In the modern digital landscape, the gateway to our most sensitive information—ranging from private communications and health records to financial accounts—is often a simple string of characters. While we use them daily, the technical nuances of what constitutes “characters” for a password and how they function within the architecture of cybersecurity are often misunderstood.
At its core, a password is a shared secret between a user and a system. The “characters” we choose are the individual units of data that form the basis of this authentication method. However, as computational power increases and cyber-attacks become more sophisticated, the definition of an effective character set has evolved. This article explores the technical foundations of password characters, the mathematics of entropy, and the best practices for securing digital identities in an era of persistent threats.
1. The Anatomy of Password Character Sets
When a system asks you to create a password, it typically defines a set of allowed characters. This is not an arbitrary request; it is a way to define the “keyspace”—the total number of possible combinations a hacker would have to guess to break into your account. In technical terms, password characters are generally categorized into four primary groups based on the standard ASCII (American Standard Code for Information Interchange) character set.
Uppercase and Lowercase Letters
The most basic building blocks of any password are alphabetic characters. In the English language, there are 26 lowercase and 26 uppercase letters. Most security protocols insist on a mix of both to increase complexity. From a technical standpoint, distinguishing between ‘a’ and ‘A’ doubles the potential options for each slot in the password string, making it significantly harder for automated scripts to guess through simple permutations.
Numerical Digits
The inclusion of numbers (0–9) adds another ten possibilities to each character position. While numbers are essential, their placement often falls into predictable patterns (such as adding “1” or a birth year at the end), which sophisticated “dictionary attack” algorithms are designed to exploit. True security relies on integrating numbers randomly throughout the string rather than as predictable suffixes.
Special Characters and Symbols
Special characters—such as symbols (!, @, #, $, %, ^, &, *), punctuation, and brackets—are the most potent tools for increasing a password’s resistance to brute-force attacks. There are approximately 33 printable special characters in the standard ASCII set. By requiring at least one symbol, a system forces the “character pool” to expand from 52 (letters only) or 62 (letters and numbers) to 95. This expansion drastically increases the mathematical difficulty of cracking the password.
2. Entropy and the Mathematics of Character Selection
In the world of digital security, the strength of a password is measured by “entropy.” Entropy is a measure of how unpredictable a password is. Understanding how characters contribute to entropy is vital for anyone looking to protect their technical infrastructure.
The Formula for Password Strength
The strength of a password is not just about the types of characters used, but how those characters are combined. The formula for entropy is $E = log_2(R^L)$, where $R$ is the size of the character pool (the range of characters available) and $L$ is the length of the password.
While adding a special character increases $R$, increasing the length ($L$) has an exponential impact on security. For example, a 10-character password using only lowercase letters is mathematically weaker than a 15-character password using the same letters. This realization has led many tech experts to shift their focus from “complexity” (using many types of characters) to “length” (using more characters overall).
The Myth of Complexity vs. The Power of Length
For years, the standard advice was to create short, complex passwords like “P@ssw0rd!”. However, modern cybersecurity research, including updated guidelines from NIST (the National Institute of Standards and Technology), suggests that humans are poor at remembering complex strings and often choose predictable substitutions (like ‘@’ for ‘a’).
Technically, a longer “passphrase” consisting of several random words (e.g., “blue-mountain-keyboard-coffee”) provides much higher entropy and is significantly harder for a computer to guess than a short, complex string. This is because the sheer number of character positions creates a combinatorial explosion that outpaces current brute-force computing capabilities.
3. Vulnerabilities: How Characters are Exploited
Even the most carefully chosen characters can be vulnerable if the underlying technical threats are not understood. Hackers use several methods to bypass character-based security, ranging from automated guessing to social engineering.

Brute-Force and Dictionary Attacks
A brute-force attack is a trial-and-error method where a program attempts every possible combination of characters until it finds the right one. The more characters and the larger the variety of character types, the longer this process takes.
A dictionary attack is a more refined version of this. Instead of trying every combination, the software tries common words, phrases, and “leetspeak” substitutions (e.g., “53cur1ty” for “security”). If your password characters follow a linguistic pattern or a common cultural reference, the characters themselves—no matter how many symbols you include—become a liability.
Credential Stuffing and Hashing
When a website is breached, hackers don’t usually get your password characters in plain text. Instead, they get a “hash”—a cryptographic representation of those characters. If a site uses weak hashing algorithms, hackers can use “rainbow tables” (pre-calculated hashes of common character combinations) to reverse-engineer your password. This is why using unique characters for every different service is a technical necessity; if one set of characters is compromised, your entire digital identity is at risk.
4. Best Practices for Implementing Password Characters
As we navigate the complexities of digital security, certain technical standards have emerged as the “gold standard” for managing password characters.
