In the rapidly evolving landscape of information technology, terminology often borrows from the biological world to describe phenomena that are pervasive, invasive, and difficult to eradicate. While the general public associates the term “Flu B” with a seasonal respiratory infection, within specific circles of cybersecurity and system architecture, “Flu B” has emerged as a metaphorical descriptor for a specific class of systemic digital vulnerabilities. This “Digital Flu B” refers to a secondary variant of software instability—specifically, those recursive bugs and latent vulnerabilities that remain dormant in legacy codebases until triggered by modern integration attempts.
Understanding what the “Flu B” of technology represents is crucial for developers, security analysts, and IT stakeholders. It is not merely a single glitch but a category of technical debt that spreads through interconnected APIs and shared libraries, threatening the health of enterprise-level digital ecosystems.
The Anatomy of Flu B: Defining the Modern Software Vulnerability
In the tech sector, “Flu B” is often used to categorize vulnerabilities that are not as immediately destructive as a “Type A” total system failure or a catastrophic ransomware attack, but are more insidious due to their ability to linger and mutate. These are the secondary strains of bugs that arise after an initial system patch or a major architectural shift.
From Biological to Binary: Why the Nickname?
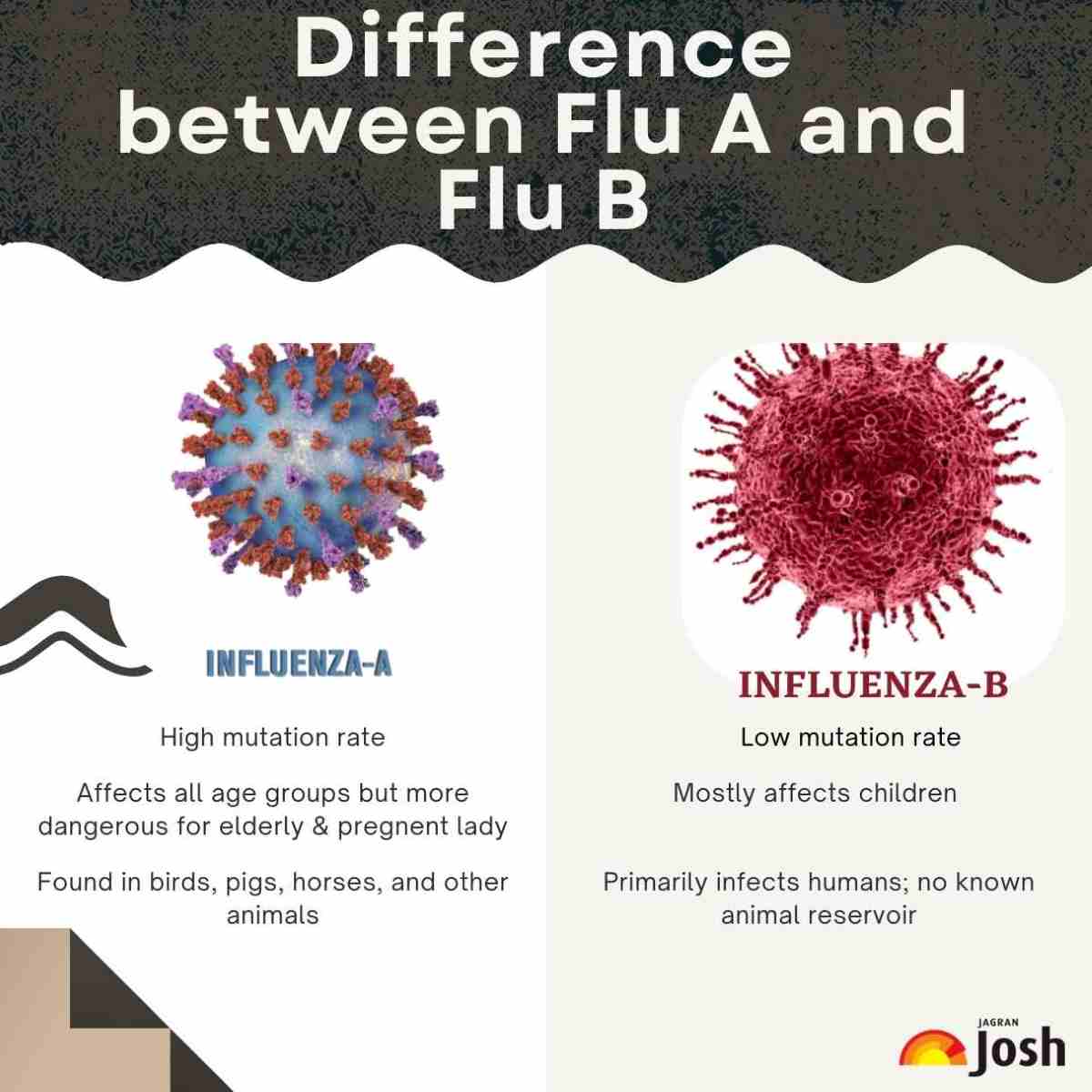
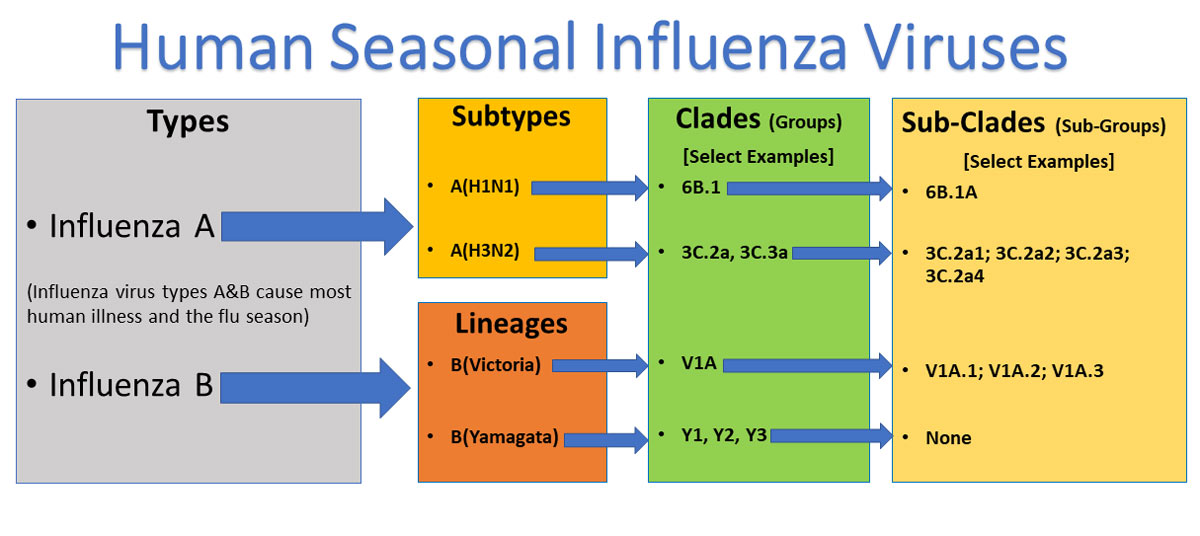
The nickname “Flu B” is derived from the way these technical issues behave similarly to their biological namesake. Much like the biological influenza B virus, which is known for slower mutation rates than Type A but maintains a persistent presence in the population, “Flu B” tech vulnerabilities are persistent. They often exist in the “B-side” or the secondary layers of software—such as the middleware, the background processes, or the older, less-frequented segments of an application’s source code.
