In the biological world, rabies is a lethal viral disease that attacks the central nervous system, characterized by its aggressive spread and devastating impact on the host. In the rapidly evolving landscape of information technology, we are witnessing the emergence of a digital equivalent. “Digital Rabies”—a metaphor for hyper-aggressive, self-replicating malware and ransomware—represents a tier of cyber threats that move with terrifying speed, bypass traditional defenses, and “infect” the core operational logic of global enterprises.
Understanding what these digital infections are caused by is no longer just a concern for IT departments; it is a fundamental requirement for business continuity and national security. To diagnose the causes of digital rabies, we must look beyond simple code errors and examine the complex intersection of human behavior, systemic technological vulnerabilities, and the weaponization of artificial intelligence.
The Anatomy of a Digital Infection: What Causes the Spread?
To identify the “pathogens” of the tech world, we must first understand that digital infections do not occur in a vacuum. They are the result of specific environmental conditions and structural weaknesses within a network’s architecture.
Biological Analogies in Computer Science
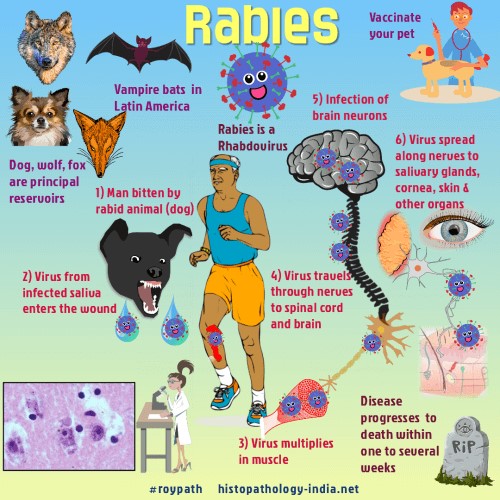
The term “computer virus” was not chosen by accident. Much like their biological counterparts, digital viruses require a host (a file or a program) and a method of transmission. However, “Digital Rabies” refers to a more virulent strain: the “Worm” and the “Ransomware” hybrid. These are caused by self-propagating code that does not require human intervention to spread once it has entered a system. The cause of this autonomy is often found in the way modern networks are interconnected, allowing a single point of failure to cascade into a total system blackout.
The Role of Social Engineering and Human Vulnerability
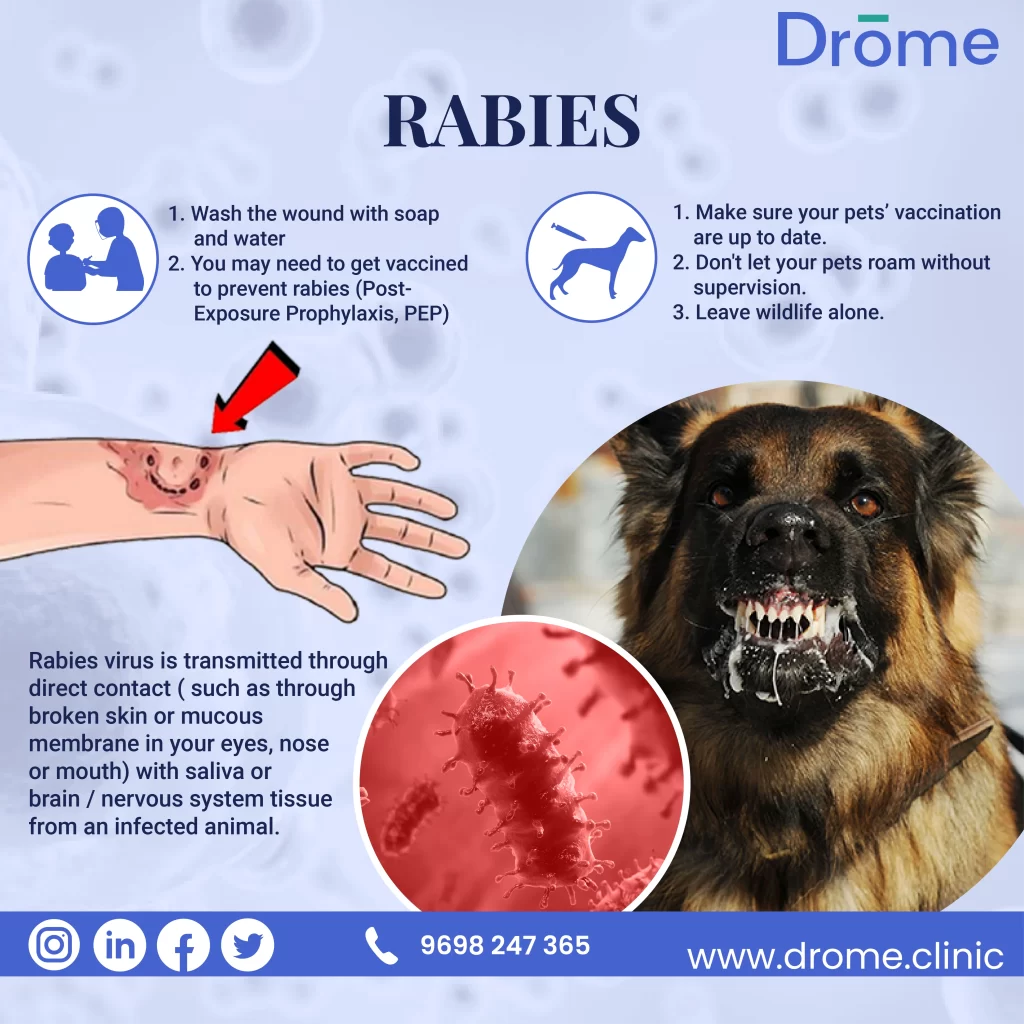
