In the competitive landscape of modern gaming, the integrity of a software environment is as critical as the gameplay itself. For a global phenomenon like Fortnite, maintaining a level playing field is not merely a design preference—it is a technical necessity. To protect its ecosystem from malicious actors, Epic Games employs a sophisticated, multi-layered digital security architecture. Specifically, Fortnite utilizes a dual-system approach involving two of the industry’s most prominent anti-cheat solutions: Easy Anti-Cheat (EAC) and BattlEye.
This technical deep dive explores the mechanics of these systems, the shift toward kernel-level security, and how machine learning is being integrated to stay ahead of increasingly sophisticated cheating software.
The Dual-Layer Defense: Understanding Easy Anti-Cheat and BattlEye
Fortnite is unique in its deployment of two distinct anti-cheat providers simultaneously. While most titles rely on a single vendor, Epic Games leverages a “hybrid” approach to ensure that if a vulnerability is discovered in one system, the other acts as a redundant fail-safe.
Easy Anti-Cheat (EAC): The Epic-Owned Standard
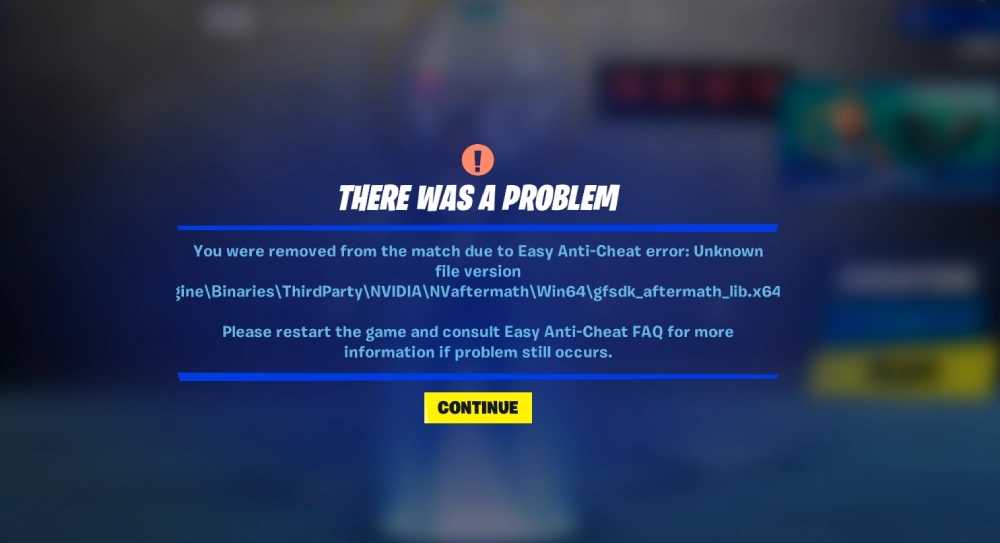
Easy Anti-Cheat, originally developed by Kamu and acquired by Epic Games in 2018, serves as the primary pillar of Fortnite’s security. EAC is a proactive anti-cheat service that focuses on preventing the “root causes” of cheating rather than just punishing the symptoms. From a software perspective, EAC operates by monitoring the integrity of game files and scanning for unauthorized third-party software attempting to hook into the game process. Because Epic Games owns EAC, the integration is exceptionally tight, allowing for rapid updates and deep optimization within the Unreal Engine environment.
BattlEye: The Proactive Shield
BattlEye is the second component of the dual-defense strategy. Known for its aggressive scanning and “proactive” protection, BattlEye has been a staple in the PC gaming industry for over a decade. It operates on a global scale, cross-referencing a massive database of known cheat signatures. By running alongside EAC, BattlEye provides an additional layer of behavioral analysis. It is particularly effective at identifying “zero-day” exploits—newly developed cheats that have not yet been logged in standard signature databases.
Why Fortnite Uses Two Systems Simultaneously
The decision to run two anti-cheat systems is a strategic technological maneuver designed to eliminate a single point of failure. Cheat developers often spend months attempting to reverse-engineer a specific anti-cheat driver. By alternating between EAC and BattlEye (or using them in tandem depending on the platform and region), Epic Games forces cheat developers to bypass two completely different sets of encryption and detection logic. This significantly raises the “cost of entry” for creating functional cheats, effectively pricing many script-kiddies and amateur developers out of the market.
The Architecture of Kernel-Level Security
To understand how Fortnite remains secure, one must understand the hierarchy of the Windows operating system. Most standard applications run in “User Mode” (Ring 3), where they have limited access to the system’s core resources. However, modern cheats often operate at the “Kernel Mode” (Ring 0), where the operating system’s core resides. To counter this, Fortnite’s anti-cheat systems must also operate at the kernel level.
Ring 0 Access: How Drivers Work at the Core of the OS
When you launch Fortnite, the anti-cheat system loads a kernel-mode driver. This driver sits between the hardware and the software, giving it the highest possible privilege level. From this vantage point, the anti-cheat can see every process running on the computer. If a cheat attempts to hide its presence by masquerading as a system driver or by manipulating the Windows kernel to hide a process from the Task Manager, the kernel-level anti-cheat can detect the anomaly because it is operating on the same plane of existence as the threat.
