In the intricate world of cybersecurity, the concept of a Demilitarized Zone (DMZ) plays a pivotal role in safeguarding the digital assets of an organization. Much like its geopolitical namesake, a network DMZ is a buffer zone, a strategically isolated segment of a private network that sits between an untrusted external network (like the internet) and a trusted internal network. Its primary purpose is to provide an additional layer of security, allowing external users to access specific services hosted within the DMZ without granting them direct access to the sensitive internal network. This architectural design is crucial for businesses and organizations that offer public-facing services such as web servers, email servers, or DNS servers, while simultaneously needing to protect their confidential data and internal systems.
The Foundational Principles of a Network DMZ
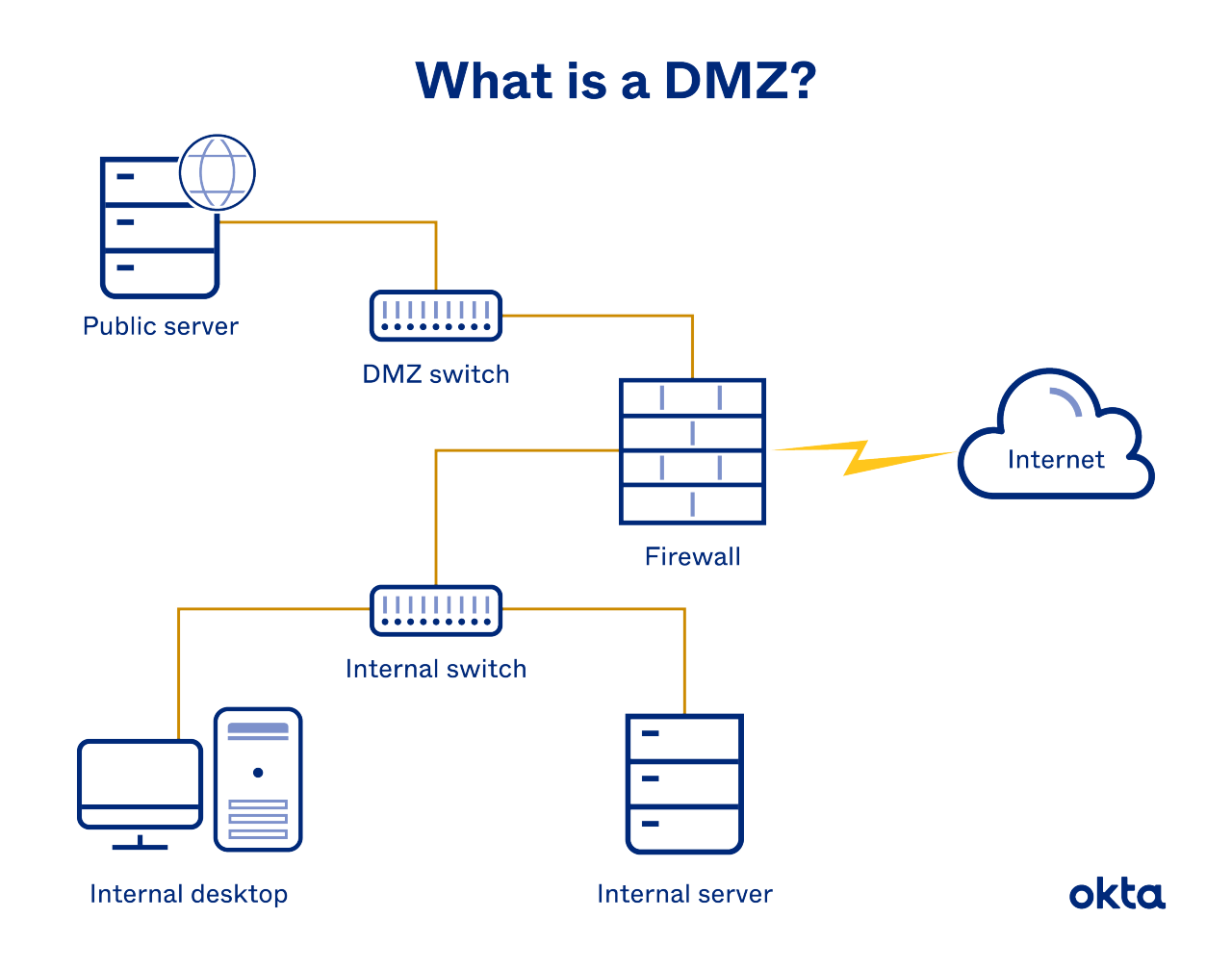
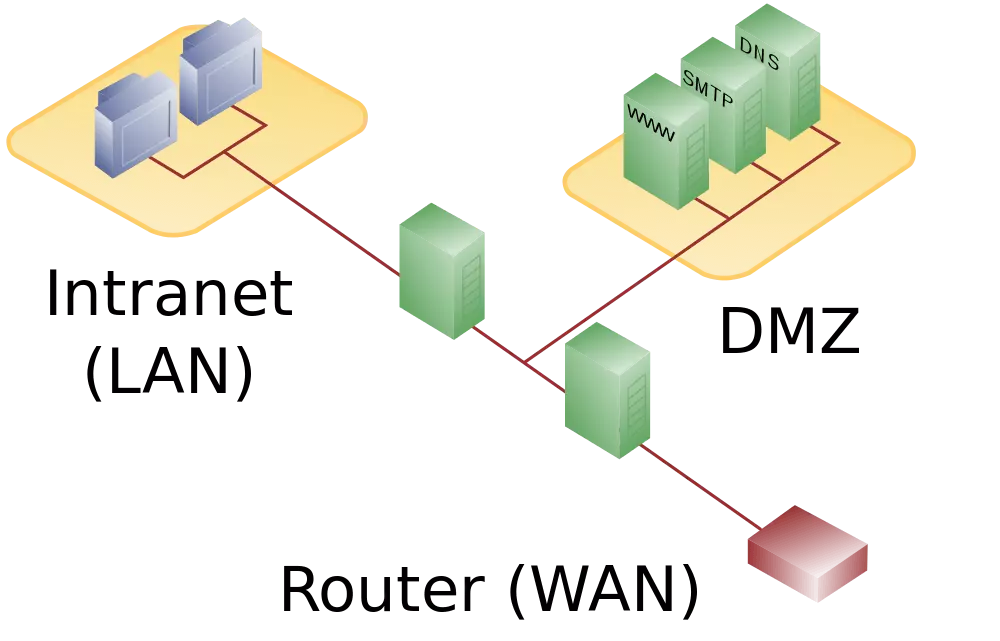
The core idea behind a network DMZ is segregation. Instead of directly exposing critical internal servers to the internet, a DMZ acts as an intermediary. This intermediary zone hosts services that are intended for public access, but these services are carefully managed and monitored. The DMZ is typically implemented using a combination of firewalls and routers, creating a network segment that is neither fully trusted nor completely untrusted. Understanding the fundamental principles governing its operation is key to appreciating its security benefits.
Layered Security Architecture
At its heart, a DMZ is an embodiment of layered security, also known as defense in depth. This strategy posits that no single security control is foolproof. Instead, by implementing multiple, independent layers of security, the overall resilience of the system is significantly enhanced. In a DMZ setup, this typically involves at least two firewalls: an external firewall protecting the DMZ from the internet and an internal firewall safeguarding the internal network from the DMZ.