If we ask what causes the initial “bite” of a digital infection, the answer is frequently human psychology. Social engineering remains the primary vector for high-intensity malware. Phishing, spear-phishing, and “vishing” (voice phishing) exploit trust, urgency, or fear. By mimicking legitimate corporate communication, attackers induce employees to click a link or download an attachment. This moment of human error is the catalyst, introducing the “pathogen” into an otherwise secured environment.
Systemic Vulnerabilities and Zero-Day Exploits
Beyond human error, the most sophisticated causes of digital rabies are Zero-Day exploits. These are vulnerabilities in software or hardware that are unknown to the vendor. When a “rabid” piece of code exploits a Zero-Day, there is no immediate “vaccine” (patch) available. These vulnerabilities are often caused by the increasing complexity of software development, where millions of lines of code inevitably contain overlooked flaws. In the tech industry, the pressure to ship products quickly often results in a “security-later” mindset, creating the perfect breeding ground for viral exploits.
The Evolution of “Rabid” Malware: From Simple Viruses to Aggressive Ransomware
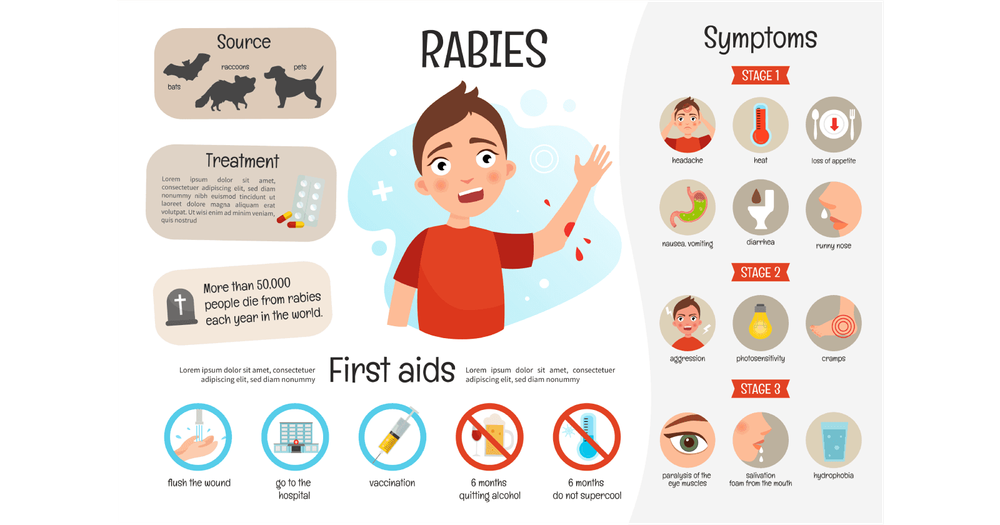
The nature of what causes these digital threats has shifted from prank-oriented scripts in the 1990s to profit-driven, state-sponsored cyber-warfare tools today. The modern “rabid” strain is characterized by its aggression and its ability to mutate.
Self-Replicating Code: The Digital Pathogen
The primary cause of a malware outbreak’s speed is its self-replicating nature. Using protocols like SMB (Server Message Block), malware can move laterally across a network in milliseconds. This lateral movement is what makes a threat “rabid.” For instance, the infamous WannaCry outbreak was caused by an exploit known as EternalBlue, which allowed the malware to jump from one computer to another without any user action. This mimicry of a biological contagion allows the infection to outpace the human ability to respond.
