In the dynamic and ever-evolving landscape of digital security, understanding the tools and techniques employed by both attackers and defenders is paramount. Among the arsenal of offensive cybersecurity tools, Meterpreter stands out as a particularly potent and versatile post-exploitation framework. Developed by Rapid7 as part of the Metasploit Project, Meterpreter is not a standalone exploit, but rather a sophisticated payload designed to be delivered after an initial vulnerability has been successfully leveraged. Its primary purpose is to provide an attacker with advanced control and extensive capabilities over a compromised system, allowing them to move laterally, escalate privileges, exfiltrate data, and maintain persistence.
The realm of cybersecurity encompasses a broad spectrum of knowledge, from understanding emerging technology trends and the latest AI tools to mastering personal branding and navigating the complexities of personal finance. Within this vast digital ecosystem, the importance of digital security cannot be overstated. As individuals and organizations increasingly rely on technology for daily operations, communication, and commerce, the threat of cyberattacks grows in parallel. This is where tools like Meterpreter come into play, representing a crucial element in the ongoing battle for digital control and security.
This article will delve into the intricacies of Meterpreter, exploring its fundamental functionalities, its operational mechanisms, and its significance within the broader context of cybersecurity. We will examine why it is such a sought-after tool by penetration testers and malicious actors alike, and how its capabilities can be leveraged for both offensive and defensive analyses.
Understanding Meterpreter: Beyond the Initial Breach
The term “Meterpreter” itself is a portmanteau of “meter” (referring to its ability to meter/measure and control) and “interpreter” (highlighting its command-line interface and dynamic functionality). Unlike traditional payloads that might execute a single command and then terminate, Meterpreter operates as an in-memory, extensible shell. This means it runs directly within the memory space of the compromised process, making it significantly harder to detect by traditional antivirus software and disk-based forensics.
The Core Functionality: What Meterpreter Does
At its heart, Meterpreter empowers an attacker with a comprehensive suite of commands to interact with and manipulate a compromised system. These functionalities can be broadly categorized as follows:
- System Information Gathering: Once Meterpreter is active, it can immediately begin gathering crucial information about the compromised host. This includes details about the operating system, installed software, running processes, network configuration, logged-in users, and system architecture. This intelligence is vital for planning subsequent actions and identifying further attack vectors.
- File System Manipulation: Meterpreter provides robust capabilities to navigate and interact with the compromised system’s file system. Attackers can upload and download files, list directories, create, delete, and rename files, and even modify file permissions. This is essential for exfiltrating sensitive data or planting malicious files.
- Process Management: The ability to control and manipulate running processes is a key feature. Meterpreter can list active processes, terminate them, and importantly, it can inject itself into other processes. This process migration technique further enhances stealth and allows the attacker to leverage the privileges of the newly infiltrated process.
- Privilege Escalation: Gaining elevated privileges (e.g., from a standard user to an administrator or root) is a common goal in post-exploitation. Meterpreter offers various modules and techniques to facilitate privilege escalation, allowing the attacker to gain deeper access and control over the system.
- Network Pivoting and Lateral Movement: Meterpreter is not designed to be confined to a single compromised machine. It excels at enabling lateral movement within a network. By leveraging the compromised host’s network access, attackers can scan adjacent network segments, establish new connections to other vulnerable systems, and essentially “pivot” their attack.
- Persistence: Maintaining access to a compromised system is crucial for long-term objectives. Meterpreter provides mechanisms to establish persistence, ensuring that the attacker can regain access even after a system reboot or if the initial exploit is patched. This can involve creating new user accounts, modifying startup routines, or installing backdoors.
- Credential Dumping: A primary objective for many attackers is to obtain user credentials. Meterpreter includes functionalities to dump password hashes and clear-text passwords from memory, which can then be used to authenticate to other systems or services.
- Screen Capture and Keystroke Logging: For more interactive espionage, Meterpreter can capture screenshots of the compromised user’s desktop and log keystrokes, providing valuable insights into user activity and potentially revealing sensitive information.
