The creation of a cryptocurrency is a complex undertaking, fundamentally rooted in advanced computer science, cryptography, and distributed systems architecture. It’s a journey from conceptualizing a digital asset to engineering its underlying blockchain network, securing its operations, and ensuring its functionality within a decentralized ecosystem. This guide delves into the technical intricacies involved, outlining the essential steps, technologies, and considerations for anyone looking to embark on this cutting-edge development project. We will strictly adhere to the technological aspects, focusing on software, security, infrastructure, and development processes.
The Foundational Pillars: Understanding Blockchain Technology
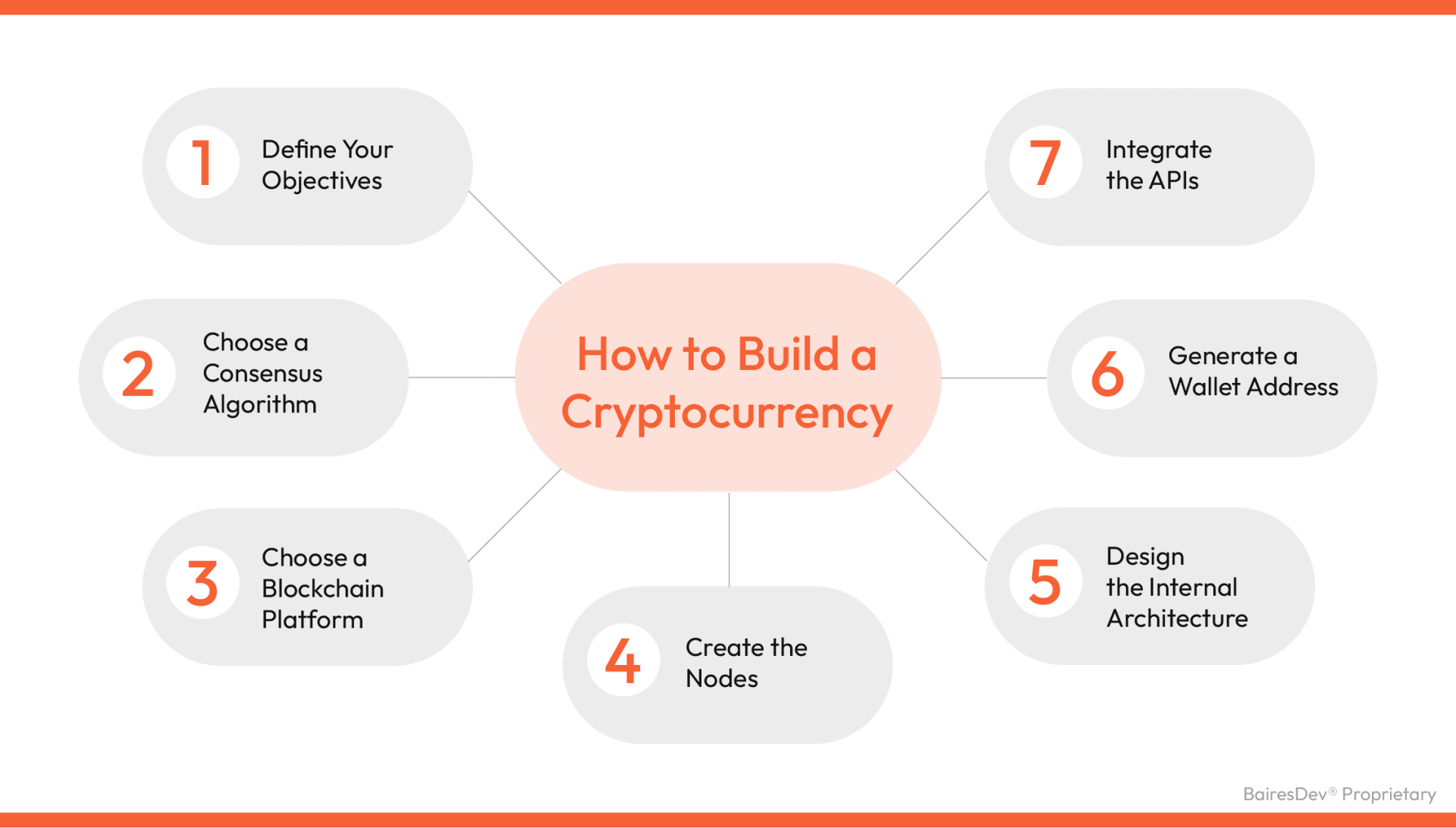
Before diving into the practicalities of building a cryptocurrency, a deep understanding of its core technological backbone – blockchain – is indispensable. A cryptocurrency is, at its heart, a digital representation of value or utility secured and managed by a blockchain.
