In an increasingly digitized world, the battle for cybersecurity is a relentless and sophisticated arms race. While much attention is rightly paid to “defensive security” – the practices and technologies designed to protect systems and data – an equally critical, though often less understood, discipline is “offensive security.” Far from being malicious, offensive security is a proactive and ethical approach that involves simulating real-world cyberattacks to identify vulnerabilities, measure the effectiveness of existing defenses, and ultimately strengthen an organization’s overall security posture. It’s about thinking like an adversary to better prepare for their inevitable attempts.
This specialized field employs a range of techniques, tools, and methodologies to systematically probe, test, and exploit weaknesses within an organization’s digital infrastructure, applications, and even human elements. By adopting the mindset of a malicious actor, cybersecurity professionals can uncover blind spots, validate security controls, and provide actionable insights that help organizations patch vulnerabilities before they can be exploited by actual attackers. This article delves into the core concepts, methodologies, benefits, tools, and the evolving landscape of offensive security, revealing why it is an indispensable component of any robust cybersecurity strategy.
The Core Concept of Offensive Security
At its heart, offensive security is a paradigm shift from solely reacting to threats to actively seeking out potential avenues of compromise. It’s an adversarial approach, executed ethically and with explicit authorization, designed to improve the target’s resilience against cyberattacks.
Defining Offensive Security
Offensive security encompasses all activities that aim to evaluate the security of an information system, network, or application by attempting to find and exploit vulnerabilities, just as a malicious attacker would. Unlike a theoretical assessment, offensive security involves practical, hands-on attempts to breach security controls. The primary goal is not to cause harm but to provide a realistic demonstration of how an attacker could compromise assets and to deliver concrete evidence of exploitable weaknesses. These activities are always conducted within a defined scope, under strict legal agreements, and with the full knowledge and permission of the asset owner.
The “Attacker’s Mindset”
A cornerstone of offensive security is the adoption of the “attacker’s mindset.” This means thinking critically about how a determined adversary would approach a target, what tools and techniques they might use, and what their motivations could be. It involves stepping beyond standard security checklists and delving into creative ways to circumvent security measures. Professionals in this field analyze systems not just for known vulnerabilities but for logical flaws, misconfigurations, and subtle weaknesses that might be overlooked by defensive security tools. This perspective allows them to anticipate emerging threats and uncover zero-day vulnerabilities – flaws previously unknown to the software vendor or the public – that standard defensive measures might miss.
Distinguishing from Defensive Security
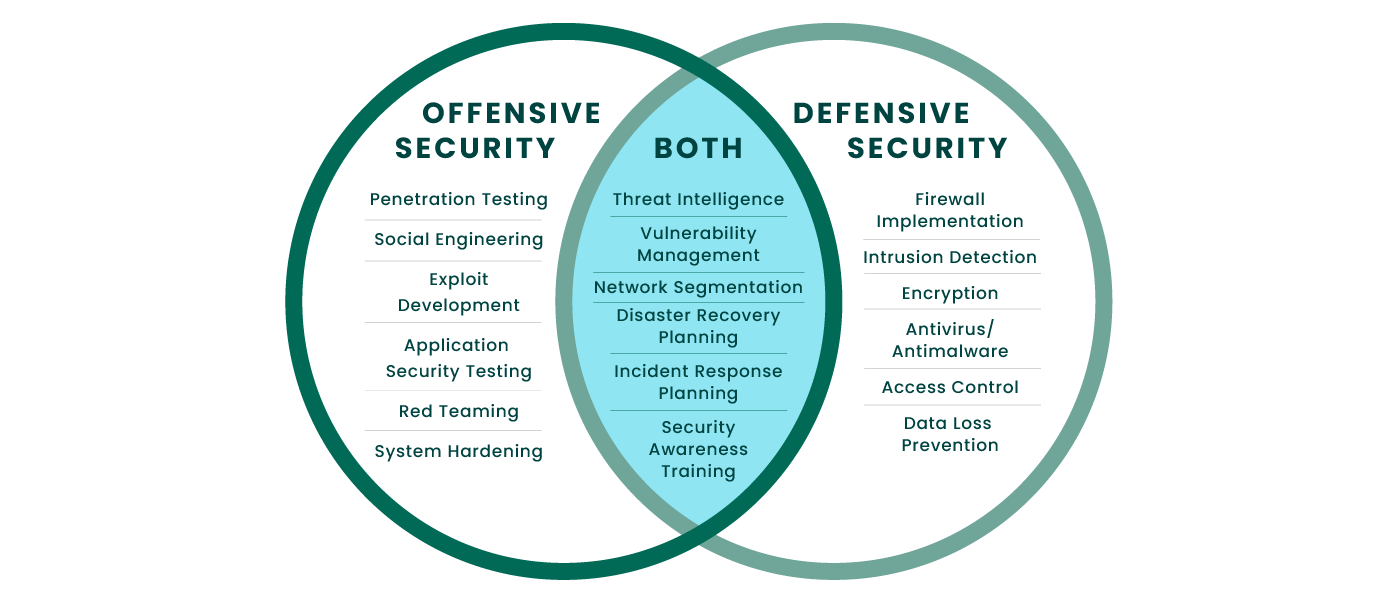
It’s crucial to understand the symbiotic relationship and key differences between offensive and defensive security. Defensive security focuses on building, maintaining, and monitoring security controls to prevent, detect, and respond to attacks. This includes firewalls, intrusion detection systems (IDS), security information and event management (SIEM) systems, antivirus software, and incident response plans. Its practitioners are the guardians, constantly fortifying the perimeter and watching for intruders.
