If you have ever spent time monitoring your PC’s performance through the Windows Task Manager, you have likely encountered a sea of cryptic process names. While some, like “Google Chrome” or “Spotify,” are self-explanatory, others are shrouded in technical ambiguity. One such process that frequently catches the eye of concerned users is AggregatorHost.exe.
Often appearing unexpectedly and sometimes consuming noticeable system resources, AggregatorHost is a component that triggers two immediate questions: “What does it do?” and “Is it a security risk?” In this comprehensive guide, we will break down the technical architecture of AggregatorHost, its role within the Windows ecosystem, and how to manage it if it begins to impact your computer’s performance.

1. The Core Functions of AggregatorHost.exe
At its most basic level, AggregatorHost.exe is an executable file developed by Microsoft as an integral part of the Windows operating system. Specifically, it is a component of the Windows Security (formerly Windows Defender) platform. In the modern Windows 10 and 11 environments, security is no longer a single “app” but a complex web of interconnected services working in the background.
The Role of Data Aggregation
The term “Aggregator” in the name provides the biggest clue to its function. In software engineering, an aggregator is a tool that collects data from various sources and compiles it into a single, cohesive format. AggregatorHost serves as a centralized hub for security-related telemetry and background tasks. It gathers data points from various security modules—such as real-time protection, firewall logs, and network inspection—and prepares that data for analysis by the Windows Security Center.
Coordination of Security Tasks
Windows does not perform all its security checks at once; doing so would paralyze the CPU. Instead, it schedules tasks like quick scans, definition updates, and “health reports.” AggregatorHost acts as a “host” for these scheduled operations. By using a host process, Windows can isolate these tasks from the main kernel, ensuring that if a specific security sub-task crashes, it does not take down the entire operating system.
Integration with the Windows Security Ecosystem
AggregatorHost is deeply integrated with the Windows Defender Advanced Threat Protection (ATP) and the Windows Security app interface. When you open your “Security at a Glance” dashboard, the information displayed regarding your device’s health and protection status often relies on the data processed by AggregatorHost.
2. Why is AggregatorHost Running in the Background?
Many users become concerned when they see AggregatorHost active even when they aren’t actively running a virus scan. However, its presence is a sign that Windows is performing its “housekeeping” duties to keep your digital environment safe.
Telemetry and Proactive Defense
Modern cybersecurity is proactive, not reactive. Microsoft uses telemetry—anonymous data about how system processes are behaving—to identify new malware strains globally. AggregatorHost is one of the primary conduits for this telemetry. It collects information about suspicious file behaviors and sends it to Microsoft’s cloud-based protection servers. This allows your PC to defend against “zero-day” threats that haven’t been added to a local database yet.
Background Maintenance and Scanning
Windows is designed to run maintenance tasks when the system is “idle.” If you step away from your computer, AggregatorHost might trigger a background synchronization or a low-priority scan. This is why you might return to your desk and hear your laptop fans spinning, only to see AggregatorHost at the top of the Task Manager list. It is essentially taking advantage of your inactivity to ensure the system is clean.
The Shift Toward Modular Architecture
In older versions of Windows, security was often handled by a single, massive process. Modern Windows versions have moved toward a modular “micro-service” architecture. AggregatorHost is a product of this shift. By breaking functions into smaller host processes, Microsoft makes the OS more stable and easier to update. When a new security feature is added, Microsoft can simply update the instructions handled by the AggregatorHost rather than rewriting the entire security core.
3. Troubleshooting High CPU and Disk Usage

While AggregatorHost is a legitimate and necessary process, it isn’t always perfectly optimized. There are instances where users report that the process consumes 30%, 50%, or even 100% of their CPU or Disk resources, leading to system lag and overheating.
Common Causes of Resource Spikes
High resource usage by AggregatorHost is usually temporary. It typically occurs during:
- Large Windows Updates: After a major OS update, the security database often needs a full re-indexing, which is handled by this process.
- Corrupted Security Definitions: If a Windows Defender update fails or becomes corrupted, AggregatorHost may enter a loop, trying to process data that it cannot read.
- Conflicts with Third-Party Antivirus: If you have another antivirus (like McAfee or Norton) installed, it can sometimes clash with Windows Defender’s background processes, causing AggregatorHost to work overtime as it competes for file access.
How to Resolve Performance Issues
If you notice that AggregatorHost is consistently slowing down your machine, there are several steps you can take to mitigate the issue:
- Run Windows Update: Often, a spike in CPU usage is caused by a known bug that Microsoft has already patched. Ensure your system is fully up to date.
- Restart the Windows Security Service: You can do this through the “Services” app (services.msc). Restarting the “Windows Security Service” can clear the temporary cache and stop any stuck processes.
- Perform a System File Checker (SFC) Scan: Open the Command Prompt as an administrator and type
sfc /scannow. This will check for corrupted system files—including AggregatorHost—and replace them with healthy versions from the Windows image. - Check for Disk Errors: Sometimes high disk usage is a result of the process struggling to read data from a failing sector on your hard drive. Running a
chkdskcommand can help identify if the hardware is the underlying problem.
Should You Disable It?
Technically, it is possible to disable the services associated with AggregatorHost, but it is highly discouraged. Disabling this process effectively blinds Windows Security. You would lose real-time protection, automated updates, and the ability for the OS to report on its own health. For 99% of users, the better path is to fix the underlying performance issue rather than turning off the security feature entirely.
4. Is It Malware? How to Distinguish Between System Files and Threats
Whenever a process uses high resources, the specter of malware arises. Cybercriminals often name their malicious files similarly to legitimate system files to avoid detection—a technique known as “masquerading.”
Verifying the File Path
The legitimate AggregatorHost.exe file is always located in a specific directory: C:WindowsSystem32.
