In the rapidly evolving landscape of computer hardware and digital security, the term “DMA card” has transitioned from a niche hardware development tool to a subject of intense discussion among cybersecurity experts, software developers, and the competitive gaming community. Standing for Direct Memory Access, a DMA card is a sophisticated piece of hardware designed to interact with a system’s memory independently of the Central Processing Unit (CPU).
While the concept of Direct Memory Access has been a fundamental part of computing architecture for decades, the advent of specialized, consumer-accessible PCIe DMA cards has opened new frontiers—and controversies—regarding how we monitor, manipulate, and secure digital environments. To understand what a DMA card is, one must delve into the mechanics of data transfer, the architecture of the Peripheral Component Interconnect Express (PCIe) bus, and the unique capabilities of Field Programmable Gate Arrays (FPGAs).

The Fundamentals of Direct Memory Access (DMA) Technology
At its core, Direct Memory Access is a feature of computer systems that allows certain hardware subsystems to access main system memory (RAM) independently of the CPU. In a traditional computing operation, the CPU acts as a mediator for every data transfer. If a hard drive needs to move data to RAM, the CPU manages the request, moving the data bit by bit. This “Programmed I/O” (PIO) is inefficient for high-speed data transfer because it consumes valuable CPU cycles.
How DMA Differs from Traditional Processing
DMA technology was invented to alleviate this bottleneck. By using a DMA controller, the system can transfer data directly between peripherals and memory with minimal intervention from the CPU. The CPU simply initiates the transfer and is then free to perform other tasks, receiving an interrupt signal only when the operation is complete.
A DMA card takes this concept to its logical extreme. It is a physical expansion card—usually a PCIe device—that possesses its own processing logic. Because it sits directly on the PCIe bus, it has the “authority” to request access to any memory address within the system.
The Role of the PCIe Interface
The PCIe interface is the highway of the modern motherboard. It provides high-bandwidth, low-latency communication between the CPU and external components like GPUs, NVMe drives, and DMA cards. DMA cards utilize the “Bus Mastering” capability of the PCIe standard. When a DMA card is plugged into a PCIe slot, it acts as a master on the bus, allowing it to read and write to the system’s RAM at hardware speeds, often bypassing the operating system’s standard security checks.
Components and Mechanics of a DMA Card