Distributed Ledger Technology (DLT)
At the core of any blockchain is the concept of a Distributed Ledger Technology (DLT). Unlike traditional centralized databases, DLTs maintain a shared, immutable, and synchronized database across a network of participants, known as nodes. Each transaction, once validated, is added as a new “block” to a chain of existing blocks, creating a chronological and tamper-proof record. This distributed nature eliminates single points of failure and enhances resilience against attacks. For developing a cryptocurrency, designing your DLT involves defining how data is structured within blocks, how blocks are linked, and how new transactions are broadcast and recorded across the network. This includes choices regarding block size, transaction capacity, and the overall data model.
Cryptographic Principles
Cryptography is the lynchpin of blockchain security and integrity. Public-key cryptography ensures that only the rightful owner can access and spend their cryptocurrency. Each user has a public key (their wallet address) and a private key (a secret string of characters). Transactions are digitally signed with the private key, which can then be verified by anyone using the corresponding public key, confirming the sender’s authenticity and preventing repudiation. Hash functions are another critical cryptographic tool, used to uniquely identify blocks and transactions, creating a fingerprint that is nearly impossible to reverse-engineer or tamper with. The integrity of the entire chain relies on these cryptographic hashes, as any alteration to a single block would change its hash, invalidating all subsequent blocks. Designing your cryptocurrency requires careful selection and implementation of robust cryptographic algorithms to safeguard assets and data.
Consensus Mechanisms Explained
A consensus mechanism is the algorithm that determines how the distributed network reaches agreement on the current state of the ledger. It is crucial for preventing fraudulent transactions and maintaining the integrity of the blockchain without a central authority. Various mechanisms exist, each with its own trade-offs concerning security, scalability, and decentralization:
- Proof of Work (PoW): Pioneered by Bitcoin, PoW requires “miners” to solve complex cryptographic puzzles to validate transactions and create new blocks. This process consumes significant computational resources, making it costly to attack the network but also energy-intensive.
- Proof of Stake (PoS): In PoS, validators are chosen to create new blocks based on the amount of cryptocurrency they “stake” as collateral. This mechanism is generally more energy-efficient and scalable than PoW, as it doesn’t rely on competitive computation.
- Delegated Proof of Stake (DPoS): A variation of PoS where token holders vote for a limited number of delegates to validate transactions and maintain the network. DPoS offers higher transaction throughput but can lead to greater centralization among the chosen delegates.
- Other Mechanisms: There are numerous other consensus mechanisms like Proof of Authority (PoA), Proof of History (PoH), and various Byzantine Fault Tolerance (BFT) derivatives, each tailored for specific network requirements.
Choosing the right consensus mechanism is one of the most critical design decisions, directly impacting your cryptocurrency’s performance, security, and decentralization profile.
Choosing Your Technological Path: Building or Leveraging Existing Infrastructure
Once the foundational concepts are clear, the next decision involves the actual implementation strategy: building a blockchain from the ground up or utilizing an existing platform.
Developing a Blockchain from Scratch
Creating an entirely new blockchain from scratch provides maximum customization and control over every aspect of the network. This approach involves developing your own distributed ledger software, implementing unique consensus algorithms, designing novel cryptographic schemes, and defining custom network protocols. It requires a highly skilled team proficient in low-level programming (e.g., C++, Rust, Go), network engineering, and advanced cryptography. While offering unparalleled flexibility, it is an immensely resource-intensive and technically challenging endeavor, demanding significant time, expertise, and capital. This path is typically pursued by projects aiming to innovate fundamentally on blockchain technology or those with highly specialized requirements that existing platforms cannot meet.
Utilizing Established Blockchain Platforms (e.g., Ethereum, Solana, Polkadot)
For most projects, leveraging an existing, robust blockchain platform is a more practical and efficient approach. These platforms provide a battle-tested infrastructure, including established networks of nodes, security features, and development tools.
- Ethereum: The most popular platform for decentralized applications (dApps) and custom cryptocurrencies (tokens). Its Turing-complete virtual machine (EVM) allows for the creation of complex smart contracts, primarily written in Solidity.
- Solana: Known for its high throughput and low transaction costs, Solana utilizes a unique Proof of History (PoH) consensus mechanism in conjunction with PoS. It’s an excellent choice for applications requiring rapid transaction finality.
