The illicit drug trade, a persistent global challenge, has increasingly migrated into the digital realm. While the physical appearance of substances like cocaine is a concern for law enforcement and public health officials, from a digital security perspective, understanding “what pure cocaine looks like” translates to recognizing the digital footprints, communication patterns, and online infrastructure associated with its trafficking. This article will explore how technology is employed to identify and combat the online presence of pure cocaine, focusing on the digital indicators and investigative tools that law enforcement and cybersecurity professionals utilize.

The Digital Manifestations of Illicit Drug Trade
The concept of “pure cocaine” in a digital context isn’t about its crystalline structure but about identifying the purity of the online operation itself. This involves discerning legitimate e-commerce from illicit marketplaces, recognizing coded language, and understanding the digital identities of those involved.
Identifying Illicit Online Marketplaces
The dark web has become a notorious hub for the sale of illegal substances, including cocaine. These marketplaces, accessible only through specialized browsers like Tor, are designed to offer anonymity. They often mimic the appearance of legitimate e-commerce sites, featuring product listings, vendor profiles, and customer reviews. However, digital security experts look for several tell-tale signs to distinguish these from legitimate platforms. These include:
- Domain Names and URLs: While often obfuscated, patterns in domain registration, unusual top-level domains (TLDs), or the use of subdomains in specific configurations can raise red flags. The transient nature of many dark web marketplaces means they frequently migrate to new addresses, making continuous monitoring crucial.
- Website Design and Functionality: While some dark web sites are sophisticated, many exhibit amateurish design, inconsistent user interfaces, or a focus on a limited range of illicit products. Legitimate e-commerce sites generally adhere to established design principles and offer a broader array of goods or services.
- Payment Methods: Illicit marketplaces predominantly rely on cryptocurrencies like Bitcoin, Monero, or others designed for enhanced privacy. The integration of cryptocurrency wallets directly into the checkout process, without the option for traditional fiat currency transactions, is a strong indicator of illicit activity.
