In an era where cybersecurity is the cornerstone of national defense and organizational integrity, the Common Access Card (CAC) stands as one of the most successful implementations of multi-factor authentication (MFA) and digital identity management in history. Issued by the United States Department of Defense (DoD), the CAC is much more than a simple identification badge. It is a sophisticated piece of technology—a “smart card” that integrates hardware, software, and cryptographic protocols to secure both physical and logical environments.
For tech professionals, security analysts, and digital identity enthusiasts, understanding the contents of a CAC provides a masterclass in how to secure a massive, decentralized workforce. This article explores the physical, digital, and cryptographic layers of the CAC, detailing exactly what this small piece of plastic contains and how it functions as a pillar of modern digital security.
The Anatomy of a CAC: Physical and Digital Components
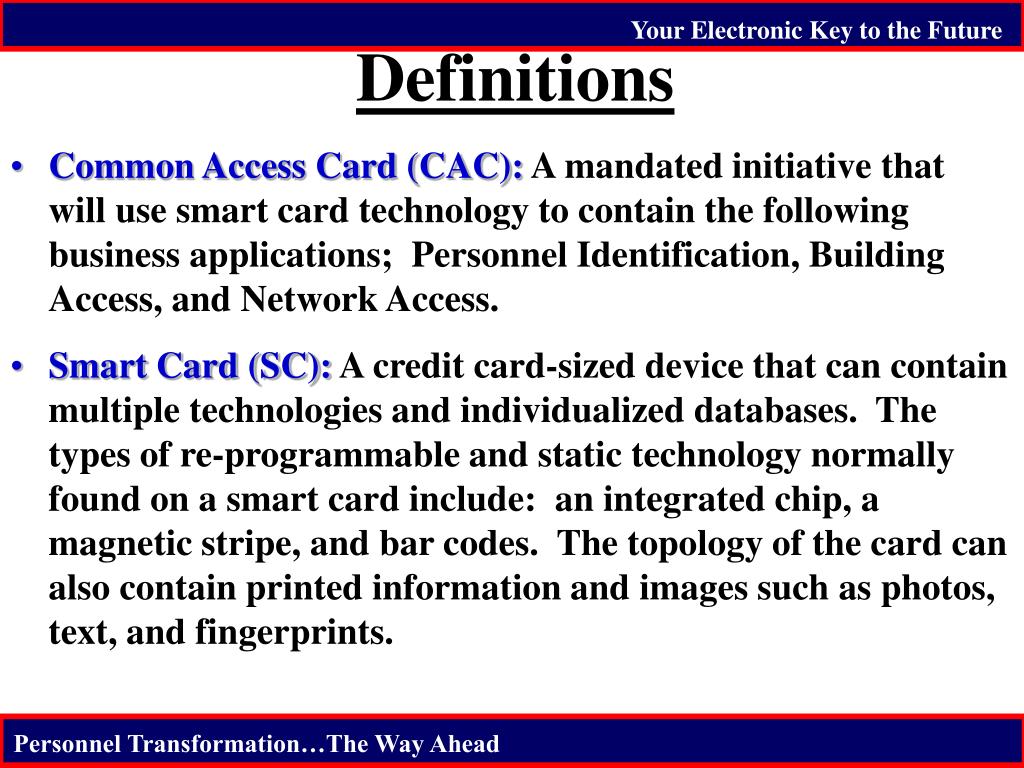
At first glance, the Common Access Card looks like a standard credit card, but its construction follows rigorous international standards (ISO/IEC 7816). It is designed to be tamper-resistant and contains several layers of data storage and transmission technology.
Visual Identification Features
The surface of the CAC contains high-resolution printed information that serves as the first line of identity verification. This includes the cardholder’s full-color photograph, name, rank/grade, and organizational affiliation (e.g., Army, Navy, Air Force, or Defense Contractor). It also features several security markings, such as microprinting and holographic overlays, which are designed to prevent physical counterfeiting.
The Integrated Circuit Chip (ICC)
The “brain” of the CAC is the gold-plated Integrated Circuit Chip (ICC) embedded on the front. This is a contact-based chip that requires a card reader to interface with computer systems. Unlike a simple magnetic stripe, which only stores static data, the ICC is a microprocessor capable of performing active cryptographic computations. It contains its own operating system and secure memory areas that are shielded from unauthorized access.
