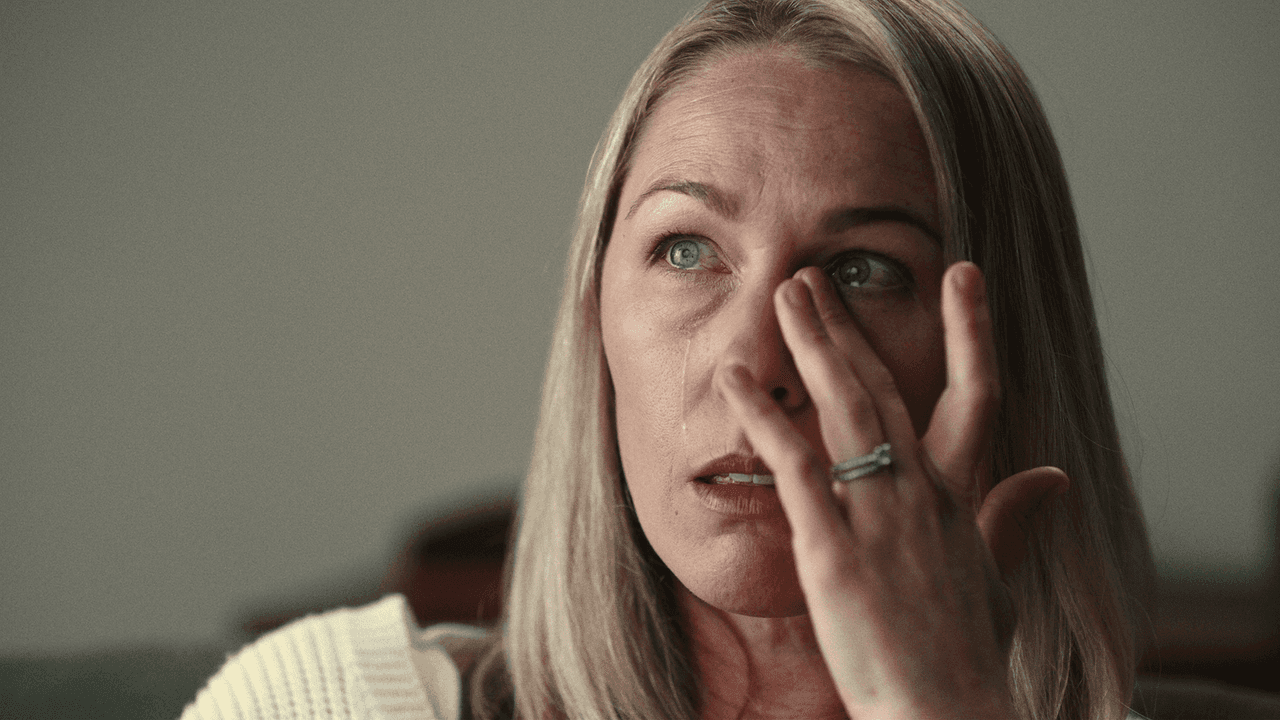
The 2015 kidnapping of Denise Huskins, often sensationalized in the media as the “Real-Life Gone Girl” story, is frequently discussed through the lens of true crime and police misconduct. However, beneath the headlines lies a complex narrative regarding the failure and eventual triumph of digital security and forensic technology. The case serves as a pivotal moment in how law enforcement utilizes—and sometimes ignores—digital footprints, and it offers profound lessons for the evolution of personal security tech and data-driven investigations.
To understand what happened to Denise Huskins is to understand the technical divide between traditional investigative intuition and the objective reality provided by modern digital forensics.

The Failure of Initial Digital Evidence Collection
When Denise Huskins was abducted from her boyfriend Aaron Quinn’s home in Vallejo, California, the initial investigation was plagued by a dismissal of digital evidence. The perpetrators used sophisticated methods to bypass the home’s physical security, but they left behind a trail of digital Breadcrumbs that the Vallejo Police Department (VPD) initially failed to synthesize.
The Myth of the “Digital Hoax”
In the immediate aftermath of the kidnapping, the VPD labeled the event a “hoax.” This conclusion was reached not because of a lack of evidence, but because of a failure to analyze the digital communication properly. The kidnapper sent several emails to a local news outlet, providing proof of life and later, proof of Denise’s release.
From a tech perspective, the failure here was the inability of local authorities to perform rapid IP tracking and metadata analysis. Because the kidnapping did not fit the “traditional” profile, investigators ignored the digital signals that were screaming for attention. The “hoax” narrative was a direct result of human bias overriding digital data points that suggested a highly organized, tech-savvy perpetrator.
Early Investigative Oversights in Mobile Forensics
Aaron Quinn’s phone was a goldmine of evidence. He had been drugged, but the kidnappers had used his devices to monitor him and communicate. In 2015, mobile forensics was already advanced, yet the lag time in processing Quinn’s digital activity allowed the perpetrators to remain at large for months. The case highlights the critical need for “Digital First Responders”—technicians who can secure cloud data and local device caches before they are overwritten or dismissed by skeptical investigators.
