In the modern digital landscape, where data breaches and state-sponsored surveillance are becoming increasingly common, the need for robust encryption has transitioned from a niche concern to a fundamental requirement. Among the various technologies developed to safeguard digital communication, OpenVPN stands out as one of the most trusted and versatile solutions. This article explores the intricate details of OpenVPN, examining its technical architecture, its security advantages, and its role in the future of digital privacy.
Understanding the Technical Architecture of OpenVPN
To understand what OpenVPN is, one must first distinguish between its two primary identities: it is both an open-source software application and a suite of communication protocols. Unlike proprietary protocols developed by individual corporations, OpenVPN was built on the philosophy of transparency and community-driven development.
The Open Source Foundation and OpenSSL
At its core, OpenVPN utilizes the OpenSSL library to provide encryption and authentication. This is a critical technical distinction. By leveraging OpenSSL, OpenVPN can utilize a wide variety of cryptographic algorithms, including AES (Advanced Encryption Standard), Camellia, and ChaCha20. Because the source code is open to the public, security researchers around the world can audit the protocol for vulnerabilities, ensuring that “backdoors” are virtually non-existent—a claim that many proprietary competitors cannot verify.
SSL/TLS Handshake Protocols
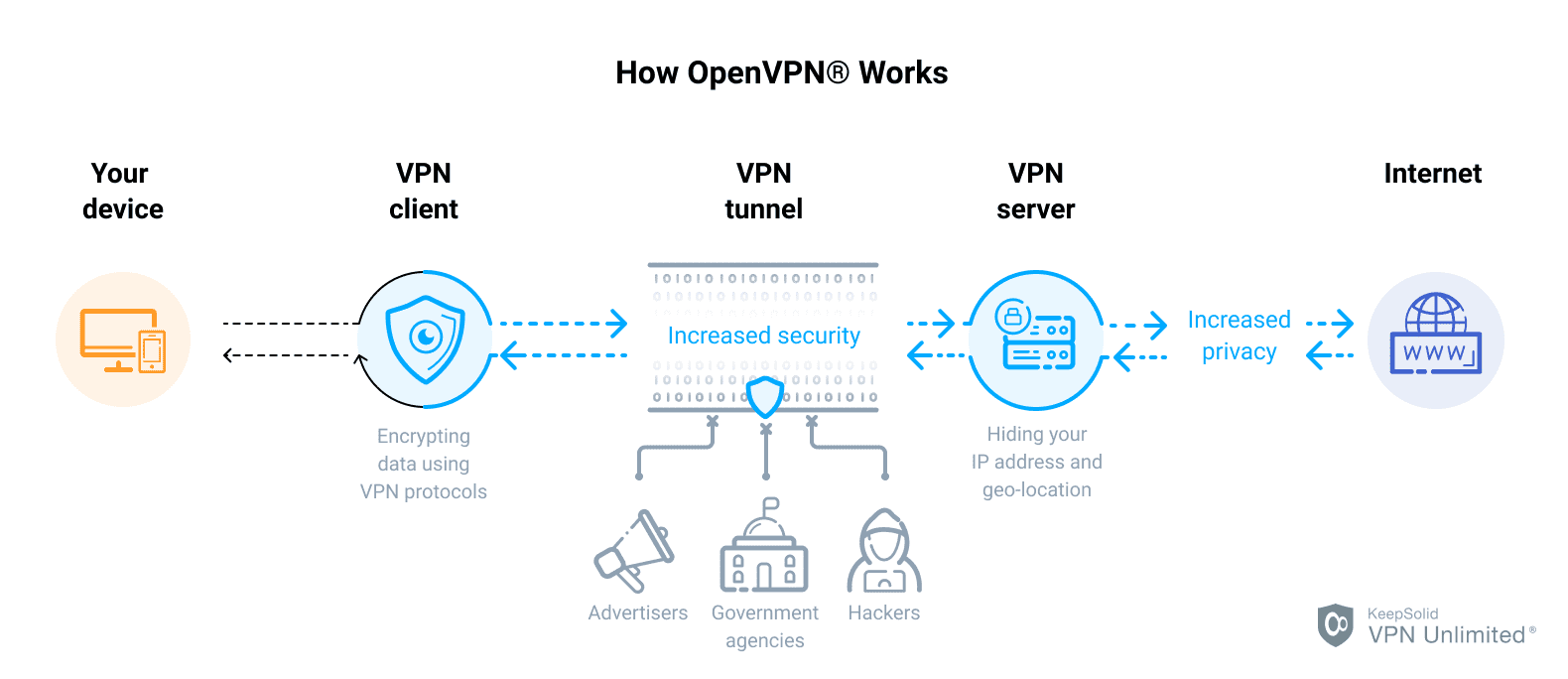
OpenVPN operates on a custom security protocol that utilizes SSL/TLS (Secure Sockets Layer/Transport Layer Security) for key exchange. This is the same logic that secures your browser’s connection to a bank (HTTPS). During the initial connection, OpenVPN performs a “handshake” where the client and server verify each other’s identities using digital certificates. This process ensures that even if a malicious actor attempts a “man-in-the-middle” attack, they cannot decrypt the traffic without the unique private keys held by the authorized devices.