- Polkadot: A multi-chain framework designed to enable interoperability between different blockchains. It allows for the creation of “parachains,” independent blockchains that can connect to Polkadot’s relay chain for shared security and communication.
Choosing an existing platform significantly reduces development time and overhead, as much of the underlying infrastructure is already in place. Developers can focus on building the application layer and smart contract logic specific to their cryptocurrency.
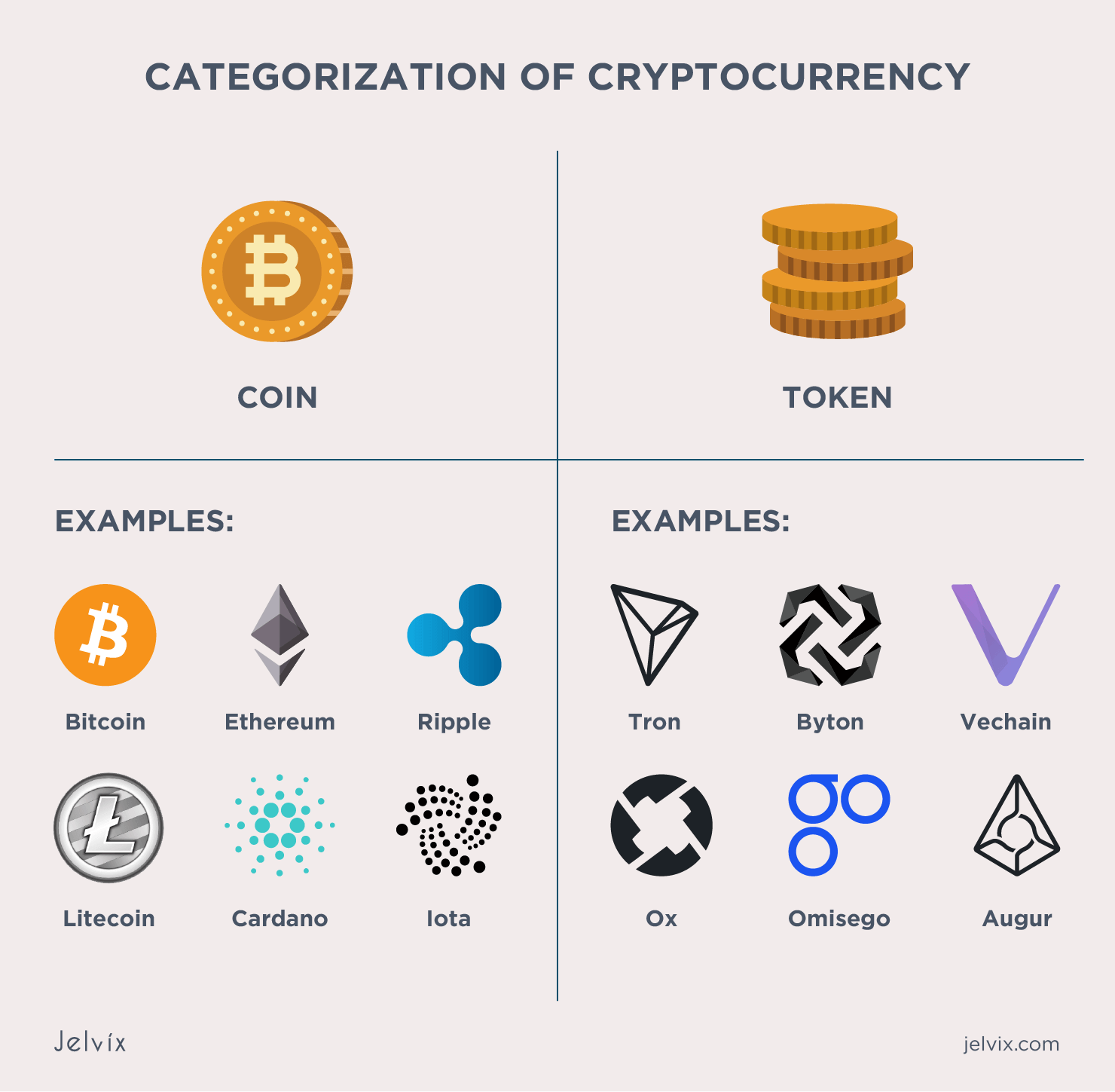
The Role of Token Standards (ERC-20, BEP-20, SPL)
When building on an existing platform, you’ll typically create a “token” rather than an entirely new coin. Tokens are cryptocurrencies that operate on another blockchain’s infrastructure. To ensure interoperability and compatibility with wallets, exchanges, and other decentralized applications, these tokens often adhere to specific technical standards.