How Advanced Surveillance Tech Led to the Real Perpetrator
The exoneration of Denise Huskins and Aaron Quinn did not come from a confession; it came from a physical security breach in a different jurisdiction that was solved through digital forensics. Matthew Muller, the perpetrator, was eventually linked to the Huskins case after a separate attempted robbery in Dublin, California.
GPS Tracking and Cell Tower Triangulation
The turning point occurred when Muller accidentally left a cell phone at the scene of the Dublin crime. Detectives in Dublin, unlike the Vallejo PD, utilized rigorous digital tracking. By using GPS data and cell tower triangulation, they were able to map Muller’s movements over the preceding months.
This technical mapping was the smoking gun. It placed Muller at the scene of the Huskins-Quinn residence at the exact time of the abduction. This transition from “anecdotal evidence” to “geospatial data” is what ultimately forced the FBI and the VPD to admit their errors. It demonstrated that while human witnesses can be questioned, the movement of a synced device provides an immutable record of events.
Physical Security Systems vs. Digital Vulnerabilities
Muller, a Harvard-trained lawyer and former Marine, understood the vulnerabilities of home security systems. He utilized “tech-stacking”—using drones for surveillance and specialized tools to bypass locks. The Huskins case exposed a significant gap in the consumer security market of the mid-2010s: the lack of integrated, smart-home monitoring that could alert users to perimeter breaches via mobile apps. Today’s ecosystem of Ring cameras, Nest sensors, and end-to-end encrypted home security hubs was born out of the necessity to prevent the kind of “silent entry” Muller perfected.

Digital Forensics: The Turning Point in the Huskins Case
Once the FBI became fully engaged in the Muller investigation, the scope of the tech-based inquiry expanded. The recovery of data from Muller’s personal devices revealed the terrifying extent of his planning and the technological sophistication of his crimes.
Analyzing Encrypted Communications
The kidnappers had used encrypted email services to taunt the media and the police. In 2015, the “encryption debate” was reaching a fever pitch in the tech world. Law enforcement argued that encryption hindered investigations, while tech advocates argued for the necessity of privacy.
In the Huskins case, forensic experts were able to use “logical acquisition” methods to bypass certain encryption layers on Muller’s hardware. By recovering “deleted” files from a laptop found in a Mustang registered to Muller, investigators found photos of the room where Huskins was held. This recovery of fragmented data from the hard drive’s unallocated space is a hallmark of modern digital forensics, proving that “deleted” rarely means “gone” in the eyes of a skilled forensic analyst.
The Role of the FBI’s Forensic Toolkits
The FBI utilized advanced software to reconstruct the digital environment Muller had created. This included analyzing his search history, which revealed meticulous research on his victims. The use of “Big Data” in criminal profiling allowed the FBI to link Muller to other unsolved cases. This shift—from looking for a motive to looking for a digital pattern—is how the modern security apparatus functions. By analyzing the “Digital DNA” of a suspect, tech tools can now predict and prevent crimes before they escalate to the level of the Huskins kidnapping.
Modern Applications: Learning from the “Gone Girl” Investigation
The legacy of the Denise Huskins case is etched into the way we view digital security today. It serves as a cautionary tale for both the public and the tech industry regarding the reliability of data and the danger of digital gaslighting.
Enhancing Personal Digital Security
Today, the technology available to individuals has evolved to prevent the isolation that Denise and Aaron faced. We now have:
- Emergency SOS Features: Integrated into iPhones and Androids, allowing users to send location data to emergency services and pre-set contacts silently.
- Two-Factor Authentication (2FA): Preventing unauthorized access to the communications devices that Muller used to monitor his victims.
- Cloud-Based Continuous Recording: Unlike the early 2010s, where security footage was often stored on local DVRs that could be stolen, modern footage is uploaded instantly to the cloud, ensuring an off-site record of any intrusion.
The Future of AI in Criminal Identification
Looking forward, the integration of Artificial Intelligence (AI) into forensic software will further reduce the “human error” seen in the Huskins case. AI-driven video analytics can now identify “unusual behavior” patterns in neighborhood camera feeds, potentially flagging a stalker or an unauthorized vehicle long before a crime is committed.
Furthermore, Natural Language Processing (NLP) is now used to analyze the “stylometry” of ransom notes or emails. Had the VPD used NLP in 2015, they might have noticed that the sophisticated, legalistic tone of the emails sent by the kidnapper matched the professional background of Matthew Muller, rather than the “hoax” profile they had wrongly attributed to the victims.
Conclusion: The Digital Exoneration
What happened to Denise Huskins was a tragedy compounded by a technological blind spot. For months, she and Aaron Quinn were treated as suspects because the authorities failed to trust the digital evidence available to them. It was only through the persistent application of digital forensics—tracking cell signals, recovering deleted hard drive data, and analyzing encrypted communications—that the truth was revealed.
This case stands as a landmark in the tech and security industry. It emphasizes that in the modern era, our digital identities are just as important as our physical ones. As digital security tools become more accessible and forensic software more powerful, the hope is that stories like that of Denise Huskins will never again be dismissed as fiction, but instead be solved in real-time through the power of data. The evolution of this technology ensures that while a perpetrator may hide in the shadows, their digital footprint remains indelible.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.