In the sophisticated world of enterprise software development, the ability to store, move, and reconstruct complex data structures is a fundamental requirement. Java, as one of the most resilient and widely used programming languages in the tech industry, provides a native mechanism for this process known as serialization. To the uninitiated, serialization might seem like a niche utility, but it is the backbone of many distributed systems, caching mechanisms, and persistence frameworks that power modern digital infrastructure.
The Core Mechanics: How Java Serialization Works
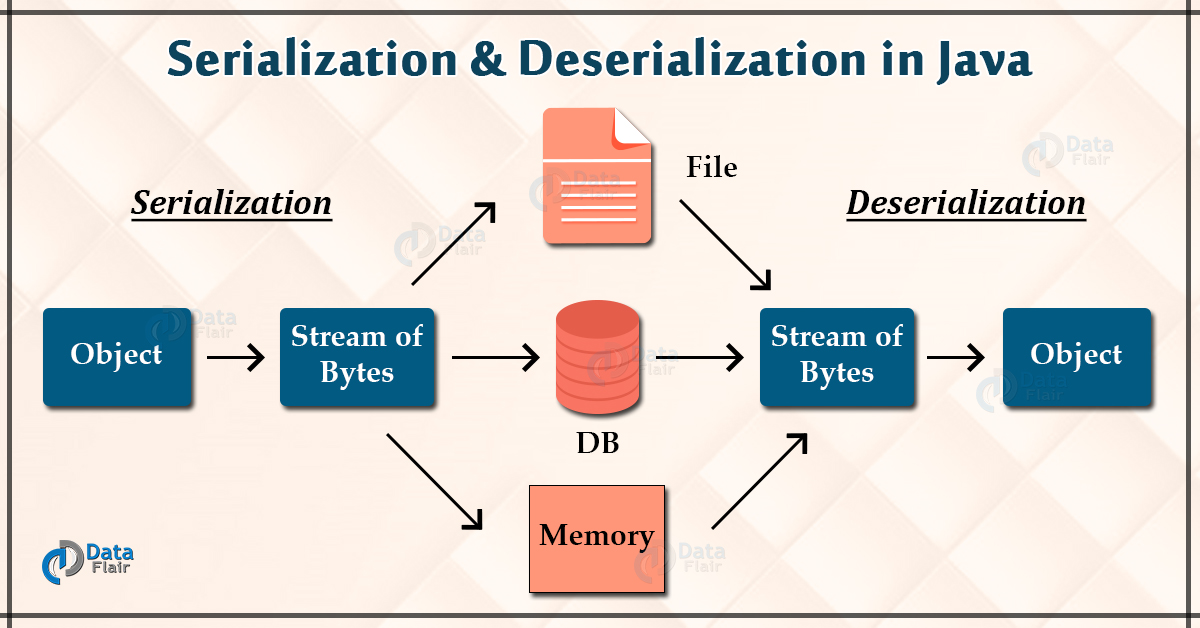
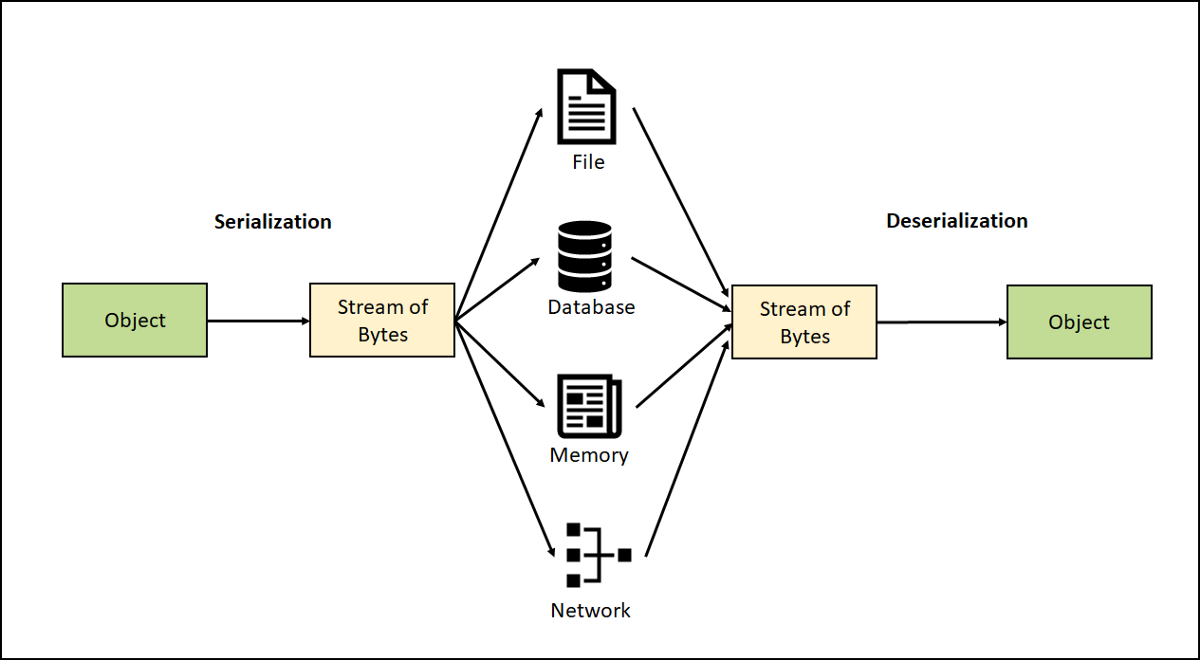
At its most basic level, serialization in Java is the process of converting the state of an object into a byte stream. This byte stream can then be persisted to a disk, stored in a database, or sent over a network to another Java Virtual Machine (JVM). The reverse process—turning a byte stream back into a live object in memory—is called deserialization.
The Serializable Interface: A Gateway to Persistence
In the Java ecosystem, serialization is not an automatic property of every object. To make a class “serializable,” it must implement the java.io.Serializable interface. This is what developers call a “marker interface.” It contains no methods or fields; its sole purpose is to signal to the JVM that the class’s objects are eligible for conversion into a byte stream. If a developer attempts to serialize an object that does not implement this interface, the system will throw a NotSerializableException, effectively acting as a safety gate.
The Role of ObjectOutputStream and ObjectInputStream
The heavy lifting of the serialization process is performed by two primary classes in the java.io package: ObjectOutputStream and ObjectInputStream.