Magnetic Stripes and Barcodes
While the chip is the primary source of digital security, the CAC also features legacy technologies to ensure interoperability. A linear barcode and a 2D PDF417 barcode are printed on the back, containing the cardholder’s Electronic Data Interchange Personal Identifier (EDIPI) and other basic personnel data. A magnetic stripe is often included for physical access to older building security systems that have not yet been upgraded to chip-reading technology.
Digital Identity and Public Key Infrastructure (PKI)
The true power of the CAC lies in its implementation of Public Key Infrastructure (PKI). This is the technology that allows the DoD to verify that a user is who they say they are and to ensure that digital communications remain confidential and untampered with.
Understanding Cryptographic Certificates
The ICC on a CAC typically stores four distinct PKI certificates, each serving a specific technological purpose:
- Identity Certificate: Used for logging into computers and gaining access to secure networks.
- Email Signing Certificate: Allows the user to digitally sign emails, proving the sender’s identity and ensuring the message has not been altered in transit.
- Encryption Certificate: Enables others to send encrypted emails to the cardholder, which can only be decrypted using the private key stored securely on the card’s chip.
- PIV Auth Certificate: Used for physical access to facilities and cross-agency authentication.
Digital Signatures and Non-Repudiation
When a user signs a document or an email with their CAC, the chip uses the stored private key to generate a unique digital fingerprint. Because the private key never leaves the chip, it provides “non-repudiation.” This means the user cannot later claim they did not sign the document, as the signature could only have been generated by someone in physical possession of the card and the knowledge of its PIN.
Two-Factor Authentication (2FA) in Action
The CAC is the “something you have” component of multi-factor authentication. To function, it requires “something you know”—a Personal Identification Number (PIN). This combination ensures that even if a card is lost or stolen, it cannot be used by an adversary without the PIN. From a technical standpoint, the PIN is not stored in plain text; it is used to “unlock” the cryptographic functions of the chip.
Data Storage: What Information is Actually on the Chip?
Beyond the certificates, the CAC’s internal memory holds a specific set of data points required for personnel management and security verification. This data is categorized under the Personal Identity Verification (PIV) standards.
Personal and Personnel Data
The chip stores the cardholder’s name, Social Security Number (usually encrypted or obscured in modern iterations), date of birth, and the Electronic Data Interchange Personal Identifier (EDIPI). The EDIPI is a unique 10-digit number assigned to every person in the DoD’s Defense Enrollment Eligibility Reporting System (DEERS). This number is the primary key used to link the physical card to the user’s digital profile in global databases.
Biometric Templates
To enhance security, the CAC contains biometric data—specifically, digital templates of the cardholder’s fingerprints. It is important to note that the chip does not usually store a full, high-resolution image of the fingerprint. Instead, it stores a mathematical “template” or “minutiae” map. When a user is required to provide a fingerprint at a high-security checkpoint, the system compares the live scan against the template stored on the card to verify a match.
Security Clearance and Organizational Indicators
While the CAC does not explicitly state “Top Secret” on its face, the digital data on the chip includes indicators of the user’s personnel category (Active Duty, Reservist, Civilian, or Contractor). This data helps automated systems determine what level of network access the user should be granted based on their role and current status in the DEERS database.
The Role of the CAC in Network and Cyber Security
The CAC is the gatekeeper for the DoD’s Global Information Grid. Its technological integration ensures that security is baked into the hardware level rather than relying on vulnerable software-based passwords.
Guarding the Digital Perimeter
Traditional passwords are prone to phishing, brute-force attacks, and credential stuffing. The CAC eliminates these vulnerabilities. Because the authentication process happens on the chip, the user’s password (the PIN) is never transmitted over the network. This makes “man-in-the-middle” attacks significantly more difficult to execute.
Mitigating Insider Threats through Least Privilege
By using the data stored on the CAC, network administrators can implement “Role-Based Access Control” (RBAC). When a user inserts their card, the system checks their digital certificates and EDIPI against permissions databases. This ensures that a user only has access to the specific data and applications required for their job, a concept known as the “Principle of Least Privilege.”