Detecting Memory Manipulation and Code Injection
Most cheats work through “code injection” or “memory manipulation.” For example, an aimbot might read the memory addresses where player coordinates are stored and then force the mouse input to lock onto those coordinates. Because EAC and BattlEye have kernel access, they can implement “Read/Write” protections on the game’s memory space. If an external process attempts to access the memory allocated to Fortnite, the anti-cheat immediately flags the action as a security breach.
The Privacy Debate Surrounding Kernel-Level Protection
The transition to kernel-level drivers has sparked a significant debate within the digital security community. Critics argue that giving a video game “Ring 0” access is a potential security risk; if the anti-cheat driver itself has a vulnerability, a hacker could theoretically use it to take over a user’s entire system. However, from a technical standpoint, this is currently the only effective way to combat modern “internal” cheats. Epic Games mitigates these risks by ensuring their drivers are digitally signed and undergo rigorous third-party security audits to prevent them from being exploited as backdoors.

Beyond Client-Side Protection: Server-Side Logic and AI
While the software on the user’s computer (the client) does a heavy amount of the lifting, the battle against cheating is increasingly moving to the server. Epic Games utilizes advanced server-side validation to ensure that what happens in the game world is physically and logically possible.
Behavioral Analysis and Heuristic Detection
Heuristic detection involves looking for patterns rather than specific files. Instead of searching for a program named “Aimbot.exe,” the system looks for “inhuman” behavior. For instance, if a player’s reticle moves between two targets in a single frame with 100% mathematical precision every time, the server-side logic flags this as anomalous. This behavioral data is processed in real-time, allowing the system to kick players who are clearly bypassing the client-side protections.
Machine Learning in Fair Play Enforcement
Epic Games has invested heavily in machine learning (ML) to improve detection accuracy. By feeding millions of hours of gameplay data into an ML model, the system learns to differentiate between a highly skilled professional player and a player using a “silent aim” cheat. These AI models can detect subtle “micro-adjustments” in aim that are characteristic of software assistance but invisible to the human eye. This technical layer is constantly evolving, training on new data to recognize the next generation of “closet cheats”—users who try to hide their cheating by acting like normal players.
The Role of Server-Side Validation
A fundamental rule in secure software development is “never trust the client.” Fortnite’s server-side architecture validates every action. If a client sends a packet saying, “I am now at these coordinates,” the server checks the player’s previous position and velocity. If the move is impossible (e.g., teleporting across the map), the server rejects the movement. This “authoritative server” model prevents many legacy cheats, such as speed hacks or infinite health, from functioning regardless of the client-side anti-cheat status.
Enforcement Mechanisms: Hardware Bans and Account Security
Detection is only half the battle; enforcement is the other. When a user is caught cheating in Fortnite, Epic Games doesn’t just ban the account—they leverage hardware-level identification to prevent the user from simply creating a new one.
Hardware ID (HWID) Tracking
When the EAC or BattlEye drivers are active, they generate a unique “fingerprint” of the user’s computer based on components like the motherboard serial number, MAC address, and disk drive IDs. This is known as a Hardware ID (HWID). If a player is banned, their HWID is blacklisted. Even if they reinstall Windows or use a VPN, the anti-cheat will recognize the hardware components and immediately terminate any new accounts associated with that machine.
Protecting the Ecosystem from Recurring Offenders
This technical deterrent is vital for a free-to-play game. Since there is no financial barrier to creating a new account, the “technical barrier” of an HWID ban is the primary tool for maintaining long-term integrity. While “HWID spoofers” exist, they are often unstable and easily detected by the kernel-level drivers, creating a constant “cat-and-mouse” game between cheat developers and Epic’s security team.
The Future of Anti-Cheat Technology in Competitive Gaming
As we look toward the future of digital security in gaming, the methods used by Fortnite will likely become more integrated with the hardware itself. We are already seeing a shift toward utilizing Windows security features like TPM 2.0 (Trusted Platform Module) and Secure Boot.
Cloud-Based Processing and Reduced Latency
One of the biggest challenges with anti-cheat software is the performance “overhead.” Running deep scans can occasionally cause “stuttering” or reduced frame rates. The next evolution in this tech involves offloading much of the heavy analysis to the cloud. By streaming telemetry data to high-performance servers, the local client can remain “light” while the cloud-based AI performs the complex calculations required to identify sophisticated cheats.

The Constant Arms Race Against Cheat Developers
The technology Fortnite uses—Easy Anti-Cheat, BattlEye, kernel-level monitoring, and AI-driven behavioral analysis—represents the current pinnacle of digital security in the gaming industry. However, the “arms race” never truly ends. As cheat developers experiment with external hardware “DMA” (Direct Memory Access) cards to bypass the CPU entirely, Epic Games and its partners will continue to innovate, potentially integrating anti-cheat logic directly into the GPU or utilizing specialized security chips within modern processors.
In conclusion, Fortnite’s security is not a single program, but a massive, multi-tiered infrastructure. By combining the strengths of EAC and BattlEye with the deep privileges of kernel-mode drivers and the intelligence of machine learning, Epic Games has created one of the most robust anti-cheat environments in software history. For the end-user, this complex web of technology remains invisible, serving its ultimate purpose: ensuring that every “Victory Royale” is earned through skill, not software.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.