Offensive security, on the other hand, actively challenges these defenses. It acts as the ultimate quality assurance for defensive measures. While defensive security builds the wall and mans the watchtowers, offensive security tests the wall for cracks, tries to dig tunnels underneath, and attempts to trick the watchmen. Both are indispensable for a holistic cybersecurity strategy; one without the other leaves an organization dangerously exposed. Defensive security sets the standard, and offensive security rigorously tests if that standard is truly met in the face of sophisticated threats.
Key Disciplines and Methodologies
Offensive security is not a monolithic practice but rather a collection of specialized disciplines, each employing distinct methodologies to achieve its objectives. These practices vary in scope, depth, and the level of simulation realism.
Penetration Testing (Pen Testing)
Penetration testing is perhaps the most widely recognized form of offensive security. It involves a simulated cyberattack against a specific system, network, application, or organization, designed to find exploitable vulnerabilities. Pen tests are typically scoped, time-boxed, and focus on specific objectives, such as gaining access to a particular database, achieving administrative privileges, or testing a specific application’s resilience. Testers use a combination of automated tools and manual techniques to discover, exploit, and document vulnerabilities, providing a detailed report on the findings and recommended remediation steps. Pen tests can be “black box” (no prior knowledge of the target), “white box” (full knowledge), or “gray box” (partial knowledge), mimicking various attacker scenarios.
Vulnerability Assessment
Often a precursor to penetration testing, a vulnerability assessment involves scanning systems and applications for known security weaknesses. While it identifies potential vulnerabilities, it typically does not attempt to exploit them. Tools are used to systematically check for misconfigurations, missing patches, outdated software, and common vulnerabilities listed in databases like the Common Vulnerabilities and Exposures (CVE). The output is a list of potential security flaws, prioritized by severity. Vulnerability assessments are crucial for ongoing maintenance and compliance but lack the real-world exploitation aspect that characterizes penetration testing.
Red Teaming Operations
Red teaming is a much broader and more comprehensive form of offensive security, designed to simulate a persistent, sophisticated real-world adversary. Unlike a penetration test, which often has a narrow scope and defined objectives, a red team operation typically has a broader goal, such as testing an organization’s overall detection and response capabilities over a longer period. It involves emulating the tactics, techniques, and procedures (TTPs) of advanced persistent threats (APTs), including social engineering, physical security breaches, and zero-day exploitation, without giving prior notice to the blue team (the defensive security team). The goal is to provide a realistic assessment of an organization’s ability to withstand a targeted attack and to identify weaknesses in people, processes, and technology.
Social Engineering
Cybersecurity isn’t just about technology; it’s also about people. Social engineering is a non-technical attack method that relies on manipulating individuals into divulging confidential information or performing actions that compromise security. In offensive security, social engineering tests are conducted to assess an organization’s human element, which is often considered the weakest link. This can involve phishing campaigns, pretexting (creating a fabricated scenario), baiting, or tailgating to gain unauthorized access. Ethical social engineering helps train employees to recognize and resist such attacks, significantly reducing the risk of human error-induced breaches.