Targeted Attacks vs. Indiscriminate Infection
While some digital rabies is spread indiscriminately to catch as many victims as possible, we are seeing a rise in “Targeted Rabies” (Advanced Persistent Threats). These are caused by threat actors who spend months researching a specific target’s infrastructure. They identify the “nervous system” of the company—its servers, backups, and administrative accounts—and strike with surgical precision. The cause here is not just a virus, but a coordinated campaign by professional hacking collectives or nation-states.
The Rise of Botnets and Distributed Denial of Service (DDoS)
Another manifestation of digital virality is the Botnet. This is caused by the infection of thousands of Internet of Things (IoT) devices—cameras, smart fridges, and routers. Once infected, these devices become “zombies” under the control of a master server. The cause of this susceptibility is the lack of standardized security protocols in the IoT industry. When these “rabid” devices are commanded to attack a single target simultaneously, they create a DDoS attack that can cripple the internet infrastructure of entire regions.
Prevention and Mitigation: Vaccinating Your Infrastructure
If we identify the causes of digital rabies as vulnerability and connectivity, the solution must involve a “vaccination” strategy that focuses on resilience and proactive defense.
Proactive Defense: The Role of AI and Machine Learning
Modern cybersecurity tools are now using Artificial Intelligence (AI) to act as a digital immune system. These tools look for “behavioral anomalies” rather than known signatures. Just as an immune system recognizes a foreign pathogen by its behavior, AI-driven security can identify a “rabid” process by its attempt to encrypt files at high speeds or its unusual requests for administrative access. This shift from reactive to proactive defense is essential in a world where new “strains” of malware are created every second.
Implementing Zero-Trust Architecture
One of the most effective ways to prevent the spread of a digital infection is the implementation of Zero-Trust Architecture. The philosophy is simple: “Never trust, always verify.” In a traditional network, once a virus gets past the perimeter, it has free rein. In a Zero-Trust environment, every single movement within the network requires authentication. This creates “internal quarantines” or micro-segmentation, ensuring that even if one segment of the tech stack is “bitten,” the infection cannot spread to the rest of the enterprise.
Patch Management as a Digital Quarantine
The most common cause of preventable infections is the failure to update software. “Patching” is the tech equivalent of a booster shot. Most major malware outbreaks of the last decade exploited vulnerabilities for which a patch already existed. Organizations that fail to maintain a rigorous patch management schedule are essentially leaving their digital doors unlocked. Effective IT management requires a culture where security updates are prioritized over uptime and convenience.
The Future of Cyber-Pathology: Predictive Analytics and Beyond
As we look toward the future, the “causes” of digital rabies will likely become even more sophisticated, involving automated exploits and quantum-resistant encryption-breaking.
Behavioral Analysis: Identifying the “Symptom” Before the “Bite”
The next frontier in tech security is predictive analytics. By analyzing vast amounts of metadata, security firms can identify the preparations for a cyber-attack before it is even launched. This involves monitoring the “Dark Web” for the sale of specific exploits or observing unusual patterns in global internet traffic. The goal is to move from treating the “disease” to preventing the “exposure” entirely.
Quantum Computing: A New Frontier for Digital Immunity
While quantum computing poses a threat to current encryption methods, it also offers a new level of digital immunity. Quantum Key Distribution (QKD) could create unhackable communication channels, effectively eliminating the possibility of “interception-based” infections. However, the transition to quantum-resistant algorithms is a massive undertaking for the tech industry, and the delay in this transition could be the cause of the next great digital pandemic.
The Human-Centric Security Model
Finally, we must recognize that the ultimate cause of digital rabies is often the gap between technological capability and human understanding. The future of tech security lies in “Human-Centric Design”—creating systems that are inherently difficult to misuse. If a system is designed so that a single wrong click cannot trigger a global shutdown, we have successfully neutralized the primary cause of digital contagion.
In conclusion, “What are rabies caused by” in a technological context is a multi-faceted question. It is caused by the inherent vulnerabilities in complex code, the aggressive evolution of self-replicating malware, the psychological manipulation of social engineering, and the systemic failure to prioritize security hygiene. By understanding these digital pathogens through the lens of virality, the tech industry can develop the sophisticated “vaccines” and “immune responses” necessary to protect our increasingly connected world. The goal is not just to survive the “bite,” but to build a digital ecosystem where such infections have no room to spread.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.