To verify yours:
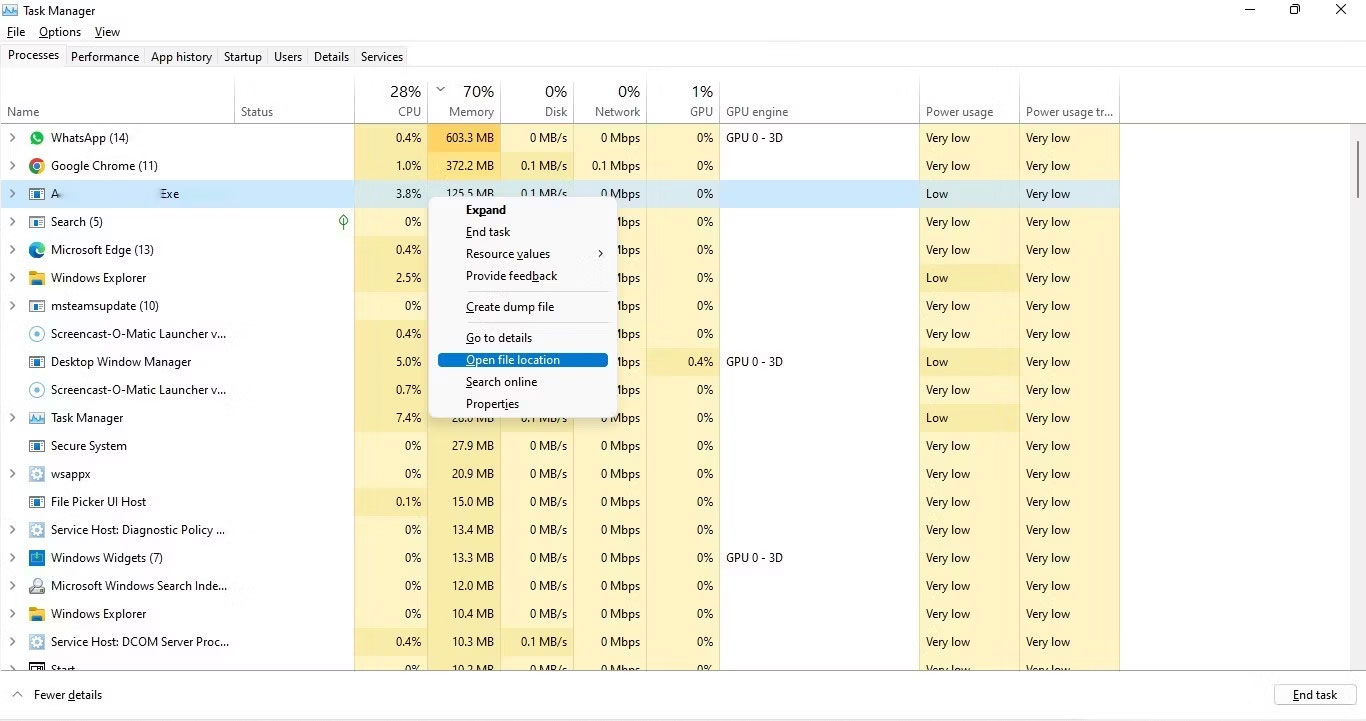
- Open Task Manager.
- Find AggregatorHost in the “Details” tab.
- Right-click it and select Open file location.
If the folder that opens is anywhere other thanSystem32(for example, inAppDataRoamingor a temp folder), you are likely dealing with a virus or a trojan.
Checking the Digital Signature
Microsoft signs all its official system files with a digital certificate. To check this:
- Right-click the
AggregatorHost.exefile in its folder. - Select Properties and go to the Digital Signatures tab.
- Look for “Microsoft Windows” or “Microsoft Corporation.” If the signature is missing or belongs to an unknown entity, it is a red flag.
Common Malware Disguises
Some miners and info-stealers might name themselves aggregator-host.exe (with a hyphen) or agregatorhost.exe (misspelled). They rely on the user’s quick glance to stay hidden. If you see two instances of AggregatorHost running and one is using significantly more power than the other, perform a full system scan with a reputable secondary scanner like Malwarebytes to ensure your system’s integrity.
5. Maintaining Long-Term System Health
Understanding AggregatorHost is part of a broader strategy for maintaining a healthy Windows environment. As software becomes more complex, the burden on the user to understand these background processes increases.
Keeping Your Security Suite Lean
One of the best ways to ensure AggregatorHost runs efficiently is to avoid “bloatware.” Many new laptops come pre-installed with trial versions of various security suites. These often interfere with native Windows processes. If you prefer Windows Defender, uninstalling these trials and using the “Refresh” feature in Windows Security can streamline background operations and reduce the workload on AggregatorHost.
Managing Startup and Background Apps
AggregatorHost doesn’t work in a vacuum; it interacts with everything else running on your PC. By managing your startup apps (via the Task Manager “Startup” tab), you reduce the total number of processes that the security engine needs to monitor upon boot-up. This results in a faster login experience and less initial CPU “thrashing.”
The Future of Windows Background Processes
As we move further into the era of AI and machine learning, processes like AggregatorHost will likely become even more sophisticated. Microsoft is increasingly using local AI models to detect anomalies in system behavior. Future versions of this process may use even more telemetry to provide “zero-trust” security environments. Staying informed about these components allows you to distinguish between a healthy, busy computer and one that is genuinely in trouble.
In conclusion, AggregatorHost.exe is a vital, legitimate part of the Windows Security infrastructure. While it may occasionally cause performance hiccups, its role in aggregating security data and coordinating defenses is essential for protecting your data from modern cyber threats. By knowing how to verify its authenticity and resolve resource conflicts, you can ensure your PC stays both fast and secure.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.