Exploit Development
A highly specialized aspect of offensive security, exploit development involves creating custom tools and code to take advantage of specific software vulnerabilities. When a vulnerability is discovered for which no public exploit exists, offensive security researchers may develop one to demonstrate the impact and feasibility of exploitation. This process requires deep technical knowledge of operating systems, programming languages, and network protocols. Exploit development is critical for understanding emerging threats and for validating the severity of newly discovered vulnerabilities, pushing the boundaries of what is possible in an attack scenario.
The Importance and Benefits of Offensive Security

Implementing offensive security practices offers a wealth of benefits that extend beyond simply finding vulnerabilities. It is a proactive investment that fortifies an organization from within, significantly reducing its risk profile.
Proactive Risk Mitigation
Perhaps the most significant benefit of offensive security is its ability to enable proactive risk mitigation. Instead of waiting for a breach to occur and then reacting, organizations can use offensive security to identify and address vulnerabilities before malicious actors can exploit them. By simulating attacks, businesses can understand their exposure to various threat vectors, prioritize remediation efforts based on actual risk, and implement more effective controls. This foresight translates into fewer successful attacks, reduced downtime, and significant cost savings associated with breach response and recovery.
Strengthening Defensive Posture
Offensive security provides invaluable insights that directly contribute to strengthening an organization’s defensive posture. When a penetration test or red team operation uncovers a vulnerability, it not only highlights a specific flaw but also reveals potential weaknesses in the underlying defensive mechanisms, configurations, or monitoring capabilities. This feedback loop is essential. It allows defensive teams (blue teams) to fine-tune their security tools, update policies, improve incident response plans, and conduct targeted training for personnel. Essentially, offensive security acts as a rigorous training exercise for the defensive team, preparing them for real-world scenarios.
Compliance and Regulatory Requirements
Many industry regulations and compliance frameworks, such as PCI DSS, HIPAA, GDPR, and ISO 27001, either mandate or strongly recommend regular security assessments, including penetration testing. Engaging in offensive security practices helps organizations meet these stringent requirements, demonstrating due diligence in protecting sensitive data and systems. Beyond mere compliance, it also showcases a commitment to robust security, which can enhance an organization’s reputation and trust among customers and partners. Failing to conduct such assessments can result in hefty fines, legal repercussions, and severe reputational damage.
Business Continuity and Reputation Protection
A successful cyberattack can cripple business operations, leading to significant financial losses, data theft, intellectual property compromise, and severe damage to an organization’s reputation. By proactively identifying and neutralizing potential threats through offensive security, organizations can significantly enhance their business continuity. Reducing the likelihood of a major security incident protects critical business processes, ensures uninterrupted service delivery, and safeguards customer trust. In today’s interconnected world, an organization’s security posture is increasingly tied to its brand image and market value, making offensive security a vital component of long-term business resilience.
Tools and Technologies in Offensive Security
The field of offensive security relies on a diverse array of tools and technologies, ranging from sophisticated frameworks to specialized scripts, all designed to facilitate the discovery and exploitation of vulnerabilities. These tools empower practitioners to simulate attacks effectively and efficiently.
Common Offensive Security Frameworks
Several powerful frameworks serve as foundational toolkits for offensive security professionals.
- Metasploit Framework: One of the most widely used open-source penetration testing tools, Metasploit provides a vast collection of exploits, payloads, and post-exploitation modules. It allows users to develop, test, and execute exploits against remote targets, making it indispensable for identifying and validating vulnerabilities.
- Nmap (Network Mapper): This free and open-source utility is essential for network discovery and security auditing. Nmap can identify hosts and services on a computer network, discovering open ports, operating systems, and versions of software running on devices, providing a crucial reconnaissance layer for any offensive operation.
- Burp Suite: A popular integrated platform for performing security testing of web applications. Burp Suite’s various tools work seamlessly together to support the entire testing process, from initial mapping and analysis of an application’s attack surface to finding and exploiting security vulnerabilities.
- Kali Linux: A Debian-derived Linux distribution designed for digital forensics and penetration testing. It comes pre-installed with hundreds of tools, including those mentioned above, making it a go-to operating system for offensive security practitioners.