A modern DMA card is not a simple data conduit; it is a complex piece of programmable hardware. Understanding its components is essential to understanding why it is so powerful and why it is increasingly difficult for traditional software to regulate.
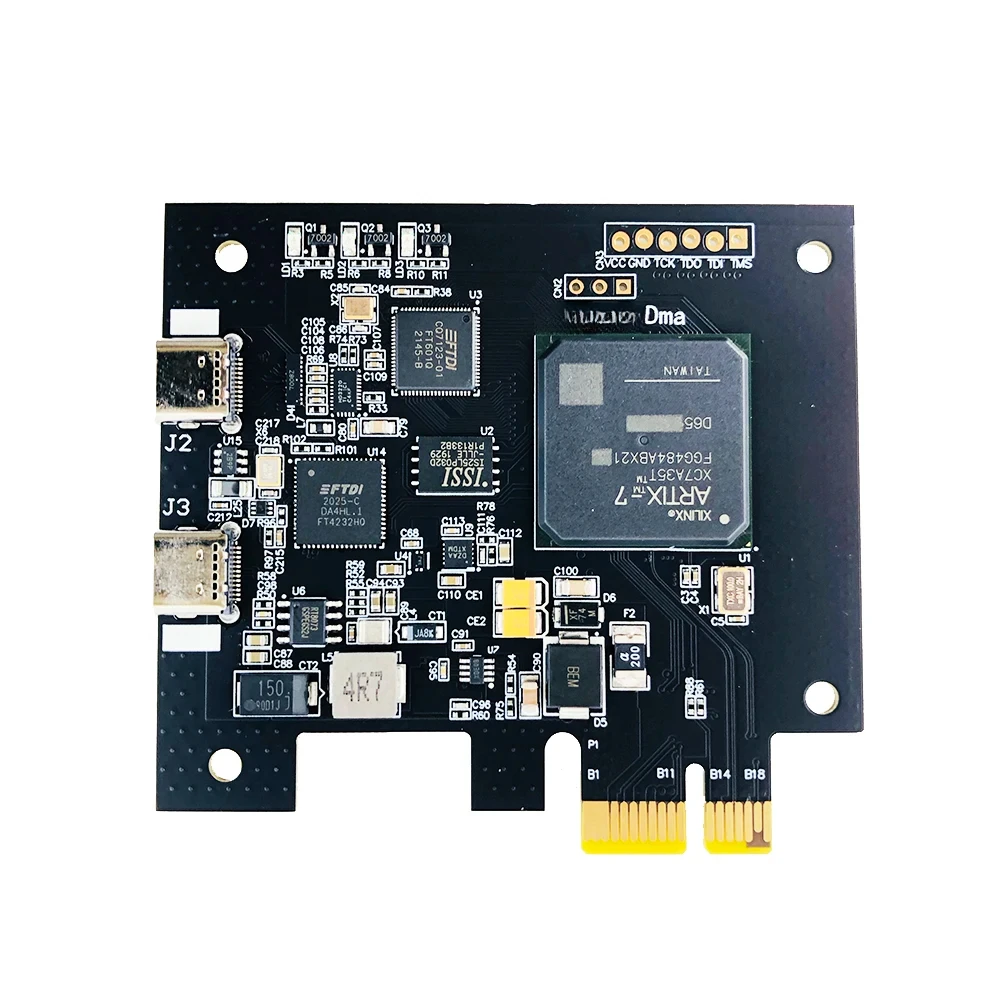
FPGA: The Heart of the Device
Most high-end DMA cards are built around a Field Programmable Gate Array (FPGA), such as the Xilinx Artix-7. Unlike a standard processor that has a fixed set of instructions, an FPGA is a blank slate of logic gates that can be “programmed” at the hardware level. This allows the card to emulate other devices. For example, a DMA card can be programmed to identify itself to the computer as a network adapter, a sound card, or a USB controller. This “spoofing” capability is central to the card’s ability to remain stealthy within a system.
Firmware and Customization
The intelligence of a DMA card resides in its firmware. The firmware tells the FPGA how to handle data requests and how to present itself to the BIOS and Operating System. In the tech community, “custom firmware” is highly sought after. Custom firmware allows the user to modify the device’s configuration space (its digital ID), making it virtually indistinguishable from legitimate hardware. This level of customization is what separates a standard development board from a specialized DMA card used for advanced memory manipulation.
The Dual-PC Setup
One of the most defining characteristics of DMA card usage is the dual-PC configuration. The DMA card is installed in the “Host” or “Target” PC (the machine whose memory is being accessed). A second “Analysis” or “Attack” PC is connected to the DMA card via a high-speed data cable (usually USB-C or Thunderbolt).
The software that reads or modifies the memory runs entirely on the second PC. Because the “Target” PC is only seeing a hardware device sitting on its PCIe bus and is not running any suspicious software processes, the activity is incredibly difficult to detect through standard software-based monitoring tools.

Practical Applications: From Development to Gaming
The utility of a DMA card spans a wide spectrum, from legitimate engineering and security research to more controversial applications in the world of online competition.
Memory Forensics and Security Research
In the realm of cybersecurity, DMA cards are invaluable tools for memory forensics. When a system is compromised by sophisticated malware or “rootkits,” the operating system itself can no longer be trusted. A DMA card allows a security researcher to “dump” the entire contents of the RAM to an external device for analysis without ever running code on the infected machine. This provides a “frozen” snapshot of the system state, allowing researchers to find hidden processes, encryption keys, or malicious code that would otherwise hide from the OS.