These vulnerabilities often go unnoticed during standard QA testing because they do not cause immediate crashes. Instead, they lead to performance degradation, “memory leaks,” and minor data inconsistencies that, over time, compromise the entire system’s integrity.
How Flu B Compromises System Integrity
The primary danger of a “Flu B” tech variant lies in its subtlety. When a software environment is infected with this type of technical debt, it creates a “low-grade fever” in the system. Applications may run 10% slower, or API calls might fail once every thousand attempts. Because the symptoms are not catastrophic, they are often ignored in favor of more pressing features or “Type A” bugs.
However, as systems become more interconnected through the Internet of Things (IoT) and cloud-native microservices, these minor instabilities can synchronize. When multiple “Flu B” strains interact across different software modules, they can create a “cytokine storm” in the server environment, leading to unexpected outages that are notoriously difficult to diagnose because the root cause is distributed across multiple, seemingly minor points of failure.
The Architecture of Digital Infection: How Flu B Spreads
To defend against these digital contagions, one must understand their vector of transmission. In the modern tech stack, the “Flu B” does not move through the air; it moves through shared dependencies, open-source repositories, and poorly managed automated updates.
Legacy Systems and Open-Source Weaknesses
One of the most common breeding grounds for “Flu B” is the reliance on aging open-source libraries that are no longer actively maintained. When a modern framework is “bolted onto” a legacy foundation, the friction between the old and the new creates vulnerabilities.