Transport Layer Flexibility: UDP vs. TCP
One of the most powerful technical features of OpenVPN is its ability to run over two different transport protocols: User Datagram Protocol (UDP) and Transmission Control Protocol (TCP).
- OpenVPN over UDP: This is the default and preferred setting. UDP does not perform the “error-checking” that TCP does, which reduces latency and overhead, making it ideal for streaming, gaming, and VoIP.
- OpenVPN over TCP: While slower due to its “packet confirmation” requirements, TCP is far more reliable on unstable connections. Furthermore, TCP can be configured to run over Port 443, the same port used for standard web traffic. This makes OpenVPN over TCP incredibly effective at bypassing firewalls and censorship in restrictive environments.
Why OpenVPN is the Industry Standard for Digital Security
For over two decades, OpenVPN has maintained its position as the “gold standard” for Virtual Private Networks. This longevity is not a result of marketing, but rather a result of its uncompromising approach to data integrity and user privacy.
Robust Encryption Standards (AES-256)
OpenVPN typically employs AES-256-bit encryption. To put the strength of this encryption into perspective, a brute-force attack on a 256-bit key would require more computing power than currently exists on Earth, taking billions of years to crack. When combined with 2048-bit or 4096-bit RSA keys for authentication, OpenVPN creates a tunnel that is practically impenetrable to modern hacking techniques.
Perfect Forward Secrecy (PFS)
A vital feature of OpenVPN is its support for Perfect Forward Secrecy. PFS ensures that a unique session key is generated for every single connection. If, in a hypothetical scenario, a private encryption key were compromised in the future, the attacker would still be unable to decrypt past sessions because each session used a different, temporary key. This layer of security is essential for long-term data protection in high-stakes corporate and governmental environments.
Unmatched Customizability
Unlike “plug-and-play” protocols that offer limited options, OpenVPN is highly modular. Network administrators can tweak everything from the encryption strength and authentication methods to the size of the data packets (MTU). This flexibility allows OpenVPN to be deployed across a wide range of hardware, from high-end enterprise servers to low-power IoT (Internet of Things) devices and home routers.
Comparing OpenVPN with Other Modern Protocols
In the world of digital security, no technology exists in a vacuum. To truly understand the value of OpenVPN, it is helpful to compare it against other prominent protocols like WireGuard, IKEv2, and the now-obsolete PPTP.
OpenVPN vs. WireGuard
WireGuard is the “new kid on the block,” gaining popularity for its extreme speed and lean code base (roughly 4,000 lines compared to OpenVPN’s 100,000+). While WireGuard is faster and easier to set up, OpenVPN remains the choice for high-security environments because it supports a wider range of cryptographic algorithms and has undergone more rigorous, decades-long third-party auditing. Furthermore, OpenVPN’s ability to use TCP/Port 443 gives it an edge in bypassing strict firewalls where WireGuard (which only uses UDP) might be blocked.