The Shift Toward Passphrases
As previously mentioned, the industry is moving away from the “8-character complex password” toward the “16+ character passphrase.” By using a long string of characters that form random words, users can achieve high entropy without sacrificing memorability. Technical implementations of login screens are increasingly allowing for spaces and longer character counts to accommodate this shift.
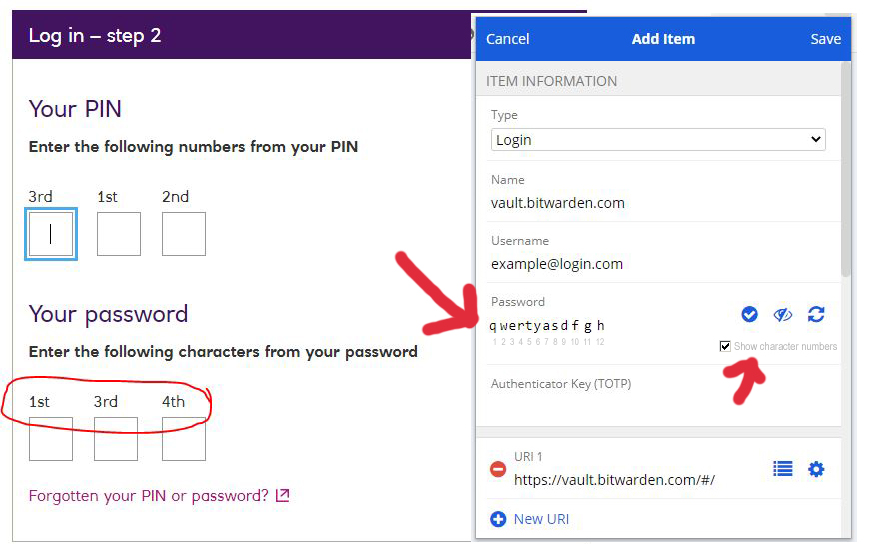
Utilizing Password Managers
Human memory is the weakest link in the character-selection process. To truly secure a digital ecosystem, tech professionals recommend the use of password managers. These tools generate truly random strings of characters—for example, k7!vP$9zQ*m2N#L1—which provide the highest possible entropy. Because the user doesn’t need to remember the characters, the password can be maximized for length and complexity, effectively neutralizing dictionary attacks.
Character Encoding and Unicode
In a globalized tech environment, we are seeing a move beyond the basic 95 ASCII characters. Modern systems often support Unicode, which includes characters from different languages, emojis, and specialized symbols. While this creates a massive potential keyspace, it can also lead to technical issues with character encoding (how the computer reads the data) across different platforms. Sticking to the standard extended ASCII set is generally recommended for maximum compatibility across various apps and devices.
5. Beyond Characters: The Future of Authentication
While understanding password characters is essential, the tech industry is gradually moving toward “passwordless” environments. The limitations of character-based security have spurred innovation in alternative authentication methods.
Biometrics and Hardware Tokens
Characters are “something you know,” but they can be stolen or guessed. Modern security is shifting toward “something you are” (biometrics like fingerprints or facial recognition) and “something you have” (hardware security keys like YubiKeys). These methods eliminate the need for the user to manage a string of characters, instead using high-level encryption and cryptographic handshakes to verify identity.
Multi-Factor Authentication (MFA)
Even the strongest combination of characters should not stand alone. Multi-factor authentication adds a layer of security that exists outside the password string. Whether it is a time-based one-time password (TOTP) generated by an app or a push notification to a trusted device, MFA ensures that even if a hacker successfully cracks your password characters, they still lack the secondary “key” required to gain access.
The Role of AI in Password Security
Artificial Intelligence is a double-edged sword in the realm of password characters. On one hand, AI-driven tools like PassGAN can analyze millions of leaked passwords to predict the character patterns users are likely to choose. On the other hand, AI is being used by security teams to detect “impossible travel” or unusual login behaviors, providing a safety net that protects accounts even when the password characters themselves have been compromised.

Conclusion
Characters are the fundamental units of digital access, but their effectiveness depends entirely on how they are utilized. A secure password is more than just a random collection of letters and symbols; it is a mathematically robust defense mechanism designed to withstand the immense processing power of modern cyber-threats.
By prioritizing length, embracing the randomness provided by password managers, and supplementing character-based security with multi-factor authentication, users and organizations can build a formidable defense. As we look toward a future of biometric and cryptographic authentication, the humble password character remains our first line of defense in an increasingly complex digital world. Understanding the technical principles behind these characters is not just a matter of convenience—it is a critical requirement for digital survival.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.