In the rapidly evolving world of information technology, the term “locking in”—more formally known as vendor lock-in—refers to a situation where a customer becomes dependent on a particular vendor for products and services, unable to use another vendor without substantial switching costs. In the digital age, this is no longer just about buying a specific brand of hardware; it encompasses software ecosystems, cloud infrastructure, data formats, and even artificial intelligence models.
While “locking in” often provides seamless integration and optimized performance, it creates a strategic vulnerability for businesses and individual users alike. As we navigate a landscape dominated by tech giants and proprietary standards, understanding the mechanics, risks, and mitigation strategies of technological lock-in is essential for maintaining digital sovereignty and operational flexibility.
The Mechanics of Vendor Lock-In: Why Organizations Get Stuck
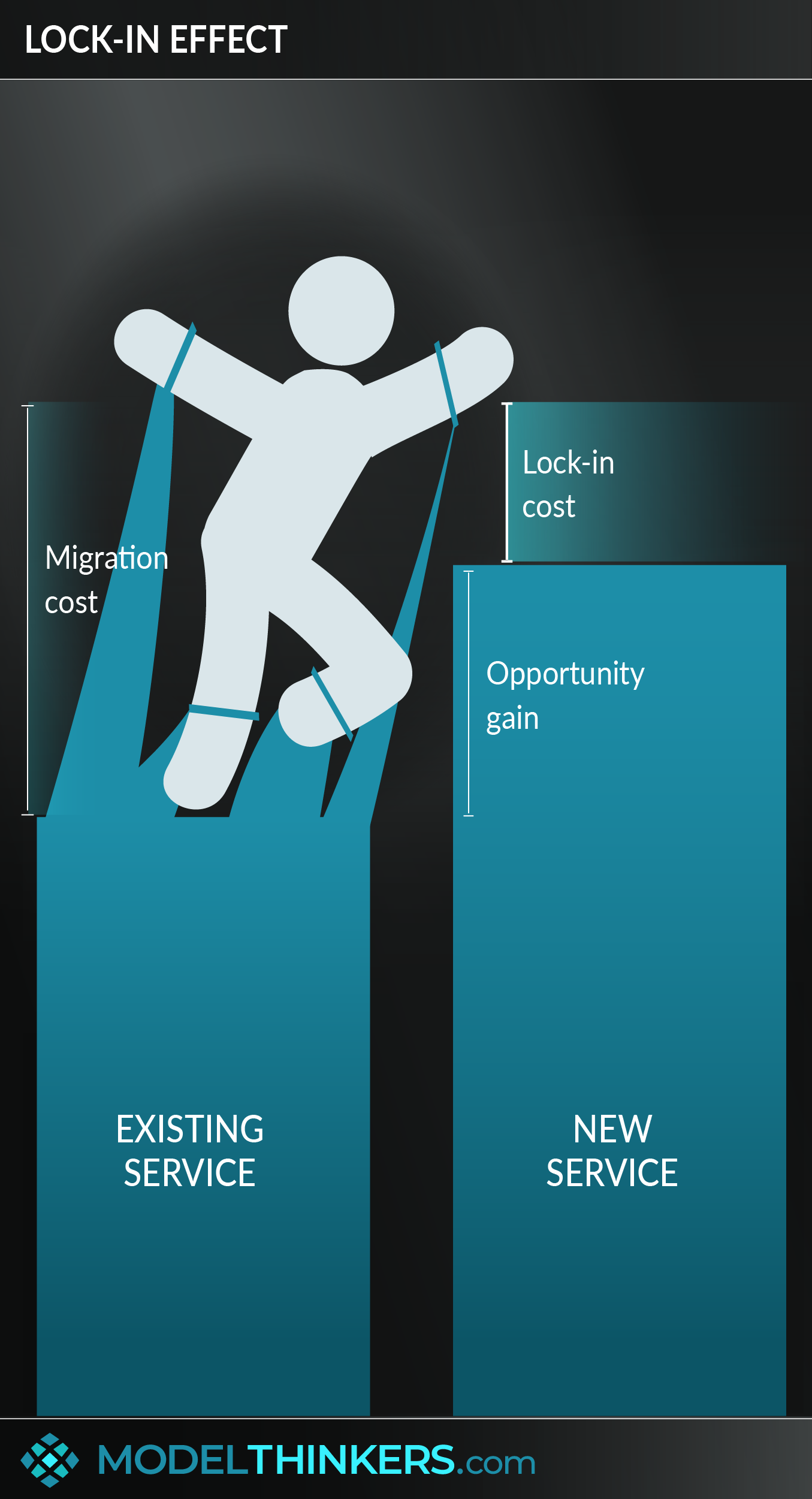
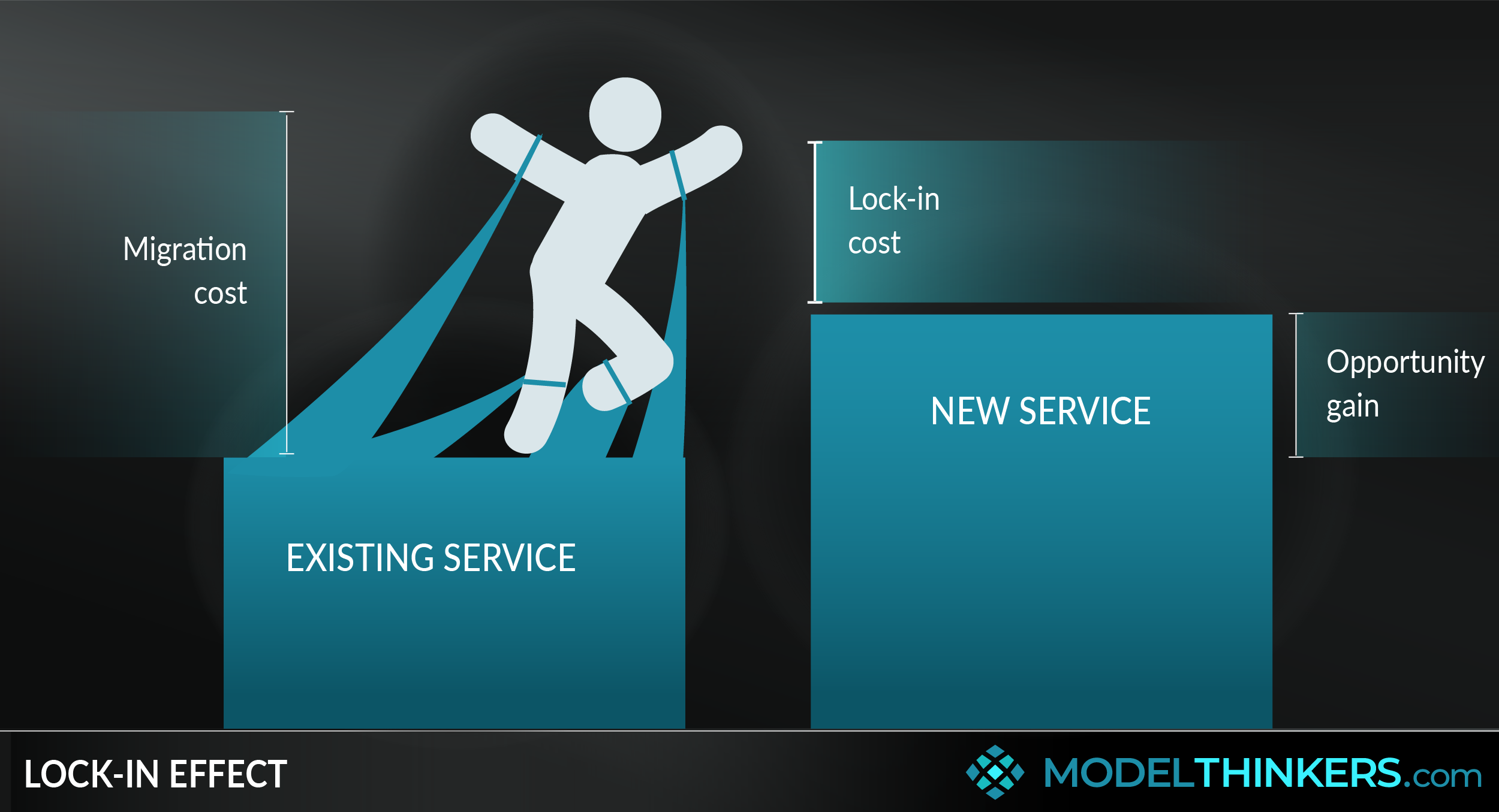
Vendor lock-in is rarely the result of a single decision; rather, it is the cumulative effect of technical and financial commitments that make migration prohibitively expensive or complex. To understand how “locking in” occurs, we must examine the specific levers that vendors use to ensure customer longevity.