The Controversial Rise in Online Gaming
Perhaps the most discussed use of DMA cards today is in the creation of hardware-level cheats for competitive video games. Traditional cheats function by injecting code into a game’s process or modifying files on the disk—actions that are easily caught by Anti-Cheat (AC) software like Easy Anti-Cheat (EAC) or BattlEye.
A DMA card changes the game. By reading the game’s memory from an external PC, a user can display “ESP” (Extra Sensory Perception, like seeing through walls) on a separate monitor or a transparent overlay. Since the cheat software never runs on the gaming PC, the Anti-Cheat has no process to scan and no suspicious hooks to detect. This has led to a “hardware arms race” between cheat developers and game security companies.
High-Performance Data Transfer
Beyond security and gaming, DMA-like architectures are essential in high-performance computing (HPC) and big data. Devices that require massive throughput—such as 100Gbps network cards or high-end RAID controllers—rely on DMA to move data quickly enough to prevent system lag. While these are not “DMA cards” in the consumer sense, they utilize the same underlying technology to ensure the CPU is not overwhelmed by data movement.
Security Implications and Detection Challenges
The existence of consumer-grade DMA hardware poses a significant challenge to the fundamental “Trust Model” of modern computing. Most security systems assume that if the hardware is physically secure, the kernel and memory can be protected by software layers. DMA cards bypass this assumption.
Why DMA Cards are Hard to Detect
The primary difficulty in detecting a DMA card lies in its transparency. To the motherboard, the card is just another PCIe device. If the firmware is correctly written, the card responds to system queries exactly like a legitimate peripheral. Furthermore, because the card operates at the hardware layer (Layer 0), it can read memory before the operating system even finishes booting.
Standard antivirus and anti-cheat programs operate at the “User Mode” (Layer 3) or “Kernel Mode” (Layer 1). They are essentially “higher” up the chain than the DMA card, meaning the card can see them, but they struggle to see the card’s internal logic or its communication with the external PC.
The Battle Between Anti-Cheat Software and DMA
To combat DMA-based manipulation, software developers have had to get creative. Modern Anti-Cheats now look for “anomalies” rather than specific software signatures. They might check:
- PCIe Configuration Space: Looking for inconsistencies in how a device identifies itself.
- IOMMU (Input-Output Memory Management Unit): This is a hardware-level feature that acts as a “firewall” for RAM, restricting which PCIe devices can access specific memory regions. However, IOMMU can often decrease system performance, so it is frequently disabled by default on gaming rigs.
- Latency Checks: Measuring how long it takes for memory to respond. Sometimes, the presence of a DMA card introduces a tiny, measurable delay in memory access.
Future Trends in DMA Hardware and Digital Security
As we look toward the future, the role of DMA hardware will likely expand, moving from the fringes of the tech enthusiast world into the mainstream of hardware security discussions.
Evolving Encryption and Hardware Authentication
We are likely to see a shift toward “encrypted memory” architectures. Modern CPUs, like those from AMD and Intel, are beginning to implement Total Memory Encryption (TME). If the data in the RAM is encrypted and the key is held only within the CPU, a DMA card reading the memory would only see “garbage” data. This would effectively neutralize the effectiveness of DMA cards for unauthorized memory reading.
The Expansion of DMA in AI and Edge Computing
In the world of Artificial Intelligence, the need for rapid data movement between NPUs (Neural Processing Units) and system memory is paramount. We may see a new generation of “Smart DMA” cards designed to accelerate AI training by offloading data pre-processing directly onto the FPGA of the DMA card. This would allow for real-time data filtering before the information even reaches the main processor.
In conclusion, a DMA card is a double-edged sword of modern computing. It represents the pinnacle of hardware-level control, offering unparalleled speed and access to a system’s most vital resource: its memory. Whether used as a vital tool for digital forensics or a controversial bypass for software security, the DMA card highlights the ongoing tension between hardware capability and software control. As our systems become more complex, the mastery of Direct Memory Access will remain a critical frontier for anyone invested in the future of technology and security.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.