- ERC-20 (Ethereum Request for Comment 20): The most widely adopted standard for fungible tokens on the Ethereum blockchain. It defines a set of functions and events that a smart contract must implement, such as
totalSupply,balanceOf,transfer, andapprove. Adhering to ERC-20 makes a token compatible with the vast Ethereum ecosystem. - BEP-20 (Binance Smart Chain Evolution Proposal 20): A standard similar to ERC-20 but for the Binance Smart Chain (now BNB Chain). It adds some BSC-specific functionalities and is designed for compatibility within the BNB ecosystem.
- SPL (Solana Program Library): Solana’s equivalent of token standards. The SPL Token program provides a flexible framework for creating and managing fungible and non-fungible tokens on the Solana blockchain.
These standards provide a blueprint for token behavior, simplifying integration and ensuring that your cryptocurrency can be seamlessly managed and traded across various platforms.
Smart Contract Development and Execution
Smart contracts are the backbone of most modern cryptocurrencies, especially those built on platforms like Ethereum. They are self-executing agreements with the terms directly written into lines of code.
Programming Languages for Smart Contracts (Solidity, Rust)
The choice of programming language is critical for smart contract development:
- Solidity: The most popular language for writing smart contracts on Ethereum and other EVM-compatible blockchains. It’s a high-level, contract-oriented language designed to implement business logic for decentralized applications. Its syntax is similar to JavaScript, making it accessible to many developers.
- Rust: Gaining traction for smart contract development, particularly on platforms like Solana and Polkadot. Rust is a system-level programming language known for its performance, memory safety, and concurrency. It offers powerful capabilities for high-performance and secure decentralized applications, though it has a steeper learning curve than Solidity.
Other languages like Vyper (a Python-like language for EVM) also exist, each offering different trade-offs in terms of security features, readability, and performance.
Designing and Implementing Smart Contract Logic
The smart contract code defines the fundamental rules and functionalities of your cryptocurrency. This includes:
- Token Creation: Defining the total supply, token name, symbol, and decimal places.
- Transfer Functions: Logic for transferring tokens between addresses.
- Access Control: Implementing roles and permissions for specific actions (e.g., who can mint new tokens, who can pause transfers).
- Burning Mechanisms: Optional functions to destroy tokens, reducing the total supply.
- Additional Features: Depending on the cryptocurrency’s utility, smart contracts can include complex logic for staking, yield farming, governance mechanisms (e.g., voting on protocol changes), or integration with other dApps.

Careful architectural design and meticulous coding are paramount to prevent vulnerabilities that could lead to financial losses or network instability.
Rigorous Smart Contract Auditing and Security
Given the immutable nature of blockchain and the financial implications, security auditing of smart contracts is non-negotiable. Before deployment, smart contracts must undergo thorough review by independent third-party security auditors. This process involves:
- Vulnerability Assessment: Identifying common vulnerabilities such as reentrancy attacks, integer overflows, unchecked external calls, and access control issues.
- Code Review: Examining the code for best practices, efficiency, and adherence to security standards.
- Penetration Testing: Simulating attacks to discover weaknesses.
- Formal Verification: Using mathematical methods to prove the correctness of the contract’s logic under all possible conditions.
Skipping or inadequately performing security audits can expose the cryptocurrency to severe risks, leading to potential exploits and loss of user funds. It is a critical step in ensuring the integrity and trustworthiness of your digital asset.
Architecting the Ecosystem: Wallets, Nodes, and Network Security
A cryptocurrency isn’t just code; it’s an entire ecosystem of interacting components that enable its functionality and security.
Designing Secure Digital Wallets
Wallets are essential software tools that allow users to store, manage, and transact with their cryptocurrency. Technically, a wallet doesn’t hold the tokens themselves but rather the cryptographic keys (public and private) that control access to them on the blockchain.
- Key Management: The primary function of a wallet is secure private key generation and storage. This involves using strong cryptographic random number generators.
- Transaction Signing: Wallets facilitate the signing of transactions with a user’s private key before broadcasting them to the network.
- User Interface: A well-designed user interface is crucial for usability, allowing users to view their balance, transaction history, and easily send/receive tokens.
- Types of Wallets: This can range from hardware wallets (physical devices for maximum security), software wallets (desktop or mobile apps), to web-based wallets.