High Switching Costs and Data Gravity
The most significant barrier to leaving a tech ecosystem is the cost of moving data. Known as “data gravity,” the idea is that as data sets grow larger, they become harder to move. In a cloud environment, for example, many providers offer free “ingress” (moving data into the cloud) but charge significant “egress” fees for moving data out. When a company has petabytes of data stored in a proprietary format or a specific cloud region, the sheer cost of bandwidth and the time required for migration can effectively lock them into that provider indefinitely.
Proprietary APIs and Custom Integrations
Software ecosystems often rely on proprietary Application Programming Interfaces (APIs). When developers build applications that are deeply integrated with a specific vendor’s unique APIs—such as AWS Lambda for serverless computing or Google’s Firebase for backend services—the code becomes “sticky.” To move to a competitor, the organization would need to rewrite significant portions of its codebase, leading to months of development work and potential downtime.
Contractual and Financial Incentives
Lock-in is often reinforced through multi-year enterprise agreements and volume discounts. Vendors may offer substantial price breaks if a customer commits to a three-year “lock-in” period. While this looks like a cost-saving measure on the balance sheet, it removes the organization’s ability to pivot to newer, more efficient technologies that may emerge during that timeframe.
The Cloud Conundrum: Infrastructure and Platform Services
As businesses move away from on-premise servers toward the cloud, the nature of “locking in” has shifted from hardware to managed services. The major cloud providers—Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP)—each offer a suite of services designed to keep users within their specific orbit.
Managed Services vs. Portability
There is a fundamental trade-off in the cloud: convenience versus portability. Using a managed database service like Amazon RDS or Azure SQL is significantly easier than managing your own database on a virtual machine. However, these managed services often include proprietary features that do not exist elsewhere. The more a company utilizes “higher-level” cloud services (like AI-as-a-service or specialized IoT frameworks), the deeper the lock-in becomes.
The Rise of Serverless Architecture
Serverless computing represents the pinnacle of cloud efficiency, but also the peak of vendor lock-in. In a serverless model, the cloud provider manages the server allocation entirely. Because the underlying execution environment is hidden and specialized, migrating a serverless application from one cloud to another often requires a total architectural overhaul. This “functional lock-in” is one of the most debated topics among modern systems architects.
Ecosystem Synergies
Cloud providers often lock users in through cross-product synergies. For a company already using Microsoft 365 for productivity and Windows for its OS, choosing Azure for its cloud infrastructure is a path of least resistance. These integrations—such as unified identity management through Azure Active Directory—create a cohesive experience that is difficult to replicate using a “best-of-breed” approach with multiple vendors.
The Consumer “Walled Garden”: Hardware and Software Interdependency

For individual users, “locking in” is experienced through the “walled garden” approach favored by consumer tech companies. This strategy aims to create an ecosystem where the value of each product increases when used in conjunction with others from the same brand, while simultaneously making it difficult to exit.