When you want to save an object, you wrap a FileOutputStream (or any other output stream) with an ObjectOutputStream. By calling the writeObject() method, the JVM traverses the entire object graph. If your object contains references to other objects, Java attempts to serialize those as well, provided they are also serializable. Conversely, ObjectInputStream utilizes the readObject() method to reconstruct the object from the byte stream, effectively “resurrecting” the data in its original state.
Essential Components and Advanced Customization
While the basic implementation of serialization is straightforward, professional software engineering requires a deeper understanding of how to manage versioning, security, and performance.
The Importance of serialVersionUID
One of the most critical aspects of Java serialization is the serialVersionUID. This is a unique version identifier for each serializable class. The JVM uses this ID during deserialization to ensure that the sender and receiver of a serialized object have loaded classes for that object that are compatible with respect to serialization.
If a developer modifies a class—for instance, by adding a new field—without explicitly defining a serialVersionUID, the JVM will automatically generate a new one. If an older version of the object (saved with the old ID) is then read by the updated class, a InvalidClassException occurs. By explicitly declaring a static final long serialVersionUID, developers can maintain backward compatibility across different versions of their software.
Using the transient Keyword for Data Security
Not all data within an object should be serialized. Some fields might contain sensitive information, such as passwords, API keys, or personal identification numbers. Others might contain data that is only relevant in the current execution context, such as a database connection or a file handle.