OpenVPN vs. IKEv2/IPsec
IKEv2 (Internet Key Exchange version 2) is often praised for its performance on mobile devices. It excels at “reconnecting” when a user switches from Wi-Fi to cellular data. However, IKEv2 is often part of a closed-source ecosystem (developed by Microsoft and Cisco), which makes it less transparent than the open-source OpenVPN. For users who prioritize privacy and the ability to audit their security software, OpenVPN is generally preferred.
The Obsolescence of PPTP and L2TP
Protocols like PPTP (Point-to-Point Tunneling Protocol) are now considered insecure. PPTP has known vulnerabilities that can be exploited by the NSA and other agencies within minutes. L2TP/IPsec is more secure but lacks the sophisticated firewall-traversal capabilities of OpenVPN. In the hierarchy of tech security, OpenVPN effectively rendered these older protocols obsolete for anyone serious about data protection.
Practical Applications and Implementation
OpenVPN is not just for tech enthusiasts; its applications span across various sectors of the digital economy, providing the backbone for secure remote work and private browsing.
Remote Access for the Modern Workforce
With the rise of remote and hybrid work models, businesses require a secure way for employees to access internal servers. OpenVPN provides a “Client-to-Site” architecture where employees use an OpenVPN client on their laptops to create a secure tunnel into the corporate office. This ensures that sensitive company data is never exposed to the “open” internet, even if the employee is working from an unsecure public Wi-Fi network at a coffee shop.
Site-to-Site Networking
For corporations with multiple geographic locations, OpenVPN can be used to link two different offices into a single private network. This “Site-to-Site” configuration allows a branch in London to securely access resources on a server in New York as if they were in the same building. Because OpenVPN can be installed directly on routers, this process is seamless for the end-user.
Consumer VPN Services
Most of the world’s leading consumer VPN providers (such as NordVPN, ExpressVPN, and Mullvad) utilize OpenVPN as a core part of their service offering. When a user clicks “Connect” on a VPN app, the software is often launching an OpenVPN instance in the background. It provides the necessary balance of speed, security, and the ability to circumvent “geoblocks”—allowing users to access content that might be restricted in their specific geographic region.
Challenges and the Future of OpenVPN
While OpenVPN is an industry leader, it is not without its challenges. The technology must continue to evolve to remain relevant in an era of quantum computing and ultra-high-speed fiber optics.
Performance Overheads and “Bloat”
The primary criticism of OpenVPN is its performance. Because it operates in the “user space” of an operating system (rather than the “kernel space”), there is a slight delay as data moves between the application and the system’s core. This results in slightly slower speeds compared to WireGuard. However, as modern processors become faster and support hardware acceleration for AES encryption (AES-NI), the “OpenVPN speed penalty” is becoming less noticeable for the average user.
Configuration Complexity
For a novice, setting up an OpenVPN server from scratch can be a daunting task. It involves generating certificates, configuring firewall rules, and managing .ovpn configuration files. To address this, the tech community has developed various “scripts” and graphical user interfaces (GUIs) to simplify the process. Furthermore, OpenVPN Inc. (the commercial entity behind the protocol) offers “OpenVPN Access Server,” a more user-friendly version designed for businesses that require easier management.

Preparing for the Post-Quantum Era
As researchers make progress in quantum computing, there is a theoretical risk that current encryption standards (like RSA) could be broken. The OpenVPN community is already investigating “Quantum-Resistant” algorithms. Because the protocol is so flexible and modular, it is well-positioned to swap out current encryption methods for post-quantum alternatives as soon as they are standardized, ensuring that OpenVPN remains a cornerstone of digital security for decades to come.
In conclusion, OpenVPN is much more than just a tool for hiding an IP address. It is a sophisticated, open-source framework that provides the essential infrastructure for secure communication in a hyper-connected world. Its combination of high-level encryption, transport flexibility, and transparency makes it an indispensable asset for anyone—from individual users to global enterprises—looking to protect their digital footprint.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.