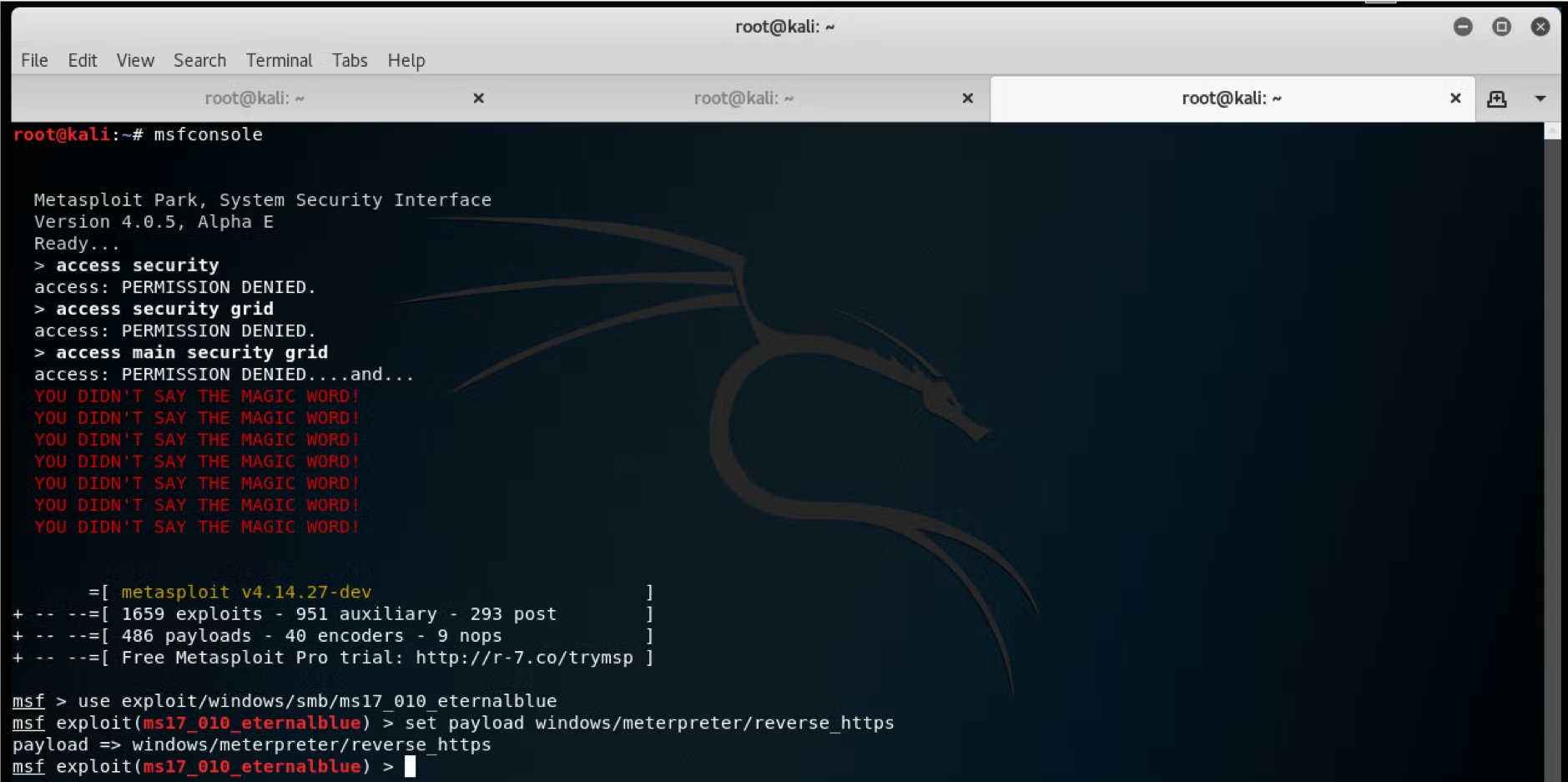
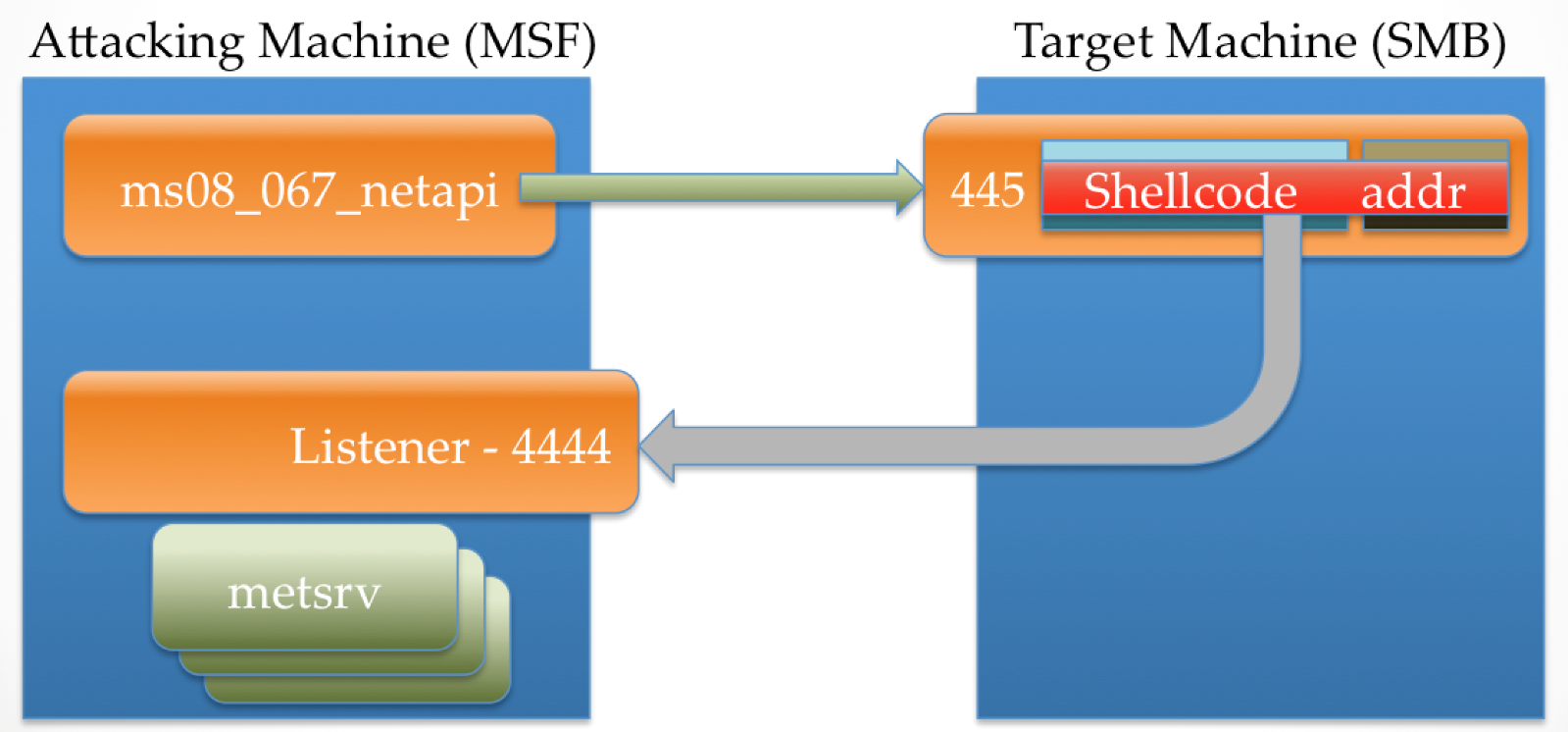
The Technical Underpinnings: How Meterpreter Works
Meterpreter’s power and stealth stem from its innovative architecture. Unlike traditional payloads that rely on a separate executable file, Meterpreter is loaded as a DLL (Dynamic Link Library) into the memory space of a compromised process. This in-memory operation has several significant advantages:
- Stealth: By residing entirely in RAM, Meterpreter avoids writing to the disk, making it significantly harder for signature-based antivirus software to detect. Traditional security solutions often rely on scanning files for known malicious patterns, a method rendered less effective against in-memory threats.
- Extensibility: Meterpreter’s core functionality can be extended through a rich ecosystem of plugins and scripts. This allows users to add new commands and capabilities on the fly, tailoring the payload to specific attack scenarios. These extensions can be loaded dynamically, further enhancing its adaptability.
- Interactivity: The interactive command-line interface provides a seamless experience for the attacker, allowing them to issue commands and receive responses in real-time. This is akin to having a remote command shell, but with far greater power and flexibility.
- Platform Independence (to a degree): While specific Meterpreter payloads are compiled for different operating systems (e.g., Windows, Linux, macOS), the core concepts and command structures remain consistent, offering a familiar experience for users across various platforms.