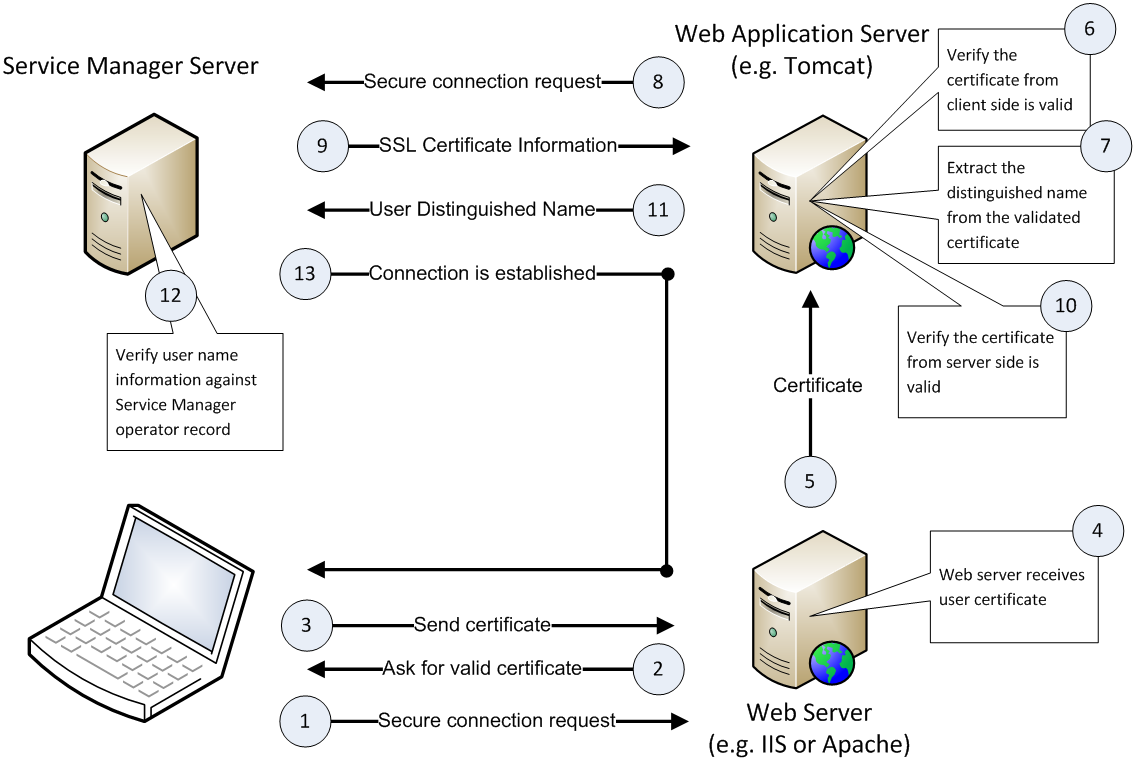
Middleware: The Interface Layer
For a computer to talk to a CAC, it requires “middleware”—software like ActivClient or OpenSC. This software acts as a translator between the computer’s operating system and the card’s integrated circuit. The middleware handles the request for certificates, the verification of the PIN, and the handshaking process required to establish a secure session.
Life Cycle and Security Protocols
The security of the CAC is not just about what is on the card, but how the card is managed from issuance to destruction.
Issuance via the DEERS System
CACs are only issued at authorized Real-time Automated Personnel Identification System (RAPIDS) sites. During issuance, the user’s identity is vetted against federal databases, their biometrics are captured, and the PKI certificates are “burned” onto the chip in a secure environment. This ensures a “Chain of Trust” from the moment the card is created.
Revocation and Certificate Expiration
One of the most critical features of the CAC tech stack is the ability to revoke access instantly. If a card is reported lost or a member is discharged, their certificates are added to a Certificate Revocation List (CRL) or flagged via the Online Certificate Status Protocol (OCSP). The next time the card is inserted into a networked reader, the system will recognize it as invalid and deny access, regardless of the physical condition of the card.
Future-Proofing Identity Management
As we move toward a “Zero Trust” architecture, the CAC remains a foundational tool. However, the tech is evolving. The DoD is exploring “Derived Credentials,” which allow the security power of a CAC to be “derived” onto a mobile device’s secure element. This allows smartphones and tablets to maintain the same level of cryptographic security as the physical card, ensuring that as technology moves toward mobile-first environments, the rigorous standards of the Common Access Card remain intact.
In conclusion, the Common Access Card is a triumph of digital security engineering. By combining physical hardware, biometric data, and complex Public Key Infrastructure, it provides a robust defense against both physical and cyber threats. For the tech-conscious professional, the CAC serves as a reminder that true security lies at the intersection of hardware-backed identity and sophisticated cryptographic protocols.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.