In the intricate world of biology, an inflammatory response is the body’s fundamental reaction to injury or infection. It’s a complex, dynamic process designed to protect the organism, remove harmful stimuli, and initiate the healing process. Characterized by redness, heat, swelling, pain, and loss of function, it is a testament to the body’s sophisticated defense mechanisms. But what if we were to translate this powerful biological metaphor into the realm of technology, particularly in the context of digital security? What would an “inflammatory response” look like for a software system, a network, or an entire digital infrastructure?
In the rapidly evolving landscape of cybersecurity, systems are constantly under threat from diverse adversaries – from sophisticated state-sponsored actors to opportunistic cybercriminals and even internal vulnerabilities. Just as a biological organism must react swiftly and effectively to pathogens or damage, a digital system requires an equally robust and adaptive response mechanism to protect its integrity, confidentiality, and availability. This article explores the concept of an “inflammatory response” within the technology sector, examining how digital systems detect, react to, and recover from attacks, drawing insightful parallels between biological defense and cybersecurity incident response.
The Biological Blueprint: Understanding Systemic Defense
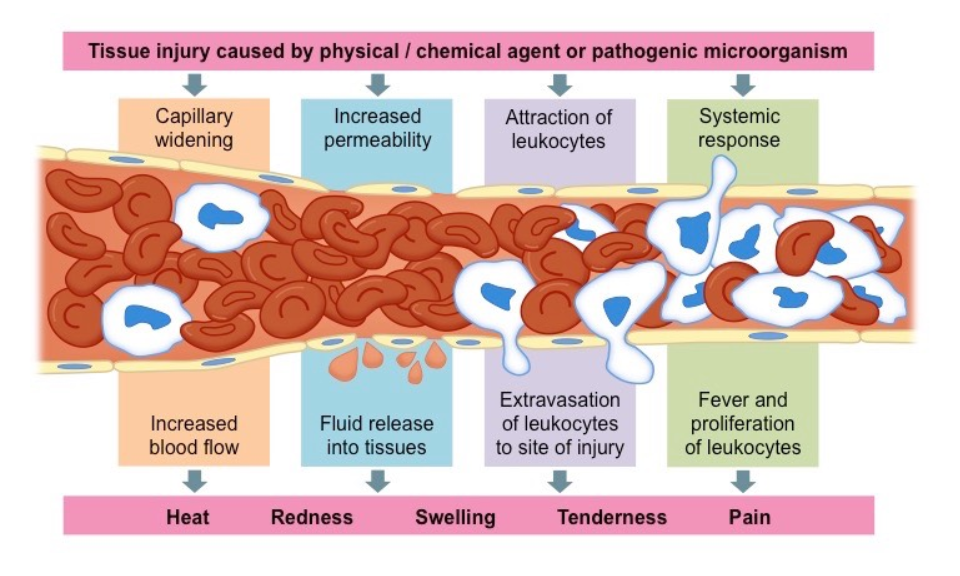
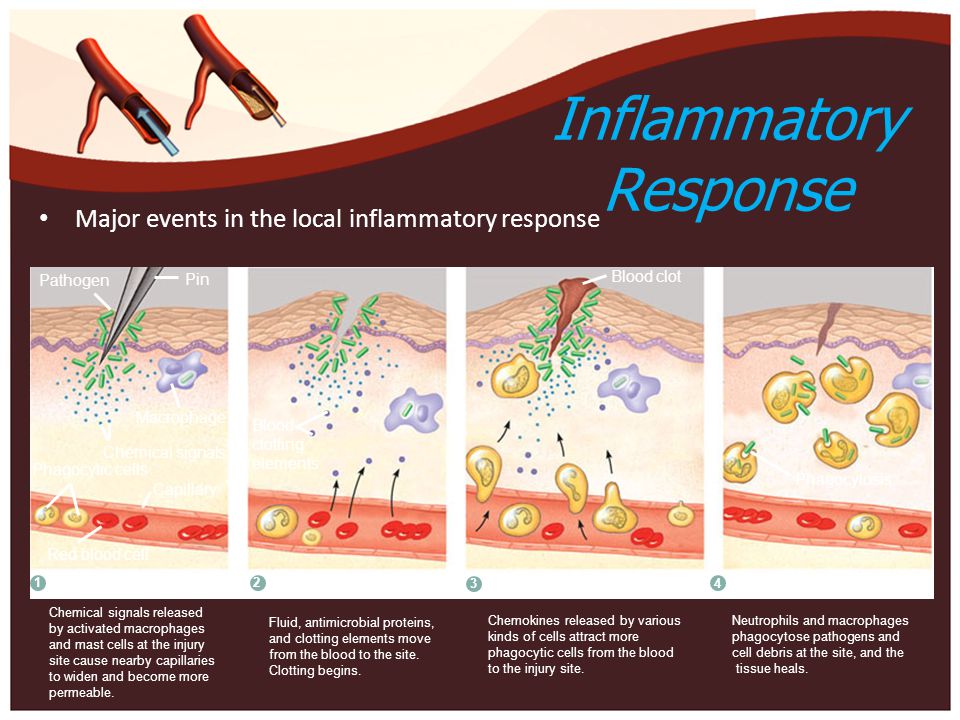
Before delving into the digital realm, a brief understanding of the biological inflammatory response provides the perfect conceptual framework. When tissues are injured or infected, a cascade of events unfolds:
- Recognition: Immune cells detect foreign invaders or damaged cells.