- Integration: For a new cryptocurrency, ensuring compatibility with existing wallet software (e.g., MetaMask for ERC-20 tokens) or developing a proprietary wallet is a key technical consideration.
Security features like multi-factor authentication, seed phrase generation, and hierarchical deterministic (HD) wallet structures are paramount in wallet design.
Network Infrastructure: Nodes and Decentralization
The decentralization and resilience of a cryptocurrency hinge on its network of nodes. Nodes are computers that run the blockchain software, validate transactions, and maintain a copy of the ledger.
- Full Nodes: Store a complete copy of the blockchain and independently verify all transactions and blocks. They contribute significantly to the network’s security and decentralization.
- Light Nodes: Download only block headers and request additional data as needed, relying on full nodes for verification. They are less resource-intensive but offer less security.
- Mining/Staking Nodes: Nodes specifically configured to participate in the consensus mechanism (e.g., mining in PoW, staking in PoS).
Developing a robust cryptocurrency involves providing clear documentation and software for users to easily set up and run nodes, thereby increasing the network’s decentralization and fault tolerance. Incentivizing node operators (e.g., through block rewards) is often part of the protocol design.
Implementing Robust Security Protocols
Beyond smart contract audits and wallet security, overall network security is paramount. This encompasses protection against various forms of attacks:
- 51% Attacks: Where a single entity gains control of more than 50% of the network’s hashing power (PoW) or staked tokens (PoS), allowing them to manipulate transactions. Robust consensus mechanisms and a distributed node network mitigate this.
- Sybil Attacks: An attacker creates multiple fake identities to gain disproportionate influence.
- DDoS Attacks: Malicious attempts to disrupt the network by overwhelming it with traffic.
- Code Vulnerabilities: Exploits in the underlying blockchain software or protocol.
Implementing best practices such as continuous security monitoring, bug bounty programs, regular software updates, and cryptographic best practices for all components (hashing, signatures, encryption) are vital for maintaining a secure and reliable cryptocurrency network.
Deployment, Maintenance, and Future Iteration
The journey of creating a cryptocurrency doesn’t end with coding; deployment, ongoing maintenance, and future development are continuous processes.
Launching on Testnets and Mainnets
Before a full public release, a cryptocurrency must undergo rigorous testing:
- Testnets: A separate blockchain network, identical to the main network in terms of protocol and software, but using worthless test tokens. Developers deploy their smart contracts and applications here to identify and fix bugs without real financial risk. This phase is crucial for testing transaction flow, smart contract interactions, and network stability under various loads.
- Mainnet Deployment: Once thoroughly tested on the testnet and audited, the cryptocurrency is deployed to the mainnet. This is the live, public blockchain where real transactions occur using valuable tokens. The deployment process involves broadcasting the smart contract code or the new blockchain client software to the network, making it available for public interaction.
Careful planning for mainnet deployment, including infrastructure setup and monitoring, is essential for a smooth launch.
Ongoing Development, Updates, and Governance
A cryptocurrency’s underlying technology is not static. Continuous development is necessary to:
- Address Bugs and Vulnerabilities: Even after extensive testing, new issues may arise, requiring patches and updates.
- Implement New Features: Evolving technological landscape and user needs necessitate new functionalities, improved scalability, or enhanced privacy features.
- Optimize Performance: Refining the code and protocol for better transaction speed, lower fees, or reduced energy consumption.
Many decentralized projects employ a governance model where token holders can vote on proposed changes (on-chain or off-chain) to the protocol, ensuring community-driven evolution. Technical teams must be prepared to manage these updates, often involving complex upgrade mechanisms for smart contracts or hard/soft forks for the underlying blockchain.
Building a Competent Technical Team
The creation and ongoing maintenance of a cryptocurrency require a diverse and highly skilled technical team. Key roles include:
- Blockchain Developers: Proficient in specific blockchain frameworks (e.g., Ethereum, Solana) and smart contract languages (Solidity, Rust).
- Cryptographers: Experts in cryptographic algorithms and security protocols.
- Backend Developers: For off-chain components, APIs, and database interactions.
- Frontend Developers: To build user interfaces for wallets, explorers, and dApps.
- DevOps Engineers: For managing infrastructure, deployments, and continuous integration/delivery pipelines.
- Security Auditors: Specialists in identifying and mitigating vulnerabilities.
Assembling a cohesive and experienced team is as critical as the technology itself, ensuring the project’s long-term viability, security, and innovative capacity. The journey of making a cryptocurrency is a marathon of technical challenges, demanding continuous learning, robust engineering, and an unwavering commitment to security and decentralization.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.