPA is not just a legal obligation but a cornerstone of building and maintaining a trustworthy Corporate Identity and a strong Brand Reputation. Ethical data practices are increasingly becoming a competitive differentiator, impacting not only customer trust but also a company’s financial health.
Ultimately, the power of an IP address is a double-edged sword. By embracing a proactive and informed approach to Tech and Digital Security, both individuals and organizations can harness its benefits while effectively mitigating its risks, ensuring a safer, more private, and more prosperous digital future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.