The external firewall permits traffic from the internet to reach specific ports and protocols destined for servers within the DMZ. However, it strictly blocks any traffic attempting to bypass the DMZ and reach the internal network. Conversely, the internal firewall allows only authorized traffic from the DMZ to enter the internal network, and often imposes even stricter rules. This dual firewall approach ensures that even if an attacker successfully compromises a server within the DMZ, they are still faced with another formidable barrier before gaining access to the organization’s most sensitive data.
Controlled Access and Exposure
The primary benefit of a DMZ is the controlled exposure of services. Servers that need to be accessible from the internet, such as web servers hosting a company’s website or mail servers handling email, are placed within the DMZ. This means that if one of these servers is compromised, the damage is contained within the DMZ. The attacker would then need to breach the internal firewall to access the internal network, a much more difficult task.
This controlled access is achieved through granular firewall rules. Firewalls are configured to allow only specific types of traffic to reach the DMZ servers. For instance, a web server might only be allowed to accept HTTP (port 80) and HTTPS (port 443) traffic from the internet. Any other inbound traffic is blocked. Similarly, outbound traffic from the DMZ to the internal network is severely restricted. For example, a web server might only be permitted to query a database server on the internal network for specific data, but it would not be allowed to initiate arbitrary connections or transfer large files. This principle of least privilege is paramount in DMZ design.