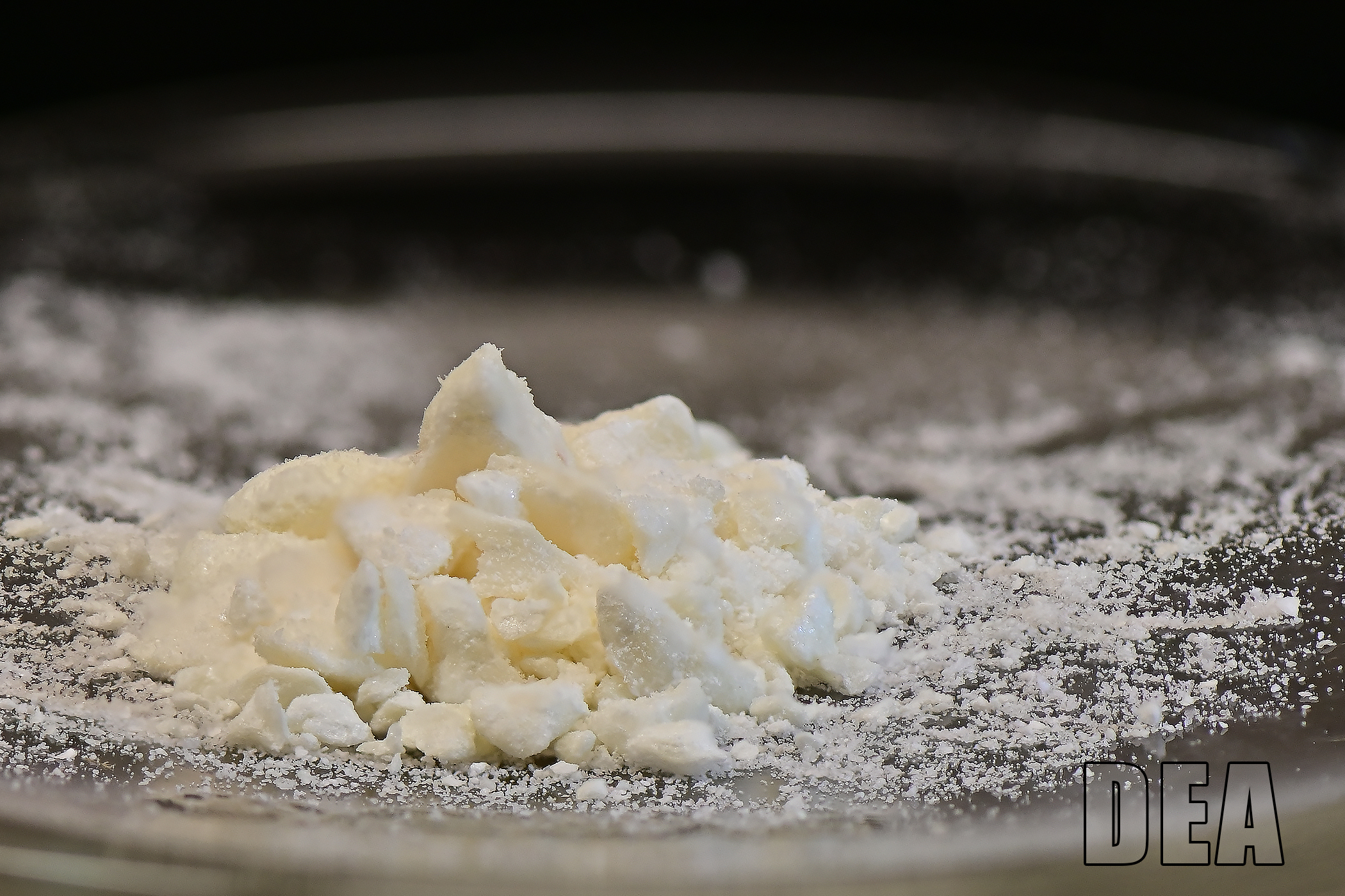
- Product Descriptions and Imagery: While vendors may attempt to create professional-looking listings, descriptions that are overly generic, focus on quantities and shipping times for illegal goods, or use coded language are often indicative of drug trafficking. Images of the product, while sometimes high-quality, may also reveal packaging or delivery methods associated with known drug couriers.
The Role of Cryptocurrencies in Illicit Transactions
Cryptocurrencies are the lifeblood of many online illicit activities. Their pseudonymous nature and decentralized structure make them attractive for drug traffickers seeking to evade traditional financial surveillance. Understanding the flow of these digital assets is paramount for digital security investigations.
Tracing Cryptocurrency Flows
While cryptocurrencies offer a degree of anonymity, they are not entirely untraceable. Blockchain technology, the underlying ledger for most cryptocurrencies, is public and immutable. Digital security firms and law enforcement agencies employ sophisticated blockchain analysis tools to track the movement of funds. This involves:
- Wallet Address Clustering: Identifying clusters of wallet addresses that are likely controlled by the same entity. This can reveal connections between buyers, sellers, and money launderers.
- Transaction Pattern Analysis: Examining the volume, frequency, and destinations of transactions. Large, irregular, or repeated transactions to and from known illicit exchange points can be significant indicators.
- De-anonymization Techniques: While challenging, advanced techniques can sometimes link cryptocurrency transactions to real-world identities through exchanges that require Know Your Customer (KYC) verification or by correlating blockchain data with other intelligence sources.
Emerging Cryptocurrencies and Privacy Coins
The emergence of privacy-focused cryptocurrencies, such as Monero, presents a greater challenge. These coins employ advanced cryptographic techniques to obscure transaction details, making them significantly harder to trace. Digital security efforts in this area focus on identifying the operational security (OpSec) measures employed by users of these coins and developing new analytical approaches to mitigate their privacy advantages.