The communication between the attacker’s control machine and the Meterpreter payload on the compromised system is typically established over a network connection. This connection can be encrypted, further obscuring the malicious activity. Common communication channels include TCP and HTTP(S), with HTTP(S) often being used to blend in with legitimate web traffic, making it even harder to distinguish from normal network activity.
Meterpreter in the Cybersecurity Ecosystem

The existence and capabilities of Meterpreter highlight several critical aspects of the cybersecurity landscape.
The Role in Penetration Testing and Red Teaming
For ethical hackers and penetration testers, Meterpreter is an indispensable tool. Its comprehensive functionalities allow them to simulate realistic attack scenarios, identify vulnerabilities beyond initial access, and assess the true impact of a compromise. By using Meterpreter, penetration testers can:
- Demonstrate the full attack chain: Move beyond simply proving an initial exploit works and show how an attacker could escalate privileges, exfiltrate data, and maintain long-term access.
- Test incident response capabilities: By operating stealthily and demonstrating advanced techniques, Meterpreter can help organizations test the effectiveness of their detection and response mechanisms.
- Identify critical assets: Through lateral movement and information gathering, penetration testers can help organizations identify which systems and data are most vulnerable and valuable.
The Threat to Organizations and Individuals
Conversely, Meterpreter represents a significant threat to organizations and individuals. Malicious actors leverage its power to conduct sophisticated cyberattacks, including:
- Data breaches: Exfiltrating sensitive customer data, intellectual property, or financial information.
- Ransomware deployment: Gaining initial access and then deploying ransomware to encrypt critical systems.
- Espionage: Conducting long-term surveillance and intelligence gathering.
- Botnet creation: Compromising systems to create a network of bots for distributed denial-of-service (DDoS) attacks or other malicious activities.
The ability of Meterpreter to evade detection and maintain persistence makes it a formidable weapon in the hands of determined attackers. Understanding its capabilities is therefore crucial for building effective defenses.
Defending Against Meterpreter and Similar Threats
While Meterpreter is a powerful offensive tool, effective defensive strategies can significantly mitigate its impact. The principles of good cybersecurity hygiene are the first line of defense.
Proactive Security Measures
- Regular Patching and Updates: Keeping all software, operating systems, and applications updated with the latest security patches is paramount. Many Meterpreter deployments rely on exploiting known vulnerabilities that have already been patched.
- Strong Access Controls and Least Privilege: Implementing strict access controls and adhering to the principle of least privilege ensures that users and processes only have the necessary permissions to perform their functions. This limits the scope of damage an attacker can inflict if they gain access.
- Network Segmentation: Dividing networks into smaller, isolated segments can prevent lateral movement. If one segment is compromised, the attacker’s ability to spread to other critical areas is significantly hampered.
- Endpoint Detection and Response (EDR) Solutions: Advanced EDR solutions are designed to detect malicious activity at the endpoint, including in-memory threats. These solutions go beyond traditional signature-based antivirus and employ behavioral analysis, anomaly detection, and threat hunting capabilities.
- Intrusion Detection and Prevention Systems (IDPS): Network-based IDPS can monitor network traffic for suspicious patterns and block malicious connections, potentially preventing the initial delivery or communication of Meterpreter.
- Security Awareness Training: Educating users about phishing attempts, social engineering tactics, and safe browsing habits can prevent initial compromise through human error.
Incident Response and Forensics
- Robust Logging and Monitoring: Comprehensive logging of system and network activity is essential for detecting and investigating compromises. Analyzing these logs can reveal the tell-tale signs of Meterpreter activity.
- Memory Forensics: In the event of a suspected compromise, memory forensics can be crucial for analyzing the contents of system RAM to identify the presence of in-memory payloads like Meterpreter.
- Threat Intelligence: Staying informed about the latest threats, vulnerabilities, and attack techniques, including those involving Meterpreter, allows security teams to proactively update their defenses and incident response plans.
In conclusion, Meterpreter represents a sophisticated and highly capable post-exploitation framework that has profoundly influenced the landscape of offensive cybersecurity. Its in-memory operation, extensibility, and broad range of functionalities make it a powerful tool for both ethical hackers and malicious actors. While its capabilities pose a significant threat, a layered approach to cybersecurity, encompassing proactive measures, robust detection mechanisms, and effective incident response, is essential for mitigating the risks associated with Meterpreter and similar advanced threats in our increasingly digitized world. Understanding what Meterpreter is, how it operates, and how to defend against it is a critical component of any comprehensive digital security strategy.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.