Since the publication of the whitepaper “Bitcoin: A Peer-to-Peer Electronic Cash System” by the pseudonymous Satoshi Nakamoto in 2008, the world has grappled with a fundamental shift in how we perceive digital data and value. While many discuss Bitcoin in the context of market volatility or investment potential, its true brilliance lies in its technical architecture. At its core, Bitcoin is not just a currency; it is a breakthrough in computer science, cryptography, and distributed systems. It solved the “Double Spending Problem”—the ability to duplicate digital information—without the need for a central authority. To understand how Bitcoin works, one must look under the hood at the sophisticated interplay of peer-to-peer networking, cryptographic hashing, and consensus algorithms.

The Foundation of Decentralization: Peer-to-Peer Architecture
The primary technical innovation of Bitcoin is its decentralized nature. Unlike traditional digital systems where a central server (like a bank or a social media platform) validates and stores data, Bitcoin operates on a Peer-to-Peer (P2P) network. This architecture ensures that no single entity has control over the system, making it resilient to censorship and single points of failure.
Removing the Intermediary
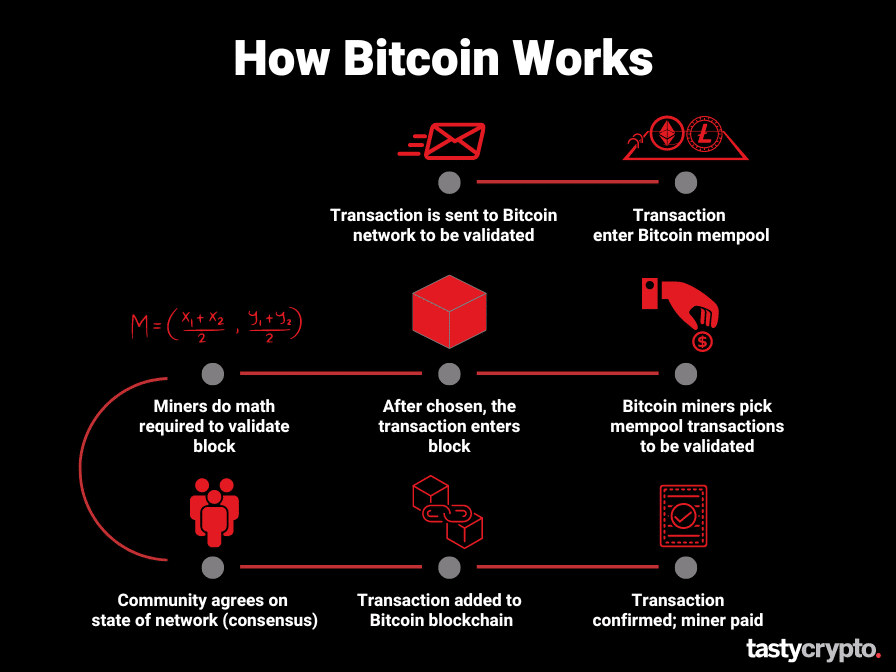
In a standard centralized tech stack, a database is managed by an administrator who has the power to add, move, or delete entries. In the Bitcoin protocol, the “database” is shared among thousands of participants. When a transaction occurs, it is not sent to a central hub; instead, it is broadcast to the entire network. This peer-to-peer distribution ensures that every participant has an identical copy of the transaction history, effectively removing the need for a trusted third party to verify the validity of the data.
The Role of Nodes and Network Consensus
The Bitcoin network is composed of “nodes”—computers running the Bitcoin software. These nodes serve as the guardians of the protocol. There are different types of nodes, but “Full Nodes” are the most critical. They download every block and transaction and check them against Bitcoin’s core consensus rules. These rules include ensuring that the sender has sufficient balance and that the digital signature is valid. If a transaction violates these rules, the node simply rejects it. This democratic verification process ensures that the software, rather than a human or a corporation, enforces the integrity of the system.
Cryptography and the Security Infrastructure
The “crypto” in cryptocurrency refers to the advanced mathematical techniques used to secure the network. Bitcoin utilizes two primary cryptographic concepts: Asymmetric Cryptography (Public-Key Cryptography) and Cryptographic Hashing. These tools ensure that only the rightful owner of a digital asset can spend it and that the history of the network cannot be tampered with.
Public and Private Key Infrastructure
Every Bitcoin “wallet” is essentially a pair of cryptographic keys. The Public Key is comparable to an email address or a bank account number; it can be shared openly, allowing others to send data (Bitcoin) to it. The Private Key, however, is a secret mathematical string that acts as a digital signature.
When a user initiates a transaction, the software uses the private key to sign a digital message. This signature proves that the user has the authority to move the funds associated with a specific public address without ever revealing the private key itself. The network nodes use the corresponding public key to verify that the signature is authentic. This ensures that even if a hacker intercepts a transaction message, they cannot alter its contents or forge a new signature.