- Vascular Response: Blood vessels dilate, increasing blood flow to the affected area, bringing in immune cells and chemical mediators.
- Cellular Recruitment: White blood cells (like neutrophils and macrophages) are recruited to the site to engulf pathogens and clear debris.
- Tissue Repair: As the threat is neutralized, the body begins to repair damaged tissue.
This coordinated series of actions is essential for survival. It’s not just about fighting off an immediate threat, but also about laying the groundwork for recovery and rebuilding. In the context of technology, an analogous mechanism is critical for the resilience and long-term health of digital systems.
Digital Systems Under Siege: The “Inflammatory Response” in Cybersecurity
In cybersecurity, the “inflammatory response” refers to the comprehensive set of actions an organization takes when a security incident occurs. It’s an organized, methodical approach to detecting, containing, eradicating, recovering from, and learning from cyberattacks. This digital inflammatory response is not a single tool or a one-time fix but a continuous process integrated into an organization’s overall security posture.
The threats that trigger this response are varied: malware infections, phishing attacks, denial-of-service (DoS) attempts, data breaches, unauthorized access, insider threats, and zero-day exploits. Each of these can be likened to a pathogen or injury that requires immediate attention. Without an effective “inflammatory response,” a minor compromise can quickly escalate into a catastrophic system failure, leading to significant financial losses, reputational damage, and operational disruption.
The parallels are striking:
- Pathogen/Injury: A cyberattack (malware, breach, etc.)
- Immune System: The organization’s security team, tools, and processes.
- Inflammation Symptoms: Alerts, system performance degradation, data anomalies, unauthorized activity.
- Healing Process: Incident response, remediation, system hardening, and policy updates.
The goal, like its biological counterpart, is not just to survive the attack but to emerge stronger, more resilient, and better prepared for future threats.
Stages of a Digital “Inflammatory Response”: From Detection to Recovery
A well-defined incident response plan is the backbone of a robust digital “inflammatory response.” Industry standards, such as those from NIST (National Institute of Standards and Technology), typically break down the process into several critical phases:
Initial Detection and Alert Generation
The first phase is analogous to the body’s immediate recognition of a threat. In digital systems, this involves continuous monitoring for anomalies, suspicious activities, and known attack signatures. Tools like Intrusion Detection Systems (IDS), Security Information and Event Management (SIEM) systems, Endpoint Detection and Response (EDR) solutions, and network traffic analysis play a crucial role. These systems collect logs, monitor network packets, analyze user behavior, and apply threat intelligence to identify potential breaches.
When a suspicious event is detected, an alert is generated, signaling the potential onset of a “digital inflammation.” This alert might trigger automated responses, such as blocking an IP address, or escalate the incident to human analysts for further investigation. The speed and accuracy of this initial detection are paramount, as every minute lost can increase the potential damage. Early detection allows for a more contained and less costly response.
Containment and Isolation
Once an incident is confirmed, the immediate priority is containment – preventing the attack from spreading further and minimizing its impact. This is akin to the body’s attempt to localize an infection. Strategies include:
- Network Segmentation: Isolating affected systems or networks from the rest of the infrastructure.
- System Shutdown: Temporarily taking compromised systems offline if necessary.
- Blocking Malicious Traffic: Implementing firewall rules or network access control lists (ACLs) to stop communication with threat actors.
- Credential Revocation: Disabling compromised user accounts or changing passwords.
The goal here is to create a digital “quarantine zone” to prevent lateral movement of the attacker and protect uninfected assets. This phase requires careful planning to avoid disrupting critical business operations unnecessarily, while still being aggressive enough to halt the attack’s progression.
Eradication and Threat Removal
With the threat contained, the next step is to eradicate it completely. This involves meticulously removing all traces of the attacker and their tools from the environment. This phase is comparable to the immune system actively destroying pathogens and clearing damaged cells. Key activities include:
- Malware Removal: Using antivirus software, specialized cleanup tools, or manual processes to remove malicious code.
- Vulnerability Patching: Applying security updates and patches to fix the vulnerabilities that allowed the breach in the first place.
- Backdoor Identification and Removal: Searching for and eliminating any persistent access mechanisms left by the attacker.
- Forensic Analysis: Deep diving into logs and system images to understand the full scope of the compromise, identify patient zero, and ensure all affected areas are addressed.