Isolation of Critical Assets
Perhaps the most significant advantage of a DMZ is the isolation it provides for critical internal assets. Confidential customer data, financial records, intellectual property, and internal applications that are not meant for public consumption reside in the secure internal network, behind the internal firewall. By placing these valuable assets in a segment of the network that is entirely inaccessible from the internet, the risk of data breaches and unauthorized access is dramatically reduced.
Even if a sophisticated attack manages to penetrate the external defenses and compromise a DMZ server, the internal network remains a fortress. The attacker would face the challenge of defeating the internal firewall, which is typically configured with much more restrictive policies than the external firewall. This isolation is not just a theoretical benefit; it’s a practical implementation of security best practices that significantly strengthens an organization’s overall security posture.
Implementing a Network DMZ: Architecture and Components
The effective implementation of a DMZ requires careful planning and the judicious selection of network components. While the concept is straightforward, the actual deployment involves specific architectural considerations and hardware/software choices. The goal is to create a secure, isolated segment that effectively serves its purpose without introducing new vulnerabilities.
Single-Homed vs. Dual-Homed Firewalls
Historically, DMZs were often implemented using a single firewall with three network interfaces (a “triple-homed” firewall). One interface connected to the internet, another to the DMZ, and a third to the internal network. However, modern security best practices and the availability of more robust networking hardware have largely favored a dual-homed firewall approach, which is generally considered more secure.
In a dual-homed firewall configuration, two separate firewalls are used. The external firewall connects the internet to the DMZ, and the internal firewall connects the DMZ to the internal network. This approach offers several advantages:
- Enhanced Security: If one firewall is compromised, the other still provides protection.
- Simplified Management: Each firewall can be managed independently, with specific policies tailored to its role.
- Reduced Complexity: Less complex firewall configurations can lead to fewer misconfigurations and security holes.
- Better Performance: By distributing the firewalling tasks, overall network performance can be improved.
The external firewall is configured to allow specific inbound traffic to the DMZ, while the internal firewall is configured to allow specific outbound traffic from the DMZ to the internal network and strictly control any inbound traffic from the DMZ.
Firewall Configuration and Rule Sets
The effectiveness of a DMZ hinges on the precise configuration of its firewalls and the establishment of robust rule sets. These rules dictate what traffic is permitted and what is denied, forming the backbone of the DMZ’s security. The principle of least privilege is strictly applied here, meaning that only the absolute minimum necessary access is granted.
For inbound traffic from the internet to the DMZ, rules are typically defined to allow specific protocols and ports for the services hosted in the DMZ. For example, a web server might only permit TCP traffic on port 80 (HTTP) and port 443 (HTTPS). Any other inbound traffic is automatically dropped or rejected.
For outbound traffic from the DMZ to the internal network, the rules are even more stringent. A web server might need to query an internal database. In this case, the rule would explicitly allow TCP traffic on the specific port used by the database from the web server’s IP address to the database server’s IP address. No other outbound connections are permitted unless absolutely essential.
Furthermore, rules governing traffic between the DMZ and the internet are also vital. Typically, outbound traffic from the DMZ to the internet is permitted, allowing DMZ servers to receive necessary updates or communicate with external APIs. However, these rules are also carefully scrutinized to prevent the DMZ from being used as a launching pad for malicious attacks against other external systems.

Proxy Servers and Bastion Hosts
Within a DMZ architecture, certain specialized components are often employed to further enhance security and control. Proxy servers and bastion hosts are two such examples, each serving a distinct purpose in managing access and mitigating risks.
A proxy server acts as an intermediary for specific types of traffic. For instance, an outbound web proxy in the DMZ can filter and log all web requests made by internal users (if accessing the internet through the DMZ). Conversely, an inbound proxy can handle requests for web content, fetching it from the internet and serving it to external users. This approach can offer benefits like caching, content filtering, and masquerading the origin of requests.
A bastion host is a highly secured server positioned within the DMZ. It is specifically hardened and configured to withstand potential attacks. Bastion hosts are often used as the sole point of entry for administrators to access the internal network. All remote administrative access to internal servers is routed through the bastion host, where it is logged, monitored, and potentially audited. This centralizes administrative access, making it easier to control and secure. The bastion host itself is heavily protected, with minimal services running and strict access controls.