Hashing: The Digital Fingerprint of Data
Bitcoin relies heavily on the SHA-256 (Secure Hash Algorithm 256-bit) hashing function. A hash function takes an input of any size and produces a fixed-size string of characters, which looks like a random sequence of numbers and letters. This “digital fingerprint” is deterministic (the same input always produces the same output) but one-way (you cannot reverse-engineer the input from the hash).
Hashing is used in every aspect of Bitcoin’s security. It secures the data within a block, links blocks together, and is the fundamental component of the mining process. If a single character in a transaction is changed, the resulting hash would be completely different, immediately alerting the network to the attempted fraud.
The Blockchain Ledger and Transaction Lifecycle
The term “Blockchain” refers to the specific way Bitcoin organizes data. Rather than a continuous stream of information, transactions are bundled into “blocks,” which are then cryptographically linked in a chronological chain.
How Blocks are Formed
When a user sends Bitcoin, the transaction enters a “Mempool” (memory pool), which is a waiting room for unconfirmed transactions. Miners—specialized nodes in the network—select transactions from the Mempool to package into a new block. A typical block contains approximately 2,000 to 3,000 transactions, along with metadata such as a timestamp and a reference to the previous block.
The Verification Process and Immutability
What makes the blockchain “immutable” is the way these blocks are linked. Each block contains the hash of the block that came before it. This creates a chain of dependency. If an attacker wanted to change a transaction in an old block, the hash of that block would change. Consequently, the “previous block hash” stored in the next block would no longer match, breaking the chain. To successfully alter the ledger, an attacker would have to re-calculate every subsequent block in the chain, a task that is computationally impossible given the current scale of the network.
Proof of Work: The Mechanics of Mining
The mechanism that keeps the Bitcoin network synchronized and secure without a central leader is called “Proof of Work” (PoW). This is often the most misunderstood part of the technology, frequently dismissed as “wasted energy,” but in reality, it is the digital “anchor” that ties the virtual world to physical reality through thermodynamics.
Solving the Cryptographic Puzzle
Mining is the process of finding a specific hash for a block that meets a certain criteria. Specifically, the hash must start with a certain number of leading zeros. Because hash outputs are unpredictable, the only way to find a valid hash is through “brute force”—guessing billions of times per second.
Miners use specialized hardware (ASICs) to iterate through different “nonces” (random numbers) until they hit a hash that satisfies the network’s difficulty requirement. The first miner to find the valid hash broadcasts it to the network. Because the hash is easy to verify but hard to find, other nodes can instantly confirm the work was done and add the block to the chain.
Difficulty Adjustments and Network Stability
One of Bitcoin’s most elegant technical features is the Difficulty Adjustment. To ensure that blocks are found roughly every 10 minutes regardless of how many miners are active, the software automatically adjusts the complexity of the cryptographic puzzle every 2,016 blocks (approximately every two weeks). If more computing power joins the network, the puzzle gets harder; if miners leave, it gets easier. This self-regulating feedback loop ensures the stability and predictability of the system.
Scarcity, Code, and the Future of Digital Security
Bitcoin’s technical design also dictates its monetary policy, which is hard-coded into the software and enforced by the nodes. This blends software engineering with economic theory, creating a system of “digital scarcity.”
The Halving Protocol
To control the supply of Bitcoin, the “Block Subsidy”—the amount of new Bitcoin rewarded to miners for finding a block—is programmed to decrease over time. Approximately every four years (or every 210,000 blocks), the reward is cut in half. This “Halving” event continues until the total supply of Bitcoin reaches 21 million, estimated to occur around the year 2140. This code-based scarcity is a stark departure from traditional software systems where data can be duplicated infinitely.

Smart Contracts and Layer 2 Innovations
As the base layer of Bitcoin (Layer 1) is optimized for security and decentralization, it is intentionally limited in speed. To scale the technology, developers have built “Layer 2” solutions like the Lightning Network. The Lightning Network uses smart contracts—self-executing code—to create “payment channels” off the main blockchain. This allows for nearly instantaneous, high-volume transactions while still relying on the security of the main Bitcoin ledger for final settlement.
Furthermore, recent updates like “Taproot” have enhanced Bitcoin’s scriptability, allowing for more complex cryptographic conditions and improved privacy. These technical evolutions ensure that Bitcoin remains not just a static ledger, but a dynamic platform for decentralized digital infrastructure.
In conclusion, Bitcoin works through a harmonious blend of P2P networking, SHA-256 hashing, and a Proof-of-Work consensus mechanism. It is a self-sustaining technical ecosystem that uses math and physics to replace the need for human trust. By understanding these technical pillars, one can see that Bitcoin is far more than a financial asset—it is the internet’s native layer for secure, verifiable, and decentralized information.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.