Software developers often pull packages from repositories like NPM or PyPI without fully auditing the secondary and tertiary dependencies. If a “Flu B” bug exists in a library four levels deep in the dependency tree, it “infects” every application that utilizes that stack. This creates a systemic risk where a single minor flaw in a widely used utility library can compromise thousands of enterprise applications simultaneously.
The Role of Edge Computing in Viral Propagation
The rise of edge computing has expanded the “surface area” for digital infections. Devices at the edge—such as smart sensors, industrial controllers, and consumer gadgets—often have limited processing power for robust security protocols. When a “Flu B” variant enters an edge network, it can propagate rapidly between devices.
Because these devices are often set to “auto-update” or, conversely, are never updated at all, the “Flu B” can reside in the network indefinitely. This creates a persistent threat where the infected edge devices act as “asymptomatic carriers,” feeding corrupted data or unauthorized requests back into the central cloud infrastructure.
Mitigation Strategies: Immunizing Your Tech Stack
Addressing the “Flu B” of technology requires a shift from reactive patching to proactive “digital hygiene” and systemic immunization. It is no longer enough to wait for a system to break; organizations must build resilience into the very fabric of their software architecture.
Zero-Trust Architecture as a Digital Vaccine
The most effective “vaccine” against the spread of digital contagions is the implementation of a Zero-Trust Architecture (ZTA). In a ZTA environment, no part of the system is automatically trusted, regardless of whether it is inside or outside the network perimeter.
By requiring constant verification of every user, device, and API call, ZTA prevents a “Flu B” vulnerability in one module from “leaking” into others. If a microservice becomes infected with a recursive bug or a minor exploit, the Zero-Trust protocols contain the “infection,” ensuring that the rest of the ecosystem remains functional while the specific module is quarantined and repaired.
Real-Time Monitoring and AI-Driven Patching
To catch a “Flu B” variant early, organizations are increasingly turning to Artificial Intelligence (AI) and Machine Learning (ML) tools. These tools are designed to monitor system telemetry in real-time, looking for the “early symptoms” of digital illness—such as slight deviations in processor usage, unusual packet sizes, or unauthorized lateral movement within a network.
AI-driven observability platforms can identify the signature of a “Flu B” bug long before a human analyst would notice the performance dip. Furthermore, “Self-Healing” systems are being developed that can automatically roll back updates or apply temporary “virtual patches” when they detect the onset of a known vulnerability pattern, effectively providing the system with an automated immune response.
The Future of Tech Resilience in a Post-Flu B World
As we move further into the decade, the complexity of our digital world will only increase. The “Flu B” phenomenon serves as a reminder that as software becomes more sophisticated, so too do the ways in which it can fail. The future of technology is not just about faster processors or larger data sets; it is about the “biological” resilience of our digital infrastructure.
Predictive Analysis and Threat Intelligence
The next frontier in digital security is predictive analysis. Rather than reacting to “Flu B” after it has spread, tech leaders are using global threat intelligence feeds to anticipate where the next “strain” of vulnerability might emerge. By analyzing global coding trends and monitoring the “dark web” for new exploit methodologies, companies can pre-emptively harden their systems against specific types of binary instability.
This proactive stance turns the traditional security model on its head. Instead of a “castle and moat” approach, it creates a dynamic, evolving defense system that learns from every “infection” encountered across the global tech landscape.

Building “Self-Healing” Software Infrastructures
Ultimately, the goal is to create a “Self-Healing” infrastructure. This is a system where the “Flu B” is not an existential threat but a routine maintenance event. In a self-healing environment, if a piece of code begins to exhibit “sick” behavior, the system automatically spins up a healthy containerized version of that code, isolates the malfunctioning unit, and runs a diagnostic to determine if a patch is required.
This level of automation represents the ultimate evolution of the tech industry’s response to systemic vulnerabilities. By treating software more like an organism and less like a static machine, we can create a digital world that is not only more powerful but significantly more robust against the inevitable “flus” of the future.
In conclusion, “What’s the Flu B” in the context of technology is a call to action. It represents the persistent, mutating challenges inherent in complex software systems. By acknowledging these risks and employing modern strategies like Zero-Trust, AI-driven monitoring, and self-healing architectures, the tech industry can ensure that even when the “digital flu” strikes, the global network remains resilient, secure, and operational.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.