Eradication must be thorough, as any lingering remnants of the attack can lead to re-infection or continued compromise. This often requires significant expertise and a deep understanding of the attacker’s tactics, techniques, and procedures (TTPs).
Recovery and Restoration
Once the threat has been eradicated, the focus shifts to restoring affected systems and data to their pre-incident state. This is the “healing” phase, where the digital organism repairs itself. This involves:
- System Rebuilding: Rebuilding compromised servers or workstations from clean backups.
- Data Restoration: Restoring lost or corrupted data from trusted backups.
- System Hardening: Implementing additional security controls and configurations to prevent similar incidents.
- Monitoring: Placing enhanced monitoring on recovered systems to ensure no recurrence of the attack.
The priority is to bring business operations back online safely and efficiently, ensuring data integrity and system reliability. This phase often involves significant coordination between security teams, IT operations, and business units.
Post-Incident Analysis and Prevention
The final, crucial stage of the digital inflammatory response is often the most overlooked: learning from the incident. This involves a thorough post-mortem analysis to understand exactly what happened, why it happened, and how similar incidents can be prevented in the future. This continuous improvement loop is vital for building “digital immunity.” Activities include:
- Root Cause Analysis: Identifying the underlying cause of the incident.
- Lessons Learned: Documenting the incident response process, identifying strengths and weaknesses.
- Policy and Procedure Updates: Revising security policies, incident response plans, and operational procedures based on new insights.
- Security Control Enhancements: Implementing new technologies or improving existing security controls (e.g., enhanced monitoring, stronger authentication, security awareness training).
- Threat Intelligence Sharing: Contributing to community knowledge by sharing anonymized indicators of compromise (IOCs) and TTPs.
This phase transforms a reactive event into a proactive opportunity, fortifying the organization’s defenses and making it more resilient against future attacks.
Proactive Measures: Strengthening Digital Immunity
Just as a healthy lifestyle and vaccinations bolster the biological immune system, robust proactive measures are essential for strengthening an organization’s “digital immunity.” These are the preventative actions taken to minimize the likelihood and impact of security incidents:
- Robust Security Architecture: Designing systems with security in mind from the ground up, incorporating principles like least privilege, defense-in-depth, and zero trust.
- Regular Security Audits and Penetration Testing: Proactively identifying vulnerabilities before attackers can exploit them.
- Employee Security Awareness Training: Educating staff to recognize and report threats like phishing attempts, as human error remains a significant attack vector.
- Patch Management: Consistently applying security updates to all software and hardware to close known vulnerabilities.
- Data Backup and Recovery Strategies: Ensuring critical data is regularly backed up and can be quickly restored.
- Threat Intelligence Integration: Utilizing real-time information about emerging threats and attack methodologies to anticipate and counter them.
- Secure Coding Practices: Training developers to write secure code to reduce software vulnerabilities.
These proactive measures act as the “antibodies” and “white blood cells” of the digital immune system, continuously defending against threats and reducing the chances of a full-blown “inflammatory response.”

The Role of AI and Automation in Enhancing Response
The sheer volume and sophistication of modern cyber threats can overwhelm human security teams. This is where Artificial Intelligence (AI) and automation are becoming increasingly critical in enhancing the digital “inflammatory response.”
- Automated Detection: AI-driven tools can analyze vast amounts of data, detect subtle anomalies, and identify complex attack patterns far more rapidly than humans. Machine learning algorithms can learn normal system behavior and flag deviations instantly.
- Orchestrated Containment: Security Orchestration, Automation, and Response (SOAR) platforms can automate initial containment actions, such as isolating compromised endpoints, blocking malicious IP addresses, or resetting user credentials, reducing response times from hours to minutes or even seconds.
- Faster Eradication: AI can assist in malware analysis, identifying variants and recommending specific eradication steps, speeding up the cleanup process.
- Predictive Analytics: AI can analyze historical incident data and current threat landscapes to predict potential attack vectors, allowing organizations to strengthen defenses proactively.
- Reduced Alert Fatigue: AI can help filter out false positives from security alerts, allowing human analysts to focus on genuine threats and critical incidents.
While AI and automation cannot fully replace human intuition and strategic decision-making, they significantly augment the capabilities of security teams, making the digital “inflammatory response” faster, more precise, and more scalable in the face of an ever-growing threat landscape.
In conclusion, viewing cybersecurity through the lens of a biological inflammatory response provides a powerful and intuitive framework for understanding the essential elements of incident detection, reaction, and recovery in digital systems. Just as our bodies possess an innate ability to heal and protect themselves, robust digital systems must be equipped with comprehensive, adaptive, and proactive mechanisms to withstand the onslaught of modern cyber threats. By embracing this holistic perspective and continuously refining our incident response capabilities, organizations can build truly resilient digital ecosystems, capable of not only surviving attacks but emerging stronger and more secure.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.