Digital Forensics and Investigative Technologies
Beyond marketplace identification and transaction tracing, a range of digital forensics and investigative technologies are employed to understand and disrupt the “pure cocaine” trade online. This involves gathering intelligence from various digital sources.
Social Media and Encrypted Messaging Apps
Social media platforms and encrypted messaging applications, while essential for legitimate communication, are also exploited by drug traffickers. These channels can be used for recruitment, coordination, distribution, and even direct sales.
Recognizing Coded Language and Emojis
Drug traffickers often employ coded language, slang, and emojis to communicate about their activities without explicitly mentioning illegal substances. Digital security analysts and social media intelligence (SOCMINT) experts develop lexicons and algorithms to identify these patterns. For example, certain emojis might be used to represent drugs, quantities, or even the act of trafficking. Analyzing the context in which these symbols appear, alongside other communication patterns, can reveal illicit intent.
Monitoring Public and Private Channels
While encrypted messaging apps pose a significant challenge due to their end-to-end encryption, investigations often involve analyzing metadata, identifying communication patterns between known or suspected individuals, and, in certain legal circumstances, leveraging decryption capabilities. Publicly accessible social media groups, forums, and even private messages (when legally permissible) are scoured for keywords, suspicious interactions, and evidence of illicit trade.
The Use of AI and Machine Learning in Threat Detection
The sheer volume of data generated online necessitates the use of advanced analytical tools. Artificial intelligence (AI) and machine learning (ML) are increasingly being deployed to automate the detection of illicit activities.
Automated Content Moderation and Anomaly Detection
AI algorithms can be trained to scan vast amounts of online content, identifying posts, images, or discussions that match predefined patterns associated with drug trafficking. This includes recognizing specific keywords, phrases, and even visual cues in images that might indicate the presence of illicit substances or their associated paraphernalia. ML models can also detect anomalies in communication networks or transaction patterns that deviate from normal behavior, flagging them for human review.
Predictive Analytics for Threat Intelligence
By analyzing historical data and current trends, AI can be used to develop predictive models. These models can forecast potential new marketplaces, identify emerging trafficking routes, or predict the likelihood of certain types of illicit activities occurring in specific online spaces. This proactive approach allows digital security efforts to be more targeted and effective.
Challenges and Future Directions in Digital Security
The dynamic nature of the illicit drug trade, coupled with rapid advancements in technology, presents ongoing challenges for digital security professionals. The constant evolution of anonymization techniques and the global reach of the internet require a continuous adaptation of strategies.
The Evolving Landscape of Anonymization Tools
As digital security measures become more sophisticated, so too do the tools used to circumvent them. Advancements in VPN technology, secure communication protocols, and the development of new cryptocurrencies with enhanced privacy features create a constant arms race. Staying ahead requires continuous research into emerging anonymization techniques and the development of countermeasures.
International Cooperation and Legal Frameworks
Combating the global digital drug trade necessitates robust international cooperation. Law enforcement agencies and cybersecurity professionals across different jurisdictions must share intelligence, coordinate investigations, and collaborate on the development of effective legal frameworks to address online criminal activity. The challenge lies in harmonizing differing national laws and establishing protocols for cross-border digital evidence collection and prosecution.

The Ethical Considerations of Digital Surveillance
The methods employed to identify and disrupt illicit online activities, while necessary for public safety, also raise important ethical considerations regarding privacy and civil liberties. Digital security professionals must navigate this complex terrain, ensuring that surveillance efforts are proportionate, targeted, and conducted within strict legal and ethical boundaries. The focus remains on identifying and mitigating threats without infringing upon the legitimate privacy of law-abiding citizens.
In conclusion, understanding “what pure cocaine looks like” from a digital security standpoint is an intricate process of identifying digital footprints, analyzing communication patterns, and leveraging advanced technologies to detect and disrupt illicit online activities. The ongoing battle against the digital drug trade is a testament to the critical role of technology and the continuous innovation required to safeguard online spaces from criminal exploitation.