The Role and Benefits of a DMZ in Modern Networking
In today’s interconnected digital landscape, the role of a DMZ has evolved but remains critically important for robust network security. Its ability to create a secure buffer zone for public-facing services offers significant advantages for organizations of all sizes, from small businesses to large enterprises.
Protecting Internal Resources and Data
The paramount benefit of a DMZ is the enhanced protection it offers to an organization’s internal resources and sensitive data. By segmenting the network and placing public-facing services in an isolated zone, the attack surface for the internal network is dramatically reduced. If a web server or other public-facing application within the DMZ is compromised, the attacker is contained within this perimeter. They cannot directly access confidential customer databases, proprietary intellectual property, or internal employee records that reside on the secure internal network. This containment is crucial for preventing data breaches, reputational damage, and financial losses.
Enabling Secure Access to Public Services
Organizations that rely on providing services to the public, such as e-commerce platforms, online banking portals, or SaaS applications, require a mechanism to allow external users to connect. A DMZ provides a secure way to do this. Instead of exposing the internal network directly to the internet, these public services are hosted on servers within the DMZ. This allows customers and users to access the necessary applications and information without compromising the security of the organization’s internal operations and sensitive data. The DMZ acts as a controlled gateway, ensuring that only legitimate traffic reaches the public-facing services, and that any potential compromise is confined to that designated zone.
Improving Network Performance and Stability
While the primary focus of a DMZ is security, it can also contribute to improved network performance and stability. By offloading the burden of handling public-facing services from the internal network, the internal network’s resources can be dedicated to core business operations. This can lead to faster internal application performance and a more stable user experience for employees.
Furthermore, by routing internet traffic through the DMZ, it can act as a point for implementing caching mechanisms or content delivery networks (CDNs). This can accelerate the delivery of web content to external users, reducing latency and improving overall responsiveness. The segregation also helps in isolating potential performance bottlenecks. If a public-facing server in the DMZ experiences high traffic load, it is less likely to impact the performance of critical internal systems.
Common Use Cases and Best Practices for DMZs
Understanding where and how DMZs are typically deployed, along with adhering to best practices, is essential for maximizing their effectiveness. While the concept is universal, specific implementations often cater to particular needs and industry standards.
Web Servers, Email Servers, and FTP Servers
One of the most common use cases for a DMZ is to host services that need to be accessible from the internet. These include:
- Web Servers: Hosting company websites, e-commerce platforms, and public-facing applications.
- Email Servers: Handling inbound and outbound email traffic for an organization.
- FTP (File Transfer Protocol) Servers: Allowing external users to upload or download files.
- DNS (Domain Name System) Servers: Resolving domain names to IP addresses for public access.
- VPN (Virtual Private Network) Servers: Providing secure remote access for employees or partners.
By placing these servers in the DMZ, any potential attacks targeting these services are contained within this isolated network segment, protecting the more sensitive internal network.
Implementing Redundancy and High Availability
For critical public-facing services, ensuring redundancy and high availability is paramount. DMZs can be designed to incorporate these features. For instance, multiple web servers can be deployed in a load-balanced cluster within the DMZ. If one server fails, traffic is automatically redirected to other available servers, ensuring continuous service availability.
Redundancy can also be applied to the firewalls themselves. Using redundant firewall pairs ensures that if one firewall experiences an issue, the other can take over without interruption. This robust design is crucial for businesses that cannot afford downtime for their public services.
The Importance of Regular Auditing and Updates
A DMZ, like any other network component, requires ongoing maintenance and vigilance. Regular auditing of firewall logs and server configurations is essential to detect any suspicious activity or potential security misconfigurations. Unattended or unpatched servers in the DMZ can quickly become entry points for attackers.
Keeping all software and firmware on DMZ servers and firewalls up-to-date with the latest security patches is non-negotiable. This proactive approach helps to close known vulnerabilities that attackers might exploit. Furthermore, regularly reviewing and refining firewall rule sets to ensure they remain relevant and effective is a critical aspect of maintaining a secure DMZ. As the organization’s needs and the threat landscape evolve, so too should the DMZ’s security posture.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.