The Ecosystem Effect
The most prominent example of consumer lock-in is the integration between hardware, software, and services. When a user owns a smartphone, a smartwatch, and wireless earbuds from the same manufacturer, the “hand-off” features and seamless synchronization create a high level of user satisfaction. However, this convenience acts as a golden cage. Replacing just the smartphone with a different brand would break the functionality of the watch and the earbuds, effectively forcing the user to replace their entire tech stack.
Proprietary Standards and Social Locking
Lock-in is not always technical; it can be social. Messaging protocols are a primary example. When a platform uses a proprietary messaging standard that offers exclusive features (such as high-quality media sharing or specific “read” receipts), users feel a social pressure to remain within that ecosystem to maintain communication quality with their peers. This “network effect” ensures that even if a superior technology arrives, the cost of leaving the established user base is too high.
Digital Content and App Stores
Once a user has spent years purchasing apps, movies, and books within a specific digital storefront, they are locked into the platform that hosts those licenses. Most digital content is sold under a “right to use” license rather than true ownership, and these licenses are rarely transferable between platforms. This creates a psychological and financial barrier to switching, as the user would lose access to their entire digital library.
Strategies for Mitigation: Achieving Technological Fluidity
While complete independence from vendors is nearly impossible in the modern era, savvy organizations and users can take steps to minimize the risks of “locking in.” This involves a shift toward open standards and a “cloud-agnostic” mindset.
Embracing Open Source and Open Standards
The most effective way to prevent lock-in is to use technologies based on open-source standards. For example, instead of using a proprietary cloud database, an organization might use PostgreSQL or MySQL, which are supported by almost every provider. If a vendor raises prices or service quality drops, the data and the application logic can be migrated to a new host with minimal friction because the underlying technology is standardized.
Containerization and Kubernetes
In the world of DevOps, containerization has revolutionized the ability to move applications. Tools like Docker allow developers to package an application and all its dependencies into a “container” that runs the same way regardless of the environment. Kubernetes, an open-source system for automating deployment and scaling of containers, acts as an abstraction layer. By building on Kubernetes, companies can run their workloads on AWS, Azure, or on-premise servers interchangeably, significantly reducing infrastructure lock-in.
Multi-Cloud and Hybrid Strategies
Many large enterprises are adopting a multi-cloud strategy, intentionally splitting their workloads across two or more providers. While this increases management complexity, it provides a “fail-safe” and prevents a single vendor from having total leverage over the company’s digital operations. Similarly, a hybrid cloud approach—keeping sensitive data on-premise while using the public cloud for scalable processing—ensures that the “crown jewels” of the company’s data remain under its direct control.
The Future of Locking In: Artificial Intelligence and Data Sovereignty
As we enter the age of Artificial Intelligence (AI), the concept of “locking in” is entering a new and more complex phase. The race for AI dominance is creating new types of dependencies that could be even more difficult to break than cloud or hardware lock-in.
Model Lock-In and Weights
As businesses integrate Large Language Models (LLMs) into their operations, they face “model lock-in.” If a company fine-tunes a proprietary model with its own data to perform specific tasks, that expertise is often trapped within that specific vendor’s ecosystem. Because the “weights” and the specific architecture of the model are proprietary, moving that intelligence to a different AI provider is currently impossible.
The Battle for Data Sovereignty
In response to the risks of locking in, we are seeing a global movement toward data sovereignty. Governments and regulatory bodies are increasingly demanding that users have the right to data portability—the ability to download their data in a machine-readable format and move it to a competitor. As these regulations evolve, vendors will be forced to move away from “hostage-taking” tactics and instead compete on the actual value and innovation of their services.
Conclusion: Balancing Convenience and Autonomy
“Locking in” is a double-edged sword in the tech world. On one hand, it provides the tight integration and “it just works” experience that defines modern computing. On the other hand, it represents a loss of control and a potential financial liability. For the tech-forward business or individual, the goal is not necessarily to avoid all forms of lock-in—which is often impractical—but to be consciously aware of it. By choosing technologies that prioritize interoperability and open standards, we can enjoy the benefits of modern ecosystems without surrendering our long-term digital freedom.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.