The transient keyword is the developer’s primary tool for exclusion. When a field is marked as transient, the Java serialization mechanism ignores it during the conversion to a byte stream. Upon deserialization, the field is restored to its default value (e.g., null for objects, 0 for integers). This ensures that sensitive or non-persistent data does not leave the secure confines of the local memory.

Implementing Externalizable for More Control
For scenarios where the standard serialization process is too slow or consumes too much memory, Java offers the java.io.Externalizable interface. Unlike Serializable, which automates the process, Externalizable requires the developer to implement two methods: writeExternal() and readExternal(). This grants complete control over what data is written to the stream and in what format, often resulting in significant performance gains for high-throughput applications.
Practical Applications and Real-World Use Cases
Serialization is not merely a theoretical concept; it is a practical tool used across the technology landscape to solve complex architectural challenges.
Network Communication and Remote Method Invocation (RMI)
In distributed computing, different parts of an application might run on different servers. When Server A needs to send an object to Server B, it cannot send a memory address, as the memory spaces are distinct. Instead, it serializes the object into a byte stream, transmits it over TCP/IP, and Server B deserializes it. This is the foundational principle behind Java Remote Method Invocation (RMI) and was historically used extensively in Enterprise JavaBeans (EJB) architectures.
Deep Copying and Caching Strategies
In software design, sometimes a “shallow copy” of an object (where only references are copied) is insufficient. Developers use serialization to perform a “deep copy.” By serializing an object and immediately deserializing it, one creates a completely independent clone of the original object and its entire tree of dependencies.
Furthermore, serialization is a cornerstone of caching frameworks. In a high-traffic web application, reconstructing complex objects from a database on every request can be resource-intensive. Instead, the application can serialize the object and store it in a fast-access cache like Redis or an in-memory disk store. When the data is needed again, it is quickly deserialized, bypassing the expensive database query.
Modern Challenges: Security, Performance, and Alternatives
As technology has evolved, the “native” Java serialization mechanism has faced scrutiny, particularly regarding security vulnerabilities and the rise of cross-platform interoperability.
Addressing Deserialization Vulnerabilities
The tech industry has seen a rise in “deserialization attacks.” Because deserialization can trigger the execution of code (through the construction of objects and the invocation of certain methods), malicious actors can craft a byte stream that, when deserialized, executes unauthorized commands on the host system.
To combat this, modern Java versions have introduced “serialization filters.” These allow developers to define a whitelist of classes that are permitted to be deserialized, effectively blocking potential exploits. Security professionals now recommend a “security-first” approach, where serialization is only used within trusted environments or protected by robust filtering logic.
The Shift Toward JSON, XML, and Protocol Buffers
One of the primary limitations of Java serialization is that it is language-dependent. A byte stream created by a JVM can only be read by another JVM. In today’s microservices-heavy world, a Java backend often needs to communicate with a Python data science tool or a JavaScript frontend.
This has led to the widespread adoption of language-neutral formats:
- JSON (JavaScript Object Notation): The industry standard for web APIs. It is human-readable and supported by almost every programming language.
- XML: Frequently used in legacy enterprise systems and SOAP-based web services.
- Protocol Buffers (Protobuf): Developed by Google, this is a binary format that is much faster and smaller than standard Java serialization, making it ideal for high-performance microservices.
Conclusion: The Future of Java Serialization
Despite the rise of third-party alternatives, native Java serialization remains a vital skill for any serious developer. It provides a quick, integrated way to handle persistence and communication within the Java ecosystem. However, the modern “Tech” perspective on serialization is one of balance. Professional developers must weigh the convenience of the Serializable interface against the performance benefits of Externalizable and the security/interoperability requirements of modern distributed architectures.
As Java continues to evolve—with projects like “Project Loom” and “Project Valhalla” aiming to modernize the language’s core—the way we handle data and object state will continue to shift. Yet, the fundamental concept of turning an abstract object into a transportable stream of data remains a cornerstone of computer science and technical innovation.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.