Open-Source vs. Commercial Tools
The offensive security landscape features a mix of open-source and commercial tools, each with its advantages. Open-source tools, such as Metasploit, Nmap, and Wireshark, offer flexibility, community support, and often come without a direct cost, making them accessible. However, they may require more technical expertise to configure and use effectively. Commercial tools, on the other hand, often provide more user-friendly interfaces, dedicated support, regular updates, and advanced features, sometimes incorporating machine learning capabilities. Examples include Cobalt Strike for red teaming and Nessus for vulnerability scanning. The choice between open-source and commercial tools often depends on the specific project requirements, budget, and the expertise of the security team. Many organizations utilize a hybrid approach, leveraging the strengths of both.
Role of Automation and AI in Offensive Operations
The increasing complexity and scale of digital environments make manual security testing a daunting task. Automation plays a crucial role in offensive security by speeding up repetitive tasks, enabling continuous vulnerability scanning, and managing large-scale operations. Automated tools can efficiently identify common vulnerabilities, conduct reconnaissance, and even attempt basic exploits.
Furthermore, artificial intelligence (AI) and machine learning (ML) are beginning to transform offensive security. AI can analyze vast datasets to identify attack patterns, predict potential vulnerabilities, and even autonomously develop novel attack vectors. For instance, AI can enhance social engineering campaigns by crafting highly personalized phishing emails or assist in reverse engineering malware. While still in its nascent stages, the integration of AI promises to make offensive security operations more sophisticated, efficient, and capable of discovering complex, multi-stage attack scenarios that might elude traditional methods.
The Evolving Landscape and Future of Offensive Security
The digital threat landscape is in constant flux, driven by technological advancements, new vulnerabilities, and the increasing sophistication of malicious actors. Offensive security must continuously adapt to remain effective and relevant.
Emerging Threats (e.g., IoT, Cloud, AI-driven attacks)
As technology evolves, so do the targets and methods of attack. The proliferation of Internet of Things (IoT) devices, often with weak default security, presents a vast new attack surface. Cloud computing environments, with their shared responsibility models and complex configurations, introduce unique security challenges that require specialized offensive security testing. Furthermore, the rise of AI and machine learning not only offers defensive capabilities but also presents new tools and methods for attackers, enabling more sophisticated and automated attacks. Offensive security professionals must continually update their skills and knowledge to address vulnerabilities specific to these emerging technologies, from assessing the security of smart home devices to testing serverless functions in the cloud, and even defending against AI-generated deepfakes used in social engineering.
Legal and Ethical Considerations
Offensive security, by its very nature, involves activities that would be illegal if performed without authorization. Therefore, strict legal and ethical boundaries are paramount. All offensive security engagements must be conducted with explicit, written consent from the asset owner, clearly defining the scope, objectives, and legal boundaries of the assessment. Professionals in this field adhere to strict codes of conduct, ensuring that no actual harm is caused, data integrity is maintained, and privacy is respected. The “ethical hacker” operates under a mandate to improve security, not to exploit it for personal gain or malicious intent. Misuse of offensive security knowledge and tools can lead to severe legal penalties and reputational damage.

Career Paths in Offensive Security
The growing demand for cybersecurity expertise has fueled a robust job market for offensive security professionals. Common career paths include:
- Penetration Tester: Specializing in finding and exploiting vulnerabilities in applications, networks, and systems.
- Red Team Operator: Conducting full-scope attack simulations against an organization’s defenses.
- Vulnerability Researcher: Discovering zero-day vulnerabilities in software and hardware.
- Exploit Developer: Creating custom exploits for identified vulnerabilities.
- Security Consultant: Advising organizations on their security posture and conducting various offensive security assessments.
These roles require a blend of technical skills, including networking, operating systems, programming, and cryptography, along with strong problem-solving abilities and a deep understanding of attacker methodologies. Continuous learning and adaptation are key to success in this dynamic field.
In conclusion, offensive security is not merely a technical practice but a critical philosophical approach to cybersecurity. By systematically challenging an organization’s defenses through ethical simulations of attacks, it uncovers weaknesses, fortifies existing controls, and builds resilience against the ever-present threat of cyberattacks. In an era where digital threats are increasingly sophisticated and persistent, embracing offensive security is no longer an option but a strategic imperative for any organization committed to safeguarding its digital assets, maintaining business continuity, and preserving its reputation.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.